Wi-Fi Authentication Demystified Companion Guide - Xirrus
Wi-Fi Authentication Demystified Companion Guide - Xirrus
Wi-Fi Authentication Demystified Companion Guide - Xirrus
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
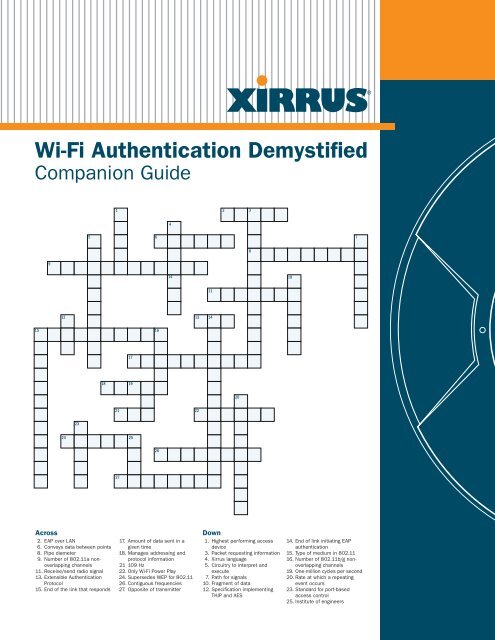
<strong>Wi</strong>-<strong>Fi</strong> <strong>Authentication</strong> <strong>Demystified</strong><br />
<strong>Companion</strong> <strong>Guide</strong><br />
15<br />
9<br />
24<br />
23<br />
18<br />
1<br />
21<br />
27<br />
17<br />
19<br />
25<br />
16<br />
26<br />
4<br />
5 6 7<br />
12 13 14<br />
Across Down<br />
2. EAP over LAN<br />
6. Conveys data between points<br />
8. Pipe diameter<br />
9. Number of 802.11a nonoverlapping<br />
channels<br />
11. Receive/send radio signal<br />
13. Extensible <strong>Authentication</strong><br />
Protocol<br />
15. End of the link that responds<br />
14<br />
17. Amount of data sent in a<br />
given time<br />
18. Manages addressing and<br />
protocol information<br />
21 109 Hz<br />
22. Only <strong>Wi</strong>-<strong>Fi</strong> Power Play<br />
24. Supersedes WEP for 802.11<br />
26. Contiguous frequencies<br />
27. Opposite of transmitter<br />
22<br />
11<br />
2<br />
20<br />
1. Highest performing access<br />
device<br />
3. Packet requesting information<br />
4. <strong>Xirrus</strong> language<br />
5. Circuitry to interpret and<br />
execute<br />
7. Path for signals<br />
10. Fragment of data<br />
12. Specification implementing<br />
TKIP and AES<br />
3<br />
8<br />
10<br />
14. End of link initiating EAP<br />
authentication<br />
15. Type of medium in 802.11<br />
16. Number of 802.11b/g nonoverlapping<br />
channels<br />
19. One-million cycles per second<br />
20. Rate at which a repeating<br />
event occurs<br />
23. Standard for port-based<br />
access control<br />
25. Institute of engineers
2<br />
<strong>Wi</strong>-<strong>Fi</strong> <strong>Authentication</strong> <strong>Demystified</strong><br />
Contents<br />
Introduction .............................................................................3<br />
The History of <strong>Authentication</strong> .....................................................4<br />
<strong>Authentication</strong> Framework .........................................................5<br />
<strong>Wi</strong>reless Infrastructure ..............................................................7<br />
Roaming and <strong>Authentication</strong> ......................................................9<br />
Recommendations ..................................................................10<br />
Leading Architecture ...............................................................11<br />
About <strong>Xirrus</strong> ...........................................................................11<br />
©2008 <strong>Xirrus</strong>, Inc. All Rights Reserved.
<strong>Companion</strong> <strong>Guide</strong><br />
Introduction<br />
<strong>Authentication</strong> is a critical part of any network security policy. <strong>Authentication</strong> validates the identity of a user<br />
or device, which is an important point as most people only look at authentication as authenticating the<br />
client. When using a mutual authentication scheme, not only is the client authenticated, but so is the network<br />
itself. This process allows the first device to authenticate the second and the second device to authenticate<br />
the first. Initial wireless authentication used a wireless encryption method, known as WEP to provide the<br />
authentication. The idea being that if both sides had a common encryption key it would serve as a way to<br />
provide proper authentication. However, WEP was cracked and as a result it was no longer considered to be<br />
sufficient as an authentication or encryption method.<br />
The overall goal of <strong>Wi</strong>-<strong>Fi</strong> authentication is to ensure that an authorized device does not connect to unauthorized<br />
access devices, such as a rogue AP. Rogue APs are unauthorized devices that have been detected in a<br />
network. Rogues can be either benign, such as neighboring APs or newly added devices or a threat when<br />
added to the network for malicious reasons. These rogue APs can create numerous issues for the network,<br />
for example:<br />
1.<br />
2.<br />
An attack called man-in-the-middle can occur in which the rogue insert themselves between authorized<br />
devices and collect information and credentials from the user and the network.<br />
An attack called replay-attack in which a valid data transmission is maliciously or fraudulently repeated<br />
or delayed by the attacker. These attacks can be designed to steal information or effect the normal<br />
operation, such as a denial of service attack.<br />
Typical <strong>Wi</strong>-<strong>Fi</strong> Infrastructure<br />
In a typical <strong>Wi</strong>-<strong>Fi</strong><br />
infrastructure, stations<br />
associate to an Access<br />
Point. The Access Point<br />
is the Authenticator and<br />
interfaces with the<br />
<strong>Authentication</strong> Server to<br />
validate the stations<br />
identity and then allow<br />
access to the network.<br />
<strong>Wi</strong>reless Stations<br />
(Supplicant)<br />
Ethernet<br />
Switch<br />
Authenticator Authenticator<br />
©2008 <strong>Xirrus</strong>, Inc. All Rights Reserved. 3<br />
Router<br />
<strong>Authentication</strong><br />
Server
4<br />
For these reasons and more not listed, it helps to hide the users’ identity from being exposed from a sniffer or<br />
other type of eavesdropper on the network. There are additional benefits to authentication, such as encryption<br />
key management, which automatically expires user passwords and forces them to change credentials, like<br />
user name and password on a regular basis. <strong>Authentication</strong> is critical for protecting corporate and personal<br />
information, scaling and managing large groups of users at multiple locations normally requires the use<br />
of dynamic authentication process. In addition to just authorizing access to the network it also provides<br />
accounting and auditing information of every connection occurring in the network. All of this is extremely<br />
important in proving compliance with regulations such as HIPPA and PCI. Many forms of <strong>Authentication</strong> also<br />
allow for extended control over end-user access, such as time-of-day or restricted guest-access policies.<br />
The History of <strong>Authentication</strong><br />
Most people are familiar with RADIUS, which stands for Remote <strong>Authentication</strong> Dial-In User Service and has<br />
been around since the days of dial-up network access. The RADIUS server sits on the wired network and<br />
completes the process of authentication. The RADIUS service has three components: The authentication<br />
server, such as Microsoft’s IAS. The RADIUS client, in the wireless world this is the AP or the WLAN Switch and<br />
the Supplicant. The supplicant is the <strong>Wi</strong>-<strong>Fi</strong> client to be authenticated. The supplicant forwards authentication<br />
information to the RADIUS client, which in turns forwards this information to the RADIUS server. The server will<br />
authorize or deny access to the network. In addition the RADIUS server may return configuration information<br />
to the AP, such as placing the <strong>Wi</strong>-<strong>Fi</strong> user in a specific VLAN.<br />
RADIUS<br />
RADIUS (RFC 2138) defines the backend authentication process between the Authenticator and <strong>Authentication</strong> Server. RADIUS Attributes carry<br />
specific authentication, authorization, information and configuration detail for the Access request and response types.<br />
Code<br />
(1 Byte)<br />
Identifier<br />
(1 Byte)<br />
Length<br />
(2 Bytes)<br />
Value Description<br />
0 Access-Request<br />
2 Access-Accept<br />
3 Access-Reject<br />
4 Accounting-Request<br />
5 Accounting-Response<br />
11 Access-Challenge<br />
12 Status-Server (experimental)<br />
13 Status-Client (experimental)<br />
255 Reserved<br />
Authenticator<br />
<strong>Fi</strong>eld contains<br />
challenge text<br />
and MD5<br />
hashed<br />
responses<br />
(passwords)<br />
Authenticator<br />
(16 Bytes)<br />
Example Attributes include:<br />
– User Name (Type <strong>Fi</strong>eld = 1)<br />
– Password (Type <strong>Fi</strong>eld = 2)<br />
Items such as which VLAN the user is to be<br />
assigned to or what wireless user group policies<br />
to use can be defined by the use of Vendor<br />
Specific Attributes (VSAs) (Type <strong>Fi</strong>eld = 26).<br />
...<br />
Attribute 1 Attribute ...N<br />
Type<br />
(1 Byte)<br />
Values=<br />
1 to 63<br />
Length<br />
(1 Byte)<br />
Value<br />
(1 or<br />
more Bytes)<br />
Attribute <strong>Fi</strong>eld<br />
A RADIUS server can also access things like an active directory service or other directory service on the back<br />
end of the network to enforce policies. This allows RADIUS to be implemented without having to recreate<br />
account information that may already exist in another directory.<br />
©2008 <strong>Xirrus</strong>, Inc. All Rights Reserved.
In 1999, the 802.11standard was adopted which contained a couple of methods for basic authentication. One<br />
was called “open authentication” which was not really authentication at all. Open authentication basically<br />
allows <strong>Wi</strong>-<strong>Fi</strong> association to all 802.11 compliant devices. A second method was WEP and stood for <strong>Wi</strong>red<br />
Equivalent Privacy. This form of authentication, known as “shared key WEP authentication” allowed a shared<br />
WEP key to be used for authenticating users to access the network. In May 2001, an IEEE Task Group known<br />
as 802.11i began work on new enhanced security standards for 802.11. By August 2001, WEP was cracked<br />
creating a large security breach and adversely impacting the adoption of <strong>Wi</strong>-<strong>Fi</strong> in the enterprise. At this point<br />
WEP became known as Weak Encryption Protocol.<br />
Needing improved security and not being able to wait for the developing IEEE standard, the <strong>Wi</strong>-<strong>Fi</strong> Alliance<br />
announced in October 2002 a new security standard called WPA, which stands for <strong>Wi</strong>-<strong>Fi</strong> Protected Access.<br />
It was a security enhancement based on the work being done by the IEEE 802.11i Task Group. WPA was<br />
quickly put in place to correct the problems with WEP. This was accomplished via the implementation of an<br />
authentication framework and stronger encryption modes, and the 802.11i addendum was finally ratified.<br />
<strong>Authentication</strong> Framework<br />
There were three basic building blocks that led up to 802.11i. <strong>Fi</strong>rst, there was EAP, which stands for Extensible<br />
<strong>Authentication</strong> Protocol. EAP is a framework for authentication, allowing for a number of authentication<br />
methods to be used.<br />
EAP/EAPOL Frame Format<br />
EAPOL (EAP Over LAN) is used by 802.1X to encapsulate the EAP protocol. The EAP protocol defines a number of methods for authentication.<br />
EAPOL Packet<br />
Destination MAC<br />
(6 Bytes)<br />
Value Description<br />
1 Request<br />
2 Response<br />
3 Success<br />
4 Failure<br />
Source MAC<br />
(6 Bytes)<br />
Code<br />
(1 Byte)<br />
EAP Packet<br />
Ethertype<br />
Code<br />
(2 Bytes)<br />
0x888e<br />
ID<br />
(1 Byte)<br />
Protocol<br />
Version<br />
(1 Byte)<br />
1<br />
Length<br />
(2 Bytes)<br />
# of Bytes<br />
Packet<br />
Type<br />
(1 Byte)<br />
Type<br />
(1 Byte)<br />
Body<br />
Length<br />
(2 Bytes)<br />
# of Bytes<br />
Data<br />
Packet Body<br />
Value Description<br />
1 Identity<br />
2 Notification<br />
3 NAK<br />
4 MD5 Challenge<br />
Value Description<br />
0 EAP Packet<br />
1 EAPOL Start<br />
2 EAPOL Logoff<br />
3 EAPOL Key<br />
4 EAPOL Alert<br />
5 One Time Password<br />
6 Generic Token Card<br />
13 TLS<br />
©2008 <strong>Xirrus</strong>, Inc. All Rights Reserved. 5
6<br />
One of those methods is 802.1x, a port level authentication method originally designed for wired networks.<br />
802.1x, EAP, and additional encryption modes TKIP and AES were all components of the 802.11i standard.<br />
802.11i Security<br />
802.11i is the official security standard for 802.11 <strong>Wi</strong>reless LANs as ratified by the IEEE in 2004. Its operation consists of 4 primary phases<br />
to establish secure communications. Phase 2 and portion of Phase 3 are addressed in this poster; Phase 4 and a portion of Phase 3 are<br />
addressed in the companion <strong>Wi</strong>-<strong>Fi</strong> Encryption poster.<br />
Station<br />
Phase 1<br />
Phase 2<br />
Phase 3<br />
Phase 4<br />
Security Discovery/Negotiation<br />
802.1X <strong>Authentication</strong><br />
Key Management RADIUS Key Distribution<br />
Data Confidentiality and Integrity<br />
Authenticator <strong>Authentication</strong><br />
Server<br />
Additionally, mutual authentication and key exchange processes were added to the standard. All these<br />
additions allowed the authentication process to scale and also provided for dynamic key creation and<br />
updating, providing faster client authentication and roaming.<br />
©2008 <strong>Xirrus</strong>, Inc. All Rights Reserved.
802.11i Packet Exchange<br />
802.11i Packet Exchange describes the wireless authentication process, and begins with a supplicant<br />
(the wireless station) associating to the access point and initiating an 802.1X exchange.<br />
<strong>Authentication</strong><br />
Supplicant Authenticator<br />
Server<br />
Probe Request<br />
Probe Response<br />
<strong>Authentication</strong> Request<br />
<strong>Authentication</strong> Response<br />
Association Request<br />
Association Response<br />
EAPOL-Start (Start Process)<br />
EAP-Request (Identity)<br />
EAP-Response (Identity)<br />
3. The users identity is passed to the<br />
Authenticator and then forwarded to<br />
the <strong>Authentication</strong> Server.<br />
EAP-Request (Challenge)<br />
4. An EAP packet with challenge text is<br />
sent from the <strong>Authentication</strong> Server.<br />
EAP-Response (Credentials)<br />
5. An EAP packet with the encrypted<br />
challenge text is sent back to<br />
the Server.<br />
EAP-Success<br />
EAPOL Key 1<br />
EAPOL Key 2<br />
EAPOL Key 3<br />
EAPOL Key 4<br />
EAP-Logoff<br />
Port Unauthorized<br />
Port Authorized<br />
1. The authentication process starts with<br />
a virtual port in the Array set to<br />
“unauthorized” such that only<br />
authentication protocols are forwarded.<br />
2. The station starts the authentication<br />
process with an EAPOL Start message.<br />
RADIUS Access Request<br />
RADIUS Access Challenge<br />
RADIUS Access Request<br />
RADIUS Access Accept<br />
6. If the station has the correct credentials,<br />
a RADIUS Access Accept packet is returned,<br />
which also includes a Master Key used by<br />
WPA to generate unique per user encryption<br />
keys (see <strong>Wi</strong>-<strong>Fi</strong> Encryption Poster).<br />
7. 802.11i adds 4-way handshake to<br />
generate and verify encryption keys for<br />
the supplicant station (see <strong>Wi</strong>-<strong>Fi</strong><br />
Encryption Poster).<br />
8. Upon successful authentication and key<br />
exchange, the Access Point allows traffic to<br />
be forwarded from the station to the network.<br />
Port Unauthorized<br />
<strong>Wi</strong>reless Infrastructure<br />
Now let’s talk about how authentication works in a<br />
<strong>Wi</strong>-<strong>Fi</strong> network today. At a high level, the <strong>Wi</strong>-<strong>Fi</strong> client<br />
associates to an AP, also known as the authenticator.<br />
The station then sends an authentication request<br />
to the authenticator. The authenticator is designed<br />
so that prior to proper authentication all standard<br />
packets are discarded. While in this state the AP will<br />
only forward EAP packets. These packets are allowed<br />
to transverse to the wired side in order to reach the<br />
authentication server. Next, the clients and server use<br />
the EAP packets to complete a four-way handshake.<br />
The result of which is the authenticator and client<br />
define session keys, and finally, the authenticator<br />
moves its port into an authorized mode and normal<br />
access to the network ensues.<br />
As mentioned before, the 802.1x framework uses<br />
EAP to exchange information; however there are<br />
several types of EAP methods used today. Seven of<br />
these types are approved for interoperability by the<br />
<strong>Wi</strong>-<strong>Fi</strong> Alliance. The first is EAP-TLS, which requires a<br />
server-site certificate and a client-site certificate for<br />
credentials. The second most popular type is EAP-TTLS<br />
whereby a user must have a server-site certificate, and<br />
uses just a user name and password. Typically a thirdparty<br />
supplicant is needed for this method.<br />
<strong>Wi</strong>reless <strong>Authentication</strong><br />
Framework<br />
<strong>Wi</strong>-<strong>Fi</strong> <strong>Authentication</strong> (802.11i) is built on top of 802.1X and EAP.<br />
EAP (RFC 3748)<br />
Extensible<br />
<strong>Authentication</strong><br />
Protocol<br />
IEEE 802.1X<br />
<strong>Wi</strong>red port-based<br />
authentication<br />
uses EAP and EAPOL<br />
as the underlying<br />
authentication protocol<br />
IEEE 802.11i<br />
wireless authentication<br />
extends 802.1X to a<br />
wireless network and<br />
generates a Master Key.<br />
The Master Key is used by<br />
the Access Point and station<br />
to derive per session keys<br />
©2008 <strong>Xirrus</strong>, Inc. All Rights Reserved. 7
8<br />
The next type, and probably most commonly deployed is EAP-PEAP, which stands for Protected EAP. In this<br />
method, the server-site certificate is required, the client-site certificate is optional, and a standard user name<br />
and password is used. Advantage of PEAP is it can leverage user name and passwords already defined in<br />
<strong>Wi</strong>ndows Active Directory. Another type commonly seen is EAP-PEAP-GTC, which stands for Generic Token<br />
Card. It is a physical token that is used in the authentication process. Likewise, EAP-SIM uses a SIM card, a<br />
Subscriber Identity Module, for a GSM mobile handset. The last two types are Cisco authored and proprietary<br />
protocols. One is LEAP (Lightweight Extensible <strong>Authentication</strong> Protocols), which was widely used early on,<br />
but is not recommended anymore due to a dictionary attack that can be easily harnessed against it. LEAP<br />
did not require certificates on both sides of the link as only a password was needed. To fix LEAP, fast-EAP<br />
was deployed. It is still password based and also does not require certificates on either side of the link.<br />
EAP Types<br />
Server Side Client Side User Credentials User Database Security<br />
EAP Type Description Certificate Certificate Used Access Issues<br />
EAP-PEAP Protected EAP Required Optional <strong>Wi</strong>ndows XP, 2000, CE, <strong>Wi</strong>ndows Domains,<br />
(widely used) Username/Passwords and Active Directory<br />
other 3rd party Supplicants<br />
EAP-TLS EAP with Transport Layer Security Required Required Certificate <strong>Wi</strong>ndows Domains, User Identity<br />
Active Directory, Exposed<br />
Novel NDS OTP<br />
EAP-TTLS EAP with Tunneled Transport Required None Password <strong>Wi</strong>ndows Domains,<br />
Layer Security Active Directory<br />
EAP-PEAP-GTC Protected EAP with Generic Required None <strong>Wi</strong>ndows, Novell NDS,<br />
Token Card One Time Password Token<br />
EAP-SIM EAP – Subscriber Identity Module Required None Subscriber Identity Module<br />
(SIM). Uses SIM card found in (SIM Card)<br />
GSM mobile phone handsets<br />
LEAP Lightweight EAP. Not recommended None None Password <strong>Wi</strong>ndows Domains, Dictionary Attack<br />
due to dictionary attacks Active Directory User Identity Exposed<br />
Fast EAP Cisco EAP based on PEAP None None Password <strong>Wi</strong>ndows Domains,<br />
Active Directory<br />
RADIUS also has the ability to use what are called VSA, or vendor specific attributes. By using the VSA’s<br />
information can be passed from the RADIUS server to the authenticator, or AP. This information can be used<br />
for assigning a used group or VLAN assignment so policies can be applied to the end user connecting to the<br />
network.<br />
Another type of authentication available is web-based authentication, typically used to allow temporary users<br />
or guests to gain restricted access to the network. This process is used in many places, but commonly seen<br />
in hotels. When a user opens their web browser, they are redirected to a webpage where they can enter a<br />
user name and password. <strong>Authentication</strong> is then granted normally from RADIUS server and the session can<br />
continue or their connection may be redirected back to another webpage. Web pages can be hosted directly<br />
in the <strong>Xirrus</strong> <strong>Wi</strong>-<strong>Fi</strong> Array where it can be implemented on a per SSID-basis.<br />
©2008 <strong>Xirrus</strong>, Inc. All Rights Reserved.
Web-based <strong>Authentication</strong><br />
Web-Based <strong>Authentication</strong> eliminates need to configure client software but requires manual entry of username/password. It is not used to<br />
configure an encrypted wireless link.<br />
1. A user associates to an open <strong>Wi</strong>-<strong>Fi</strong> network<br />
2. User’s web session is captured and redirected to a<br />
landing page in the Access Point<br />
3. The user is prompted for a username and password<br />
4. The Access Point uses these credentials to<br />
authenticate the user with the <strong>Authentication</strong> Server<br />
5. Access is granted and the user’s original URL<br />
is reloaded<br />
Roaming and <strong>Authentication</strong><br />
Authenticator <strong>Authentication</strong><br />
Server<br />
Captive Portal Original URL<br />
Clients using 802.11i can pre-authenticate with multiple access points at the same time providing for faster<br />
roaming methods across the network. The security association generates something called the Pairwise Master<br />
Key (or PMK) which is the result of the four-way hand shake discussed before. The PMK can be cached by the<br />
client and network AP anticipating the fact that the client will roam from one AP to another. When a client<br />
attempts to roam to another AP, they can request the PMK ID they were using before or that they have in their<br />
cache. As a result of this cached key the full 802.1x exchange is not required, thus saving considerable amounts<br />
of time. This feature is fully supported by <strong>Xirrus</strong> <strong>Wi</strong>-<strong>Fi</strong> Arrays and is crucial for things like voice roaming time<br />
needs to be as short as possible.<br />
802.11i Fast Roaming<br />
Supplicant<br />
Stations can<br />
pre-authenticate<br />
with new Access Point<br />
prior to roaming<br />
Pre-<br />
Authenticate<br />
then<br />
Roam<br />
PMK Caching<br />
Authenticator<br />
<strong>Authentication</strong><br />
Server<br />
©2008 <strong>Xirrus</strong>, Inc. All Rights Reserved. 9<br />
Ethernet<br />
Switch<br />
Access Points can share Pairwise Master Keys (PMK)<br />
in advance of stations roaming to them<br />
Stations can use existing PMK when roaming to a new<br />
Access Point that has pre-shared it with prior Access Point<br />
If Access Point has PMK, only the 4-way handshake needs<br />
to take place, otherwise full 802.11X exchange takes place
10<br />
Recommendations<br />
Our recommendation for authentication is as follows:<br />
Use 802.11i and WPA-2 for the strongest security that’s available today, as well as PEAP with MS-chap<br />
for easiest administration where no client site certificates are needed. It uses the built-in <strong>Wi</strong>ndows user<br />
name and password that the user is already assigned for the domain.<br />
Use an authentication server to enforce access policies like time-of-day access. It also notifies what<br />
resources VLAN users have access to on the wired network. Web-based authentication is a great way to<br />
allow easy access on to the <strong>Wi</strong>-<strong>Fi</strong> network.<br />
Lastly, replication and availability of your authentication server is important. RADIUS servers need to be<br />
capable of handling the peak loading in terms of the number of users that authenticate to it at the same<br />
time. Also the location of your RADIUS server should not be located near a slow wan link or a remote site<br />
where it might take time and latency before the authentication process completes.<br />
©2008 <strong>Xirrus</strong>, Inc. All Rights Reserved.
Leading Architecture<br />
<strong>Xirrus</strong> planned for the success of <strong>Wi</strong>-<strong>Fi</strong> by developing<br />
an award-winning <strong>Wi</strong>-<strong>Fi</strong> architecture powerful<br />
enough to handle high-bandwidth applications today<br />
and modular enough to be upgraded for future<br />
enhancements.<br />
<strong>Wi</strong>th the <strong>Wi</strong>-<strong>Fi</strong> Array, <strong>Xirrus</strong> delivers the only ‘Power<br />
Play’ architecture in <strong>Wi</strong>-<strong>Fi</strong> networking with the<br />
most bandwidth and coverage per cable drop in<br />
the industry. <strong>Xirrus</strong> <strong>Wi</strong>-<strong>Fi</strong> Arrays deliver up to 8x<br />
the bandwidth of a single access point and are<br />
compact, easy-to-install, ceiling-mounted devices.<br />
No other current-generation <strong>Wi</strong>-<strong>Fi</strong> technology can<br />
deliver the bandwidth or throughput of <strong>Xirrus</strong> Arrays<br />
because they are limited to 2 radios producing only<br />
108Mbps of shared bandwidth.<br />
<strong>Xirrus</strong> <strong>Wi</strong>-<strong>Fi</strong> Array<br />
Multiple <strong>Wi</strong>-<strong>Fi</strong><br />
Radios Produce<br />
864Mbps of<br />
Bandwidth<br />
Redundant Gigabit Ethernet Uplinks<br />
High Gain<br />
Directional<br />
Antennas<br />
Increase<br />
Range<br />
©2008 <strong>Xirrus</strong>, Inc. All Rights Reserved. 11<br />
Sectored<br />
Antenna<br />
Sectored<br />
Antenna<br />
Sectored<br />
Antenna<br />
<strong>Wi</strong>-<strong>Fi</strong><br />
Radio<br />
<strong>Wi</strong>-<strong>Fi</strong><br />
Radio<br />
<strong>Wi</strong>-<strong>Fi</strong><br />
Radio<br />
<strong>Wi</strong>-<strong>Fi</strong><br />
Radio<br />
Sectored<br />
Antenna<br />
Sectored<br />
Antenna<br />
<strong>Wi</strong>-<strong>Fi</strong><br />
Radio<br />
<strong>Wi</strong>-<strong>Fi</strong><br />
Radio<br />
<strong>Wi</strong>-<strong>Fi</strong><br />
Radio<br />
<strong>Wi</strong>-<strong>Fi</strong><br />
Radio<br />
<strong>Wi</strong>-<strong>Fi</strong> Controller<br />
Sectored<br />
Antenna<br />
Ethernet<br />
Switch<br />
Sectored<br />
Antenna<br />
<strong>Wi</strong>-<strong>Fi</strong><br />
Radio<br />
<strong>Wi</strong>-<strong>Fi</strong><br />
Radio<br />
<strong>Wi</strong>-<strong>Fi</strong><br />
Radio<br />
Sectored<br />
Antenna<br />
Sectored<br />
Antenna<br />
<strong>Wi</strong>-<strong>Fi</strong><br />
Radio<br />
<strong>Wi</strong>-<strong>Fi</strong><br />
Radio<br />
<strong>Wi</strong>-<strong>Fi</strong><br />
Radio<br />
<strong>Wi</strong>-<strong>Fi</strong><br />
Radio<br />
Sectored<br />
Antenna<br />
Sectored<br />
Antenna<br />
Sectored<br />
Antenna<br />
50% Sector<br />
Overlap<br />
No other current-generation <strong>Wi</strong>-<strong>Fi</strong> technology can deliver<br />
the bandwidth or throughput of <strong>Xirrus</strong> <strong>Wi</strong>-<strong>Fi</strong> Arrays.<br />
By integrating these key components: the <strong>Wi</strong>-<strong>Fi</strong> controller, Gigabit Ethernet Switch, Gigabit uplinks, multiple<br />
access points, sectored antenna system, <strong>Wi</strong>-<strong>Fi</strong> stateful firewall and <strong>Wi</strong>-<strong>Fi</strong> threat sensor into a single device,<br />
<strong>Xirrus</strong> Arrays are able to provide a centrally-managed platform that delivers unparalleled range, client capacity<br />
and performance, along with better RF management and roaming for voice, video and data applications — all<br />
in a single device that is fully upgradeable to 802.11n.<br />
About <strong>Xirrus</strong><br />
<strong>Xirrus</strong>, Inc. is a privately held firm headquartered in Westlake Village, California. Founded by the same team<br />
that created Xircom (acquired by Intel in 2001), <strong>Xirrus</strong> has developed the next generation in enterprise<br />
wireless LAN architectures centered around the award-winning Array.<br />
Backed by leading venture capital firms U.S. Venture Partners and August Capital, <strong>Xirrus</strong> brings a proven<br />
management team and patented approach to delivering the performance, scalability and security needed to<br />
deploy a true wireless extension of the wired Ethernet network capable of delivering Triple Play (voice, video,<br />
data) enablement.
15<br />
S<br />
H<br />
A<br />
R<br />
E<br />
D<br />
M<br />
E<br />
D<br />
I<br />
U<br />
M<br />
9<br />
T<br />
U<br />
W<br />
W<br />
P<br />
A<br />
24<br />
8<br />
<strong>Wi</strong>-<strong>Fi</strong> <strong>Authentication</strong> <strong>Demystified</strong><br />
Crossword Puzzle—Answer Key<br />
23<br />
E<br />
P<br />
8<br />
0<br />
2<br />
1<br />
X<br />
C<br />
O<br />
N<br />
T<br />
R<br />
O<br />
L<br />
L<br />
E<br />
R<br />
2<br />
18<br />
T<br />
I<br />
F<br />
1<br />
1<br />
A<br />
R<br />
R<br />
A<br />
Y<br />
21<br />
27<br />
C<br />
R<br />
G<br />
1<br />
R<br />
-<br />
I<br />
E<br />
E<br />
E<br />
T<br />
C<br />
S<br />
H<br />
A N T<br />
H<br />
T H R<br />
E<br />
A M<br />
H<br />
E<br />
H Z<br />
17<br />
19<br />
25<br />
16<br />
26<br />
S<br />
E<br />
4<br />
X<br />
I<br />
R<br />
R<br />
I<br />
A<br />
N<br />
5 6 7<br />
12 13 14<br />
Across Down<br />
2. EAP over LAN<br />
6. Conveys data between points<br />
8. Pipe diameter<br />
9. Number of 802.11a non-overlapping<br />
channels<br />
11. Receive/send radio signal<br />
13. Extensible <strong>Authentication</strong> Protocol<br />
15. End of the link that responds<br />
17. Amount of data sent in a given time<br />
18. Manages addressing and protocol<br />
information<br />
21 109 Hz<br />
22. Only <strong>Wi</strong>-<strong>Fi</strong> Power Play<br />
24. Supersedes WEP for 802.11<br />
26. Contiguous frequencies<br />
27. Opposite of transmitter<br />
14<br />
O<br />
P<br />
I<br />
G<br />
E<br />
U<br />
E<br />
V<br />
22<br />
N<br />
E<br />
E<br />
G<br />
X<br />
C<br />
E<br />
11<br />
A<br />
A<br />
A<br />
U<br />
T<br />
H<br />
E<br />
N<br />
T<br />
I<br />
C<br />
A<br />
T<br />
O<br />
R<br />
2<br />
E<br />
L<br />
N<br />
P<br />
P<br />
R<br />
R<br />
20<br />
A<br />
T<br />
U<br />
F<br />
R<br />
E<br />
Q<br />
U<br />
E<br />
N<br />
C<br />
Y<br />
3<br />
P<br />
R<br />
O<br />
B<br />
E<br />
R<br />
E<br />
Q<br />
U<br />
E<br />
S<br />
T<br />
8<br />
U<br />
M<br />
O<br />
A<br />
N<br />
S<br />
L<br />
N<br />
N<br />
10<br />
D<br />
P<br />
A<br />
C<br />
K<br />
E<br />
T<br />
W I D T<br />
1. Highest performing access device<br />
3. Packet requesting information<br />
4. <strong>Xirrus</strong> language<br />
5. Circuitry to interpret and execute<br />
7. Path for signals<br />
10. Fragment of data<br />
12. Specification implementing TKIP<br />
and AES<br />
14. End of link initiating EAP<br />
authentication<br />
15. Type of medium in 802.11<br />
16. Number of 802.11b/g<br />
non-overlapping channels<br />
19. One-million cycles per second<br />
20. Rate at which a repeating event<br />
occurs<br />
23. Standard for port-based access<br />
control<br />
25. Institute of engineers<br />
C<br />
H<br />
A<br />
N<br />
N<br />
E<br />
L<br />
<strong>Xirrus</strong>, Inc.<br />
www.xirrus.com<br />
sales@xirrus.com<br />
370 North Westlake Blvd. Suite 200<br />
Westlake Village, California 91362, USA<br />
1.800. 947.7871 Toll Free in the US<br />
+1. 805.497.0955 Corporate Office<br />
+1. 805.497.7871 Sales<br />
+1. 805.449.1180 Fax<br />
Copyright© 2008, <strong>Xirrus</strong>, Inc. All Rights Reserved. <strong>Xirrus</strong> and the <strong>Xirrus</strong> logo<br />
are trademarks of <strong>Xirrus</strong>, Inc. All other trademarks belong to their respective<br />
owners. Protected by patent #US D526,973 S. Other patents pending.