Editor's note
Editor's note
Editor's note
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
QRjacking<br />
A malicious sticker can be pasted over the original<br />
sticker, e.g. on public advertisement in the street or<br />
other public spaces, simply replaced where possible<br />
– websites, brochures etc.<br />
Scanjacking<br />
The scanned barcode would redirect to malicious web<br />
site or run any malicious code. Hence, various attacks<br />
can be executed, e.g. phishing, man-in-the-browser<br />
(form of man-in-the-middle attack), SMS abuse (social<br />
engineering is required) etc.<br />
IPhone users and application permissions<br />
IPhone devices can be divided into two main categories<br />
– legal (factory default configuration) and jailbroken<br />
(running a hacked, modified operating system version).<br />
On one hand, legal iPhone devices can execute only<br />
Apple-approved applications, which may lower the total<br />
risk of getting malicious software on the device. On the<br />
other hand, the jailbroken devices are more vulnerable<br />
to malicious applications since these devices allow<br />
installation of applications which had not been checked<br />
and verified by Apple.<br />
There are several options to install applications on<br />
iPhones: App Store, iTunes, iPhone configuration<br />
utility and over-the-air (from a web server). Of course,<br />
Cidya and Installous are also available on jailbroken<br />
devices.<br />
One thing is certain about both the legal and most of<br />
the jailborken devices – they have a default password<br />
for the root user; by default it’s alpine (without the<br />
quotes, of course).<br />
Why is this interesting? By default, applications<br />
don’t have root access to the iPhones but instead are<br />
provided with a limited access by the user mobile (for<br />
which the default password is dottie). In order to get root<br />
privilege access, we need to do some coding as will be<br />
explained later in this article.<br />
starterkit 02/2011(2)<br />
QR botnet<br />
After understanding QR threats and iPhone limitations, I<br />
can explain the idea behind the title of this article.<br />
In order to build a botnet we need to combine<br />
the threats of the QR code readers with the iPhone<br />
limitations.<br />
The main idea of this attack is to install a malicious<br />
application from a web server directly on the iPhone. It<br />
almost does not matter whether the iPhone is legal or<br />
jailbroken with default root password.<br />
Step 1: Locate vulnerable QR reader<br />
Since we would like to install an application from a web<br />
site, the QR reader should have automatic redirection to<br />
URL. I have been testing the following 10 applications<br />
on my iPhone with iOS 5: QRReader, RedLaser,<br />
QR+, ShopSavvy, Scan, ConnectMe, HP CodeScan,<br />
ATTScanner, ScanLife and i-Nigma. To make it close<br />
to the reality, I searched the word QR in App Store and<br />
downloaded the first 10.<br />
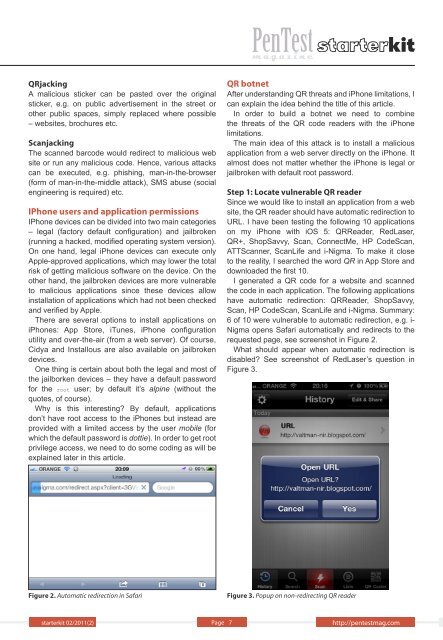
I generated a QR code for a website and scanned<br />
the code in each application. The following applications<br />
have automatic redirection: QRReader, ShopSavvy,<br />
Scan, HP CodeScan, ScanLife and i-Nigma. Summary:<br />
6 of 10 were vulnerable to automatic redirection, e.g. i-<br />
Nigma opens Safari automatically and redirects to the<br />
requested page, see screenshot in Figure 2.<br />
What should appear when automatic redirection is<br />
disabled? See screenshot of RedLaser’s question in<br />
Figure 3.<br />
Figure 2. Automatic redirection in Safari Figure 3. Popup on non-redirecting QR reader<br />
Page 7 http://pentestmag.com