Kaspersky_Lab_crouching_yeti_appendixes_eng_final
Kaspersky_Lab_crouching_yeti_appendixes_eng_final
Kaspersky_Lab_crouching_yeti_appendixes_eng_final
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
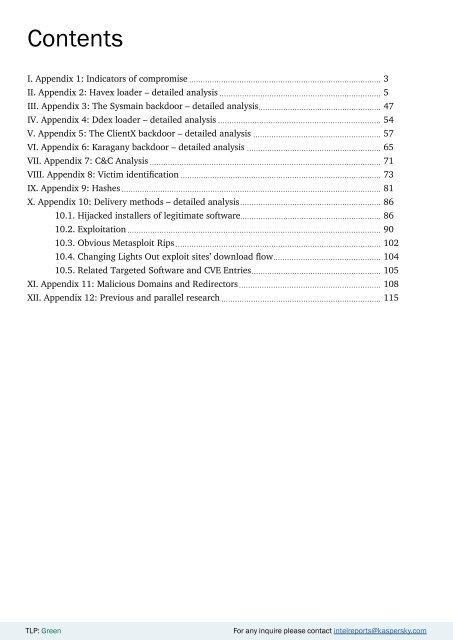
Contents<br />
I. Appendix 1: Indicators of compromise 3<br />
II. Appendix 2: Havex loader – detailed analysis 5<br />
III. Appendix 3: The Sysmain backdoor – detailed analysis 47<br />
IV. Appendix 4: Ddex loader – detailed analysis 54<br />
V. Appendix 5: The ClientX backdoor – detailed analysis 57<br />
VI. Appendix 6: Karagany backdoor – detailed analysis 65<br />
VII. Appendix 7: C&C Analysis 71<br />
VIII. Appendix 8: Victim identification 73<br />
IX. Appendix 9: Hashes 81<br />
X. Appendix 10: Delivery methods – detailed analysis 86<br />
10.1. Hijacked installers of legitimate software 86<br />
10.2. Exploitation 90<br />
10.3. Obvious Metasploit Rips 102<br />
10.4. Changing Lights Out exploit sites’ download flow 104<br />
10.5. Related Targeted Software and CVE Entries 105<br />
XI. Appendix 11: Malicious Domains and Redirectors 108<br />
XII. Appendix 12: Previous and parallel research 115<br />
TLP: Green<br />
For any inquire please contact intelreports@kaspersky.com