An Ontology for Digital Forensics in IT Security Incidents - OPUS
An Ontology for Digital Forensics in IT Security Incidents - OPUS
An Ontology for Digital Forensics in IT Security Incidents - OPUS
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
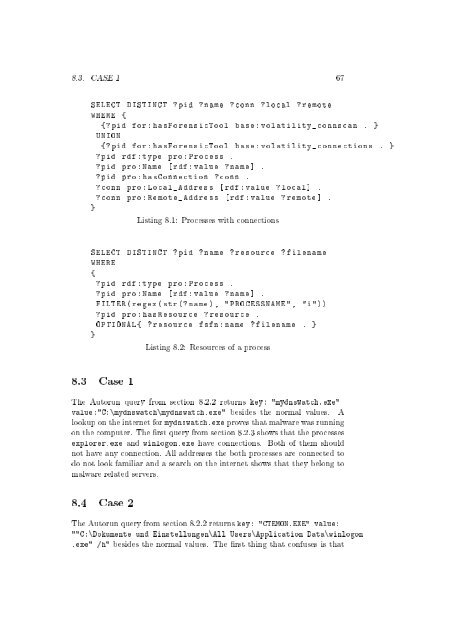
8.3. CASE 1 67<br />
SELECT DISTINCT ? pid ? name ? conn ? local ? remote<br />
WHERE {<br />
{? pid <strong>for</strong> : hasForensicTool base : volatility_connscan . }<br />
UNION<br />
{? pid <strong>for</strong> : hasForensicTool base : volatility_connections . }<br />
? pid rdf : type pro : Process .<br />
? pid pro : Name [ rdf : value ? name ] .<br />
? pid pro : hasConnection ? conn .<br />
? conn pro : Local_Address [ rdf : value ? local ] .<br />
? conn pro : Remote_Address [ rdf : value ? remote ] .<br />
}<br />
List<strong>in</strong>g 8.1: Processes with connections<br />
SELECT DISTINCT ? pid ? name ? resource ? filename<br />
WHERE<br />
{<br />
? pid rdf : type pro : Process .<br />
? pid pro : Name [ rdf : value ? name ] .<br />
FILTER ( regex ( str (? name ), " PROCESSNAME ", "i "))<br />
? pid pro : hasResource ? resource .<br />
OPTIONAL { ? resource fsfn : name ? filename . }<br />
}<br />
List<strong>in</strong>g 8.2: Resources of a process<br />
8.3 Case 1<br />
The Autorun query from section 8.2.2 returns key: "mydnswatch.exe"<br />
value:"C:\mydnswatch\mydnswatch.exe" besides the normal values. A<br />
lookup on the <strong>in</strong>ternet <strong>for</strong> mydnswatch.exe proves that malware was runn<strong>in</strong>g<br />
on the computer. The rst query from section 8.2.3 shows that the processes<br />
explorer.exe and w<strong>in</strong>logon.exe have connections. Both of them should<br />
not have any connection. All addresses the both processes are connected to<br />
do not look familiar and a search on the <strong>in</strong>ternet shows that they belong to<br />
malware related servers.<br />
8.4 Case 2<br />
The Autorun query from section 8.2.2 returns key: "CTEMON.EXE" value:<br />
""C:\Dokumente und E<strong>in</strong>stellungen\All Users\Application Data\w<strong>in</strong>logon<br />
.exe" /h" besides the normal values. The rst th<strong>in</strong>g that confuses is that