- Page 2 and 3: CONTENTS PREFACE xxii Part I BASICS
- Page 4 and 5: Contents ix 4.3 Relational Calculus
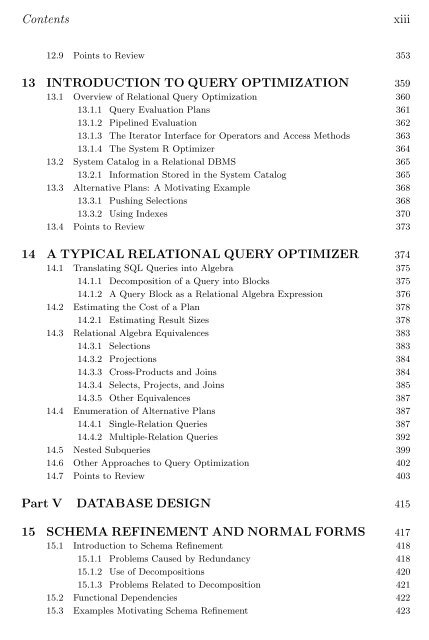
- Page 6 and 7: Contents xi 7.7.1 Fixed-Length Reco
- Page 10 and 11: Contents xv 16.8.5 Horizontal Decom
- Page 12 and 13: Contents xvii 21.3.2 Sorting 602 21
- Page 14 and 15: Contents xix 24.3.6 The Use of Asso
- Page 16 and 17: Contents xxi 28.3 Mobile Databases
- Page 18 and 19: Preface xxiii Choice of Topics The
- Page 20 and 21: Preface xxv 6 QBE II 4 Relational A
- Page 22 and 23: Preface xxvii Acknowledgments This
- Page 24 and 25: Preface xxix phone calls in which h
- Page 27 and 28: 1 INTRODUCTION TO DATABASE SYSTEMS
- Page 29 and 30: Introduction to Database Systems 5
- Page 31 and 32: Introduction to Database Systems 7
- Page 33 and 34: Introduction to Database Systems 9
- Page 35 and 36: Introduction to Database Systems 11
- Page 37 and 38: Introduction to Database Systems 13
- Page 39 and 40: Introduction to Database Systems 15
- Page 41 and 42: Introduction to Database Systems 17
- Page 43 and 44: Introduction to Database Systems 19
- Page 45 and 46: Introduction to Database Systems 21
- Page 47 and 48: Introduction to Database Systems 23
- Page 49 and 50: The Entity-Relationship Model 25 Da
- Page 51 and 52: The Entity-Relationship Model 27 me
- Page 53 and 54: The Entity-Relationship Model 29 Th
- Page 55 and 56: The Entity-Relationship Model 31 in
- Page 57 and 58: The Entity-Relationship Model 33 DE
- Page 59 and 60:
The Entity-Relationship Model 35 wi
- Page 61 and 62:
The Entity-Relationship Model 37 Mo
- Page 63 and 64:
The Entity-Relationship Model 39 2.
- Page 65 and 66:
The Entity-Relationship Model 41 Bu
- Page 67 and 68:
The Entity-Relationship Model 43 na
- Page 69 and 70:
The Entity-Relationship Model 45 An
- Page 71 and 72:
The Entity-Relationship Model 47 Gr
- Page 73 and 74:
The Entity-Relationship Model 49 Fo
- Page 75 and 76:
3 THE RELATIONAL MODEL TABLE: An ar
- Page 77 and 78:
The Relational Model 53 is a table,
- Page 79 and 80:
The Relational Model 55 The degree,
- Page 81 and 82:
The Relational Model 57 condition t
- Page 83 and 84:
The Relational Model 59 Specifying
- Page 85 and 86:
The Relational Model 61 cid CHAR(20
- Page 87 and 88:
The Relational Model 63 discuss the
- Page 89 and 90:
The Relational Model 65 The symbol
- Page 91 and 92:
The Relational Model 67 3.5.1 Entit
- Page 93 and 94:
The Relational Model 69 specify tha
- Page 95 and 96:
The Relational Model 71 CREATE TABL
- Page 97 and 98:
The Relational Model 73 To ensure t
- Page 99 and 100:
The Relational Model 75 1. We can m
- Page 101 and 102:
The Relational Model 77 name ssn lo
- Page 103 and 104:
The Relational Model 79 name sid co
- Page 105 and 106:
The Relational Model 81 Clubs(cname
- Page 107 and 108:
The Relational Model 83 ALTER TABLE
- Page 109 and 110:
The Relational Model 85 2. Write th
- Page 111:
The Relational Model 87 Integrity c
- Page 115 and 116:
4 RELATIONAL ALGEBRA AND CALCULUS S
- Page 117 and 118:
Relational Algebra and Calculus 93
- Page 119 and 120:
Relational Algebra and Calculus 95
- Page 121 and 122:
Relational Algebra and Calculus 97
- Page 123 and 124:
Relational Algebra and Calculus 99
- Page 125 and 126:
Relational Algebra and Calculus 101
- Page 127 and 128:
Relational Algebra and Calculus 103
- Page 129 and 130:
Relational Algebra and Calculus 105
- Page 131 and 132:
Relational Algebra and Calculus 107
- Page 133 and 134:
Relational Algebra and Calculus 109
- Page 135 and 136:
Relational Algebra and Calculus 111
- Page 137 and 138:
Relational Algebra and Calculus 113
- Page 139 and 140:
Relational Algebra and Calculus 115
- Page 141 and 142:
Relational Algebra and Calculus 117
- Page 143 and 144:
5 SQL: QUERIES, PROGRAMMING, TRIGGE
- Page 145 and 146:
SQL: Queries, Programming, Triggers
- Page 147 and 148:
SQL: Queries, Programming, Triggers
- Page 149 and 150:
SQL: Queries, Programming, Triggers
- Page 151 and 152:
SQL: Queries, Programming, Triggers
- Page 153 and 154:
SQL: Queries, Programming, Triggers
- Page 155 and 156:
SQL: Queries, Programming, Triggers
- Page 157 and 158:
SQL: Queries, Programming, Triggers
- Page 159 and 160:
SQL: Queries, Programming, Triggers
- Page 161 and 162:
SQL: Queries, Programming, Triggers
- Page 163 and 164:
SQL: Queries, Programming, Triggers
- Page 165 and 166:
SQL: Queries, Programming, Triggers
- Page 167 and 168:
SQL: Queries, Programming, Triggers
- Page 169 and 170:
SQL: Queries, Programming, Triggers
- Page 171 and 172:
SQL: Queries, Programming, Triggers
- Page 173 and 174:
SQL: Queries, Programming, Triggers
- Page 175 and 176:
SQL: Queries, Programming, Triggers
- Page 177 and 178:
SQL: Queries, Programming, Triggers
- Page 179 and 180:
SQL: Queries, Programming, Triggers
- Page 181 and 182:
SQL: Queries, Programming, Triggers
- Page 183 and 184:
SQL: Queries, Programming, Triggers
- Page 185 and 186:
SQL: Queries, Programming, Triggers
- Page 187 and 188:
SQL: Queries, Programming, Triggers
- Page 189 and 190:
SQL: Queries, Programming, Triggers
- Page 191 and 192:
SQL: Queries, Programming, Triggers
- Page 193 and 194:
SQL: Queries, Programming, Triggers
- Page 195 and 196:
SQL: Queries, Programming, Triggers
- Page 197 and 198:
SQL: Queries, Programming, Triggers
- Page 199 and 200:
SQL: Queries, Programming, Triggers
- Page 201 and 202:
6 QUERY-BY-EXAMPLE (QBE) Example is
- Page 203 and 204:
Query-by-Example (QBE) 179 intuitiv
- Page 205 and 206:
Query-by-Example (QBE) 181 Notice h
- Page 207 and 208:
Query-by-Example (QBE) 183 6.6 THE
- Page 209 and 210:
Query-by-Example (QBE) 185 Sailors
- Page 211 and 212:
Query-by-Example (QBE) 187 Sailors
- Page 213 and 214:
Query-by-Example (QBE) 189 two logi
- Page 215 and 216:
Query-by-Example (QBE) 191 Supplier
- Page 217:
PARTIII DATA STORAGE AND INDEXING
- Page 220 and 221:
196 Chapter 7 7.1 THE MEMORY HIERAR
- Page 222 and 223:
198 Chapter 7 single-sided or doubl
- Page 224 and 225:
200 Chapter 7 (This observation is
- Page 226 and 227:
202 Chapter 7 since the disk wears
- Page 228 and 229:
204 Chapter 7 Level 0+1: Striping a
- Page 230 and 231:
206 Chapter 7 A RAID Level 5 system
- Page 232 and 233:
208 Chapter 7 instructions: “Read
- Page 234 and 235:
210 Chapter 7 Incrementing pin coun
- Page 236 and 237:
212 Chapter 7 Buffer management in
- Page 238 and 239:
214 Chapter 7 7.5 FILES AND INDEXES
- Page 240 and 241:
216 Chapter 7 Directory of Pages An
- Page 242 and 243:
218 Chapter 7 Rids in commercial sy
- Page 244 and 245:
220 Chapter 7 in order to ensure th
- Page 246 and 247:
222 Chapter 7 Record formats in com
- Page 248 and 249:
224 Chapter 7 Large records in real
- Page 250 and 251:
226 Chapter 7 EXERCISES Exercise 7.
- Page 252 and 253:
228 Chapter 7 Exercise 7.19 Conside
- Page 254 and 255:
8 FILE ORGANIZATIONS & INDEXES If y
- Page 256 and 257:
232 Chapter 8 8.2 COMPARISON OF THR
- Page 258 and 259:
234 Chapter 8 file. We can locate t
- Page 260 and 261:
236 Chapter 8 be scanned.) The cost
- Page 262 and 263:
238 Chapter 8 age h1 h(age)=00 h(ag
- Page 264 and 265:
240 Chapter 8 Indexes that maintain
- Page 266 and 267:
242 Chapter 8 records in the data f
- Page 268 and 269:
244 Chapter 8 8.5 INDEX SPECIFICATI
- Page 270 and 271:
246 Chapter 8 sid name login age gp
- Page 272 and 273:
248 Chapter 9 9.1 INDEXED SEQUENTIA
- Page 274 and 275:
250 Chapter 9 Data Pages Index Page
- Page 276 and 277:
252 Chapter 9 placeholder for futur
- Page 278 and 279:
254 Chapter 9 Index entries (Direct
- Page 280 and 281:
256 Chapter 9 func find (search key
- Page 282 and 283:
258 Chapter 9 proc insert (nodepoin
- Page 284 and 285:
260 Chapter 9 sibling of this leaf
- Page 286 and 287:
262 Chapter 9 proc delete (parentpo
- Page 288 and 289:
264 Chapter 9 Root 5 13 17 30 2* 3*
- Page 290 and 291:
266 Chapter 9 Duplicate handling in
- Page 292 and 293:
268 Chapter 9 Daniel Lee David Smit
- Page 294 and 295:
270 Chapter 9 We have redistributed
- Page 296 and 297:
272 Chapter 9 9.8.4 The Effect of I
- Page 298 and 299:
274 Chapter 9 A B C 10 20 30 80 I1
- Page 300 and 301:
276 Chapter 9 1. How many levels do
- Page 302 and 303:
10 HASH-BASED INDEXING Not chaos-li
- Page 304 and 305:
280 Chapter 10 The main problem wit
- Page 306 and 307:
282 Chapter 10 Next, let us conside
- Page 308 and 309:
284 Chapter 10 LOCAL DEPTH GLOBAL D
- Page 310 and 311:
286 Chapter 10 10.3 LINEAR HASHING
- Page 312 and 313:
288 Chapter 10 conditions based on
- Page 314 and 315:
290 Chapter 10 Level=0 h1 h0 PRIMAR
- Page 316 and 317:
292 Chapter 10 We observe that the
- Page 318 and 319:
294 Chapter 10 3 64 16 Bucket A 000
- Page 320 and 321:
296 Chapter 10 3. Static Hashing ve
- Page 322 and 323:
298 Chapter 10 BIBLIOGRAPHIC NOTES
- Page 325 and 326:
11 EXTERNAL SORTING Good order is t
- Page 327 and 328:
External Sorting 303 proc 2-way ext
- Page 329 and 330:
External Sorting 305 11.2 EXTERNAL
- Page 331 and 332:
External Sorting 307 As an example,
- Page 333 and 334:
External Sorting 309 the current ru
- Page 335 and 336:
External Sorting 311 N B=1,000 B=5,
- Page 337 and 338:
External Sorting 313 Index entries
- Page 339 and 340:
External Sorting 315 N Sorting p=1
- Page 341 and 342:
External Sorting 317 2. How many pa
- Page 343 and 344:
12 EVALUATION OF RELATIONAL OPERATO
- Page 345 and 346:
Evaluation of Relational Operators
- Page 347 and 348:
Evaluation of Relational Operators
- Page 349 and 350:
Evaluation of Relational Operators
- Page 351 and 352:
Evaluation of Relational Operators
- Page 353 and 354:
Evaluation of Relational Operators
- Page 355 and 356:
Evaluation of Relational Operators
- Page 357 and 358:
Evaluation of Relational Operators
- Page 359 and 360:
Evaluation of Relational Operators
- Page 361 and 362:
Evaluation of Relational Operators
- Page 363 and 364:
Evaluation of Relational Operators
- Page 365 and 366:
Evaluation of Relational Operators
- Page 367 and 368:
Evaluation of Relational Operators
- Page 369 and 370:
Evaluation of Relational Operators
- Page 371 and 372:
Evaluation of Relational Operators
- Page 373 and 374:
Evaluation of Relational Operators
- Page 375 and 376:
Evaluation of Relational Operators
- Page 377 and 378:
Evaluation of Relational Operators
- Page 379 and 380:
Evaluation of Relational Operators
- Page 381 and 382:
Evaluation of Relational Operators
- Page 383 and 384:
13 INTRODUCTION TO QUERY OPTIMIZATI
- Page 385 and 386:
Introduction to Query Optimization
- Page 387 and 388:
Introduction to Query Optimization
- Page 389 and 390:
Introduction to Query Optimization
- Page 391 and 392:
Introduction to Query Optimization
- Page 393 and 394:
Introduction to Query Optimization
- Page 395 and 396:
Introduction to Query Optimization
- Page 397 and 398:
Introduction to Query Optimization
- Page 399 and 400:
A Typical Relational Query Optimize
- Page 401 and 402:
A Typical Relational Query Optimize
- Page 403 and 404:
A Typical Relational Query Optimize
- Page 405 and 406:
A Typical Relational Query Optimize
- Page 407 and 408:
A Typical Relational Query Optimize
- Page 409 and 410:
A Typical Relational Query Optimize
- Page 411 and 412:
A Typical Relational Query Optimize
- Page 413 and 414:
A Typical Relational Query Optimize
- Page 415 and 416:
A Typical Relational Query Optimize
- Page 417 and 418:
A Typical Relational Query Optimize
- Page 419 and 420:
A Typical Relational Query Optimize
- Page 421 and 422:
A Typical Relational Query Optimize
- Page 423 and 424:
A Typical Relational Query Optimize
- Page 425 and 426:
A Typical Relational Query Optimize
- Page 427 and 428:
A Typical Relational Query Optimize
- Page 429 and 430:
A Typical Relational Query Optimize
- Page 431 and 432:
A Typical Relational Query Optimize
- Page 433 and 434:
A Typical Relational Query Optimize
- Page 435 and 436:
A Typical Relational Query Optimize
- Page 437:
A Typical Relational Query Optimize
- Page 441 and 442:
15 SCHEMA REFINEMENT AND NORMAL FOR
- Page 443 and 444:
Schema Refinement and Normal Forms
- Page 445 and 446:
Schema Refinement and Normal Forms
- Page 447 and 448:
Schema Refinement and Normal Forms
- Page 449 and 450:
Schema Refinement and Normal Forms
- Page 451 and 452:
Schema Refinement and Normal Forms
- Page 453 and 454:
Schema Refinement and Normal Forms
- Page 455 and 456:
Schema Refinement and Normal Forms
- Page 457 and 458:
Schema Refinement and Normal Forms
- Page 459 and 460:
Schema Refinement and Normal Forms
- Page 461 and 462:
Schema Refinement and Normal Forms
- Page 463 and 464:
Schema Refinement and Normal Forms
- Page 465 and 466:
Schema Refinement and Normal Forms
- Page 467 and 468:
Schema Refinement and Normal Forms
- Page 469 and 470:
Schema Refinement and Normal Forms
- Page 471 and 472:
Schema Refinement and Normal Forms
- Page 473 and 474:
Schema Refinement and Normal Forms
- Page 475 and 476:
Schema Refinement and Normal Forms
- Page 477 and 478:
Schema Refinement and Normal Forms
- Page 479 and 480:
Schema Refinement and Normal Forms
- Page 481 and 482:
16 PHYSICAL DATABASE DESIGN AND TUN
- Page 483 and 484:
Physical Database Design and Tuning
- Page 485 and 486:
Physical Database Design and Tuning
- Page 487 and 488:
Physical Database Design and Tuning
- Page 489 and 490:
Physical Database Design and Tuning
- Page 491 and 492:
Physical Database Design and Tuning
- Page 493 and 494:
Physical Database Design and Tuning
- Page 495 and 496:
Physical Database Design and Tuning
- Page 497 and 498:
Physical Database Design and Tuning
- Page 499 and 500:
Physical Database Design and Tuning
- Page 501 and 502:
Physical Database Design and Tuning
- Page 503 and 504:
Physical Database Design and Tuning
- Page 505 and 506:
Physical Database Design and Tuning
- Page 507 and 508:
Physical Database Design and Tuning
- Page 509 and 510:
Physical Database Design and Tuning
- Page 511 and 512:
Physical Database Design and Tuning
- Page 513 and 514:
Physical Database Design and Tuning
- Page 515 and 516:
Physical Database Design and Tuning
- Page 517 and 518:
Physical Database Design and Tuning
- Page 519 and 520:
Physical Database Design and Tuning
- Page 521 and 522:
17 SECURITY I know that’s a secre
- Page 523 and 524:
Security 499 the GRANT and REVOKE c
- Page 525 and 526:
Security 501 Role-based authorizati
- Page 527 and 528:
Security 503 Suppose that this comm
- Page 529 and 530:
Security 505 the name of the object
- Page 531 and 532:
Security 507 System (System, Joe, S
- Page 533 and 534:
Security 509 unauthorized user can
- Page 535 and 536:
Security 511 bid bname color Securi
- Page 537 and 538:
Security 513 example, military data
- Page 539 and 540:
Security 515 Another approach to en
- Page 541 and 542:
Security 517 Further, because the c
- Page 543 and 544:
Security 519 1. Show the view defin
- Page 545:
PARTVI TRANSACTION MANAGEMENT
- Page 548 and 549:
524 Chapter 18 an execution of a us
- Page 550 and 551:
526 Chapter 18 Of course, since use
- Page 552 and 553:
528 Chapter 18 18.3.2 Serializabili
- Page 554 and 555:
530 Chapter 18 to another, a transa
- Page 556 and 557:
532 Chapter 18 There is another pot
- Page 558 and 559:
534 Chapter 18 T 1 T 2 X(A) R(A) W
- Page 560 and 561:
536 Chapter 18 if there is a subseq
- Page 562 and 563:
538 Chapter 18 whose effect is iden
- Page 564 and 565:
19 CONCURRENCY CONTROL Pooh was sit
- Page 566 and 567:
542 Chapter 19 T1 T2 T1 T2 (a) (b)
- Page 568 and 569:
544 Chapter 19 the data object iden
- Page 570 and 571:
546 Chapter 19 19.2.2 Deadlocks Con
- Page 572 and 573:
548 Chapter 19 T1 T2 T1 T2 T4 T3 T4
- Page 574 and 575:
550 Chapter 19 If the collection of
- Page 576 and 577:
552 Chapter 19 that exploit the hie
- Page 578 and 579:
554 Chapter 19 This approach improv
- Page 580 and 581:
556 Chapter 19 or a CREATE TABLE st
- Page 582 and 583:
558 Chapter 19 smaller number of lo
- Page 584 and 585:
560 Chapter 19 If, indeed, there ar
- Page 586 and 587:
562 Chapter 19 The Thomas Write Rul
- Page 588 and 589:
564 Chapter 19 What do real systems
- Page 590 and 591:
566 Chapter 19 EXERCISES Exercise 1
- Page 592 and 593:
568 Chapter 19 View Serializable Al
- Page 594 and 595:
570 Chapter 19 BIBLIOGRAPHIC NOTES
- Page 596 and 597:
572 Chapter 20 2. Redo: Repeats all
- Page 598 and 599:
574 Chapter 20 For recovery purpose
- Page 600 and 601:
576 Chapter 20 transaction for whic
- Page 602 and 603:
578 Chapter 20 Further, the log is
- Page 604 and 605:
580 Chapter 20 step. See Exercise 2
- Page 606 and 607:
582 Chapter 20 because either this
- Page 608 and 609:
584 Chapter 20 T 1000 while T 1000
- Page 610 and 611:
586 Chapter 20 This example illustr
- Page 612 and 613:
588 Chapter 20 the original page. T
- Page 614 and 615:
590 Chapter 20 LSN 00 10 20 30 40 5
- Page 616 and 617:
592 Chapter 20 LSN LOG 00 begin_che
- Page 619:
PARTVII ADVANCED TOPICS
- Page 622 and 623:
598 Chapter 21 sites have a signifi
- Page 624 and 625:
600 Chapter 21 SPEED-UP SCALE-UP wi
- Page 626 and 627:
602 Chapter 21 A parallel evaluatio
- Page 628 and 629:
604 Chapter 21 the join of A and B;
- Page 630 and 631:
606 Chapter 21 21.4 PARALLEL QUERY
- Page 632 and 633:
608 Chapter 21 The key to building
- Page 634 and 635:
610 Chapter 21 21.7 STORING DATA IN
- Page 636 and 637:
612 Chapter 21 21.8.1 Naming Object
- Page 638 and 639:
614 Chapter 21 21.9 DISTRIBUTED QUE
- Page 640 and 641:
616 Chapter 21 we will assume that
- Page 642 and 643:
618 Chapter 21 that only 20 percent
- Page 644 and 645:
620 Chapter 21 should be transparen
- Page 646 and 647:
622 Chapter 21 Frankfurt, and salar
- Page 648 and 649:
624 Chapter 21 Data Warehousing: An
- Page 650 and 651:
626 Chapter 21 For example, suppose
- Page 652 and 653:
628 Chapter 21 21.13.1 Normal Execu
- Page 654 and 655:
630 Chapter 21 recovers; we say tha
- Page 656 and 657:
632 Chapter 21 21.13.4 Three-Phase
- Page 658 and 659:
634 Chapter 21 periodically. There
- Page 660 and 661:
636 Chapter 21 1. Find the highest
- Page 662 and 663:
638 Chapter 21 1. Half the departme
- Page 664 and 665:
640 Chapter 21 10. Suppose that 2PC
- Page 666 and 667:
22 INTERNET DATABASES He profits mo
- Page 668 and 669:
644 Chapter 22 Science: Author:
- Page 670 and 671:
646 Chapter 22 The Database Booksto
- Page 672 and 673:
648 Chapter 22 #!/usr/bin/perl use
- Page 674 and 675:
650 Chapter 22 Web Browser HTTP Web
- Page 676 and 677:
652 Chapter 22 The design goals of
- Page 678 and 679:
654 Chapter 22 RichardFeynman
- Page 680 and 681:
656 Chapter 22 Until now we only c
- Page 682 and 683:
658 Chapter 22 even when two elemen
- Page 684 and 685:
660 Chapter 22 a LASTNAME element.
- Page 686 and 687:
662 Chapter 22 BOOK BOOK BOOK AUTHO
- Page 688 and 689:
664 Chapter 22 There are two common
- Page 690 and 691:
666 Chapter 22 A query containing a
- Page 692 and 693:
668 Chapter 22 breadth. Thus, query
- Page 694 and 695:
670 Chapter 22 Computing hub and au
- Page 696 and 697:
672 Chapter 22 and are said to be s
- Page 698 and 699:
674 Chapter 22 Exercise 22.5 Consid
- Page 700 and 701:
676 Chapter 22 advanced reader have
- Page 702 and 703:
678 Chapter 23 from many sources in
- Page 704 and 705:
680 Chapter 23 to achieve satisfact
- Page 706 and 707:
682 Chapter 23 query engines, data
- Page 708 and 709:
684 Chapter 23 country, state, andc
- Page 710 and 711:
686 Chapter 23 sales for each locat
- Page 712 and 713:
688 Chapter 23 CUBE pid, locid, tim
- Page 714 and 715:
690 Chapter 23 Beyond B+ trees: Com
- Page 716 and 717:
692 Chapter 23 bit vector for a giv
- Page 718 and 719:
694 Chapter 23 by the database desi
- Page 720 and 721:
696 Chapter 23 FROM Products P, Sal
- Page 722 and 723:
698 Chapter 23 23.5.4 Issues in Vie
- Page 724 and 725:
700 Chapter 23 23.6.1 Top N Queries
- Page 726 and 727:
702 Chapter 23 STATUS PRIORITIZE st
- Page 728 and 729:
704 Chapter 23 2. What is the relat
- Page 730 and 731:
706 Chapter 23 1. How is the follow
- Page 732 and 733:
708 Chapter 24 Finding useful trend
- Page 734 and 735:
710 Chapter 24 Usually the number o
- Page 736 and 737:
712 Chapter 24 such that the custom
- Page 738 and 739:
714 Chapter 24 24.3.1 Association R
- Page 740 and 741:
716 Chapter 24 transid custid date
- Page 742 and 743:
718 Chapter 24 We begin by introduc
- Page 744 and 745:
720 Chapter 24 tion on the basis of
- Page 746 and 747:
722 Chapter 24 depends on the measu
- Page 748 and 749:
724 Chapter 24 Input: noden, partit
- Page 750 and 751:
726 Chapter 24 WHERE R.age
- Page 752 and 753:
728 Chapter 24 Salary C 60k 30k A B
- Page 754 and 755:
730 Chapter 24 from another sequenc
- Page 756 and 757:
732 Chapter 24 24.8 POINTS TO REVIE
- Page 758 and 759:
734 Chapter 24 3. Illustrate your a
- Page 760 and 761:
25 OBJECT-DATABASE SYSTEMS with Jos
- Page 762 and 763:
738 Chapter 25 than the dollars and
- Page 764 and 765:
740 Chapter 25 1. CREATE TABLE Fram
- Page 766 and 767:
742 Chapter 25 25.2 USER-DEFINED AB
- Page 768 and 769:
744 Chapter 25 the DBMS uses a Java
- Page 770 and 771:
746 Chapter 25 gives us a collectio
- Page 772 and 773:
748 Chapter 25 Objects and oids: In
- Page 774 and 775:
750 Chapter 25 As an example, consi
- Page 776 and 777:
752 Chapter 25 for JPEG images and
- Page 778 and 779:
754 Chapter 25 camera: string, vide
- Page 780 and 781:
756 Chapter 25 25.6.2 Object Identi
- Page 782 and 783:
758 Chapter 25 pid camera listof(ro
- Page 784 and 785:
760 Chapter 25 25.7.1 Storage and A
- Page 786 and 787:
762 Chapter 25 User-Defined Aggrega
- Page 788 and 789:
764 Chapter 25 Optimizer extensibil
- Page 790 and 791:
766 Chapter 25 Class = interface +
- Page 792 and 793:
768 Chapter 25 An object of class S
- Page 794 and 795:
770 Chapter 25 25.9.2 OODBMS versus
- Page 796 and 797:
772 Chapter 25 nonreference types i
- Page 798 and 799:
774 Chapter 25 All tuples for all k
- Page 800 and 801:
776 Chapter 25 Array chunking is de
- Page 802 and 803:
778 Chapter 26 obtained through mea
- Page 804 and 805:
780 Chapter 26 between the wheel an
- Page 806 and 807:
782 Chapter 26 index will fully uti
- Page 808 and 809:
784 Chapter 26 The advantage of thi
- Page 810 and 811:
786 Chapter 26 and with radius r. W
- Page 812 and 813:
788 Chapter 26 2 1, 2, 3 A 2 1, 2,
- Page 814 and 815:
790 Chapter 26 Figure 26.6 shows tw
- Page 816 and 817:
792 Chapter 26 26.6.2 Insert and De
- Page 818 and 819:
794 Chapter 26 page that contains o
- Page 820 and 821:
796 Chapter 26 data, and multimedia
- Page 822 and 823:
798 Chapter 26 2. Assume that delet
- Page 824 and 825:
800 Chapter 27 Recursion in SQL: Th
- Page 826 and 827:
802 Chapter 27 by setting Part=trik
- Page 828 and 829:
804 Chapter 27 of relational calcul
- Page 830 and 831:
806 Chapter 27 According to this ru
- Page 832 and 833:
808 Chapter 27 by repeatedly evalua
- Page 834 and 835:
810 Chapter 27 We say that a table
- Page 836 and 837:
812 Chapter 27 Big2(Part) AS (SELEC
- Page 838 and 839:
814 Chapter 27 Unnecessary inferenc
- Page 840 and 841:
816 Chapter 27 27.4.2 Pushing Selec
- Page 842 and 843:
818 Chapter 27 When a query is pose
- Page 844 and 845:
820 Chapter 27 4. Write a program i
- Page 846 and 847:
28 ADDITIONAL TOPICS This is not th
- Page 848 and 849:
824 Chapter 28 actions, locks held
- Page 850 and 851:
826 Chapter 28 design decisions, si
- Page 852 and 853:
828 Chapter 28 discussed in Chapter
- Page 854 and 855:
830 Chapter 28 chapter illustrates,
- Page 856 and 857:
832 Appendix A A.2 CONCEPTUAL DESIG
- Page 858 and 859:
834 Appendix A the importance of th
- Page 860 and 861:
836 Appendix A author qty_in_stock
- Page 862 and 863:
838 Appendix A A.5.1 Tuning the Dat
- Page 864 and 865:
840 Appendix A A.7 APPLICATION LAYE
- Page 866 and 867:
B THE MINIBASE SOFTWARE Practice is
- Page 868 and 869:
844 Appendix B variants include fix
- Page 871 and 872:
REFERENCES [1] R. Abbott and H. Gar
- Page 873 and 874:
REFERENCES 849 [39] P. Atzeni, G. M
- Page 875 and 876:
REFERENCES 851 [84] J. Biskup and B
- Page 877 and 878:
REFERENCES 853 [128] D. Chamberlin.
- Page 879 and 880:
REFERENCES 855 [177] C. Delobel. No
- Page 881 and 882:
REFERENCES 857 [224] C. Faloutsos,
- Page 883 and 884:
REFERENCES 859 [270] D. Gifford. We
- Page 885 and 886:
REFERENCES 861 [315] J. Hellerstein
- Page 887 and 888:
REFERENCES 863 [363] L. Kerschberg,
- Page 889 and 890:
REFERENCES 865 [410] T. Leung and R
- Page 891 and 892:
REFERENCES 867 [455] J. Melton and
- Page 893 and 894:
REFERENCES 869 [500] P. O’Neil an
- Page 895 and 896:
REFERENCES 871 [544] A. Reuter. Per
- Page 897 and 898:
REFERENCES 873 [589] D. Shasha. Dat
- Page 899 and 900:
REFERENCES 875 [636] W. Sun, Y. Lin
- Page 901 and 902:
REFERENCES 877 [682] R. Williams, D
- Page 903 and 904:
SUBJECT INDEX 1NF, 430 2NF, 434 2PC
- Page 905 and 906:
Subject Index 881 Complete axioms,
- Page 907 and 908:
Subject Index 883 global object nam
- Page 909 and 910:
Subject Index 885 Granting privileg
- Page 911 and 912:
Subject Index 887 Local depth in ex
- Page 913 and 914:
Subject Index 889 Order of a B+ tre
- Page 915 and 916:
Subject Index 891 oids, 757 violati
- Page 917 and 918:
Subject Index 893 cursors, 153 orde
- Page 919 and 920:
895 Tuning, 26, 457, 459, 474 Tunin
- Page 921 and 922:
Author Index 897 Breitbart, Y., 641
- Page 923 and 924:
Author Index 899 Gehani, N.H., 176,
- Page 925 and 926:
Author Index 901 Lebowitz, F., 91 L
- Page 927 and 928:
Author Index 903 Prescod, P., 675,
- Page 929 and 930:
Author Index 905 Swagerman, R., 776