Share conversion, pseudorandom secret-sharing and ... - of the NVTI
Share conversion, pseudorandom secret-sharing and ... - of the NVTI
Share conversion, pseudorandom secret-sharing and ... - of the NVTI
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
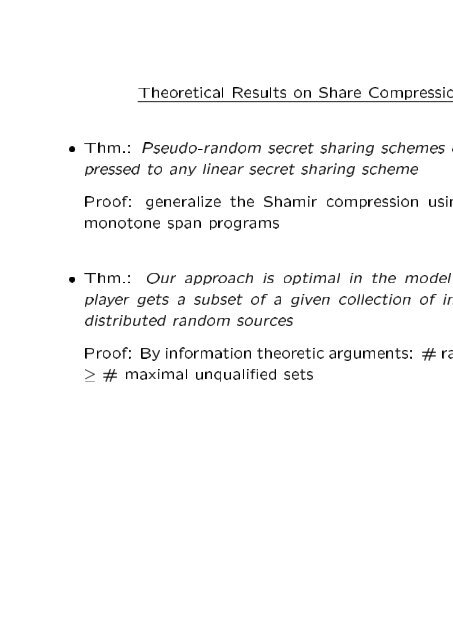
Theoretical Results on <strong>Share</strong> Compressio<br />
Thm.: Pseudo-r<strong>and</strong>om <strong>secret</strong> <strong>sharing</strong> schemes<br />
pressed to any linear <strong>secret</strong> <strong>sharing</strong> scheme<br />
Pro<strong>of</strong>: generalize <strong>the</strong> Shamir compression usin<br />
monotone span programs<br />
Thm.:<br />
Our approach is optimal in <strong>the</strong> model<br />
player gets a subset <strong>of</strong> a given collection <strong>of</strong> in<br />
distributed r<strong>and</strong>om sources<br />
Pro<strong>of</strong>: By information <strong>the</strong>oretic arguments: # ra<br />
# maximal unqualied sets