Software Security Engineering - Build Security In - US-CERT
Software Security Engineering - Build Security In - US-CERT
Software Security Engineering - Build Security In - US-CERT
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
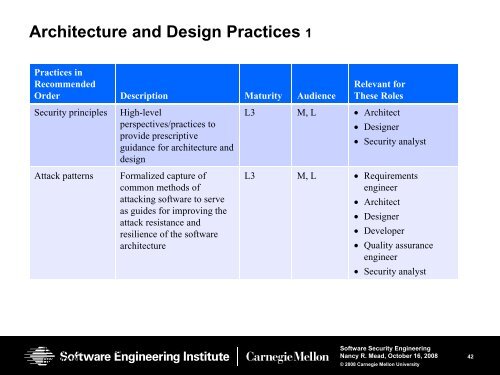
Architecture and Design Practices 1<br />
Practices in<br />
Recommended<br />
Order Description Maturity Audience<br />
Relevant for<br />
These Roles<br />
<strong>Security</strong> principles<br />
Attack patterns<br />
High-level<br />
perspectives/practices to<br />
provide prescriptive<br />
guidance for architecture and<br />
design<br />
Formalized capture of<br />
common methods of<br />
attacking software to serve<br />
as guides for improving the<br />
attack resistance and<br />
resilience of the software<br />
architecture<br />
L3 M, L • Architect<br />
• Designer<br />
• <strong>Security</strong> analyst<br />
L3 M, L • Requirements<br />
engineer<br />
• Architect<br />
• Designer<br />
• Developer<br />
• Quality assurance<br />
engineer<br />
• <strong>Security</strong> analyst<br />
Thursday, November<br />
06, 2008<br />
<strong>Software</strong> <strong>Security</strong> <strong>Engineering</strong><br />
Nancy R. Mead, October 16, 2008<br />
© 2008 Carnegie Mellon University<br />
42