- Page 1 and 2: Crouching Yeti — Appendixes Kaspe
- Page 3 and 4: 3 I. Appendix 1: Indicators of comp
- Page 5 and 6: 5 II. Appendix 2: Havex loader - de
- Page 7 and 8: 7 030: 309276719429789193750028F978
- Page 9 and 10: 9 Decoded RSA 1024 bit key: 0000000
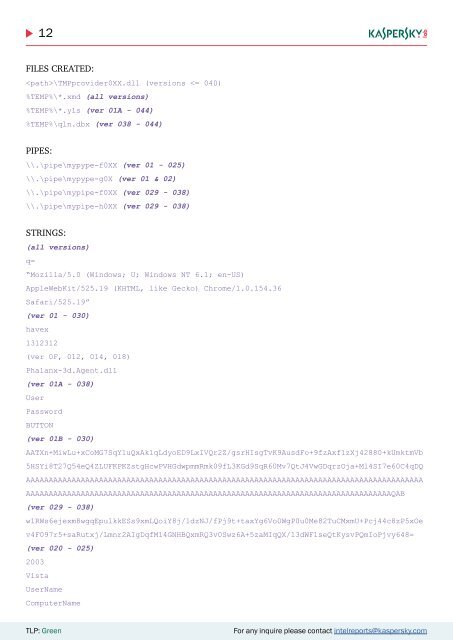
- Page 11: 11 • Running Processes • Proxy
- Page 15 and 16: 15 version 029 3x1 version 030 3x1
- Page 17 and 18: 17 CLSID: UserType: VerIndProgID:
- Page 19 and 20: 19 Config in stored in resource WRT
- Page 21 and 22: 21 compiled: Thu, 02 Feb 2012 09:50
- Page 23 and 24: 23 the RSAeuro library. They recomp
- Page 25 and 26: 25 N parameter in one sample: The E
- Page 27 and 28: 27 Havex sample details by version
- Page 29 and 30: 29 Compiled: Mon, 07 Nov 2011 09:40
- Page 31 and 32: 31 SHA-256: 8d343be0ea83597f041f9cb
- Page 33 and 34: 33 SHA-256: 0f4046be5de15727e8ac786
- Page 35 and 36: 35 Compiled: Tue, 10 Jan 2012 14:04
- Page 37 and 38: 37 SHA-256: 72ff91b3f36ccf07e3daf67
- Page 39 and 40: 39 Compiled: C2 URLs: Mon, 12 Mar 2
- Page 41 and 42: 41 Compiled: Fri, 26 Oct 2012 10:12
- Page 43 and 44: 43 www.idweb.ru/assets/modules/docm
- Page 45 and 46: 45 C2 URLs: www.pc-service-fm.de/mo
- Page 47 and 48: 47 III. Appendix 3: The Sysmain bac
- Page 49 and 50: 49 antibioticsdrugstore.com/err/log
- Page 51 and 52: 51 The path to this file is saved i
- Page 53 and 54: 53 • “dll”: load dll sent fro
- Page 55 and 56: 55 index.cgi/?loc=258 • Get systi
- Page 57 and 58: 57 V. Appendix 5: The ClientX backd
- Page 59 and 60: 59 public string[] servers; public
- Page 61 and 62: 61 Once it is done filling the prSe
- Page 63 and 64:
63 5.5.3 TIM The TIM command is res
- Page 65 and 66:
65 VI. Appendix 6: Karagany backdoo
- Page 67 and 68:
67 • Xfrost • Killklg List of s
- Page 69 and 70:
69 Main Features: * Full Screen Cap
- Page 71 and 72:
71 VII. Appendix 7: C&C Analysis Th
- Page 73 and 74:
73 VIII. Appendix 8: Victim identif
- Page 75 and 76:
75 Victim 24 Areas of activity: rec
- Page 77 and 78:
77 Victim 49 Telecommunications and
- Page 79 and 80:
79 Victim 75 University in Taiwan.
- Page 81 and 82:
81 IX. Appendix 9: Hashes Havex, Sy
- Page 83 and 84:
83 c66525285707daff30fce5d79eb1bdf3
- Page 85 and 86:
85 ClientX: 66ab3a26ffe5d9fb72083dc
- Page 87 and 88:
87 data\sydmain.dll”,AGTwLoad eWo
- Page 89 and 90:
89 Path: %TEMP%\qln.dbx Size: 2 Des
- Page 91 and 92:
91 SHA-256: e94b97716d354a21dcff365
- Page 93 and 94:
93 After the strcat call values sma
- Page 95 and 96:
95 And when decoded, the contents o
- Page 97 and 98:
97 kool.jar ¦ fcswzHCx.class, 330
- Page 99 and 100:
99 The encoding algo was a simple a
- Page 101 and 102:
101 The decoded strings here: TLP:
- Page 103 and 104:
103 f0.appendChild(document.createE
- Page 105 and 106:
105 10.5. Related Targeted Software
- Page 107 and 108:
107 the relevant code is called in
- Page 109 and 110:
109 Exploit URL roxsuite.com/compon
- Page 111 and 112:
111 Compromised Referrer Referrer P
- Page 113 and 114:
113 Compromised Referrer Referrer P
- Page 115 and 116:
115 XII. Appendix 12: Previous and