Using Wireshark to Gather Forensic Evidence on Malware ...
Using Wireshark to Gather Forensic Evidence on Malware ...
Using Wireshark to Gather Forensic Evidence on Malware ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
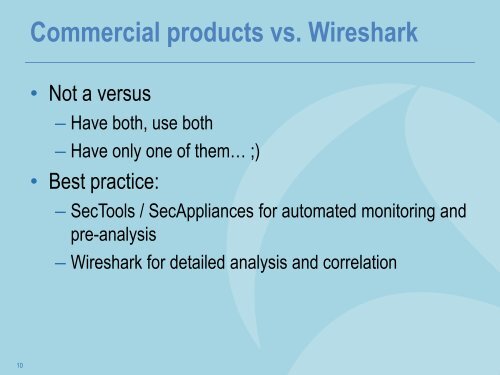
Commercial products vs. <str<strong>on</strong>g>Wireshark</str<strong>on</strong>g><br />
• Not a versus<br />
– Have both, use both<br />
– Have <strong>on</strong>ly <strong>on</strong>e of them… ;)<br />
• Best practice:<br />
– SecTools / SecAppliances for au<str<strong>on</strong>g>to</str<strong>on</strong>g>mated m<strong>on</strong>i<str<strong>on</strong>g>to</str<strong>on</strong>g>ring and<br />
pre-analysis<br />
– <str<strong>on</strong>g>Wireshark</str<strong>on</strong>g> for detailed analysis and correlati<strong>on</strong><br />
10