Download - Layer Seven Security
Download - Layer Seven Security
Download - Layer Seven Security
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
DEFENSE IN DEPTH AN INTEGRATED STRATEGY FOR SAP SECURITY 2<br />
Introduction<br />
The protection of SAP systems against unauthorized access and<br />
manipulation demands security measures at multiple levels.<br />
According to SAP, this includes measures covering landscape<br />
architectures, operating systems and databases, as well as SAP<br />
technologies, applications and authorizations. 1<br />
This white paper outlines an integrated strategy for securing SAP<br />
systems based on the principles of Defense in Depth. The strategy<br />
is designed to protect the confidentiality, integrity and availability<br />
of SAP programs and data through countermeasures applied<br />
within each interconnected layer in SAP environments.<br />
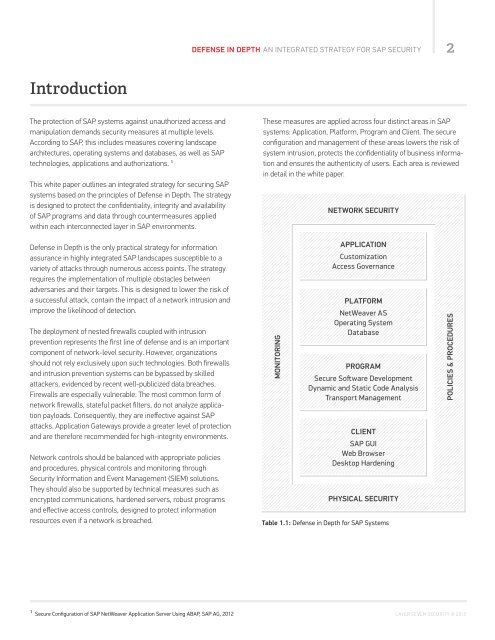
These measures are applied across four distinct areas in SAP<br />
systems: Application, Platform, Program and Client. The secure<br />
configuration and management of these areas lowers the risk of<br />
system intrusion, protects the confidentiality of business information<br />
and ensures the authenticity of users. Each area is reviewed<br />
in detail in the white paper.<br />
NETWORK SECURITY<br />
Defense in Depth is the only practical strategy for information<br />
assurance in highly integrated SAP landscapes susceptible to a<br />
variety of attacks through numerous access points. The strategy<br />
requires the implementation of multiple obstacles between<br />
adversaries and their targets. This is designed to lower the risk of<br />
a successful attack, contain the impact of a network intrusion and<br />
improve the likelihood of detection.<br />
The deployment of nested firewalls coupled with intrusion<br />
prevention represents the first line of defense and is an important<br />
component of network-level security. However, organizations<br />
should not rely exclusively upon such technologies. Both firewalls<br />
and intrusion prevention systems can be bypassed by skilled<br />
attackers, evidenced by recent well-publicized data breaches.<br />
Firewalls are especially vulnerable. The most common form of<br />
network firewalls, stateful packet filters, do not analyze application<br />
payloads. Consequently, they are ineffective against SAP<br />
attacks. Application Gateways provide a greater level of protection<br />
and are therefore recommended for high-integrity environments.<br />
Network controls should be balanced with appropriate policies<br />
and procedures, physical controls and monitoring through<br />
<strong>Security</strong> Information and Event Management (SIEM) solutions.<br />
They should also be supported by technical measures such as<br />
encrypted communications, hardened servers, robust programs<br />
and effective access controls, designed to protect information<br />
resources even if a network is breached.<br />
MONITORING<br />
APPLICATION<br />
Customization<br />
Access Governance<br />
PLATFORM<br />
NetWeaver AS<br />
Operating System<br />
Database<br />
PROGRAM<br />
Secure Soſtware Development<br />
Dynamic and Static Code Analysis<br />
Transport Management<br />
CLIENT<br />
SAP GUI<br />
Web Browser<br />
Desktop Hardening<br />
PHYSICAL SECURITY<br />
Table 1.1: Defense in Depth for SAP Systems<br />
POLICIES & PROCEDURES<br />
1 Secure Configuration of SAP NetWeaver Application Server Using ABAP, SAP AG, 2012 LAYER SEVEN SECURITY © 2013