Stefan Burschka Tranalyzer - SwiNOG
Stefan Burschka Tranalyzer - SwiNOG
Stefan Burschka Tranalyzer - SwiNOG
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
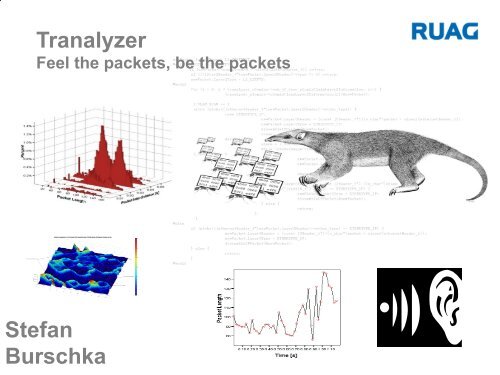
<strong>Tranalyzer</strong><br />
Feel the packets, be the packets<br />
<strong>Stefan</strong><br />
<strong>Burschka</strong>
What we do:<br />
Network Troubleshooting, Security:<br />
l<br />
l<br />
l<br />
l<br />
TRANALYZER(T2/3): High Speed and Volume Traffic Analyzer<br />
TRAVIZ: Graphical Toolset for <strong>Tranalyzer</strong><br />
Complete Tool Sets for Traffic Mining (TM), Forensics<br />
Artificial Intelligence<br />
Research: TM & Visualisation<br />
Brain support 4 multi-dim datasets<br />
Encrypted Traffic Mining<br />
Operational Picture<br />
Malware and covert channel detection<br />
Nifty stuff<br />
2
“It's the network – go fix it!”<br />
l 3
The Network is slow, The Network is insecure;<br />
NO, it's not Microsoft, shut up, It wasn't me ...<br />
Manager (MBA)<br />
Always right, DoR<br />
License to Powerpoint<br />
Production (poor Techie)<br />
Knows, Always warned,<br />
Always his fault: FUBAR<br />
License to get fired<br />
Finance (MBA)<br />
Knows basic calculus<br />
License to Excel<br />
We didn't find the problem in 4 months, can you do the job<br />
in 2 weeks? (We supply 20TB data)
Troubleshooting, Security<br />
Traffic Mining: Change your perspective<br />
5
6<br />
What is wrong here?
See the disaster now?<br />
Now you have context!<br />
7
Traffic Mining(TM):<br />
Hidden Knowledge: Listen | See, Understand, Invariants, Model<br />
Application in<br />
– Troubleshooting, Security (Classification, Encrypted TM )<br />
– Netzwerk usage (VoiP, P2P traffic shaping, application/user profiling)<br />
– Profiling & Marketing (usage performance- & market- index)<br />
– Law enforcement and Legal Interception (Indication/Evidence)<br />
8
Basic Need: Versatile Flow Compression<br />
A<br />
B<br />
Definition: (6-Tuple)<br />
Vlan(s), srcIP, srcpPort, dstIP, dstPort, L4Protocol<br />
Or why not a bit more context and meaning ?<br />
srcWho, dstWho<br />
srcNetwork, dstNetwork<br />
Bad, Good<br />
Internal / External<br />
9
Closed source loud Tools<br />
Netflow (Sometimes not so loud, comes with routers)<br />
Pro: Good hands-on tool, flow statistics, header parameters, standard<br />
Cons: Not all statistics we need, no developer support<br />
GigaStor (Horrible loud and exceptional expensive HW)<br />
Pro: heuristic expert system, Graphics, reports, whatever is in the DB<br />
Cons: What we needed is not in the DB, no developer support<br />
DPI (Elacoya, Sandvine,..) (Terrible loud and expensive HW)<br />
Pro: good protocol resolution, nice reports<br />
Cons: Its a DPI not a verstile flow engine with developer support<br />
10
Open source silent SW<br />
Wireshark, T-Shark (packet, flow statistics)<br />
Pro: Hands-on tool, protocol db, GUI, command line, filtering<br />
Cons: Limited flow statistics and file size, post processing difficult<br />
Silk (flow based)<br />
Cons: Not even close to Netflow, 5 tuple, esoteric config<br />
Netmate<br />
Pro: Flow, packet based, nice features,<br />
Cons: Config , handling, 5 tuple, that is, ... University<br />
NTOP(ng)<br />
Pro: Monitoring, flow statistics, config, GUI, Graphics<br />
Cons: not really flow based as we need it, protocol encapsulation?<br />
IDS (SNORT, BRO)<br />
Pro: Alarming, regex, flexible<br />
11<br />
Cons: Alarming, no Flows, BRO: memory leaks, university stuff
Need an Allrounder, script friendly<br />
between Wireshark, Netflow and<br />
2006: Somebody has<br />
to develop me !!
•<br />
<strong>Tranalyzer</strong>2(T2), C99, (Geek/Dev/Prof)<br />
High Volume Traffic Preprocessing and Troubleshooting<br />
Open Source<br />
Speed and Memory optimized by *.h“, config and ./autogen.sh -n<br />
Command line based, full pcap, eth and dag cards<br />
Post processing : HEX, ‘text \t’; Bash, AWK, Perl, … friendly<br />
C Plugin based, Linux, Mac, (Windoof)<br />
Subnet labeling (Who, Where, What)<br />
BPF<br />
Hands-on: Anomaly and security related flags<br />
Researchers: Full Statistical and Packet Signal Analysis support<br />
Interfaces: Matlab, GnuPlot, SPSS, Excel, oocacl, soon Netflow tools<br />
The “-s” option: The command line AWK, Perl friendly packet mode<br />
GUI: Traviz (http://sourceforge.net/projects/traviz)<br />
Easy to use but, You have to know your shit<br />
• 13
T3, C99, (Geek/Normalo NonDev/Prof)<br />
High Speed and Volume Troubleshooting, Security, Monitoring<br />
Complete new Concept and Design<br />
Full IPv4/6, more protocols as T2<br />
Basic Features from T2 + new nifty Plugins<br />
Full Subnet labeling and flexible flow aggregation<br />
Multi Threading and Interface: High performance<br />
GUI Support via professional Tool Set: Unlimited flows and files<br />
ipSOM: AI Tool Set to answer ANY question<br />
Core functions into DSP and FPGA in future for the 40Gig+<br />
More non geek/dev user friendly but,<br />
You still have to know your shit<br />
• 14
Report T2<br />
•/tranalyzer -r ~/wurst/data/weichwurst.dmp -w ~/wurst/results/hartwurst<br />
================================================================================<br />
<strong>Tranalyzer</strong> 0.5.8 (Anteater), beta. PID: 6123<br />
• ================================================================================<br />
Active plugins:<br />
00: protocolStatistics, version 0.5.8 --> _protocols.txt, ports.txt<br />
01: basicFlowOutput, version 0.5.8 --> _flow.txt / bin subnet.txt<br />
02: macRecorder, version 0.5.0 --> _flow.txt / bin<br />
03: portBasedClassifier, version 0.5.8 --> _flow.txt / bin, portmap.txt<br />
04: basicLayer4CalcStatistics, version 0.5.6 --> _flow.txt / bin<br />
05: tcpFlags, version 0.5.8 --> _flow.txt / bin<br />
06: tcpStates, version 0.5.6 --> _flow.txt / bin<br />
07: icmpDecode, version 0.5.8 --> _flow.txt / bin, _icmpStats.txt<br />
08: connectionCounter, version 0.5.5 --> _flow.txt / bin<br />
09: descriptiveStatistics, version 0.5.6 --> _flow.txt / bin<br />
10: nFirstPacketsStats, version 0.5.8 --> _flow.txt / bin<br />
11: packetSizeInterArrivalTimeHisto, version 0.5.8 --> _flow.txt / bin<br />
12: standardFileSink, version 0.5.0 --> creates text output _flow.txt<br />
13: textFileSink, version 0.5.8 --> creates binary output _flow.bin<br />
Start processing file: /home/wurst//data/weichwurst.dmp<br />
BPF: (null)<br />
Dump start: 1351794649.186547 sec : Wed 01 Nov 2012 18:30:49.186547<br />
Shutting down <strong>Tranalyzer</strong> 0.5.8...<br />
Dump stop: 1351837376.118852 sec : Thu 02 Nov 2012 06:22:42.118852<br />
Total dump duration: 42712.932305 sec<br />
Number of processed packets: 6497970<br />
Number of processed traffic bytes: 1749617780<br />
Number of ARP packets: 1603<br />
Number of RARP packets: 5<br />
Number of IPv4 fragmented packets: 299<br />
Number of IPv6 packets: 0<br />
Number of IPv4 flows: 3395325<br />
Average snapped Bandwidth: 327.634 KBit/s<br />
Average full IP Bandwidth: 326.386 Kbit/s<br />
Warning: IPv4 Fragmentation header packet missing<br />
• 15
T2 Protocol File<br />
Total packets captured: 42278<br />
L4 Protocol # Packets Relative Frequency[%] Protocol description<br />
1 21 0.049671 Internet Control Message Protocol<br />
2 6 0.014192 Internet Group Management Protocol<br />
6 41698 98.628128 Transmission Control Protocol<br />
17 250 0.591324 User Datagram Protocol<br />
103 28 0.066228 Protocol Independent Multicast<br />
Total TCP packets: 41698<br />
Port # Packets Relative Frequency[%]<br />
80 41519 99.570723 World Wide Web HTTP<br />
445 8 0.019186 Win2k+ Server Message Block<br />
5557 147 0.352535<br />
Total UDP packets: 250<br />
Port # Packets Relative Frequency[%]<br />
53 2 0.800000 Domain Name Server<br />
137 50 20.000000 NETBIOS, [trojan] Msinit<br />
138 21 8.400000 NETBIOS Datagram Service<br />
1900 18 7.200000 SSDP<br />
1908 2 0.800000 Dawn<br />
1985 156 62.400000 Hot Standby Router Protocol<br />
• 16
T2 ICMP Stats File<br />
Total # of ICMP messages: 22258<br />
ICMP / Total traffic percentage[%]: 0.343<br />
Echo reply / request ratio: 0.892<br />
Type Code # of Messages Relative Frequency [%]<br />
ICMP_ECHOREQUEST - 111 0.499<br />
ICMP_ECHOREPLY - 99 0.445<br />
ICMP_SOURCE_QUENCH - 15 0.067<br />
ICMP_TRACEROUTE - 0 0.000<br />
ICMP_DEST_UNREACH ICMP_NET_UNREACH 60 0.270<br />
ICMP_DEST_UNREACH ICMP_HOST_UNREACH 15674 70.420<br />
ICMP_DEST_UNREACH ICMP_PROT_UNREACH 0 0.000<br />
ICMP_DEST_UNREACH ICMP_PORT_UNREACH 3100 13.928<br />
ICMP_DEST_UNREACH ICMP_FRAG_NEEDED 0 0.000<br />
ICMP_DEST_UNREACH ICMP_SR_FAILED 0 0.000<br />
ICMP_DEST_UNREACH ICMP_NET_UNKNOWN 0 0.000<br />
ICMP_DEST_UNREACH ICMP_HOST_UNKNOWN 0 0.000<br />
ICMP_DEST_UNREACH ICMP_HOST_ISOLATED 0 0.000<br />
ICMP_DEST_UNREACH ICMP_NET_ANO 8 0.036<br />
ICMP_DEST_UNREACH ICMP_HOST_ANO 600 2.696<br />
ICMP_DEST_UNREACH ICMP_NET_UNR_TOS 0 0.000<br />
ICMP_DEST_UNREACH ICMP_HOST_UNR_TOS 0 0.000<br />
ICMP_DEST_UNREACH ICMP_PKT_FILTERED 776 3.486<br />
ICMP_DEST_UNREACH ICMP_PREC_VIOLATION 0 0.000<br />
ICMP_DEST_UNREACH ICMP_PREC_CUTOFF 0 0.000<br />
ICMP_REDIRECT ICMP_REDIR_NET 1125 5.054<br />
ICMP_REDIRECT ICMP_REDIR_HOST 589 2.646<br />
ICMP_REDIRECT ICMP_REDIR_NETTOS 0 0.000<br />
ICMP_REDIRECT ICMP_REDIR_HOSTTOS 0 0.000<br />
ICMP_TIME_EXCEEDED ICMP_EXC_TTL 95 0.427<br />
ICMP_TIME_EXCEEDED ICMP_EXC_FRAGTIME 0 0.000<br />
ICMP_TRACEROUTE - 0 0.000<br />
• 17
T2 Flow Header File: Hands-On<br />
20 .....<br />
21 8:NR Minimum layer3 packet size<br />
22 8:NR Maximum layer3 packet size<br />
23 19:NR Average packet load ratio<br />
24 19:NR Send packets per second<br />
25 19:NR Send bytes per second<br />
26 19:NR Packet stream asymmetry<br />
27 19:NR Byte stream asymmetry<br />
28 8:NR IP Minimum delta IP ID<br />
29 8:NR IP Maximum delta IP ID<br />
30 7:NR IP Minimum TTL<br />
31 7:NR IP Maximum TTL<br />
32 7:NR IP TTL Change count<br />
33 13:NR IP Type of Service<br />
34 14:NR IP aggregated flags<br />
35 8:NR IP options count<br />
36 13,15:NR IP aggregated options<br />
• 18
T2 Flow Header View: Hands-On<br />
37 8:NR TCP packet seq count<br />
38 10:NR TCP sent seq diff bytes<br />
39 8:NR TCP sequence number fault count<br />
40 8:NR TCP packet ack count<br />
41 10:NR TCP flawless ack received bytes<br />
42 8:NR TCP ack number fault count<br />
43 8:NR TCP initial window size<br />
44 19:NR TCP average window size<br />
45 8:NR TCP minimum window size<br />
46 8:NR TCP maximum window size<br />
47 8:NR TCP window size change down count<br />
48 8:NR TCP window size change up count<br />
49 8:NR TCP window size direction change count<br />
50 13:NR TCP aggregated protocol flags (cwr, ecn, urgent, ack, push, reset, syn, fin)<br />
51 14:NR TCP aggregated header anomaly flags<br />
52 8:NR TCP options Packet count<br />
53 8:NR TCP options count<br />
54 15:NR TCP aggregated options<br />
55 8:NR TCP Maximum Segment Length<br />
56 7:NR TCP Window Scale<br />
57 19:NR TCP Trip Time Syn, Syn-Ack | Syn-Ack, Ack<br />
58 19:NR TCP Round Trip Time Syn, Syn-Ack, Ack | TCP Ack-Ack RTT<br />
59 19:NR TCP Ack Trip Min<br />
60 19:NR TCP Ack Trip Max<br />
61 19:NR TCP Ack Trip Average<br />
62 13:NR TCP aggregated protocol state flags<br />
63 15,14:NR ICMP Aggregated type & code bit field<br />
64 19:NR ICMP Echo reply/request success ratio<br />
65 9:NR Number of connections from source IP to different hosts<br />
66 9:NR Number of connections from destination IP to different hosts<br />
Yes I know, I should do something<br />
special for the TimeStamp option<br />
• 19
T2 Flow Header View: TM geeks<br />
68 19:NR Minimum packet length<br />
69 19:NR Maximum packet length<br />
70 19:NR Mean packet length<br />
71 19:NR Lower quartile of packet lengths<br />
72 19:NR Median of packet lengths<br />
73 19:NR Upper quartile of packet lengths<br />
74 19:NR Inter quartile distance of packet lengths<br />
75 19:NR Mode of packet lengths<br />
76 19:NR Range of packet lengths<br />
77 19:NR Standard deviation of packet lengths<br />
78 19:NR Robust standard deviation of packet lengths<br />
79 19:NR Skewness of packet lengths<br />
80 19:NR Excess of packet lengths<br />
81 19:NR Minimum inter arrival time<br />
82 19:NR Maximum inter arrival time<br />
83 19:NR Mean inter arrival time<br />
84 19:NR Lower quartile of inter arrival times<br />
85 19:NR Median inter arrival times<br />
86 19:NR Upper quartile of inter arrival times<br />
87 19:NR Inter quartile distance of inter arrival times<br />
88 19:NR Mode of inter arrival times<br />
89 19:NR Range of inter arrival times<br />
90 19:NR Standard deviation of inter arrival times<br />
91 19:NR Robust standard deviation of inter arrival times<br />
92 19:NR Skewness of inter arrival times<br />
93 19:NR Excess of inter arrival times<br />
All you never wanted to<br />
know about statistics in a<br />
flow<br />
L2/3/4/7<br />
configurable<br />
Packet<br />
Statistics<br />
94 8,25:R L2L3/L4/Payload( s. PACKETLENGTH in packetCapture.h) length and inter-arrival<br />
times for the N first packets<br />
95 8,9,9,9,9:R Packetsize Inter Arrival Time histogram bins<br />
• 20
HOW TO find the<br />
needle in the flow stack?<br />
Have a break have a<br />
HEX & ¦ scripting!
T2 Text Flow File: Basic plugins<br />
A 1196278772.439355 1196279184.642073 412.202718 0x9B42 22<br />
192.168.1.10 0x00000001 2119 68.3.4.5 0x800806034 80 6<br />
00:0f:1f:cf:7c:45_00:00:0c:07:ac:0a_6387 http 6387 8272 464<br />
5437587 0 4 15.494803 1.125660<br />
-0.128590 -0.999829 1 87 128 128 0x00 0x42<br />
0x0000 116 464 6231 4116 5437724 2253 63754<br />
64831.988281 62501 65535 3342 2904 5713 0x18<br />
0xF900 0x0000 0x03 0x00000000 0x0000 -1.0 1 1<br />
1 ...<br />
B 1196278772.409312 1196279184.642073 412.232761 0x9B43 22<br />
192.168.1.10 0x00000001 80 68.3.4.5 0x80080634 2119 6<br />
00:d0:00:64:d0:00_00:0f:1f:cf:7c:45_8272 http 8272 6387<br />
5437587 464 0 1380 20.066333 13190.574633<br />
0.128590 0.999829 1 3 63 63 0x00 0x42<br />
0x0000 8146 5440245 109 116 464 8104 5840<br />
5840.000000 65535 0 0 0 0 0x18 0x1B00<br />
0x0000 0x03 0x00000000 0x0000 -1.0 1 1 1 ...<br />
• 22
T2 Binary Coding Status:<br />
2^0 0x0001 Flow Warning Flag: If A flow: Invert Flow, NOT client flow<br />
2^1 0x0002 Dump/flow: L3 Snaplength too short<br />
2^2 0x0004 Dump/flow: L2 header length too short<br />
2^3 0x0008 Dump/flow: L3 header length too short<br />
2^4 0x0010 Dump: Warning: IP Fragmentation Detected<br />
2^5 0x0020 Flow: ERROR: Severe Fragmentation Error<br />
2^6 0x0040 Flow: ERROR: Fragmentation Header Sequence Error<br />
2^7 0x0080 Flow ERROR: Fragmentation Pending at end of flow<br />
2^8 0x0100 Flow/Dump: Warning: VLAN(s) detected<br />
2^9 0x0200 Flow/Dump: Warning: MPLS unicast detected<br />
2^10 0x0400 Flow/Dump: Warning: MPLS multicast detected<br />
2^11 0x0800 Flow/Dump: Warning: L2TP detected<br />
2^12 0x1000 Flow/Dump: Warning: PPP detected<br />
2^13 0x2000 Flow/Dump: 0/1: IPv4/IPv6 detected<br />
2^14 0x4000 Flow/Dump: Warning: Land Attack detected<br />
2^15 0x8000 Flow/Dump: Warning: Time Jump<br />
So what is:<br />
0x9B43<br />
• 23
T2 Flow Binary Coding: ipFlags<br />
2^0 0x0001 IP Options present, s. IP Options Type Bit field<br />
2^1 0x0002 IPID out of order<br />
2^2 0x0004 IPID rollover<br />
2^3 0x0008 Fragmentation: Below expected RFC minimum fragment size: 576<br />
2^4 0x0010 Fragmentation: Fragments out of range (Possible tear drop attack)<br />
2^5 0x0020 Fragmentation: MF Flag<br />
2^6 0x0040 Fragmentation: DF Flag<br />
2^7 0x0080 Fragmentation: x Reserved flag bit from IP Header<br />
2^8 0x0100 Fragmentation: Unexpected position of fragment (distance)<br />
2^9 0x0200 Fragmentation: Unexpected sequence of fragment<br />
2^10 0x0400 L3 Checksum Error<br />
2^11 0x0800 L4 Checksum Error<br />
2^12 0x1000 SnapLength Warning: IP Packet truncated, L4 Checksums invalid<br />
2^13 0x2000 Packet Interdistance == 0<br />
2^14 0x4000 Packet Interdistance < 0<br />
2^15 0x8000 Internal State Bit for Interdistance assessment<br />
So what is:<br />
0x1C21<br />
• 24
T2 Flow Binary Coding: tcpFlags<br />
2^0 0x01 FIN No more data, finish connection<br />
2^1 0x02 SYN Synchronize sequence numbers<br />
2^2 0x04 RST Reset connection<br />
2^3 0x08 PSH Push data<br />
2^4 0x10 ACK Acknowledgement field value valid<br />
2^5 0x20 URG Urgent pointer valid<br />
2^6 0x40 ECE ECN-Echo<br />
2^7 0x80 CWR Congestion Window Reduced flag is set<br />
2^0 0x0001 Fin-Ack Flag<br />
2^1 0x0002 Syn-Ack Flag<br />
2^2 0x0004 Rst-Ack Flag<br />
2^3 0x0008 Syn-Fin Flag, Scan or malicious packet<br />
2^4 0x0010 Syn-Fin-Rst Flag, potential malicious scan packet or malicious channel<br />
2^4 0x0020 Fin-Rst Flag, abnormal flow termination<br />
2^5 0x0040 Null Flag, potential NULL scan packet, or malicious channel<br />
2^6 0x0080 XMas Flag, potential Xmas scan packet, or malicious channel<br />
2^8 0x0100 Due to packet loss, Sequence Number Retry, retransmit<br />
2^9 0x0200 Sequence Number out of order<br />
2^10 0x0400 Sequence mess in flow order due to pcap pkt loss<br />
2^11 0x0800 Warning: L4 Option field corrupt or not acquired<br />
2^12 0x1000 Syn retransmission<br />
2^13 0x2000 Ack number out of order<br />
2^14 0x4000 Ack Packet loss, probably on the sniffing interface<br />
2^15 0x8000 Internal state: TCP Window Size Machine<br />
So what is: 0x1B 0xC403<br />
• 25
T2 Flow Binary Coding: icmpFlags<br />
Aggregated ICMP Type & Code bit Field<br />
So what is: 0x00000100_0x0001<br />
• 26
T2 Packet Signal: Encrypted VoIP Mining<br />
PacketLength_Packet-Interdistance; …<br />
1023_0.000000;758_0.030043;1380_0.110201;80_0.00000;369_0.000010;230_0.02002<br />
9;1380_0.070101;80_0.000000;50_0.060086;1380_0.070101;80_0.090130; …<br />
27<br />
Packet Length<br />
time<br />
Post processing scripts: /<br />
tranalyzer/trunk/scripts
T2 Statistical Application / User profiling<br />
Packet length-Interdistance Statistics: Fingerprint<br />
PktLen_Packet-IAT_cnt_cntPktLen_cntIAT; …<br />
• 0_0_2322_6271_2396;0_2_82_6271_90;0_4_114_6271_114;0_6_138_6271_140;0_8_162_6271_164;0_10_157_6271_160;0_12_220<br />
_6271_224;0_14_217_6271_222;0_16_325_6271_325;0_18_373_6271_376;0_20_493_6271_498;0_22_340_6271_343;0_24_238_627<br />
1_238;0_26_283_6271_284;0_28_143_6271_143;0_30_114_6271_114;0_32_139_6271_140;0_34_175_6271_176;0_36_72_6271_73;<br />
0_38_25_6271_25;0_40_20_6271_20;0_41_12_6271_13;0_42_8_6271_8;0_43_6_6271_6;0_44_6_6271_6;0_45_4_6271_4;0_46_5_6<br />
271_5;0_47_9_6271_10;0_48_9_6271_9;0_49_6_6271_6;0_50_4_6271_4;0_51_4_6271_4;0_52_5_6271_5;0_53_3_6271_3;0_54_9_6<br />
271_9;0_55_7_6271_8;0_56_1_6271_1;0_57_4_6271_4;0_58_1_6271_1;0_59_3_6271_3;0_60_4_6271_4;0_61_4_6271_4;0_62_2_62<br />
71_2;0_63_1_6271_1;0_64_1_6271_1;0_65_1_6271_1;4_0_74_116_2396;4_2_8_116_90;4_6_2_116_140;4_8_2_116_164;4_10_3_11<br />
6_160;4_12_4_116_224;4_14_5_116_222;4_18_3_116_376;4_20_5_116_498;4_22_3_116_343;4_26_1_116_284;4_32_1_116_140;4_<br />
34_1_116_176;4_36_1_116_73;4_41_1_116_13;4_47_1_116_10;4_55_1_116_8 …..<br />
Post processing scripts: /<br />
tranalyzer/trunk/scripts<br />
Skype: Vulnerable against<br />
TM Attack<br />
• 28
Some T3 Plugins<br />
L7 Protocols: Mail, HTTP, etc<br />
Routing: OSPF<br />
DNS / DHCP<br />
Full PCRE Regex<br />
Signal Processing<br />
Artificial Intelligence (RNN, Bayes, ESOM), nifty entropy shit<br />
Connection Matrix, Centrality<br />
IP Statistics: Host<br />
Database<br />
• 29
So what?<br />
Some Examples
The one way TCP Flow problem<br />
Symptom: on and off access problems<br />
TCP flows established, unidirectional<br />
T2 proofed: Reverse connection exists, not through firewall<br />
Not communicated online mis-configuration of firewall<br />
Trampel<br />
OSPF
FFT of some Packet Signals<br />
•Packet Length<br />
• time<br />
• 32
Traffic Mining:<br />
Encrypted Content Guessing<br />
SSH Command Guessing<br />
IP Tunnel Content Profiling<br />
Pitch based Classification<br />
Encrypted Voip Guessing: CCC 2011<br />
33
TM Your OWN: Packet Length Signal<br />
See the features?<br />
Codec training<br />
<strong>Burschka</strong> (Fischkopp) Linux<br />
Dominic (Student) Windows<br />
SN<br />
Ping min l =3<br />
34
Connection plugin: Social Behaviour<br />
67<br />
60<br />
3000,00<br />
Frequency<br />
Frecuency<br />
40<br />
2000,00<br />
20<br />
16<br />
10<br />
1000,00<br />
5<br />
1 1<br />
0<br />
0 5 10 15<br />
# Connections<br />
0,00<br />
0 3 6 9 12 15 18 21 24 27<br />
# Connections<br />
• 35
What is the Unknown?<br />
• 36
HOW TO find Bad Guys?<br />
Day: 0.7% of all users 42% bandwidth, WTF?<br />
P2P Traffic P2P Traffic<br />
Average Users<br />
Bars showMeans<br />
???<br />
Percentil User<br />
37<br />
Normal Traffic<br />
Normal Traffic
HOW TO find Bad Guys?<br />
Night: Same guys @ night 3am, ...<br />
P2P Traffic<br />
Average Users<br />
Machines of<br />
WAREZ guys<br />
Percentil User<br />
Normal Traffic<br />
38
Layer3/4/whatever Visualization<br />
Graphviz --> Operational Picture in Bootcamp<br />
_flow.txt<br />
Your AWK script<br />
Graphviz: dotty<br />
• 39
Layer3/4 Visualization<br />
Graphviz --> simple forensic Picture
Network Classification<br />
Centrality<br />
Connection Matrix<br />
PCA<br />
Largest Eigenvector Plot / t<br />
• 41
Network / Host Classification<br />
Centrality
ipSOM Operational Picture:<br />
13 Dim statistical T2 Flow parameters<br />
Now conceivable by human brain<br />
Bot Scanner<br />
DNS Zone Transfer<br />
43
Questions / Comments<br />
RFM and try me<br />
Join the development force<br />
Who wants Bootcamp?<br />
http://sourceforge.net/projects/tranalyzer/<br />
http://tranalyzer.com<br />
http://sourceforge.net/projects/traviz<br />
Google: Dataming for Hackers 44<br />
stefan.burschka@ruag.com