New Danfoss VLT® Decentral Drive E cient, reliable and powerful
New Danfoss VLT® Decentral Drive E cient, reliable and powerful
New Danfoss VLT® Decentral Drive E cient, reliable and powerful
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
SECURITY<br />
Are you safe from<br />
cyber-attack?<br />
The recent widespread publicity given to the Stuxnet virus, has brought home the real threats to industrial control<br />
systems posed by viruses <strong>and</strong> hackers. Dr Richard Piggin* examines the risks – <strong>and</strong> how to minimise them.<br />
In his first-ever public speech, GCHQ director<br />
Ian Lobban recently highlighted the “real<br />
<strong>and</strong> credible” threat facing the UK’s critical<br />
infrastructure from terrorists, organised<br />
criminals <strong>and</strong> hostile foreign governments. He<br />
dem<strong>and</strong>ed a swift response to match the<br />
speed with which “cyber events” can occur,<br />
<strong>and</strong> warned that the country's future<br />
economic prosperity rested on ensuring a<br />
defence against such assaults.<br />
So, which systems are under threat? The<br />
critical national infrastructure comprises<br />
facilities, sites <strong>and</strong> networks that deliver the<br />
essential services on which daily life depends.<br />
This spans nine sectors: communications;<br />
emergency services; energy; finance; food;<br />
government; health; transport; <strong>and</strong> water. The<br />
UK’s Centre for the Protection of National<br />
Infrastructure (CPNI) works with the providers<br />
of these services <strong>and</strong> government departments<br />
to identify the critical elements <strong>and</strong> to help<br />
protect them against national security threats.<br />
Cyber-threats to control systems extend far<br />
beyond energy <strong>and</strong> telecommunications<br />
facilities. For example, activities such as food<br />
distribution <strong>and</strong> logistics could be hit, resulting<br />
in a loss of consumer confidence, <strong>and</strong><br />
potential health risks.<br />
All are potentially<br />
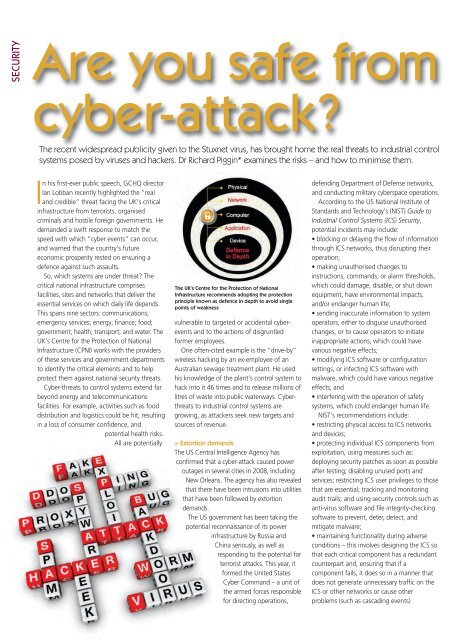
The UK’s Centre for the Protection of National<br />
Infrastructure recommends adopting the protection<br />
principle known as defence in depth to avoid single<br />
points of weakness<br />
vulnerable to targeted or accidental cyberevents<br />
<strong>and</strong> to the actions of disgruntled<br />
former employees.<br />
One often-cited example is the “drive-by”<br />
wireless hacking by an ex-employee of an<br />
Australian sewage treatment plant. He used<br />
his knowledge of the plant’s control system to<br />
hack into it 46 times <strong>and</strong> to release millions of<br />
litres of waste into public waterways. Cyberthreats<br />
to industrial control systems are<br />
growing, as attackers seek new targets <strong>and</strong><br />
sources of revenue.<br />
> Extortion dem<strong>and</strong>s<br />
The US Central Intelligence Agency has<br />
confirmed that a cyber-attack caused power<br />
outages in several cities in 2008, including<br />
<strong>New</strong> Orleans. The agency has also revealed<br />
that there have been intrusions into utilities<br />
that have been followed by extortion<br />
dem<strong>and</strong>s.<br />
The US government has been taking the<br />
potential reconnaissance of its power<br />
infrastructure by Russia <strong>and</strong><br />
China seriously, as well as<br />
responding to the potential for<br />
terrorist attacks. This year, it<br />
formed the United States<br />
Cyber Comm<strong>and</strong> – a unit of<br />
the armed forces responsible<br />
for directing operations,<br />
defending Department of Defense networks,<br />
<strong>and</strong> conducting military cyberspace operations.<br />
According to the US National Institute of<br />
St<strong>and</strong>ards <strong>and</strong> Technology’s (NIST) Guide to<br />
Industrial Control Systems (ICS) Security,<br />
potential incidents may include:<br />
• blocking or delaying the flow of information<br />
through ICS networks, thus disrupting their<br />
operation;<br />
• making unauthorised changes to<br />
instructions, comm<strong>and</strong>s, or alarm thresholds,<br />
which could damage, disable, or shut down<br />
equipment, have environmental impacts,<br />
<strong>and</strong>/or endanger human life;<br />
• sending inaccurate information to system<br />
operators, either to disguise unauthorised<br />
changes, or to cause operators to initiate<br />
inappropriate actions, which could have<br />
various negative effects;<br />
• modifying ICS software or configuration<br />
settings, or infecting ICS software with<br />
malware, which could have various negative<br />
effects; <strong>and</strong><br />
• interfering with the operation of safety<br />
systems, which could endanger human life.<br />
NIST’s recommendations include:<br />
• restricting physical access to ICS networks<br />
<strong>and</strong> devices;<br />
• protecting individual ICS components from<br />
exploitation, using measures such as:<br />
deploying security patches as soon as possible<br />
after testing; disabling unused ports <strong>and</strong><br />
services; restricting ICS user privileges to those<br />
that are essential; tracking <strong>and</strong> monitoring<br />
audit trails; <strong>and</strong> using security controls such as<br />
anti-virus software <strong>and</strong> file integrity-checking<br />
software to prevent, deter, detect, <strong>and</strong><br />
mitigate malware;<br />
• maintaining functionality during adverse<br />
conditions – this involves designing the ICS so<br />
that each critical component has a redundant<br />
counterpart <strong>and</strong>, ensuring that if a<br />
component fails, it does so in a manner that<br />
does not generate unnecessary traffic on the<br />
ICS or other networks or cause other<br />
problems (such as cascading events)