MODERN CRYPTOGRAPHY
MODERN CRYPTOGRAPHY
MODERN CRYPTOGRAPHY
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
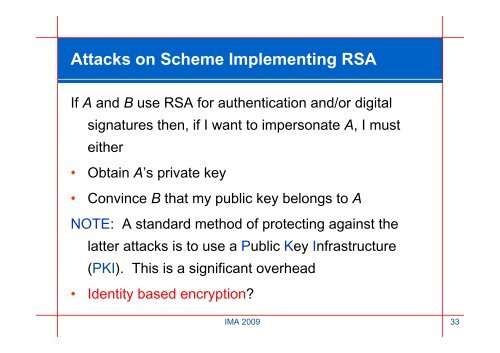
Attacks on Scheme Implementing RSA<br />
If A and B use RSA for authentication and/or digital<br />
signatures then, if I want to impersonate A, I must<br />
either<br />
• Obtain A’s private key<br />
• Convince B that my public key belongs to A<br />
NOTE: A standard method of protecting against the<br />
latter attacks is to use a Public Key Infrastructure<br />
(PKI). This is a significant overhead<br />
• Identity based encryption?<br />
IMA 2009 33



![Download NLAO Application Form [PDF] - Institute of Mathematics ...](https://img.yumpu.com/22617151/1/184x260/download-nlao-application-form-pdf-institute-of-mathematics-.jpg?quality=85)
![Download Education Grants Application Form [PDF] - Institute of ...](https://img.yumpu.com/22617149/1/184x260/download-education-grants-application-form-pdf-institute-of-.jpg?quality=85)
![IMA IPD brochure [PDF] - Institute of Mathematics and its Applications](https://img.yumpu.com/22617139/1/189x260/ima-ipd-brochure-pdf-institute-of-mathematics-and-its-applications.jpg?quality=85)