Crosby-Signed Thesis - Alliance Digital Repository
Crosby-Signed Thesis - Alliance Digital Repository
Crosby-Signed Thesis - Alliance Digital Repository
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
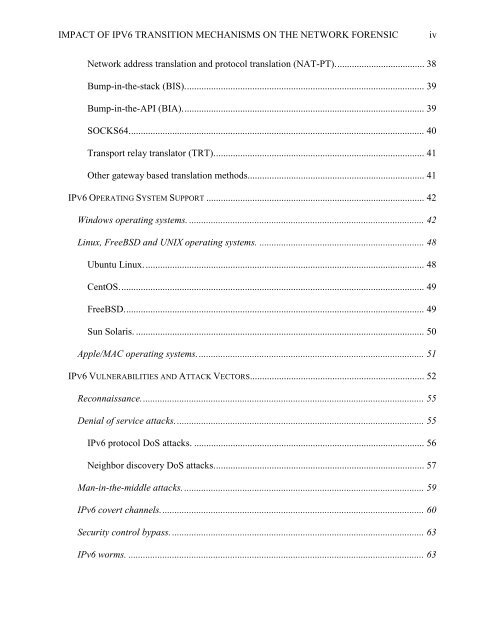
IMPACT OF IPV6 TRANSITION MECHANISMS ON THE NETWORK FORENSIC<br />
iv<br />
Network address translation and protocol translation (NAT-PT)..................................... 38<br />
Bump-in-the-stack (BIS)................................................................................................... 39<br />
Bump-in-the-API (BIA).................................................................................................... 39<br />
SOCKS64.......................................................................................................................... 40<br />
Transport relay translator (TRT)....................................................................................... 41<br />
Other gateway based translation methods......................................................................... 41<br />
IPV6 OPERATING SYSTEM SUPPORT .......................................................................................... 42<br />
Windows operating systems. ................................................................................................. 42<br />
Linux, FreeBSD and UNIX operating systems. .................................................................... 48<br />
Ubuntu Linux.................................................................................................................... 48<br />
CentOS.............................................................................................................................. 49<br />
FreeBSD............................................................................................................................ 49<br />
Sun Solaris. ....................................................................................................................... 50<br />
Apple/MAC operating systems.............................................................................................. 51<br />
IPV6 VULNERABILITIES AND ATTACK VECTORS........................................................................ 52<br />
Reconnaissance..................................................................................................................... 55<br />
Denial of service attacks....................................................................................................... 55<br />
IPv6 protocol DoS attacks. ............................................................................................... 56<br />
Neighbor discovery DoS attacks....................................................................................... 57<br />
Man-in-the-middle attacks. ................................................................................................... 59<br />
IPv6 covert channels............................................................................................................. 60<br />
Security control bypass. ........................................................................................................ 63<br />
IPv6 worms. .......................................................................................................................... 63





![pace SrntfletIc fne]its report - Alliance Digital Repository](https://img.yumpu.com/10493335/1/190x245/pace-srntfletic-fneits-report-alliance-digital-repository.jpg?quality=85)
