Paper Presentation Schedule - hicss
Paper Presentation Schedule - hicss
Paper Presentation Schedule - hicss
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
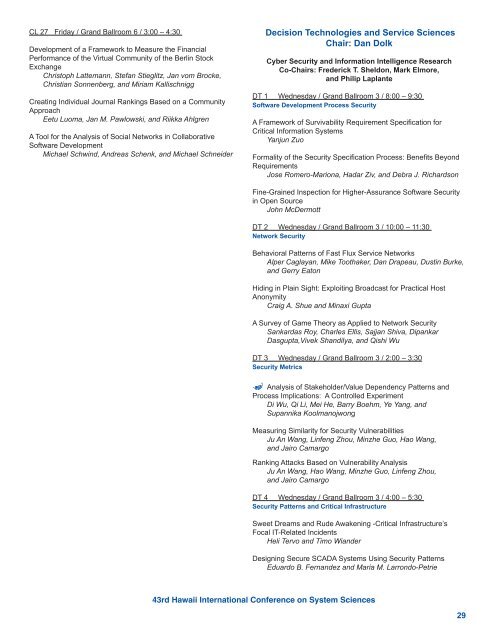
CL 27 Friday / Grand Ballroom 6 / 3:00 – 4:30<br />
Development of a Framework to Measure the Financial<br />
Performance of the Virtual Community of the Berlin Stock<br />
Exchange<br />
Christoph Lattemann, Stefan Stieglitz, Jan vom Brocke,<br />
Christian Sonnenberg, and Miriam Kallischnigg<br />
Creating Individual Journal Rankings Based on a Community<br />
Approach<br />
Eetu Luoma, Jan M. Pawlowski, and Riikka Ahlgren<br />
A Tool for the Analysis of Social Networks in Collaborative<br />
Software Development<br />
Michael Schwind, Andreas Schenk, and Michael Schneider<br />
Decision Technologies and Service Sciences<br />
Chair: Dan Dolk<br />
Cyber Security and Information Intelligence Research<br />
Co-Chairs: Frederick T. Sheldon, Mark Elmore,<br />
and Philip Laplante<br />
DT 1 Wednesday / Grand Ballroom 3 / 8:00 – 9:30<br />
Software Development Process Security<br />
A Framework of Survivability Requirement Specification for<br />
Critical Information Systems<br />
Yanjun Zuo<br />
Formality of the Security Specification Process: Benefits Beyond<br />
Requirements<br />
Jose Romero-Mariona, Hadar Ziv, and Debra J. Richardson<br />
Fine-Grained Inspection for Higher-Assurance Software Security<br />
in Open Source<br />
John McDermott<br />
DT 2 Wednesday / Grand Ballroom 3 / 10:00 – 11:30<br />
Network Security<br />
Behavioral Patterns of Fast Flux Service Networks<br />
Alper Caglayan, Mike Toothaker, Dan Drapeau, Dustin Burke,<br />
and Gerry Eaton<br />
Hiding in Plain Sight: Exploiting Broadcast for Practical Host<br />
Anonymity<br />
Craig A. Shue and Minaxi Gupta<br />
A Survey of Game Theory as Applied to Network Security<br />
Sankardas Roy, Charles Ellis, Sajjan Shiva, Dipankar<br />
Dasgupta,Vivek Shandilya, and Qishi Wu<br />
DT 3 Wednesday / Grand Ballroom 3 / 2:00 – 3:30<br />
Security Metrics<br />
% Analysis of Stakeholder/Value Dependency Patterns and<br />
Process Implications: A Controlled Experiment<br />
Di Wu, Qi Li, Mei He, Barry Boehm, Ye Yang, and<br />
Supannika Koolmanojwong<br />
Measuring Similarity for Security Vulnerabilities<br />
Ju An Wang, Linfeng Zhou, Minzhe Guo, Hao Wang,<br />
and Jairo Camargo<br />
Ranking Attacks Based on Vulnerability Analysis<br />
Ju An Wang, Hao Wang, Minzhe Guo, Linfeng Zhou,<br />
and Jairo Camargo<br />
DT 4 Wednesday / Grand Ballroom 3 / 4:00 – 5:30<br />
Security Patterns and Critical Infrastructure<br />
Sweet Dreams and Rude Awakening -Critical Infrastructure’s<br />
Focal IT-Related Incidents<br />
Heli Tervo and Timo Wiander<br />
Designing Secure SCADA Systems Using Security Patterns<br />
Eduardo B. Fernandez and Maria M. Larrondo-Petrie<br />
43rd Hawaii International Conference on System Sciences<br />
29