JSR-000058 Java TM 2 Platform, Enterprise Edition 1.3 Specification
JSR-000058 Java TM 2 Platform, Enterprise Edition 1.3 Specification
JSR-000058 Java TM 2 Platform, Enterprise Edition 1.3 Specification
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
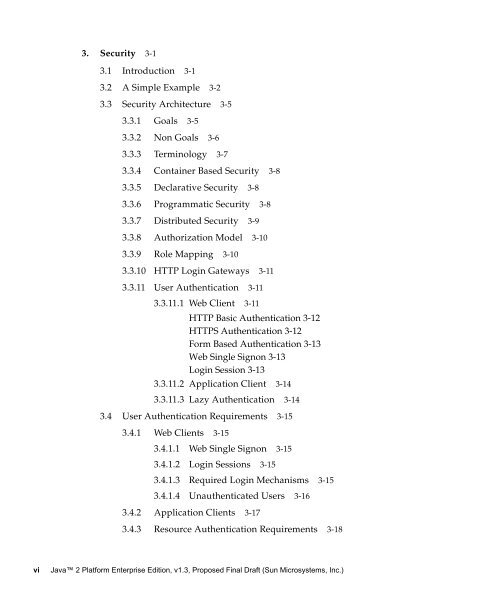
3. Security 3-1<br />
3.1 Introduction 3-1<br />
3.2 A Simple Example 3-2<br />
3.3 Security Architecture 3-5<br />
3.3.1 Goals 3-5<br />
3.3.2 Non Goals 3-6<br />
3.3.3 Terminology 3-7<br />
3.3.4 Container Based Security 3-8<br />
3.3.5 Declarative Security 3-8<br />
3.3.6 Programmatic Security 3-8<br />
3.3.7 Distributed Security 3-9<br />
3.3.8 Authorization Model 3-10<br />
3.3.9 Role Mapping 3-10<br />
3.3.10 HTTP Login Gateways 3-11<br />
3.3.11 User Authentication 3-11<br />
3.3.11.1 Web Client 3-11<br />
HTTP Basic Authentication 3-12<br />
HTTPS Authentication 3-12<br />
Form Based Authentication 3-13<br />
Web Single Signon 3-13<br />
Login Session 3-13<br />
3.3.11.2 Application Client 3-14<br />
3.3.1<strong>1.3</strong> Lazy Authentication 3-14<br />
3.4 User Authentication Requirements 3-15<br />
3.4.1 Web Clients 3-15<br />
3.4.1.1 Web Single Signon 3-15<br />
3.4.1.2 Login Sessions 3-15<br />
3.4.<strong>1.3</strong> Required Login Mechanisms 3-15<br />
3.4.1.4 Unauthenticated Users 3-16<br />
3.4.2 Application Clients 3-17<br />
3.4.3 Resource Authentication Requirements 3-18<br />
vi <strong>Java</strong> 2 <strong>Platform</strong> <strong>Enterprise</strong> <strong>Edition</strong>, v<strong>1.3</strong>, Proposed Final Draft (Sun Microsystems, Inc.)