Catalog of Control Systems Security: Recommendations for Standards Developers
Catalog of Control Systems Security: Recommendations for Standards Developers
Catalog of Control Systems Security: Recommendations for Standards Developers
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
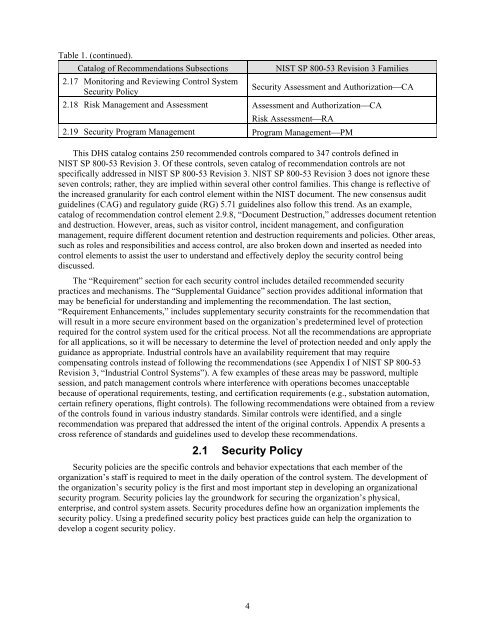
Table 1. (continued).<br />
<strong>Catalog</strong> <strong>of</strong> <strong>Recommendations</strong> Subsections NIST SP 800-53 Revision 3 Families<br />
2.17 Monitoring and Reviewing <strong>Control</strong> System<br />
<strong>Security</strong> Policy<br />
4<br />
<strong>Security</strong> Assessment and AuthorizationCA<br />
2.18 Risk Management and Assessment Assessment and AuthorizationCA<br />
Risk AssessmentRA<br />
2.19 <strong>Security</strong> Program Management Program ManagementPM<br />
This DHS catalog contains 250 recommended controls compared to 347 controls defined in<br />
NIST SP 800-53 Revision 3. Of these controls, seven catalog <strong>of</strong> recommendation controls are not<br />
specifically addressed in NIST SP 800-53 Revision 3. NIST SP 800-53 Revision 3 does not ignore these<br />
seven controls; rather, they are implied within several other control families. This change is reflective <strong>of</strong><br />
the increased granularity <strong>for</strong> each control element within the NIST document. The new consensus audit<br />
guidelines (CAG) and regulatory guide (RG) 5.71 guidelines also follow this trend. As an example,<br />
catalog <strong>of</strong> recommendation control element 2.9.8, “Document Destruction,” addresses document retention<br />
and destruction. However, areas, such as visitor control, incident management, and configuration<br />
management, require different document retention and destruction requirements and policies. Other areas,<br />
such as roles and responsibilities and access control, are also broken down and inserted as needed into<br />
control elements to assist the user to understand and effectively deploy the security control being<br />
discussed.<br />
The “Requirement” section <strong>for</strong> each security control includes detailed recommended security<br />
practices and mechanisms. The “Supplemental Guidance” section provides additional in<strong>for</strong>mation that<br />
may be beneficial <strong>for</strong> understanding and implementing the recommendation. The last section,<br />
“Requirement Enhancements,” includes supplementary security constraints <strong>for</strong> the recommendation that<br />
will result in a more secure environment based on the organization’s predetermined level <strong>of</strong> protection<br />
required <strong>for</strong> the control system used <strong>for</strong> the critical process. Not all the recommendations are appropriate<br />
<strong>for</strong> all applications, so it will be necessary to determine the level <strong>of</strong> protection needed and only apply the<br />
guidance as appropriate. Industrial controls have an availability requirement that may require<br />
compensating controls instead <strong>of</strong> following the recommendations (see Appendix I <strong>of</strong> NIST SP 800-53<br />
Revision 3, “Industrial <strong>Control</strong> <strong>Systems</strong>”). A few examples <strong>of</strong> these areas may be password, multiple<br />
session, and patch management controls where interference with operations becomes unacceptable<br />
because <strong>of</strong> operational requirements, testing, and certification requirements (e.g., substation automation,<br />
certain refinery operations, flight controls). The following recommendations were obtained from a review<br />
<strong>of</strong> the controls found in various industry standards. Similar controls were identified, and a single<br />
recommendation was prepared that addressed the intent <strong>of</strong> the original controls. Appendix A presents a<br />
cross reference <strong>of</strong> standards and guidelines used to develop these recommendations.<br />
2.1 <strong>Security</strong> Policy<br />
<strong>Security</strong> policies are the specific controls and behavior expectations that each member <strong>of</strong> the<br />
organization’s staff is required to meet in the daily operation <strong>of</strong> the control system. The development <strong>of</strong><br />
the organization’s security policy is the first and most important step in developing an organizational<br />
security program. <strong>Security</strong> policies lay the groundwork <strong>for</strong> securing the organization’s physical,<br />
enterprise, and control system assets. <strong>Security</strong> procedures define how an organization implements the<br />
security policy. Using a predefined security policy best practices guide can help the organization to<br />
develop a cogent security policy.