Question Paper Information Technology & Systems - Careergyaan.org
Question Paper Information Technology & Systems - Careergyaan.org
Question Paper Information Technology & Systems - Careergyaan.org
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
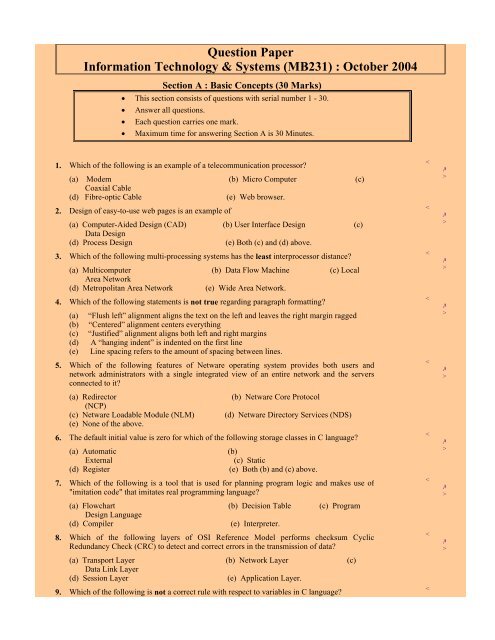
<strong>Question</strong> <strong>Paper</strong><br />
<strong>Information</strong> <strong>Technology</strong> & <strong>Systems</strong> (MB231) : October 2004<br />
Section A : Basic Concepts (30 Marks)<br />
• This section consists of questions with serial number 1 - 30.<br />
• Answer all questions.<br />
• Each question carries one mark.<br />
• Maximum time for answering Section A is 30 Minutes.<br />
1. Which of the following is an example of a telecommunication processor?<br />
(a) Modem (b) Micro Computer (c)<br />
Coaxial Cable<br />
(d) Fibre-optic Cable (e) Web browser.<br />
2. Design of easy-to-use web pages is an example of<br />
(a) Computer-Aided Design (CAD) (b) User Interface Design (c)<br />
Data Design<br />
(d) Process Design (e) Both (c) and (d) above.<br />
3. Which of the following multi-processing systems has the least interprocessor distance?<br />
(a) Multicomputer (b) Data Flow Machine (c) Local<br />
Area Network<br />
(d) Metropolitan Area Network (e) Wide Area Network.<br />
4. Which of the following statements is not true regarding paragraph formatting?<br />
(a) “Flush left” alignment aligns the text on the left and leaves the right margin ragged<br />
(b) “Centered” alignment centers everything<br />
(c) “Justified” alignment aligns both left and right margins<br />
(d) A “hanging indent” is indented on the first line<br />
(e) Line spacing refers to the amount of spacing between lines.<br />
5. Which of the following features of Netware operating system provides both users and<br />
network administrators with a single integrated view of an entire network and the servers<br />
connected to it?<br />
(a) Redirector (b) Netware Core Protocol<br />
(NCP)<br />
(c) Netware Loadable Module (NLM) (d) Netware Directory Services (NDS)<br />
(e) None of the above.<br />
6. The default initial value is zero for which of the following storage classes in C language?<br />
(a) Automatic (b)<br />
External (c) Static<br />
(d) Register (e) Both (b) and (c) above.<br />
7. Which of the following is a tool that is used for planning program logic and makes use of<br />
"imitation code" that imitates real programming language?<br />
(a) Flowchart (b) Decision Table (c) Program<br />
Design Language<br />
(d) Compiler (e) Interpreter.<br />
8. Which of the following layers of OSI Reference Model performs checksum Cyclic<br />
Redundancy Check (CRC) to detect and correct errors in the transmission of data?<br />
(a) Transport Layer (b) Network Layer (c)<br />
Data Link Layer<br />
(d) Session Layer (e) Application Layer.<br />
9. Which of the following is not a correct rule with respect to variables in C language?<br />
<<br />
<<br />
<<br />
<<br />
<<br />
<<br />
<<br />
<<br />
<<br />
A<br />
><br />
A<br />
><br />
A<br />
><br />
A<br />
><br />
A<br />
><br />
A<br />
><br />
A<br />
><br />
A<br />
>
(a) Variables should begin with a letter (b) Variables are case sensitive<br />
(c) Variable names should not be keywords (d) Spaces are not allowed<br />
(e) Underscores are not allowed in defining variable names.<br />
10. Which of the following applications usually involves software packages that assist the<br />
software developers to perform many of the activities of the systems development cycle?<br />
(a) Executive <strong>Information</strong> System (b) Computer-Aided Software Engineering<br />
(c) Office <strong>Information</strong> System (d) Multimedia Database (e) Hypertext<br />
Database.<br />
11. In which of the following analyses, an end user makes changes to variables or relationships<br />
among them, and observes the resulting changes in the values of other variables?<br />
(a) What-if Analysis (b) Sensitivity<br />
Analysis<br />
(c) Goal-seeking Analysis (d) Optimization Analysis (e) Cost-benefit<br />
Analysis.<br />
12. Functional requirements of a system are developed in which of the following stages of<br />
<strong>Systems</strong> Development Life Cycle (SDLC)?<br />
(a) <strong>Systems</strong> Investigation (b) <strong>Systems</strong> Analysis (c) <strong>Systems</strong><br />
Design<br />
(d) <strong>Systems</strong> Implementation (e) <strong>Systems</strong> Maintenance.<br />
13. Which of the following is false with respect to strategic information systems planning?<br />
(a) It is an important component of total <strong>org</strong>anizational planning and focuses on the<br />
activities and outputs of strategic business planning<br />
(b) Companies that do strategic information systems planning generally have four<br />
objectives in mind. viz., business alignment, competitive advantage, resource<br />
management and technology architecture<br />
(c) Strategic information systems planning is technology driven, and not business driven<br />
(d) Investments in information technology must be aligned with the top management's<br />
strategic agenda<br />
(e) The backing of the company's information systems policy committee and user groups is<br />
necessary for the investments in information technology.<br />
14. Which of the following systems helps users to collaborate with each other to accomplish and<br />
manage structural work tasks within a knowledge-based business process?<br />
(a) Electronic Meeting System (b) Workflow System (c)<br />
Teleconferencing<br />
(d) Data Conferencing (e) White Boarding.<br />
15. Entity-Relationship Model falls under which of the following Data Models?<br />
(a) Relational Model (b) Network Model (c) Hirerarchical<br />
Model<br />
(d) Object-Based Logical Model (e) Physical Model.<br />
16. Which of the following memories/storage devices has the fastest access speed?<br />
(a) RAM (b) ROM (c) Cache Memory (d) Hard Disk (e)<br />
Backup Tape.<br />
17. Which of the following is not an advantage of a flowchart?<br />
(a) As a flowchart is a pictorial representation of a program, it is easier for a programmer to<br />
explain the logic of a program to another programmer or to his superior through a<br />
flowchart, rather than the program itself<br />
(b) A macro flowchart that charts the mainline of the logic of a software system becomes a<br />
system model that can be broken down into detailed parts for study and further analysis<br />
of the system<br />
(c) A flowchart acts as a roadmap for the programmers<br />
(d) A flowchart facilitates in easy debugging of the program<br />
(e) There are specific standards for determining the amount of detail that should be<br />
Answer<br />
><br />
<<br />
<<br />
<<br />
<<br />
<<br />
<<br />
<<br />
<<br />
A<br />
><br />
A<br />
><br />
A<br />
><br />
A<br />
><br />
A<br />
><br />
A<br />
><br />
A<br />
><br />
A<br />
>
included in a flowchart.<br />
18. Which of the following Internet services runs on the background of the user's computer,<br />
letting him/her know when his friends or coworkers (only those who are registered) are<br />
online?<br />
(a) File Transfer Protocol (b) Internet Telephony (c)<br />
Internet Fax<br />
(d) Internet Paging (e) Usenet.<br />
19. Which of the following is not correct regarding decision-making statements in C<br />
programming language?<br />
(a) A condition is expressed using C’s relational operators<br />
(b) The relational operators compare two values to see whether they are equal to each other,<br />
not equal or whether one is greater than the other<br />
(c) The keyword ‘if’ tells the compiler that it is a decision control instruction<br />
(d) The condition following ‘if’ should be enclosed within a pair of parentheses<br />
(e) The ‘else’ statement will be executed if the condition specified is true.<br />
20. Which of the following security measures use human body parts such as retina or fingerprint<br />
to identify a unique individual?<br />
(a) Input Controls (b) Processing Controls (c)<br />
Output Controls<br />
(d) Procedural Controls (e) Biometric Controls.<br />
21. The departmental head wants to have a report that lists all those items where actual<br />
expenditures exceeded budget targets by at least 10 percent. This is an example of<br />
(a) External Report (b) Exception Report (c) Summary<br />
Report<br />
(d) Periodic Scheduled Report (e) Push Report.<br />
22. Which of the following (in communication network context) refers to the way in which the<br />
end points or stations of a network are linked together?<br />
(a) Data flow machine (b) Topology (c) Multi<br />
computer<br />
(d) Scalability (e) Resource sharing.<br />
23. The translation program that translates the entire source code into an object code and creates<br />
an object file, all in a single go, is called<br />
(a) Compiler (b) Linker (c) Complexer (d)<br />
Loader (e) Parser.<br />
24. Which of the following statements is not true about a Decision Support System (DSS)?<br />
(a) It involves an iterative analytical modeling process<br />
(b) It makes use of specialized databases<br />
(c) It is a computer based information system and does not take into account the decision<br />
makers’ own insights and judgements<br />
(d) It helps managers to explore possible alternatives<br />
(e) Focus and Decision-Web are examples of such a system.<br />
25. Which of the following is not correct regarding Central Office Exchange (Centrex)?<br />
(a) It is like a Private Branch Exchange (PBX)<br />
(b) The only difference between a PBX system and a Centrex is that the switching<br />
equipment is located in one of the telephone company’s “central exchanges” instead of<br />
on the premises of a business<br />
(c) It is typically used by large <strong>org</strong>anizations such as universities and hospitals<br />
(d) Only voice transmissions take place over such an exchange<br />
(e) An advantage of a Centrex system is the availability of large-scale networking systems<br />
that enable a business with several offices in the same metropolitan area.<br />
26. In the OSI reference model, which of the following layers splits packets into data frames<br />
which are transmitted sequentially by the sender and for which, the receiver transmits the<br />
<<br />
<<br />
<<br />
<<br />
<<br />
<<br />
<<br />
<<br />
<<br />
A<br />
><br />
A<br />
><br />
A<br />
><br />
A<br />
><br />
A<br />
><br />
A<br />
><br />
A<br />
><br />
A<br />
><br />
A<br />
>
acknowledgements?<br />
(a) The Physical Layer (b) The Data Link Layer (c) The Network<br />
Layer<br />
(d) The Transport Layer (e) The Application Layer.<br />
27. Which of the following build internetworks, in which networks using different topologies and<br />
protocols are interconnected?<br />
(a) Bridges (b) Routers (c) Hubs (d) Centers (e)<br />
Repeaters.<br />
28. Which of the following is a group of related data items of same data type that share a<br />
common name?<br />
(a) Variable (b) Structure (c) Array (d) Loop (e)<br />
Operator.<br />
29. The output of the following program is<br />
main()<br />
{<br />
int a = 5;<br />
do<br />
{<br />
printf(“%d\n”, ++a);<br />
a = -1;<br />
}while(a>0);<br />
}<br />
(a) 4 (b) 5 (c) 6 (d) Error (e)<br />
Garbage Value.<br />
30. Which of the following is not true about a Linked List in C?<br />
(a) Linked List is a list whose order is given by links from one item to the next<br />
(b) Each structure of a Linked List is called a node<br />
(c) Each node in a Linked List consists of two fields, one containing the item (value) and<br />
the other containing the address of the next item<br />
(d) The link is in the form of a pointer to another structure of the same type<br />
(e) A Linked List is a collection of structures ordered by their physical placement in the<br />
memory.<br />
END OF SECTION<br />
A<br />
< Answer ><br />
< Answer ><br />
< Answer ><br />
< Answer >
Section B : Caselets (50 Marks)<br />
• This section consists of questions with serial number 1 – 7.<br />
• Answer all questions.<br />
• Marks are indicated against each question.<br />
• Detailed explanations should form part of your answer.<br />
• Do not spend more than 110 - 120 minutes on Section B.<br />
Caselet 1<br />
Read the caselet carefully and answer the following questions:<br />
1. What types of data are involved in these two systems? What transaction level problems make this situation<br />
difficult to solve?<br />
(8 marks) < Answer ><br />
2. What are the similarities and differences between the GE and Whirlpool approaches?<br />
As a consumer, which of the two systems would you prefer to deal with?<br />
(10 marks) < Answer ><br />
3. What advantages were provided by expert system technology in case of Whirlpool?<br />
(4 marks) < Answer ><br />
Customer Service<br />
General Electric: Customer Help Line<br />
Since 1982, General Electric provided an Answer Center with a toll-free phone number for buyers of GE products. GE<br />
prides itself on having answers ready for almost all of the calls that come to the line. The Louisville, Kentucky,<br />
customer service center was then a part of $6 billion appliance division.<br />
When a call is received, the representative brings up a computerized list of symptoms and possible causes. Working<br />
through the checklist, the representative can often help the customer fix the problem on the spot. If the problem requires<br />
a technician, the caller is switched to the GE Service Center to schedule an appointment or get phone numbers of local<br />
service representatives.<br />
The system consists of a huge text database containing problems and responses to more than 1 million problems. The<br />
computerized version can retrieve answers in less than two seconds, and is considerably easier to use than the old repair<br />
manuals of the “old days”. As products are introduced or changed, the data is continually updated by four full-time<br />
programmers. An index allows representatives to search the database with a few key words.<br />
The center employed 225 people and handled 3.5 million service calls in 1991. Each representative handled more than<br />
100 calls a day. Twelve product specialists were on call for problems not recorded in the database. They also provided<br />
more detailed information for people who chose to fix more complicated problems themselves.<br />
By asking customers to call the helpline when they encountered a problem, GE gained immediate feedback on<br />
problems. The system kept customers happy by providing answers to many common questions. The service<br />
representatives also provided advice on how to best use the products and on how to care for them.<br />
An additional feature of the immediate feedback was that GE could spot potential problems. If GE suddenly saw a new<br />
problem encountered by many people, the service representatives were instructed to ask more detailed questions. It was<br />
much easier for engineers to spot problems and correlations with direct comments from the users.<br />
GE also used the system to help convince customers to buy new appliances. The system provided repair costs and<br />
pricing and feature data for new appliances. The system also recommended callers to dealers who participated in special<br />
promotional deals.<br />
After careful consideration, GE did not collect customer data. They learned that customers preferred to remain<br />
anonymous. GE’s manager of consumer communications and telemarketing, William Waers, noted that “We don’t take<br />
the caller’s name unless we have their permission, and we don’t use any automatic [phone] number identification.”
Although this information would undoubtedly be useful to the marketing department, GE determined that customers<br />
were more willing to use the system and ask “embarrassing” questions if they did not have to give their name.<br />
GE was contemplating changes to the system, such as graphics and a graphical user interface. However, they were<br />
cautious about making changes, because they needed to support 3.5 million calls a year. Annette Mattingly, information<br />
technology team leader, noted that although technology was important, the system was successful because of the<br />
employees. For service representatives, GE employed college-educated workers, provided good training for them and<br />
got a low turnover rate.<br />
Whirlpool: Customer Service<br />
In 1967, Whirlpool was one of the first companies in the United States to create a toll-free customer support line: the<br />
“Cool Line”. Gary Lockwood, the director of consumer assistance at Whirlpool’s North American Group, noted that<br />
“we’re constantly looking for technologies that improve service.” In 1992, the Whirlpool support line handled 1.6<br />
million calls from customers. The calls were handled by 100 customer representatives located in Knoxville, Tennessee.<br />
By 1995, they anticipated handling 9 million calls a year.<br />
To improve customer support, in 1988 Whirlpool surveyed customers to determine how they could provide “excellence<br />
in service”. From the problems identified in that survey, in 1991, Whirlpool built a new customer support system. The<br />
system incorporated state-of-the-art imaging technology and expert systems. It uses ISDN links between the Knoxville<br />
offices and the headquarters in Benton Harbour, Michigan.<br />
When a customer called the toll-free number, an AT&T ISDN PBX received the call, complete with the calling party’s<br />
area code and phone number. The phone number was routed to a special processor from Aristacom International. The<br />
processor scanned a DB2 database on one of Whirlpool’s IBM computers. If the number was found in the files, the<br />
associated customer information was retrieved and was routed with the call to a customer service representative. The<br />
system could automatically route the call to the service agent who last spoke with the customer.<br />
The networked personal computers on the agents’ desks were connected to 10 CD-ROM drives containing more than<br />
150,000 pages of images from 20 years’ of service and product manuals. Agents could call up text and detailed<br />
schematics in less than two seconds.<br />
When service agents received a call, they could use an expert system from Aion Corp, to help diagnose the problem.<br />
The stored images of the products and their schematics enabled the service agents to communicate with the consumer.<br />
By looking at the same images (one real, one in the computer), the agent could more easily identify problems and<br />
explain the problems.<br />
In 1992, Whirlpool Corp. won an award from the American Association for Artificial Intelligence for its AI system that<br />
helped customer service representatives troubleshoot problems. In addition to improved customer service and<br />
satisfaction, Whirlpool estimated that the system saved $4 to $6 million annually.<br />
Caselet 2<br />
Read the caselet carefully and answer the following questions:<br />
4. What are the American Express’s system inputs and outputs?<br />
(7 marks) < Answer ><br />
5. Why is the financial information compared at several steps to the information on the scanned receipts?<br />
What other competitive advantages might the new system provide for American Express?<br />
(7 marks) < Answer ><br />
American Express: Imaged Copies Increase Profitability<br />
From its earliest days, consumer credit has been presented as a prestige item reserved for a business’s best customers.<br />
The consumer had to “earn” the privilege of charging simply on the basis of his or her signature. Hotels and country<br />
clubs first introduced this concept. Fine department stores offered credit cards that were carried as an indication of the<br />
status that accompanies the opportunity to shop there. The American Express and Diners Club cards were the first to<br />
offer a credit card that was available across the country. This type of card was directed toward the business traveler who<br />
needed to keep the receipts so they could be turned in for reimbursement and tax purposes. Its annual fee and use<br />
mainly at more expensive restaurants, hotels and department stores limited its attractiveness to a fairly wealthy traveling<br />
public.<br />
The 1980s brought consumer credit to broader segments of the population. Visa and Mastercard offered easy,<br />
understandable credit to people with income levels beginning at $18,000, sometimes even without an annual fee. The<br />
late entry of the Sears Discover card into the market caused the card’s managers to present their card with no annual fee
and a 2 percent (0.2) bonus for each dollar that was charged on the card.<br />
Easy credit presented more options to the consumer. Previously American Express had advertised itself as the only card<br />
that the consumer needed to carry. In a period of a few years, consumers began to carry 4-5 credit cards at once. Visa,<br />
Mastercard and Discover had enlisted a large number of merchants to accept their card. In many cases, these were the<br />
same merchants who also accepted American Express cards. For the first time American Express found itself competing<br />
in a marketing campaign to convince consumers to pull its card rather than another out of their wallets or purses to<br />
charge purchases.<br />
One of the advantages that American Express presented for using its card was the physical return of the customer’s<br />
receipts. Customers had grown used to the convenience of balancing their receipts with those of American Express.<br />
With 2 million receipts arriving daily at its Fort Lauderdale and Phoenix locations, American Express realized that it<br />
needed a new system if it was going to be able to continue this service in an increasingly cost-competitive environment.<br />
The new system would have to meet several important goals. First, keyed data entry would have to be minimized due to<br />
the increasingly high cost of this process. Second, the entire receipt would have to be able to be stored and retrieved as a<br />
complete image to continue American Express’s tradition of returning a copy of the entire receipt. Third, the processing<br />
time between purchase and billing would have to be greatly reduced to minimize the high cost of capital. Fourth,<br />
accuracy had to be paramount because the consumer’s credit and trust in the company would be at stake. Finally, the<br />
process would have to be alterable in the future as new products and technologies were developed to be integrated into<br />
the system.<br />
The process of using the American Express card and receiving a bill involves a number of steps. When a card member<br />
makes a purchase, the card is “swiped” through a scanner and the amount of the purchase is entered on the keyboard.<br />
<strong>Information</strong> regarding the purchase, the purchaser and the retailer is immediately transmitted to the maintenance<br />
computer. Customers then sign slips for the purchases. These original slips are then submitted to American Express.<br />
When credit card slips are received from the merchant, they are scanned and the billing amounts are entered into the<br />
database. Images are sent to the system’s optical disks for storage. The imaged receipts are then balanced against the<br />
billing totals to make certain that there are no mistakes. Once everything is balanced, console operators prepare the bill<br />
by calling up the images on the screen and combining them with the actual bill.<br />
Future enhancements include the customer signing an electronic notepad. This will enable the entire imaged slip to be<br />
transmitted electronically, complete with signatures, to the billing centers. Research is also being done on character<br />
recognition technology. This will enable the dollar amounts on the slip to be read by the imager. This will eliminate the<br />
next most time-consuming step, that of keying in the dollar amounts by hand.<br />
The change to an imaged system presented some important challenges to the way American Express traditionally<br />
interacted with its customers. These were described by Cliff Dodd, senior vice-president of billing and payment<br />
services.<br />
“Getting a bill means you have to pay money, and that’s not a very pleasant experience to begin with. But if all of a<br />
sudden you change something that is very familiar and very important to a lot of people (because they use the card as a<br />
business tool), you really run the risk of alienating people. But we found that after six months of getting the Enhanced<br />
Country Club bill, 92 percent of our card members said they liked the new system better. That’s because it’s a neater<br />
package now, easier to read, understand, file and store.”<br />
The new system provides one obvious advantage. Without the receipts, the new bill provides more room in the envelope<br />
for marketing additional features of the card and other services. Another advantage occurs at the point of sale. The more<br />
information that the merchant keys into the computer system, the less will ultimately have to be entered by American<br />
Express personnel. This will improve the accuracy of the billing process and reduce American Express’s cost to<br />
maintain it.<br />
Caselet 3<br />
Read the caselet carefully and answer the following questions:<br />
6. What advantages does MetNet gain by consolidating its four main activities?<br />
(7 marks) < Answer ><br />
7. With a network of 2,000 desktops, what network management problems are likely to arise? How can they be<br />
handled cost effectively when people are scattered across 20 buildings?<br />
(7 marks) < Answer ><br />
An Art Network<br />
The New York Metropolitan Museum of Art is building a new network infrastructure named the MetNet. The new<br />
system is being constructed to better track the museum’s art objects. It is designed to consolidate the museum’s
financial operations and closely integrate its curatorial, merchandising and registration activities.<br />
The end goal of MetNet is to make art images and graphs available to nearly 2,000 desktops. Employees will be able to<br />
gather up-to-date relational data from a number of sources. This improvement will help employees make educated<br />
decisions regarding merchandising, exhibits, membership drives and endowments.<br />
Under the direction of Arthur Tisi, Chief <strong>Systems</strong> Officer at the museum, the network development team faces the<br />
challenge of integrating 20 contiguous buildings in Manhattan, several sites in other parts of the city and 20 retail<br />
locations across the country. The project is made more difficult by the fact that connections between the sites are not the<br />
same. Some are connected by dial-up lines; others through individual LANs; and still others are part of a separate<br />
mainframe-based system. <strong>Information</strong> systems officials describe the current network as a mishmash of disparate,<br />
incompatible systems that cannot be managed.<br />
When completed, MetNet will be based upon a System 5000 network hub from Bay Networks, Inc. This hub will<br />
connect over 40 Microsoft Windows NT and Novell Netware servers in 20 buildings. Internally, the museum is being<br />
rewired with fibre optic cable. T1 links will connect the remote sites with the central hub.<br />
The hubs and routers will be managed by Bay Networks’ Optivity, a network management protocol based application.<br />
The software distribution and inventory management of the desktops will be managed by the <strong>Systems</strong> Management<br />
Server. Central management will further reduce maintenance chores and costs.<br />
From a financial standpoint, the museum is testing server-based software in an effort to consolidate the financial<br />
applications and replace the mainframe-based system. Ultimately, the museum hopes to establish relational database<br />
that will consolidate the four primary operations of the museum: financial, curatorial, registration and merchandising.<br />
The new model will increase the ability of separate departments within the museum to work together. This will enable<br />
the 19 curatorial departments to exchange information with merchandising, retail operations and endowments areas.<br />
Other potential applications include a desktop imaging and a collection management program to track art objects.<br />
Internet is also being explored as a way to expand the audience for these art objects once they have been collected.<br />
END OF SECTION B<br />
Section C : Applied Theory (20 Marks)<br />
• This section consists of questions with serial number 8 - 9.<br />
• Answer all questions.<br />
• Marks are indicated against each question.<br />
• Do not spend more than 25 -30 minutes on section C.<br />
8. Management <strong>Information</strong> System can be defined as an integrated, user-machine system for providing information<br />
to support managerial, operational and decision-making functions in an <strong>org</strong>anization. It has certain characteristics<br />
that distinguish it from other information systems.<br />
In light of the above discussion, briefly explain the salient features of a Management <strong>Information</strong> System.<br />
(10 marks) < Answer ><br />
9. Executive <strong>Information</strong> <strong>Systems</strong> give top management immediate and easy access to information about a firm’s<br />
critical success factors, in accomplishing the <strong>org</strong>anization’s strategic objectives. Due to this benefit, Sumit Ltd. has<br />
decided to implement Executive <strong>Information</strong> System (EIS) in its <strong>org</strong>anization.<br />
What according to you are the pre-requisites of a successful EIS implementation? Also lay down the guidelines for<br />
preparing an effective EIS.<br />
END OF SECTION C<br />
END OF QUESTION PAPER<br />
(10 marks) < Answer >
Suggested Answers<br />
<strong>Information</strong> <strong>Technology</strong> & <strong>Systems</strong> (MB231) : October 2004<br />
Section A : Basic Concepts<br />
1. Answer : (a)<br />
Reason : A telecommunication processor supports data transmission and reception between the terminals and the<br />
computers. It performs a variety of control and support functions in a telecommunication network. e.g.<br />
a modem.<br />
Hence, from above discussion, we can infer that option (a) is correct.<br />
Option (b) is incorrect. Micro Computer is used by small <strong>org</strong>anizations, executives in large<br />
<strong>org</strong>anizations and even by professionals working out of their homes. In the past, IBM set the standards<br />
for Micro Computer hardware. Now, the distinction between a Micro Computer and a Personal<br />
Computer has got blurred because of the variety of features being provided by a Personal Computer<br />
nowadays. So, it is not applicable here.<br />
Option (c) is incorrect. Coaxial Cable consists of a sturdy copper or aluminum wire wrapped with<br />
spacers to insulate and protect it. This insulation minimizes the chance of interference from other<br />
signals, and distortion of the signals that the cable carries. So, it is not applicable here.<br />
Option (d) is incorrect. Fibre-optic Cable consists of one or more hair thin filaments of glass fibre<br />
wrapped in a protective jacket. So, it is not applicable here.<br />
Option (e) is incorrect. Web browser is a software application that allows for the browsing of the<br />
World Wide Web. So, it is not applicable here.<br />
2. Answer : (b)<br />
Reason : User Interface Design focuses on supporting the interactions between end-users and their computerbased<br />
applications. Designers concentrate on the design of attractive and efficient types of interfaces for<br />
user input and output, such as easy-to-use web pages.<br />
Hence, from above discussion, we can infer that option (b) is correct.<br />
Option (a) is incorrect. Computer Aided Design (CAD) is a set of specialized software and hardware<br />
that is used to design products directly on computer terminals. So, it is not applicable here.<br />
Option (c) is incorrect. Data Design focuses on designing of the structure of databases and files that<br />
would be used by the proposed information system. So, it is not applicable here.<br />
Option (d) is incorrect. Process Design focuses on the design of software resources, that is, the<br />
programs and procedures needed to create the proposed information system. So, it is not applicable<br />
here.<br />
Option (e) is incorrect. Data Design and Process Design are not applicable here.<br />
3. Answer : (b)<br />
Reason : Data Flow Machine consists of highly parallel computers with many functional units, all working on<br />
the same program. It has the least interprocessor distance of 0.1m.<br />
Hence, from above discussion, we can infer that option (b) is correct.<br />
Option (a) is incorrect. Multicomputer comes after Data Flow Machine and it communicates by<br />
sending messages over very short, very fast buses. It has an interprocessor distance of 1m. So, it is not<br />
applicable here.<br />
Option (c) is incorrect. Local Area Network (LAN) is a privately owned network within a single<br />
building or campus of up to a few kilometres in size. It has an interprocessor distance of 10 m to 1 km.<br />
So, it is not applicable here.<br />
Option (d) is incorrect. Metropolitan Area Network (MAN) is a bigger version of LAN and may cover<br />
a group of nearby corporate offices or a city and could be either private or public. It has an<br />
interprocessor distance of 1 km to 10 km. So, it is not applicable here.<br />
Option (e) is incorrect. Wide Area Network (WAN) would cover a large geographic area, generally a<br />
country or a continent. It has an interprocessor distance of 100 km to 1,000 km. So, it is not applicable<br />
here.<br />
4. Answer : (d)<br />
Reason : A “hanging indent” is not indented on the first line, but second and subsequent lines.<br />
< TOP ><br />
< TOP ><br />
< TOP ><br />
< TOP >
5.<br />
Hence, from above discussion, we can infer that option (d) is not true regarding paragraph formatting.<br />
Options (a), (b), (c) and (e) are all true regarding paragraph formatting.<br />
Answer : (d)<br />
Reason : Netware Directory Services (NDS) of Netware operating system provides both users and network<br />
administrators with a single integrated view of an entire network and the servers connected to it.<br />
Hence, from above discussion, we can infer that option (d) is correct.<br />
Option (a) is incorrect. A Redirector at the client workstation determines whether requests made by a<br />
user are for the local operating system or should be redirected to a server on the network. So, it is not<br />
applicable here.<br />
Option (b) is incorrect. Netware Core Protocol (NCP) includes file access, file locking, resource<br />
tracking and allocating, event notification and other services to workstations that request them. So, it is<br />
not applicable here.<br />
Option (c) is incorrect. Netware Loadable Module (NLM) includes services for name space support,<br />
internetworking, host connectivity, messaging services, communication services, etc. So, it is not<br />
applicable here.<br />
Option (e) is incorrect. Netware Directory Services (NDS) is applicable here.<br />
< TOP ><br />
6. Answer : (e)<br />
Reason : The default initial value is zero for External and Static storage classes in C language.<br />
Hence, from above discussion, we can infer that option (e) is correct.<br />
Option (a) is incorrect. The default initial value for Automatic storage class is garbage value. So, it is<br />
not applicable here.<br />
Option (b) is incorrect. Both External and Static storage classes are applicable here.<br />
Option (c) is incorrect. Both External and Static storage classes are applicable here.<br />
Option (d) is incorrect. The default initial value for Register storage class is garbage value. So, it is not<br />
applicable here.<br />
< TOP ><br />
7. Answer : (c)<br />
Reason : Program Design Language is a tool that is used for planning program logic and makes use of "imitation<br />
code" that imitates real programming language.<br />
Hence, from above discussion, we can infer that option (c) is correct.<br />
Option (a) is incorrect. A flowchart is a pictorial representation of a program. So, it is not applicable<br />
here.<br />
Option (b) is incorrect. Decision Table is used to define clearly and concisely the statement of a<br />
problem in tabular form. So, it is not applicable here.<br />
Option (d) is incorrect. Compiler is a translation program that translates the entire source code into<br />
object code and creates an object file. So, it is not applicable here.<br />
Option (e) is incorrect. Interpreter translates one line of code at a time and executes the translated<br />
information. So, it is not applicable here.<br />
< TOP ><br />
8. Answer : (c)<br />
Reason : Data Link Layer of OSI Reference Model is responsible for establishing an error-free communications<br />
path between computers over the physical channel. It performs checksum Cyclic Redundancy Check<br />
(CRC) to detect and correct errors in the transmission of data.<br />
Hence, from above discussion, we can infer that option (c) is correct.<br />
Option (a) is incorrect. Transport Layer provides control standards for a communication session for<br />
enabling two processes at both ends to exchange data reliably and sequentially. So, it is not applicable<br />
here.<br />
Option (b) is incorrect. Network Layer sets up a logical path between the source and the destination<br />
computers for the network. So, it is not applicable here.<br />
Option (d) is incorrect. Session Layer provides means for establishing, maintaining and terminating a<br />
dialogue or session between two end users. So, it is not applicable here.<br />
Option (e) is incorrect. Application Layer provides services that directly support the end user of the<br />
network. So, it is not applicable here.<br />
< TOP ><br />
9. Answer : (e) < TOP >
Reason : No special symbol other than an underscore is allowed in defining variable names in C language.<br />
Hence, from above discussion, we can infer that option (e) is not correct with respect to variables in C<br />
language.<br />
Options (a), (b), (c) and (d) are all correct with respect to variables in C language.<br />
10. Answer : (b)<br />
Reason : Computer-Aided Software Engineering usually involves software packages that assist the software<br />
developers to perform many of the activities of the systems development cycle.<br />
Hence, from above discussion, we can infer that option (b) is correct.<br />
Option (a) is incorrect. Executive <strong>Information</strong> System combines many of the features of Management<br />
<strong>Information</strong> System and Decision Support System. It gives top management immediate and easy access<br />
to information about a firm’s Critical Success Factors (CSF’s), in accomplishing its strategic<br />
objectives. So, it is not applicable here.<br />
Option (c) is incorrect. Office <strong>Information</strong> System includes workstation-based tools for document<br />
creation and document retrieval, tools for maintaining appointment calendars, and so on. So, it is not<br />
applicable here.<br />
Option (d) is incorrect. Multimedia Database contains images, spatial data, audio data, video data and<br />
the like. So, it is not applicable here.<br />
Option (e) is incorrect. Hypertext Database is enriched with lines that point to other documents. So, it is<br />
not applicable here.<br />
11. Answer : (a)<br />
Reason : In What-if Analysis, an end user makes changes to variables or relationships among them, and<br />
observes the resulting changes in the values of other variables.<br />
Hence, from above discussion, we can infer that option (a) is correct.<br />
Option (b) is incorrect. Sensitivity Analysis is a special case of What-if Analysis. Typically, the value of<br />
only one variable is changed, but many such iterations are carried out, and the resulting changes are<br />
observed. So, it is not applicable here.<br />
Option (c) is incorrect. Goal-seeking Analysis is the reverse of What-if Analysis and Sensitivity<br />
Analysis. Instead of observing how changes in a variable affect other variables, Goal-seeking Analysis<br />
sets a target value (the goal) for a variable and then repeatedly changes other values until the target<br />
value is achieved. So, it is not applicable here.<br />
Option (d) is incorrect. Optimization Analysis is a more complex extension of Goal-seeking Analysis.<br />
It attempts to find the optimum value for one or more target variables, given certain constraints. So, it is<br />
not applicable here.<br />
Option (e) is incorrect. Cost-benefit Analysis is concerned with whether expected savings, increased<br />
revenue, increased profits, reductions in required investment and other types of benefits will exceed the<br />
costs of developing and operating a proposed system. So, it is not applicable here.<br />
12. Answer : (b)<br />
Reason : <strong>Systems</strong> Analysis stage of <strong>Systems</strong> Development Life Cycle (SDLC) analyses the information needs of<br />
end users, <strong>org</strong>anizational environment and any system presently used. It develops the functional<br />
requirements of a system, that can meet the needs of end users.<br />
Hence, from above discussion, we can infer that option (b) is correct.<br />
Option (a) is incorrect. <strong>Systems</strong> Investigation determines whether a business problem or opportunity<br />
exists. So, it is not applicable here.<br />
Option (c) is incorrect. <strong>Systems</strong> Design develops specifications for hardware, software, people,<br />
network and data resources. So, it is not applicable here.<br />
Option (d) is incorrect. <strong>Systems</strong> Implementation tests the system and trains people to operate and use it.<br />
So, it is not applicable here.<br />
Option (e) is incorrect. <strong>Systems</strong> Maintenance uses a post-implementation review process to monitor,<br />
evaluate and modify the system as needed. So, it is not applicable here.<br />
13. Answer : (c)<br />
Reason : Strategic information systems planning is an important component of total <strong>org</strong>anizational planning and<br />
focuses on the activities and outputs of strategic business planning.<br />
Strategic information systems planning is business driven and not technology driven. IT strategies are<br />
developed based on strategic business opportunities.<br />
< TOP ><br />
< TOP ><br />
< TOP ><br />
< TOP >
Hence, from above discussion, we can infer that option (c) is false with respect to strategic<br />
information systems planning.<br />
Options (a), (b), (d) and (e) are all true with respect to strategic information systems planning.<br />
14. Answer : (b)<br />
Reason : Workflow System helps users to collaborate with each other to accomplish and manage structural work<br />
tasks within a knowledge-based business process.<br />
Hence, from above discussion, we can infer that option (b) is correct.<br />
Option (a) is incorrect. Electronic Meeting System facilitates group decision-making activities that<br />
take place in a computer-based decision-room setting. So, it is not applicable here.<br />
Option (c) is incorrect. Teleconferencing is an important group support facility, in which sessions are<br />
held in real time where major participants are televised, while participants from remote areas may take<br />
part with voice input of questions and responses. So, it is not applicable here.<br />
Option (d) is incorrect. Data Conferencing is a method where a Groupware Package connects two or<br />
more PCs over the Internet or Intranets, so that a team can share, mark up and revise a white board of<br />
drawings, documents and other material displayed on their screens. So, it is not applicable here.<br />
Option (e) is incorrect. White Boarding is another name of Data Conferencing. So, it is not applicable<br />
here.<br />
15. Answer : (d)<br />
Reason : Object-Based Logical Model (OBLM) is used in describing data at the logical level and at the view<br />
level. Under OBLM, Entity-Relationship (E-R) Model falls. E-R Model is based on a perception of a<br />
real world that consists of a collection of basic objects called entities and of relationships (association)<br />
among these objects.<br />
Hence, from above discussion, we can infer that option (d) is correct.<br />
Option (a) is incorrect. The database in a Relational Model is generally a two-dimensional table. So, it<br />
is not applicable here.<br />
Option (b) is incorrect. The records in Network Model are <strong>org</strong>anized as collections of arbitrary graphs.<br />
So, it is not applicable here.<br />
Option (c) is incorrect. The records in Hierarchical Model are <strong>org</strong>anized as collections of trees. So, it<br />
is not applicable here.<br />
Option (e) is incorrect. Physical Model is used to describe data at the lowest level. So, it is not<br />
applicable here.<br />
16. Answer : (c)<br />
Reason : Cache Memory is used to store frequently accessed programs and data. It is a special, high speed<br />
memory, which is used to increase the speed of processing by making current data and programs<br />
available to the CPU at a rapid rate. It has the fastest access speed compared to other memories/storage<br />
devices.<br />
Hence, from above discussion, we can infer that option (c) is correct.<br />
Option (a) is incorrect. RAM stands for Random Access Memory. It is also called main memory or<br />
primary memory. It is called RAM, as it is possible to randomly select and use any location of this<br />
memory to directly store and retrieve data and instructions. It has fast access speed, but is not as fast as<br />
Cache Memory. So, it is not applicable here.<br />
Option (b) is incorrect. ROM stands for Read Only Memory. In this memory, information is<br />
permanently stored. Data can be read from it, and not written to it. It has slow access speed. So, it is not<br />
applicable here.<br />
Option (d) is incorrect. Hard Disk stores the computer's operating system and applications, and<br />
provides space for the user's data. It has medium access speed. So, it is not applicable here.<br />
Option (e) is incorrect. Backup tape is a sequential storage device. The computer has to go through a<br />
fixed sequence of stored items to access the needed file, say, a desired song. Hence, it has a very slow<br />
access speed. So, it is not applicable here.<br />
17. Answer : (e)<br />
Reason : A flowchart is a pictorial representation of a program. In spite of the many advantages of a flowchart, it<br />
has certain limitations too. One of these is that there are no specific standards for determining the<br />
amount of detail that should be included in a flowchart.<br />
Hence, from above discussion, we can infer that option (e) is not an advantage of a flowchart.<br />
< TOP ><br />
< TOP ><br />
< TOP ><br />
< TOP >
Options (a), (b), (c) and (d) are all advantages of a flowchart.<br />
18. Answer : (d)<br />
Reason : Internet Paging, also known as “Buddy List” software, runs on the background of the user's computer,<br />
letting him/her know when his friends or coworkers (only those who are registered) are online.<br />
Hence, from above discussion, we can infer that option (d) is correct.<br />
Option (a) is incorrect. File Transfer Protocol is an Internet Standard developed to exchange files. So,<br />
it is not applicable here.<br />
Option (b) is incorrect. Internet Telephony is the mechanism of carrying out telephonic conversations<br />
over the Internet. So, it is not applicable here.<br />
Option (c) is incorrect. Internet Fax is the mechanism of sending faxes through computers connected<br />
over the Internet. So, it is not applicable here.<br />
Option (e) is incorrect. Usenet is a system where messages about any subject can be posted and other<br />
people on the Internet can reply to them. So, it is not applicable here.<br />
19. Answer : (e)<br />
Reason : The ‘else’ statement will be executed if the condition specified is false.<br />
Hence, from above discussion, we can infer that option (e) is not correct regarding decision-making<br />
statements in C programming language.<br />
Options (a), (b), (c) and (d) are all correct regarding decision-making statements in C programming<br />
language.<br />
20. Answer : (e)<br />
Reason : Biometric Controls are security measures that use human body parts such as retina or fingerprint to<br />
identify a unique individual.<br />
Hence, from above discussion, we can infer that option (e) is correct.<br />
Option (a) is incorrect. Input Controls are usually set in the form of login passwords and other security<br />
codes, formatted data entry success, appropriate error signals etc. So, they are not applicable here.<br />
Option (b) is incorrect. Processing Controls are developed to identify errors in arithmetic calculation<br />
and logical operations. So, they are not applicable here.<br />
Option (c) is incorrect. Output Controls are developed to ensure that information products are correct<br />
and complete. So, they are not applicable here.<br />
Option (d) is incorrect. Procedural Controls are methods that specify how an <strong>org</strong>anization’s computer<br />
and network resources should be operated for maximum security. So, they are not applicable here.<br />
21. Answer : (b)<br />
Reason : Exception Report is generated only in exceptional situations. It lists items that fall outside the<br />
prescribed limits. e.g., a report that lists all those items where actual expenditures exceeded budget<br />
targets by at least 10 percent.<br />
Hence, from above discussion, we can infer that option (b) is correct.<br />
Option (a) is incorrect. External Report is prepared primarily for readers outside the company. e.g.,<br />
drafts of income statements and balance sheets. So, it is not applicable here.<br />
Option (c) is incorrect. Summary Report summarizes detailed information into convenient, compact<br />
formats. So, it is not applicable here.<br />
Option (d) is incorrect. Periodic Scheduled Report uses a pre-specified format, designed to provide<br />
managers with information on a regular basis. So, it is not applicable here.<br />
Option (e) is incorrect. Push Report is pushed to a manager’s workstation through Intranet in the form<br />
of a web cast. So, it is not applicable here.<br />
22. Answer : (b)<br />
Reason : Topology (in communication network context) refers to the way in which the end points or stations of a<br />
network are linked together.<br />
(a) These are highly parallel computers with many functional units all working on the same program.<br />
(c) Multicomputers communicated by sending messages over very short, very fast buses.<br />
(d) This is the ability to increase system performance gradually as the work load grows by adding<br />
more processors.<br />
(e) Management uses resource sharing to make all programs, equipment, and data available to<br />
anyone on the network without regard to physical location of the resource and the user.<br />
< TOP ><br />
< TOP ><br />
< TOP ><br />
< TOP ><br />
< TOP >
23. Answer : (a)<br />
Reason : A language translator is one which converts a source code into object code. Mainly, there are two types<br />
of translators called compilers and interpreters. Compiler is a translation program that translates the<br />
entire source code into object code and creates an object file.<br />
(b) An assembler and a liner is a program that transforms the object code into an executable program<br />
that runs on a certain type of computer.<br />
(c) Complexer is not a translation program that translates the entire source code into object code<br />
creates an object file in a single go.<br />
(d) Operator is not a translation program that translates the entire source code into object code<br />
creates an object file in a single go.<br />
(e) An interpreter does not produce an object code. It translates one line of source code at a time and<br />
executes the translated instruction.<br />
24. Answer : (c)<br />
Reason : A Decision Support System (DSS) is a type of management support system which provides direct<br />
support to the decision-makers, with the help of ‘what-if’ analysis, ‘optimization models’ etc. It makes<br />
use of analytical models, specialized databases, and indeed, the decision-maker’s own insights and<br />
judgements, to support the making of structured and unstructured decisions by individual managers.<br />
Hence, from above discussion, we can infer that option (c) is not true about a Decision Support System<br />
(DSS).<br />
Option (a) is true because a Decision Support System (DSS) involves an iterative analytical modeling<br />
process.<br />
Option (b) is true because it makes use of specialized databases.<br />
Option (d) is true because it helps managers to explore possible alternatives.<br />
Option (e) is true because Focus and Decision-Web are examples of such a system.<br />
25. Answer : (d)<br />
Reason : Central Office Exchange (Centrex) is like a Private Branch Exchange (PBX), except that the switching<br />
equipment is located in one of the telephone company’s “central exchanges” instead of on the premises<br />
of a business. It incorporates data-over-voice technology to use telephones for simultaneous voice and<br />
data transmissions.<br />
Hence, from above discussion, we can infer that option (d) is not correct regarding Central Office<br />
Exchange (Centrex).<br />
Options (a), (b), (c) and (e) are all correct regarding Central Office Exchange (Centrex).<br />
26. Answer : (b)<br />
Reason : The OSI model is based on a proposal developed by the international standard <strong>org</strong>anization (ISO). The<br />
OSI model has seven layers. The data link layer splits packets into data frames which transmitted<br />
sequentially by the sender and the receiver transmits the acknowledgements.<br />
(a) This layer covers issues related to the physical medium between the devices. It also defines the<br />
electrical and mechanical aspects of interfacing to a physical medium for transmitting data.<br />
(c) The network layer set up a logical path between the source and the destination computers of the<br />
network. The message to be transmitted is first fragmented into packets at this layer after which it<br />
performs sequencing and error control of these packets.<br />
(d) This layer splits the message into smaller units and appends a header to each unit. It also controls<br />
message flow between the sender and the receiver so that a fast sender doesnot overwhelm a slow<br />
receiver with data.<br />
(e) This layer is a user oriented one, which provides services that directly support the end user of the<br />
network. It offers services like file transfers, remote file access, data base management etc.<br />
27. Answer : (b)<br />
Reason : Routers build Internetworks, in which networks that use different topologies and protocols are<br />
interconnected.<br />
(a) A bridge is used to increase the distance of a network and to add more stations.<br />
(c) HWB are used to build structured cabling systems<br />
(d) Centres does not build Internetworks, in which networks that use different topologies and<br />
protocols are interconnected<br />
< TOP ><br />
< TOP ><br />
< TOP ><br />
< TOP ><br />
< TOP >
(e) Repeater generates the electrical signal and doubles the allowable length of the cable.<br />
28. Answer : (c)<br />
Reason : An Array is a group of related data items that share a common name.<br />
(a) Variables are storage classes in C. Different type of storage classes are Automatic variables,<br />
External variables, Static variable and Register variables.<br />
(b) A structure is a method for packing data of different types. It is convenient tool for handling a<br />
group of logically related data items.<br />
(d) An array can be defined as a group of related data items that share a common name.<br />
(e) A decision control/instruction can be implemented in C by using the loop.<br />
29. Answer : (c)<br />
Reason : a = 5<br />
‘do loop’ is executed.<br />
+ + a = 6<br />
6 is printed.<br />
a = – 1<br />
Now a < 0. Therefore, ‘do loop’ is not repeated.<br />
The program ends.<br />
Hence the output of the given program is 6.<br />
30. Answer : (e)<br />
Reason : A Linked List in C is a collection of structures ordered by logical links that are stored as part of the<br />
data in the structure itself.<br />
< TOP ><br />
< TOP ><br />
< TOP >
Section B : Caselets<br />
1. The types of data involved in these two systems are as follows:<br />
(i) Computerized list of symptoms and possible causes of problems that may be encountered by customers.<br />
(ii) Customer complaints regarding GE products and Whirlpool products.<br />
(iii) Problems encountered by customers while using the products.<br />
(iv) Repair costs and pricing and feature data for new appliances in case of GE.<br />
(v) <strong>Information</strong> about dealers who participated in special promotional deals.<br />
(vi) <strong>Information</strong> regarding calling customers in case of Whirlpool and initially in case of GE.<br />
The transaction level here is operational level. Efficiency in data processing is of utmost importance in this<br />
situation. Accuracy in determining the customer problems and speed of solving the same and responding to<br />
customers are important factors of success in this case.<br />
The following problems make this situation difficult to solve:<br />
(i) A huge text database containing problems and responses to more than 1 million problems in case of GE and<br />
10 CD-ROM drives containing more than 150,000 pages of images from 20 years’ of service and product<br />
manuals in case of Whirlpool.<br />
(ii) Supporting 3.5 million calls a year by GE and 1.6 million calls by Whirlpool.<br />
(iii) Anticipation by Whirlpool of handling 9 million calls a year by 1995.<br />
< TOP ><br />
2.<br />
Similarities in approaches<br />
GE Whirlpool<br />
(i) Toll-free phone number.<br />
(i) Toll-free phone number.<br />
(ii) Huge database of information. (ii) Huge database of information.<br />
(iii)Use of customer service<br />
(iii)Use of customer service<br />
representatives.<br />
representatives.<br />
(iv) Computerized handling of data. (iv) Computerized handling of data.<br />
Differences in approaches<br />
GE Whirlpool<br />
(i) Absence of imaging technology. GE (i) Presence of imaging technology.<br />
was contemplating incorporating<br />
graphics and using a graphical user<br />
interface in the future, but hadn’t yet<br />
adopted them.<br />
(ii) Absence of expert system.<br />
(ii) Presence of expert system.<br />
As a consumer, I would prefer to deal with Whirlpool system as it has got an inbuilt expert system. An expert<br />
system is a knowledge-based information system that uses knowledge about a specific area to act as expert<br />
consultant to users. Such a system usually makes use of Artificial Intelligence (AI) whose major thrust is<br />
development of computer functions associated with human intelligence, such as reasoning, learning and problem<br />
solving.<br />
In case of Whirlpool, an expert system from Aion Corp was used to help diagnose the problems, which speeded up<br />
the process and brought in more efficiency.<br />
< TOP ><br />
3. The advantages provided by expert system technology in case of Whirlpool were as follows:<br />
(i) It helped service representatives diagnose the problems and accordingly troubleshoot them, thus speeding<br />
up the process and bringing in more efficiency.<br />
(ii) It improved customer service and satisfaction.<br />
(iii) It saved Whirlpool $4 to $6 million annually.<br />
(iv) It won Whirlpool an award from the American Association for Artificial Intelligence for its AI system.<br />
< TOP >
4. The American Express’s system inputs are as follows:<br />
(i) <strong>Information</strong> regarding type and amount of purchase.<br />
(ii) <strong>Information</strong> regarding the purchaser.<br />
(iii) <strong>Information</strong> regarding the retailer.<br />
(iv) Storage of entire receipt as a complete image.<br />
(v) Customer signatures.<br />
The American Express’s system outputs are as follows:<br />
(i) Customer’s receipts.<br />
(ii) Customer’s bills, like Enhanced Country Club bill and others in case of the new system.<br />
< TOP ><br />
5. The accuracy in data processing is very important in a transaction processing system, like that of American<br />
Express. So, the financial information is compared at several steps to the information on the scanned receipts to<br />
ensure that no mistakes are committed.<br />
The other competitive advantages that the new system might provide for American Express are as under:<br />
(i) Increased customer satisfaction because of a more convenient bill, which was easier to read, understand, file<br />
and store.<br />
(ii) Enhanced sales because of increased customer satisfaction.<br />
(iii) Providing convenient bills to customers might be used as the USP of American Express.<br />
(iv) A paradigm shift in the way of doing credit-card business by introducing the bill concept, in which customers<br />
were required to pay money.<br />
(v) Less transaction processing time.<br />
< TOP ><br />
6. The advantages that MetNet gains by consolidating its four main activities are as follows:<br />
(i) Greater integration across the separate departments within the museum because of sharing a common<br />
database.<br />
(ii) Enabling the 19 curatorial departments to exchange information with merchandising, retail operations and<br />
endowments areas.<br />
(iii) Gathering of up-to-date relational data from a number of sources by the employees.<br />
(iv) Helping employees to make informed and quick decisions regarding merchandising, exhibits, membership<br />
drives and endowments.<br />
(v) Doing away with data redundancy.<br />
(vi) Enhanced data security.<br />
(vii) Easier updation and maintenance of data.<br />
< TOP ><br />
7. With a network of 2,000 desktops, the network management problems that are likely to arise are as follows:<br />
(i) Excess data traffic.<br />
(ii) Loss of data during transmission.<br />
(iii) Difficulty in maintaining data integrity.<br />
(iv) Chances of data inconsistency.<br />
(v) Increased chances of virus attacks.<br />
They can be handled cost effectively when people are scattered across 20 buildings, in the following ways:<br />
(i) Convert the entire system into a client-server setup.<br />
(ii) Connect all the 20 buildings on a single LAN or WAN.<br />
(iii) Do away with the old mainframe-based system.<br />
(iv) The right step was taken in rewiring the museum with fibre optic cable.<br />
< TOP ><br />
Section C: Applied Theory<br />
8. The salient features of a Management <strong>Information</strong> System are as follows:<br />
Management oriented<br />
MIS is developed to increase <strong>org</strong>anizational efficiency. Therefore, they need to focus on the requirements of the
managers and the overall objective of the <strong>org</strong>anization.<br />
Management directed<br />
Management information systems can be costly and time consuming. Hence, it is important that the top<br />
management understand their importance in increasing <strong>org</strong>anizational efficiency which would lead to quicker<br />
implementation.<br />
Integrated systems<br />
MIS is based on five factors. viz., men, money, material, machines and methods. An MIS is a combination of<br />
subsystems. Hence, it is important that MIS be viewed as an integrated system that is a combination of functional<br />
and activity subsystems.<br />
Common data flow<br />
Activities such as data gathering, storage, retrieval and data capturing are performed only once and data is<br />
collected from the original source. By establishing a common data flow, the system tries to minimize data<br />
processing and maximize output generation. Such integration would help in building an effective management<br />
information system.<br />
Heavy planning element<br />
The implementation of an MIS requires meticulous planning and design and implementation. The system should<br />
be designed such that there is perfect synchronization between hardware, software, data processing, information<br />
presentation and feedback.<br />
Subsystem concept<br />
MIS consists of several subsystems that interact with each other and perform specialized tasks that may be<br />
integrated into the total system. For convenience the <strong>org</strong>anization can have a hierarchy of subsystems that clearly<br />
represents the relationship between subsystems and their relationship with the total system.<br />
Common database<br />
Common database acts as an integrator between the different functional subsystems in the <strong>org</strong>anization. Common<br />
database permits access to different tables by different functional subsystems. Since data requirements are<br />
different for different levels of management, the system supports one or more databases.<br />
Flexibility<br />
MIS is flexible and can be modified easily. Moreover, computerization is also simple because of the structure and<br />
comprehensive nature of the system.<br />
< TOP ><br />
9. The pre-requisites of a successful EIS implementation are the following:<br />
Find an appropriate project leader<br />
The EIS systems are successful when at least one person in the senior management agrees with the project leader.<br />
It is not necessary for the project-head to understand the technicalities of the system. But it is vital for him to<br />
understand management requirements, their work styles and current channels of obtaining information.<br />
Deliver a simple prototype quickly<br />
The quality of an EIS is judged by its user-friendliness and the relevance of the information presented. A simple<br />
prototype should be prepared and delivered quickly providing information on key issues. An effective EIS is one<br />
that is designed on the basis of executive requirements.<br />
Involve the IS Department<br />
Most of the managers make the mistake of not consulting the IS department when using expert systems. This may<br />
hamper the effectiveness of decisions since managers may have omitted some vital and relevant information. The<br />
IS personnel know best where to find relevant information. Hence, it’s necessary that the managers take their help<br />
while making plans and decisions.<br />
The guidelines for preparing an effective EIS are as under:<br />
• The information included in the EIS should be easy to collect and understand. Moreover, it should be<br />
available readily since managers cannot waste time searching for information.<br />
• The information represented in the EIS should reflect <strong>org</strong>anizational objectives in areas of productivity,<br />
resource management, quality and customer service.<br />
• The variables should be free from bias. All executives should be given due credit for their contribution.<br />
• EIS should foster team-work and cooperation while creating healthy competition to achieve <strong>org</strong>anizational<br />
goals.<br />
• The information stored in EIS should be available to everyone in the <strong>org</strong>anization.<br />
• The system should be flexible so that changes can be incorporated easily.<br />
< TOP OF THE DOCUMENT ><br />
< TOP >