- Page 3 and 4: THIRD EDITION UNIX POWER TOOLS Shel
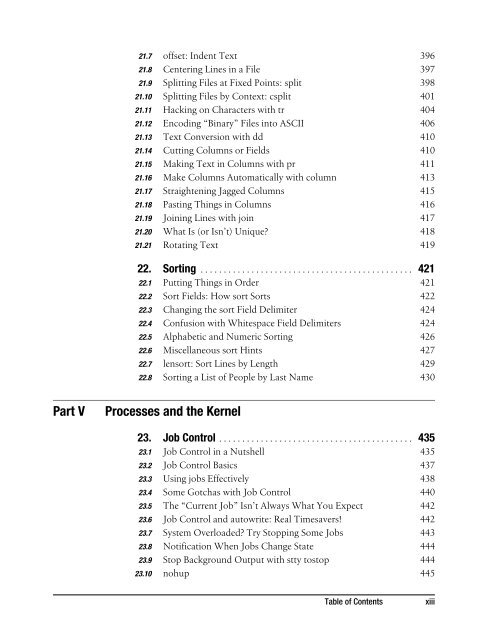
- Page 5 and 6: Table of Contents How to Use This B
- Page 7 and 8: 4. Interacting with Your Environmen
- Page 9 and 10: 8.7 Some GNU ls Features 161 8.8 A
- Page 11 and 12: 12.9 Finer Control on tail 243 12.1
- Page 13: 17.7 Get Back What You Deleted with
- Page 17 and 18: 26. System Performance and Profilin
- Page 19 and 20: 30.10 Running a Series of Commands
- Page 21 and 22: 34.19 Multiline Delete 692 34.20 Ma
- Page 23 and 24: Part VII Extending and Managing You
- Page 25 and 26: 43.7 The () Subshell Operators 893
- Page 27 and 28: 48.5 What We Mean by DoS 973 48.6 B
- Page 29 and 30: How to Use This Book Summary Boxes
- Page 31 and 32: Preface A Book for Browsing Technic
- Page 33 and 34: Cross-References If a cross-referen
- Page 35 and 36: Here’s a list of authors and thei
- Page 37 and 38: time, and the book looked to be dyi
- Page 39 and 40: Acknowledgments for the Second Edit
- Page 41: Part I I.Basic Unix Environment Par
- Page 44 and 45: 1.2 Unix is also important to power
- Page 46 and 47: 1.3 1.3 The Core of Unix In recent
- Page 48 and 49: 1.5 For example, one basic rule is
- Page 50 and 51: 1.6 syntax—as well as more featur
- Page 52 and 53: 1.8 But you’re a novice, and you
- Page 54 and 55: 1.10 You can add new directories to
- Page 56 and 57: 1.11 stay in touch. Therefore, you
- Page 58 and 59: 1.13 Table 1-1. Filename extensions
- Page 60 and 61: 1.14 not match a period; you have t
- Page 62 and 63: 1.15 To locate any file, we can giv
- Page 64 and 65:
1.16 tries to look up files relativ
- Page 66 and 67:
1.18 use the chgrp command to chang
- Page 68 and 69:
1.21 These three scripting language
- Page 70 and 71:
1.22 rcp scp This is a “remote cp
- Page 72 and 73:
Chapter 22 Getting Help 2.1 The man
- Page 74 and 75:
2.4 Output from whereis typically l
- Page 76 and 77:
2.5 2.5 How Unix Systems Remember T
- Page 78 and 79:
2.8 (Of course, you don’t need to
- Page 80 and 81:
2.9 When using the info command, if
- Page 83 and 84:
Chapter 3 3 Setting Up Your Unix Sh
- Page 85 and 86:
3.3 xterm -ls starts a login shell
- Page 87 and 88:
3.3 Korn shell The Korn shell is a
- Page 89 and 90:
3.5 Now wherever you need to know t
- Page 91 and 92:
3.8 somehost% vi .cshrc ...Make edi
- Page 93 and 94:
3.9 case 35.10 case "$-/${ENV_SET:-
- Page 95 and 96:
3.11 • If you use several kinds o
- Page 97 and 98:
3.14 3.13 Terminal Setup: Testing P
- Page 99 and 100:
3.17 On many systems, the command s
- Page 101 and 102:
3.19 Other shell variables (35.9) a
- Page 103 and 104:
3.20 $Id 39.5 .netrc Alisting of ho
- Page 105 and 106:
3.21 3.21 Make Your Own Manpages Wi
- Page 107 and 108:
3.22 less 12.3 % ls -l /usr/local/m
- Page 109 and 110:
3.22 Table 3-1. Important -man macr
- Page 111 and 112:
4.3 The default bash prompt is a go
- Page 113 and 114:
4.5 } # for ksh do_prompt() { date=
- Page 115 and 116:
4.6 # # Functions: # setprompt() {
- Page 117 and 118:
4.8 applefarm:/usr/elaineq/projects
- Page 119 and 120:
4.10 If you’re using tcsh, its sp
- Page 121 and 122:
4.11 The string \$ is replaced by a
- Page 123 and 124:
4.13 bash doesn’t need an if beca
- Page 125 and 126:
4.14 Because bash can run a command
- Page 127 and 128:
4.16 The prompt format is up to you
- Page 129 and 130:
4.17 Wow! ohh, big mouth, Mick Jagg
- Page 131 and 132:
4.19 Here’s a different sort of s
- Page 133 and 134:
5.2 5.2 The Idea of a Terminal Data
- Page 135 and 136:
5.3 5.3 Setting the Terminal Type W
- Page 137 and 138:
5.4 dialing in from home, but used
- Page 139 and 140:
5.5 The string Terminal recognized
- Page 141 and 142:
5.6 If you can log in after that, y
- Page 143 and 144:
5.6 sending data to your terminal.
- Page 145 and 146:
5.8 have, you know how disorienting
- Page 147 and 148:
5.10 xterm * gives you a window con
- Page 149 and 150:
5.13 5.12 How Many Lines to Save? I
- Page 151 and 152:
5.15 You can modify the character c
- Page 153 and 154:
5.17 Another quick way to get a lis
- Page 155 and 156:
5.18 5.18 Changing Fonts Dynamicall
- Page 157 and 158:
5.19 last selected text as a font n
- Page 159 and 160:
5.20 Figure 5-4. Text you copy from
- Page 161 and 162:
5.21 ${1+"$@"} 36.7 CTRL-d > This i
- Page 163 and 164:
5.23 5.23 Don’t Quote Arguments t
- Page 165 and 166:
6.1 Another example is if you mista
- Page 167 and 168:
6.2 One danger of using xmodmap is
- Page 169 and 170:
6.3 xclient*Buttons.foreground: xcl
- Page 171 and 172:
6.4 or nearly so. Among the less ob
- Page 173 and 174:
6.5 Anot-so-obvious principle behin
- Page 175 and 176:
6.7 6.6 Setting Resources with the
- Page 177 and 178:
6.8 will expect to read its data fr
- Page 179 and 180:
6.9 Use an editor to edit the file,
- Page 181 and 182:
6.10 Starting Remote X Clients from
- Page 183:
6.10 sapphire:joan % which rsh /bin
- Page 187 and 188:
Chapter 7 7 Directory Organization
- Page 189 and 190:
7.4 Reading a directory is relative
- Page 191 and 192:
7.7 Generally, a descriptive filena
- Page 193 and 194:
7.8 What if the parent directory do
- Page 195 and 196:
8.3 As long as we’re talking abou
- Page 197 and 198:
8.5 —JP jerry@ora ~/.bin 65 % ls
- Page 199 and 200:
8.6 you see the escape sequences wh
- Page 201 and 202:
8.7 The --color option gives you th
- Page 203 and 204:
8.10 —DS -rw------- 1 dansmith st
- Page 205 and 206:
8.11 The -C option lists the files
- Page 207 and 208:
8.13 % ls -b ab\013\014cd This show
- Page 209 and 210:
8.16 8.15 newer: Print the Name of
- Page 211 and 212:
Chapter 9 9 Finding Files with find
- Page 213 and 214:
9.2 -ls List the file’s name on s
- Page 215 and 216:
9.5 9.3 Don’t Forget -print “Wh
- Page 217 and 218:
9.6 • Takes the specified action
- Page 219 and 220:
9.9 9.8 Exact File-Time Comparisons
- Page 221 and 222:
9.10 % find . -inum 31246 -exec rm
- Page 223 and 224:
9.12 Let’s work from an example.
- Page 225 and 226:
9.15 9.14 Searching for Files by Si
- Page 227 and 228:
9.18 9.17 Duplicating a Directory T
- Page 229 and 230:
9.19 9.19 Wildcards with “Fast fi
- Page 231 and 232:
9.20 To make your own “fast find
- Page 233 and 234:
9.22 The answer is to add the Unix
- Page 235 and 236:
9.23 Here’s a practical example t
- Page 237 and 238:
9.24 To expand a range of members s
- Page 239 and 240:
9.27 Finally, let’s look at ./adi
- Page 241 and 242:
Chapter 10 10 Linking, Renaming, an
- Page 243 and 244:
10.3 The only time you actually nee
- Page 245 and 246:
10.4 ln -s /development/doc/man/man
- Page 247 and 248:
10.4 Links to a Directory While we
- Page 249 and 250:
10.6 To remove a link, either hard
- Page 251 and 252:
10.7 By using symlinks, we installe
- Page 253 and 254:
10.11 mv 'afile.new' 'afile.old' mv
- Page 255 and 256:
10.12 • Use this to copy the subd
- Page 257 and 258:
10.13 work bkup .setup - directory
- Page 259 and 260:
11.1 $ diff -e test1 test2 3c grape
- Page 261 and 262:
11.3 The diff3 command also has a -
- Page 263 and 264:
11.3 static char rcsid[] = + "$Id:
- Page 265 and 266:
11.6 To see only lines that are dif
- Page 267 and 268:
11.8 11.8 Comparing Two Files with
- Page 269 and 270:
11.9 11.9 More Friendly comm Output
- Page 271 and 272:
11.10 The basic operation that make
- Page 273 and 274:
11.11 password file is more recent
- Page 275 and 276:
12.2 1. First form: % cat file % ca
- Page 277 and 278:
12.4 Table 12-1. Commonly used less
- Page 279 and 280:
12.5 Next, od -c. It’s easier to
- Page 281 and 282:
12.7 /etc/magic has four fields: of
- Page 283 and 284:
12.10 ad0: 19569MB [39761/16/63] a
- Page 285 and 286:
12.11 enter CTRL-c (or whatever you
- Page 287 and 288:
Chapter 13 13 Searching Through Fil
- Page 289 and 290:
13.3 grep is also often used as a f
- Page 291 and 292:
13.6 % egrep "Alcuin (User|Programm
- Page 293 and 294:
13.7 rcsgrep, rcsegrep, rcsfgrep Th
- Page 295 and 296:
13.9 I’ve truncated each line for
- Page 297 and 298:
13.11 (Notice that as the problem g
- Page 299 and 300:
13.15 Ascript for looking up phone
- Page 301 and 302:
13.16 Well, as described on its own
- Page 303 and 304:
14.3 You really don’t care about
- Page 305 and 306:
14.5 14.4 Tricks for Making rm Safe
- Page 307 and 308:
14.8 —BB #!/bin/sh case $# in 0)
- Page 309 and 310:
14.11 14.10 Deletion with Prejudice
- Page 311 and 312:
14.14 14.13 Handling a Filename Sta
- Page 313 and 314:
14.16 The rmdir command often confu
- Page 315 and 316:
14.18 if 35.13 && 35.14 to a tempor
- Page 317 and 318:
Chapter 15 15 Optimizing Disk Space
- Page 319 and 320:
15.4 15.3 Save Space with “Bit Bu
- Page 321 and 322:
15.6 To eliminate core dumps entire
- Page 323 and 324:
15.6 gzip and gunzip can also compr
- Page 325 and 326:
15.7 common convention is .tgz. I
- Page 327 and 328:
15.8 This report shows information
- Page 329 and 330:
15.10 • Bigger than one block, si
- Page 331:
15.11 be repeated whenever you log
- Page 335 and 336:
Chapter 16 16 Spell Checking, Word
- Page 337 and 338:
16.2 default, the private dictionar
- Page 339 and 340:
16.4 When these spellers start, the
- Page 341 and 342:
16.5 =laserWrite =laserWrit =output
- Page 343 and 344:
16.6 16.6 Counting Lines, Words, an
- Page 345 and 346:
16.8 16.7 Find a a Doubled Word One
- Page 347 and 348:
16.9 deroff has one major failing,
- Page 349 and 350:
17.3 17.2 What We Cover The article
- Page 351 and 352:
17.4 17.4 Edits Between Files When
- Page 353 and 354:
17.7 17.6 Using Buffers to Move or
- Page 355 and 356:
17.9 Global Searches In vi you use
- Page 357 and 358:
17.13 You can combine ex line addre
- Page 359 and 360:
17.14 2. Replace one or more spaces
- Page 361 and 362:
17.17 \(...\)...\1 32.21 (You might
- Page 363 and 364:
17.18 As another example, assume yo
- Page 365 and 366:
17.20 17.20 Be Careful with vi -r R
- Page 367 and 368:
17.22 :!mail Read your mail. Be car
- Page 369 and 370:
17.23 abbr is an abbreviation for t
- Page 371 and 372:
17.26 You may be able to enforce co
- Page 373 and 374:
17.28 First, you’ll need the abso
- Page 375 and 376:
17.30 set nowrapscan wrapmargin=7 s
- Page 377 and 378:
18.2 Command Mode Maps The map comm
- Page 379 and 380:
18.3 What does that do? It executes
- Page 381 and 382:
18.4 2. Yank or delete the line(s)
- Page 383 and 384:
18.6 —JP Delete that long line in
- Page 385 and 386:
18.7 If you ask for a list of text-
- Page 387 and 388:
18.8 18.8 More Examples of Mapping
- Page 389 and 390:
18.11 Anytime you type (during text
- Page 391 and 392:
18.14 Here are two macros that cut
- Page 393 and 394:
Chapter 19 19 GNU Emacs 19.1 Emacs:
- Page 395 and 396:
19.2 Now that we all have nice work
- Page 397 and 398:
19.2 virtually every programming la
- Page 399 and 400:
19.4 First, try the command ESC-x r
- Page 401 and 402:
19.7 Along the same lines as comman
- Page 403 and 404:
19.10 Of course, now you’ll have
- Page 405 and 406:
19.11 1. Enter word-abbreviation mo
- Page 407 and 408:
Chapter 20 20 Batch Editing 20.1 Wh
- Page 409 and 410:
20.3 One additional suggestion is t
- Page 411 and 412:
20.4 delete [address] d [buffer] De
- Page 413 and 414:
20.6 20.5 Running Editing Scripts W
- Page 415 and 416:
20.7 is the directory on the local
- Page 417 and 418:
20.9 Unfortunately for programmers,
- Page 419 and 420:
20.10 For example, every Red Hat Li
- Page 421 and 422:
20.10 Except for BEGIN and END, pat
- Page 423 and 424:
20.10 Variables and Array Assignmen
- Page 425 and 426:
20.10 for for (item in array) comma
- Page 427 and 428:
20.10 format can also contain embed
- Page 429 and 430:
20.11 gawk Unfortunately, nawk is n
- Page 431 and 432:
21.2 21.2 Neatening Text with fmt O
- Page 433 and 434:
21.3 (37.4) and nroff. Using those
- Page 435 and 436:
21.5 # Get comment characters used
- Page 437 and 438:
21.8 writes to standard output. The
- Page 439 and 440:
21.9 split total 288 -r--r--r-- 1 j
- Page 441 and 442:
21.10 my $outfile; open($outfile, "
- Page 443 and 444:
21.10 There’s still a slight prob
- Page 445 and 446:
21.11 Of course, you need to be car
- Page 447 and 448:
21.12 uuencoding The uuencode utili
- Page 449 and 450:
21.12 Unlike uuencoded messages, wh
- Page 451 and 452:
21.15 The order of the columns and
- Page 453 and 454:
21.16 The columns aren’t balanced
- Page 455 and 456:
21.17 21.17 Straightening Jagged Co
- Page 457 and 458:
21.19 21.19 Joining Lines with join
- Page 459 and 460:
21.21 To show which names appear mo
- Page 461 and 462:
Chapter 22 22 Sorting 22.1 Putting
- Page 463 and 464:
22.2 field 3, continue sorting on f
- Page 465 and 466:
22.4 • Any whitespace character f
- Page 467 and 468:
22.6 1 11 12 2 ... Of course, this
- Page 469 and 470:
22.7 example, imagine you have a pr
- Page 471:
22.8 If you want more control over
- Page 475 and 476:
Chapter 23 23 Job Control 23.1 Job
- Page 477 and 478:
23.2 Some systems, like Linux, exte
- Page 479 and 480:
23.3 In fact, one job number is ass
- Page 481 and 482:
23.4 This may strike you as a defec
- Page 483 and 484:
23.7 If your system has job control
- Page 485 and 486:
23.10 background jobs that try to w
- Page 487 and 488:
23.12 PID TTY STAT TIME COMMAND 289
- Page 489 and 490:
23.13 23.13 Stopping Remote Login S
- Page 491 and 492:
Chapter 24 24 Starting, Stopping, a
- Page 493 and 494:
24.3 24.3 Managing Processes: Overa
- Page 495 and 496:
24.4 One more useful concept: when
- Page 497 and 498:
24.5 By default, ps lists only your
- Page 499 and 500:
24.6 The columns hold the username,
- Page 501 and 502:
24.7 Figure 24-1. Background jobs i
- Page 503 and 504:
24.9 24.9 The /proc Filesystem In U
- Page 505 and 506:
24.9 For a simple example, here’s
- Page 507 and 508:
24.9 cache size: 128 KB fdiv_bug: n
- Page 509 and 510:
24.11 came when the kernel detected
- Page 511 and 512:
24.13 • Processes waiting for una
- Page 513 and 514:
24.14 kill 24.12 % kill -HUP 4363 .
- Page 515 and 516:
24.15 kill is a shell builtin kill
- Page 517 and 518:
24.16 zap Amore flexible way to kil
- Page 519 and 520:
24.18 exec 36.5 —JP If that happe
- Page 521 and 522:
24.20 unique name and any value you
- Page 523 and 524:
24.21 To override the default shell
- Page 525 and 526:
24.22 to open its menus (5.17). If
- Page 527 and 528:
24.22 #!/bin/sh pidfile=/tmp/.nup-p
- Page 529 and 530:
25.2 • For processes that only ne
- Page 531 and 532:
25.2 If the first character in an e
- Page 533 and 534:
25.2 In case you’re curious, thes
- Page 535 and 536:
25.5 25.4 Including Standard Input
- Page 537 and 538:
25.8 Note that atq has no objection
- Page 539 and 540:
25.9 foreach 28.9 —JP % foreach n
- Page 541 and 542:
26.1 System performance degrades wh
- Page 543 and 544:
26.2 26.2 Timing Programs Two comma
- Page 545 and 546:
26.3 tee 43.8 stty lesleys ttypa 0.
- Page 547 and 548:
26.5 On most systems, no user can d
- Page 549 and 550:
26.5 System V C Shell nice System V
- Page 551:
Part VI VI.Scripting Part VI contai
- Page 554 and 555:
27.2 • File permissions are set i
- Page 556 and 557:
27.3 Shell Search Paths As article
- Page 558 and 559:
27.5 ures out that an input file an
- Page 560 and 561:
27.7 Searching the path (27.6) take
- Page 562 and 563:
27.8 But there’s a loophole. The
- Page 564 and 565:
27.10 What if you want the external
- Page 566 and 567:
27.11 % unalias unalias foo unalias
- Page 568 and 569:
27.12 You also need to know how man
- Page 570 and 571:
27.12 Multiline Quoting Once you ty
- Page 572 and 573:
27.13 How Quoting Works Table 27-2
- Page 574 and 575:
27.16 This command will display eac
- Page 576 and 577:
27.17 ter that is also used by the
- Page 578 and 579:
27.17 Table 27-3. Special character
- Page 580 and 581:
27.18 27.18 How Many Backslashes? T
- Page 582 and 583:
Chapter 28 Saving Time on the Comma
- Page 584 and 585:
28.3 After the interruption, I just
- Page 586 and 587:
28.4 • In zsh, {} also understand
- Page 588 and 589:
28.5 • :g makes the operation glo
- Page 590 and 591:
28.6 General Example: Filename Comp
- Page 592 and 593:
28.6 MH mail folders can be stored
- Page 594 and 595:
28.8 28.8 Repeating Commands Let’
- Page 596 and 597:
28.9 cat - 12.2 Press RETURN to see
- Page 598 and 599:
28.11 —JP 28.11 Repeating a Time-
- Page 600 and 601:
28.13 Here’s an example with zsh,
- Page 602 and 603:
28.14 The -l option lists each file
- Page 604 and 605:
28.16 As an example, here’s a ser
- Page 606 and 607:
28.17 Then xargs would run all of t
- Page 608 and 609:
28.18 Dialback It is surprising how
- Page 610 and 611:
28.18 Expect comes with several exa
- Page 612 and 613:
29.3 Note that aliases are not pass
- Page 614 and 615:
29.4 This alias has two arguments:
- Page 616 and 617:
29.6 29.6 zsh Aliases zsh has the r
- Page 618 and 619:
29.8 Alias options You aren’t lim
- Page 620 and 621:
29.10 • Renames any old prog file
- Page 622 and 623:
29.11 sed -n '/^;; ANSWER SECTION:/
- Page 624 and 625:
29.11 fac.sh The fac function calcu
- Page 626 and 627:
29.13 function, make an alias with
- Page 628 and 629:
29.13 to FPATH if it doesn’t find
- Page 630 and 631:
29.13 zsh The zsh system is mostly
- Page 632 and 633:
29.14 Here’s the same cps—store
- Page 634 and 635:
30.2 Most shells—except the origi
- Page 636 and 637:
30.5 In the first command line (co)
- Page 638 and 639:
30.7 $ rm !20:$ rm /tmp/0444-diff.t
- Page 640 and 641:
30.8 % echo xy xy % !:s/xy/yx echo
- Page 642 and 643:
30.8 This alias will pipe the outpu
- Page 644 and 645:
30.9 —DR In this example, we told
- Page 646 and 647:
30.12 30.12 Picking Up Where You Le
- Page 648 and 649:
30.13 ing numbers, so it can be rea
- Page 650 and 651:
30.14 you want to; its original ver
- Page 652 and 653:
30.14 "^X^D" -> list-choices-raw Ar
- Page 654 and 655:
30.14 There’s a complete list of
- Page 656 and 657:
30.16 An obvious point: you can set
- Page 658 and 659:
31.2 31.2 Using Relative and Absolu
- Page 660 and 661:
31.3 31.3 What Good Is a Current Di
- Page 662 and 663:
31.5 The current directory has i-nu
- Page 664 and 665:
31.7 break terminates the loop and
- Page 666 and 667:
31.8 The dirs command prints the di
- Page 668 and 669:
31.10 In the next example, trying t
- Page 670 and 671:
31.12 In fact, using echo (27.5) yo
- Page 672 and 673:
31.13 where the .global_enter file
- Page 674 and 675:
32.2 • Chapter 20, Batch Editing
- Page 676 and 677:
32.3 second character in the string
- Page 678 and 679:
32.5 [The situation is complicated
- Page 680 and 681:
32.7 32.7 Regular Expressions: Matc
- Page 682 and 683:
32.11 At first glance, it might see
- Page 684 and 685:
32.13 32.13 Regular Expressions: Re
- Page 686 and 687:
32.16 directory tree beneath it. IM
- Page 688 and 689:
32.17 32.17 Just What Does a Regula
- Page 690 and 691:
32.19 However, the pattern ends up
- Page 692 and 693:
32.21 Table 32-5. Valid metacharact
- Page 694 and 695:
32.21 with a large complement of GN
- Page 696 and 697:
32.21 Table 32-10. Search and repla
- Page 698 and 699:
33.2 • Wildcards can appear in an
- Page 700 and 701:
33.3 Table 33-1. Filename wildcards
- Page 702 and 703:
33.4 Some versions of tar understan
- Page 704 and 705:
33.6 33.6 Getting a List of Matchin
- Page 706 and 707:
33.8 #!/bin/sh case $# in vgrep 0|1
- Page 708 and 709:
Chapter 34 The sed Stream Editor 34
- Page 710 and 711:
34.4 Given filenames, sed will read
- Page 712 and 713:
34.5 runsed only modifies a file if
- Page 714 and 715:
34.6 An exclamation mark following
- Page 716 and 717:
34.9 When either the search pattern
- Page 718 and 719:
34.11 The ampersand makes it possib
- Page 720 and 721:
34.13 Note that without the numeric
- Page 722 and 723:
34.14 Look at the script: /^/H /^/
- Page 724 and 725:
34.15 s/.*the \(.*\) statement.*/\1
- Page 726 and 727:
34.16 In this example, we know wher
- Page 728 and 729:
34.17 It excludes the last line ($)
- Page 730 and 731:
34.18 For instance, the N command t
- Page 732 and 733:
34.19 The core of the script is bas
- Page 734 and 735:
34.20 Because program examples are
- Page 736 and 737:
34.22 always-true s///.” Try the
- Page 738 and 739:
Chapter 35 Shell Programming for th
- Page 740 and 741:
35.2 35.2 Everyone Should Learn Som
- Page 742 and 743:
35.3 • Test a program’s exit st
- Page 744 and 745:
35.3 printenv env By convention, th
- Page 746 and 747:
35.5 PRINTER (45.4) or LPDEST can b
- Page 748 and 749:
35.6 35.6 The PATH Environment Vari
- Page 750 and 751:
35.8 In PATH, an empty entry (::) s
- Page 752 and 753:
35.9 Just as some programs use cert
- Page 754 and 755:
35.11 Here are more details about h
- Page 756 and 757:
35.13 bash and zsh have a handy way
- Page 758 and 759:
35.14 #!/bin/sh if cp "$1" "$1.bak"
- Page 760 and 761:
35.16 catsaway /dev/null 43.12 Loop
- Page 762 and 763:
35.17 case $# in 1) gzcat "$1" >$te
- Page 764 and 765:
35.19 35.19 Shell Script “Wrapper
- Page 766 and 767:
35.20 The third argument has a perf
- Page 768 and 769:
35.22 The first pass through the fo
- Page 770 and 771:
35.23 35.23 Loop Control: break and
- Page 772 and 773:
35.25 The first argument to set, --
- Page 774 and 775:
35.25 If the first parameter you se
- Page 776 and 777:
35.27 Be sure to leave space betwee
- Page 778 and 779:
35.30 35.30 Using Shell Functions i
- Page 780 and 781:
35.30 —SJC echo "couldn't find MX
- Page 782 and 783:
36.2 • Next is an assortment of a
- Page 784 and 785:
36.4 Let’s run both commands and
- Page 786 and 787:
36.6 exec also manipulates file des
- Page 788 and 789:
36.8 Several Bourne-type shells hav
- Page 790 and 791:
36.11 The portable way to unset all
- Page 792 and 793:
36.13 The dirname command strips th
- Page 794 and 795:
36.15 When the Unix kernel starts a
- Page 796 and 797:
36.16 36.16 n>&m: Swap Standard Out
- Page 798 and 799:
36.16 $ var=`grep "Joe" afone bfoen
- Page 800 and 801:
36.18 36.18 Shell Scripts On-the-Fl
- Page 802 and 803:
36.21 36.21 Quick Reference: expr e
- Page 804 and 805:
36.22 Truncate $x if it contains fi
- Page 806 and 807:
36.23 Notice that the inner double
- Page 808 and 809:
36.24 I want the number 99 from the
- Page 810 and 811:
36.25 36.25 Testing Two Strings wit
- Page 812 and 813:
36.27 (Here’s a fun enhancement,
- Page 814 and 815:
36.27 But if the lockfile is read-o
- Page 816 and 817:
37.1 Do you want to save the debugg
- Page 818 and 819:
37.4 The zero trick doesn’t work
- Page 820 and 821:
37.5 For the special case of iterat
- Page 822 and 823:
37.7 Unix’s internal routines com
- Page 824 and 825:
37.9 37.9 Making an Arbitrary-Size
- Page 827 and 828:
Chapter 38 - 38 Backing Up Files 38
- Page 829 and 830:
38.3 Accidents and oversights happe
- Page 831 and 832:
38.5 backups (of the files on your
- Page 833 and 834:
38.5 can then use tar again to add
- Page 835 and 836:
38.6 many bytes to achieve compress
- Page 837 and 838:
38.7 But the best solution is never
- Page 839 and 840:
38.9 The answer I came up with was
- Page 841 and 842:
38.10 GNU tar Here’s another subt
- Page 843 and 844:
38.11 Here’s an example. We’re
- Page 845 and 846:
38.13 In this command, keepout goes
- Page 847 and 848:
38.14 Note also that full-scale bac
- Page 849 and 850:
39.2 39.2 Using tar to Create and U
- Page 851 and 852:
39.2 mt/mt.o mt/mt On some tars, if
- Page 853 and 854:
39.3 No extraction is being done he
- Page 855 and 856:
39.5 developers from around the wor
- Page 857 and 858:
39.6 This brief overview left out a
- Page 859 and 860:
39.8 which cvsroot you used for a p
- Page 861 and 862:
39.8 sees that the copy in the repo
- Page 863 and 864:
40.1 Table 40-1. FHS root subdirect
- Page 865 and 866:
40.5 makefile is modified to fit th
- Page 867 and 868:
40.5 Figure 40-2. Choosing the acce
- Page 869 and 870:
40.5 Figure 40-3. The introduction
- Page 871 and 872:
40.5 Figure 40-6. The dependency re
- Page 873 and 874:
40.6 The host part of the URI and t
- Page 875 and 876:
40.7 The default use of wget downlo
- Page 877 and 878:
40.10 40.9 Installation with FreeBS
- Page 879 and 880:
Chapter 41 41 Perl 41.1 High-Octane
- Page 881 and 882:
41.3 Characteristics of this binary
- Page 883 and 884:
41.4 Example 41-1. A sample Perl sc
- Page 885 and 886:
41.5 Perl allows for user defined s
- Page 887 and 888:
41.5 Table 41-3. Numerical operator
- Page 889 and 890:
41.5 tioned: @INC and @ARGV. Since
- Page 891 and 892:
41.5 Example 41-7. Iterating over a
- Page 893 and 894:
41.6 Sometimes you need to iterate
- Page 895 and 896:
41.7 Table 41-8. Common Perl regula
- Page 897 and 898:
41.8 One advantage Perl has over sh
- Page 899 and 900:
41.9 This section hardly scratched
- Page 901 and 902:
41.10 41.10 Perl Boot Camp, Part 7:
- Page 903 and 904:
41.11 The CPAN module also has an i
- Page 905 and 906:
41.12 41.12 Make Custom grep Comman
- Page 907 and 908:
41.13 $content will be empty, and t
- Page 909 and 910:
Chapter 42 42 Python 42.1 What Is P
- Page 911 and 912:
42.3 Modules that are not packaged
- Page 913 and 914:
42.3 If you use functions like map(
- Page 915 and 916:
42.3 Given that a Python module is
- Page 917 and 918:
42.6 urllib also provides a functio
- Page 919 and 920:
42.9 To get to information submitte
- Page 921:
42.10 plex the system you’re tryi
- Page 925 and 926:
Chapter 43 43 Redirecting Input and
- Page 927 and 928:
43.1 Be aware that: • While stand
- Page 929 and 930:
43.4 the background, save the outpu
- Page 931 and 932:
43.5 The better way to do this is t
- Page 933 and 934:
43.7 The noclobber variable has one
- Page 935 and 936:
43.10 43.9 How to tee Several Comma
- Page 937 and 938:
43.11 43.11 Named Pipes: FIFOs mkfi
- Page 939 and 940:
43.12 • Empty another file. Just
- Page 941 and 942:
44.2 # FreeBSD atapci0: port 0xffa
- Page 943 and 944:
44.4 CONFIG_BLK_DEV_IDEPCI=y CONFIG
- Page 945 and 946:
44.5 own filesystems with a forest
- Page 947 and 948:
44.7 Then, as a normal user in grou
- Page 949 and 950:
44.10 For more details on NFS on yo
- Page 951 and 952:
44.13 Platforms that provide a user
- Page 953 and 954:
44.14 FreeBSD’s handbook has a ch
- Page 955 and 956:
45.2 The first few articles in this
- Page 957 and 958:
45.3 The message on lp indicates th
- Page 959 and 960:
45.5 There are two ways to choose a
- Page 961 and 962:
45.6 -m Merge files, printing one i
- Page 963 and 964:
45.9 45.8 Printing Over a Network S
- Page 965 and 966:
45.10 45.10 Introduction to Typeset
- Page 967 and 968:
45.12 45.12 Typesetting Manpages: n
- Page 969 and 970:
45.14 Much like the nroff input ear
- Page 971 and 972:
45.16 Here’s an example of using
- Page 973 and 974:
45.19 subjects. Don’t be fooled b
- Page 975 and 976:
45.19 There are far too many progra
- Page 977 and 978:
46.1 IP identifies machines through
- Page 979 and 980:
46.3 telnet 23/udp smtp 25/tcp mail
- Page 981 and 982:
46.4 This shows us the address (A)
- Page 983 and 984:
46.6 46.6 Secure Shell (SSH) telnet
- Page 985 and 986:
46.9 sendmail is the most well know
- Page 987 and 988:
46.10 % dig oreilly.com ns ... ;; A
- Page 989 and 990:
46.12 into the correct private addr
- Page 991 and 992:
Chapter 47 47 Connecting to MS Wind
- Page 993 and 994:
47.2 [global] workgroup = MYGROUP ;
- Page 995 and 996:
47.3 47.3 Securing Samba The topic
- Page 997 and 998:
47.4 Figure 47-1. SWAT’s globals
- Page 999 and 1000:
47.7 47.6 Connecting to SMB Shares
- Page 1001 and 1002:
47.7 Figure 47-2. Unix VNC client c
- Page 1003 and 1004:
47.9 47.9 Citrix: Making Windows Mu
- Page 1005 and 1006:
47.9 Figure 47-4. Creating a new en
- Page 1007:
Part IX IX.Security Part IX contain
- Page 1010 and 1011:
48.2 How many times have you accide
- Page 1012 and 1013:
48.4 48.4 What We Mean by Buffer Ov
- Page 1014 and 1015:
48.6 How simple is it to access con
- Page 1016 and 1017:
48.6 Within FreeBSD and other Unix
- Page 1018 and 1019:
48.8 You can search for modified fi
- Page 1020 and 1021:
48.11 48.11 Disallow rlogin and rsh
- Page 1022 and 1023:
Chapter 49 Root, Group, and User Ma
- Page 1024 and 1025:
49.3 In Linux, Solaris, and other s
- Page 1026 and 1027:
49.6 How does Unix determine what g
- Page 1028 and 1029:
49.7 $ ls -ln total 37 -rw-r--r-- 1
- Page 1030 and 1031:
49.9 However, a quick check shows t
- Page 1032 and 1033:
49.12 Examples of aliases are: User
- Page 1034 and 1035:
Chapter 50 File Security, Ownership
- Page 1036 and 1037:
50.2 The first character in the ls
- Page 1038 and 1039:
50.3 Which Group is Which? Since gr
- Page 1040 and 1041:
50.5 50.5 Using chmod to Change Fil
- Page 1042 and 1043:
50.7 That means “for all files (*
- Page 1044 and 1045:
50.10 I couldn’t write the file u
- Page 1046 and 1047:
50.11 This setup can still be a lit
- Page 1048 and 1049:
50.12 md5sum The easy way is to com
- Page 1050 and 1051:
50.15 If you need to change ownersh
- Page 1052 and 1053:
51.3 SSH works by authenticating th
- Page 1054 and 1055:
51.5 Q: How do I authenticate witho
- Page 1056 and 1057:
51.5 Q: Trusted-host authentication
- Page 1058 and 1059:
51.5 Q: Public-key authentication i
- Page 1060 and 1061:
51.6 Q: Each time I run ssh-keygen,
- Page 1062 and 1063:
51.7 Q: I changed the sshd config f
- Page 1064 and 1065:
51.7 Q: ssh1 prints “Cannot fork
- Page 1066 and 1067:
51.7 Don’t rely on shell quirks a
- Page 1068 and 1069:
51.7 To fix this problem, be sure y
- Page 1070 and 1071:
Glossary AIX A version of Unix from
- Page 1072 and 1073:
flag flag In programming, a flagvar
- Page 1074 and 1075:
portable Sun OS also provide “nam
- Page 1076 and 1077:
word word Similar to a word in a sp
- Page 1078 and 1079:
\ (backslash) \< \> (regular expres
- Page 1080 and 1081:
# (hash mark) (continued) in commen
- Page 1082 and 1083:
agents -agent option, ssh, 799 comp
- Page 1084 and 1085:
awk utility (continued) line-number
- Page 1086 and 1087:
ind (Berkeley Internet Name Daemon)
- Page 1088 and 1089:
checksed script, 671 chess script,
- Page 1090 and 1091:
in .logout file, 89 logout file, cr
- Page 1092 and 1093:
with vi editor, 313 xclipboard, usi
- Page 1094 and 1095:
functions calling functions, 583-58
- Page 1096 and 1097:
df command, 501 output, parsing wit
- Page 1098 and 1099:
dump command arguments, correct ord
- Page 1100 and 1101:
AT, 54 CBLKWID (comment block width
- Page 1102 and 1103:
exiting directories, automatic setu
- Page 1104 and 1105:
searching by column, using awk, 258
- Page 1106 and 1107:
anonymous FTP server, configuring,
- Page 1108 and 1109:
hardware, 900 dialup PPP sessions,
- Page 1110 and 1111:
inheritance process information, 45
- Page 1112 and 1113:
daemons, 14-16 modules for device d
- Page 1114 and 1115:
linkname, ln command and, 208 links
- Page 1116 and 1117:
in shell functions, 581 loosely typ
- Page 1118 and 1119:
methods, 844 Python, 873 Microsoft
- Page 1120 and 1121:
as argument separators, 527 awk pro
- Page 1122 and 1123:
| in extended regular expressions,
- Page 1124 and 1125:
processes, 974 swap space, 975 virt
- Page 1126 and 1127:
converting source files, 932 lp and
- Page 1128 and 1129:
checking current processes for secu
- Page 1130 and 1131:
shell output and errors into tempor
- Page 1132 and 1133:
login utility, 141 disabling for se
- Page 1134 and 1135:
in .cshrc.$HOST file, 60 FPATH (for
- Page 1136 and 1137:
unning commands at, 90 multiline co
- Page 1138 and 1139:
edirecting standard I/O (see redire
- Page 1140 and 1141:
into fields, 766 SPOOL (Simultaneou
- Page 1142 and 1143:
success or failure of commands, ind
- Page 1144 and 1145:
history (see history of commands) l
- Page 1146 and 1147:
timing programs, 503 tip program, 5
- Page 1148 and 1149:
values, Python objects, 873 /var di
- Page 1150 and 1151:
newline character, 27 removing from
- Page 1152 and 1153:
xmodmap program, 105, 127 defining
- Page 1154 and 1155:
1114 Index This is the Title of the
- Page 1156:
David Futato designed the interior