Presentation - ICMCC
Presentation - ICMCC
Presentation - ICMCC
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
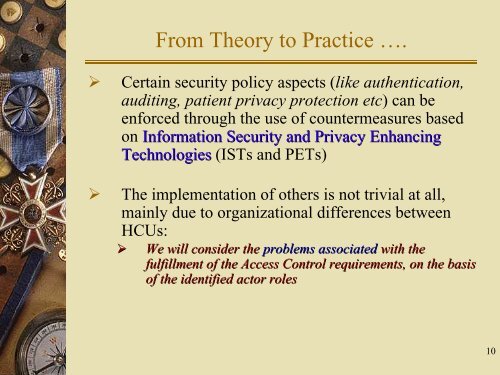
From Theory to Practice ….<br />
‣ Certain security policy aspects (like authentication,<br />
auditing, patient privacy protection etc) can be<br />
enforced through the use of countermeasures based<br />
on Information Security and Privacy Enhancing<br />
Technologies (ISTs and PETs)<br />
‣ The implementation of others is not trivial at all,<br />
mainly due to organizational differences between<br />
HCUs:<br />
‣ We will consider the problems associated with the<br />
fulfillment of the Access Control requirements, on the basis<br />
of the identified actor roles<br />
10