(.pdf) download - IAC - Defense Technical Information Center
(.pdf) download - IAC - Defense Technical Information Center
(.pdf) download - IAC - Defense Technical Information Center
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
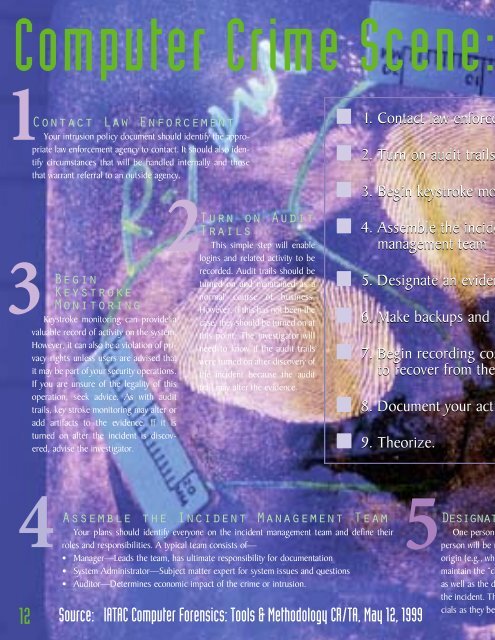
Computer Crime Scene:<br />
1Contact Law Enforcement<br />
Your intrusion policy document should identify the appropriate<br />
law enforcement agency to contact. It should also identify<br />
circumstances that will be handled internally and those<br />
that warrant referral to an outside agency.<br />
2<br />
3<br />
Begin<br />
Keystroke<br />
Monitoring<br />
Keystroke monitoring can provide a<br />
valuable record of activity on the system.<br />
However, it can also be a violation of privacy<br />
rights unless users are advised that<br />
it may be part of your security operations.<br />
If you are unsure of the legality of this<br />
operation, seek advice. As with audit<br />
trails, key stroke monitoring may alter or<br />
add artifacts to the evidence. If it is<br />
turned on after the incident is discovered,<br />
advise the investigator.<br />
Turn on Audit<br />
Trails<br />
This simple step will enable<br />
logins and related activity to be<br />
recorded. Audit trails should be<br />
turned on and maintained as a<br />
normal course of business.<br />
However, if this has not been the<br />
case, they should be turned on at<br />
this point. The investigator will<br />
need to know if the audit trails<br />
were turned on after discovery of<br />
the incident because the audit<br />
trail may alter the evidence.<br />
1. Contact law enforce<br />
2. Turn on audit trails<br />
3. Begin keystroke mo<br />
4. Assemble the incide<br />
management team<br />
5. Designate an eviden<br />
6. Make backups and p<br />
7. Begin recording cos<br />
to recover from the<br />
8. Document your acti<br />
9. Theorize.<br />
4<br />
12<br />
Assemble the Incident Management Team<br />
Your plans should identify everyone on the incident management team and define their<br />
roles and responsibilities. A typical team consists of—<br />
• Manager—Leads the team, has ultimate responsibility for documentation<br />
• System Administrator—Subject matter expert for system issues and questions<br />
• Auditor—Determines economic impact of the crime or intrusion.<br />
Source: IATAC Computer Forensics: Tools & Methodology CR/TA, May 12, 1999<br />
5D e s i g n<br />
One person<br />
person will be r<br />
origin (e.g., who<br />
maintain the “ch<br />
as well as the d<br />
the incident. Th<br />
cials as they be