EMV Glossary L - Mühlbauer Group
EMV Glossary L - Mühlbauer Group
EMV Glossary L - Mühlbauer Group
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
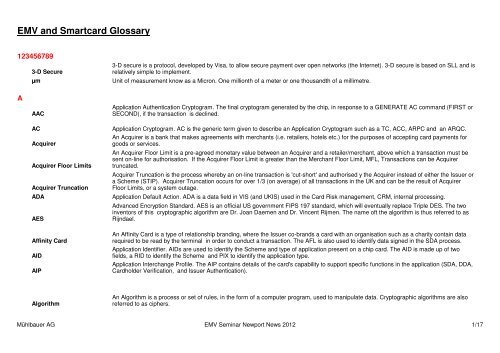
<strong>EMV</strong> and Smartcard <strong>Glossary</strong><br />
123456789<br />
3-D Secure<br />
3-D secure is a protocol, developed by Visa, to allow secure payment over open networks (the Internet). 3-D secure is based on SLL and is<br />
relatively simple to implement.<br />
µm Unit of measurement know as a Micron. One millionth of a meter or one thousandth of a millimetre.<br />
A<br />
AAC<br />
Application Authentication Cryptogram. The final cryptogram generated by the chip, in response to a GENERATE AC command (FIRST or<br />
SECOND), if the transaction is declined.<br />
AC<br />
Acquirer<br />
Acquirer Floor Limits<br />
Acquirer Truncation<br />
ADA<br />
AES<br />
Application Cryptogram. AC is the generic term given to describe an Application Cryptogram such as a TC, ACC, ARPC and an ARQC.<br />
An Acquirer is a bank that makes agreements with merchants (i.e. retailers, hotels etc.) for the purposes of accepting card payments for<br />
goods or services.<br />
An Acquirer Floor Limit is a pre-agreed monetary value between an Acquirer and a retailer/merchant, above which a transaction must be<br />
sent on-line for authorisation. If the Acquirer Floor Limit is greater than the Merchant Floor Limit, MFL, Transactions can be Acquirer<br />
truncated.<br />
Acquirer Truncation is the process whereby an on-line transaction is 'cut-short' and authorised y the Acquirer instead of either the Issuer or<br />
a Scheme (STIP). Acquirer Truncation occurs for over 1/3 (on average) of all transactions in the UK and can be the result of Acquirer<br />
Floor Limits, or a system outage.<br />
Application Default Action. ADA is a data field in VIS (and UKIS) used in the Card Risk management, CRM, internal processing.<br />
Advanced Encryption Standard. AES is an official US government FIPS 197 standard, which will eventually replace Triple DES. The two<br />
inventors of this cryptographic algorithm are Dr. Joan Daemen and Dr. Vincent Rijmen. The name oft the algorithm is thus referred to as<br />
Rijndael.<br />
Affinity Card<br />
AID<br />
AIP<br />
An Affinity Card is a type of relationship branding, where the Issuer co-brands a card with an organisation such as a charity contain data<br />
required to be read by the terminal in order to conduct a transaction. The AFL is also used to identify data signed in the SDA process.<br />
Application Identifier. AIDs are used to identify the Scheme and type of application present on a chip card. The AID is made up of two<br />
fields, a RID to identify the Scheme and PIX to identify the application type.<br />
Application Interchange Profile. The AIP contains details of the card's capability to support specific functions in the application (SDA, DDA,<br />
Cardholder Verification, and Issuer Authentication).<br />
Algorithm<br />
An Algorithm is a process or set of rules, in the form of a computer program, used to manipulate data. Cryptographic algorithms are also<br />
referred to as ciphers.<br />
Mühlbauer AG <strong>EMV</strong> Seminar Newport News 2012 1/17
ANSI<br />
APDU<br />
API<br />
API<br />
Applet<br />
Application<br />
ARC<br />
ARPC<br />
ARQC<br />
ASCII<br />
ATC<br />
ATM<br />
ATR<br />
Asymmetric Algorithm<br />
AUC<br />
American National Standards Institute. ANSI have adopted the ASCII code that assigns the numbers 0 through 127 to letters, 1000100); an<br />
exclamation point is coded as decimal 33 (Binary 0100001). By standardising the values used to represent text. Text fields in chip cards<br />
are usually encoded in ANSI. The use of ANSI and ASCII encoded characters enables computers to exchange information<br />
Application Protocol Data Unit. APDU is the command message sent from the interface device (in the terminal) and the response message<br />
returned by the chip to the interface device.<br />
Application Programming Interface. An API is the interface through which one program can interface with another. Different programs may<br />
be interchangeable if they share the same API.<br />
Application Priority Indicator. If a terminal does not support cardholder selection, the highest priority application is selected as indicated by<br />
the API written to the card at personalisation by the Issuer.<br />
An Applet is a platform independent program written in Java, designed to be downloaded to run on a chip/computer.<br />
An Application is a set of commands, data, rules and algorithms within a chip card to provide a given function in a particular system.<br />
Examples include GSM, credit/debit and electronic purse.<br />
Authorisation Response Code. The ARC is a two-digit code generated by the Issuer (as indicated in ISO 8583:1987) and transmitted to the<br />
terminal to approve, decline or refer a transaction. Most commonly used ARCs consist of an one-line approval (00), on-line decline (05),<br />
referral (01) or capture card request (04). The terminal is prohibited from altering the ARC from the Issuer. The terminal is allowed to<br />
generate an ARC in the following exception conditions: Y1 = Off-line approved Z1 = Off-line declined Y3 = Unable to go online (off-line<br />
approved) Z3 = Unable to go online (off-line declined)<br />
Authorisation Response Cryptogram. An ARPC is a cryptogram generated by the Issuer (or Scheme in STIP), sent back to the chip card<br />
as part on the on-line authorisation response message. The chip card uses the ARPC to authenticate the Issuer, in a process referred to<br />
as CAM.<br />
Authorisation Request Cryptogram. An ARQC is a cryptogram generated by the chip application, in response to the FIRST GENERATE AC<br />
command, if the transaction is to be conducted on-line The ARQC is used by the Issuer to authenticate the chip card in a process referred<br />
to as CAM.<br />
American Standard Code for Information Interchange. A code that assigns the numbers 0 through 127 to letters, the digits 0 to 9,<br />
punctuation marks, and certain other characters. For example, upper-case D is coded as decimal 68 (Binary 1000100); an exclamation<br />
point is coded as decimal 33 (binary 010001). By standardising the values used to represent text, ASCII enables computers to exchange<br />
information.<br />
Application transaction Counter. The ATC is a dynamic data field inside the chip application that increments by one when the Get<br />
Processing Options command is issued at the start of a transaction. The ATC, in conjunction with the Last On-line ATC can be used to<br />
detect counterfeit chip cards and highlight possible fraud patterns.<br />
Automated Teller Machine. An ATM is an unattended, customer-operated machine used to dispense cash and other services.<br />
Answer to Reset. An ATR is sent from the chip (after the supply voltage, the clock and the reset signal) containing various data related to<br />
the transmission protocol of the chip.<br />
An Asymmetric Algorithm is an algorithm that utilises a different key for scrambling and unscrambling the plain text. The two keys are<br />
referred to as the Private Key and the Public Key as one key never appears in clear and the other key may be made public.<br />
Application Usage Control. The AUC contains details of the card's geographic processing restrictions and support for specific services<br />
(international transactions, cash-back etc.).<br />
Mühlbauer AG <strong>EMV</strong> Seminar Newport News 2012 2/17
Authentication<br />
Authenticity<br />
Authorisation<br />
AVS<br />
Authentication is the process of verifying data or an application or product. Authentication of a chip card refers to the checking of the online<br />
cryptograms ARQC and ARPC. The correct name for chip authentication is Card Authentication Method or CAM.<br />
Proving the Authenticity of data is proving the data originated from a legitimate source.<br />
Authorisation is the process whereby the Issuer performs checks to ensure that the cardholder has sufficient funds to perform a<br />
transaction. During authorisation the authenticity of a magnetic stripe card is checked via the CVV (1)/CVC (1) and the authenticity or a<br />
chip card is checked via the ARQC.<br />
Address Verification System. Merchants use AVS and CVV2/CVC2 to authenticate customers in CNP transactions. The address specified<br />
by a customer in a CNP transaction must be the same as that recorded by the Issuer for the card being used.<br />
B<br />
Base I<br />
Base II<br />
Behavioural Scoring<br />
Binary<br />
BIN<br />
Biometrics<br />
Bit<br />
Block Cipher<br />
Byte<br />
Base I is Visa's authorisation system/messaging.<br />
Base III is Visa's settlement system/messaging.<br />
Behavioural Scoring is the use of account and payment history to calculate the nature of the cardholder's future financial performance.<br />
Binary numbers are used for counting in Base 2 using the digits 0 and 1. Most modern computes systems operate using binary logic.<br />
Computers use the binary number system by representing the values 0 and 1 using two voltage levels (usually 0 V for logic 0 and either<br />
+3.3 V or +5 V for logic 1).<br />
Binary Identification Number. A BIN is a six-digit number uniquely identifying the card Issuer. Each Issuer normally has several BINs.<br />
Biometrics is a method of verifying the identity of a person by electronically measuring some unique physical characteristic e.g. voice<br />
patterns fingerprint and retinal pattern.<br />
Binary Digit. A Binary Digit is the smallest unit of memory and therefore information within a computer. A bit can hold only one of two<br />
values, 0 or 1.<br />
A Block Cipher is a type of cipher that operates on blocks (normally 64 bits) of plain text data. DES is a type of block cipher.<br />
A Byte is a unit of data equal to eight Bits. Computer information is usually transferred or stored as binary code in byte-sized groups.<br />
C<br />
CA<br />
Certificate Authority. A Certificate Authority is a trusted organisation that creates, revokes and expires certificates. A CA is responsible for<br />
ensuring the identity of the user requesting the certificate is legitimate.<br />
CAA<br />
Caesar Cipher<br />
CAM<br />
Card Action Analysis. The card performs CAA after completion of Card Risk Management (CRM) and the setting of the CVR. CAA involves<br />
analysis of the CRM processes and responding with an appropriate cryptogram (TC to accept off-line, ARQC to go on-line and AAC to<br />
decline off-line) to the FIRST GENERATE AC request from the terminal. Often the terms CAA and CRM are used interchangeably.<br />
The Caesar Cipher is the name given to the first cipher used by Julius Caesar or military purposes. The Caesar Cipher is a type of<br />
substitution cipher where individual letters are replaced by different letters a fixed displacement along in the alphabet. For example, the<br />
letter 'd' replaces the Letter 'a', 'e' replaces the Letter 'b', 'f' replaces 'c' and so on.<br />
Card Authentication Method. CAM is the name given to the process of authenticating the card and the Issuer using the cryptograms ARQC<br />
and ARPC, respectively.<br />
Mühlbauer AG <strong>EMV</strong> Seminar Newport News 2012 3/17
CAP<br />
Cardholder<br />
Card IACs<br />
CBC<br />
CCF<br />
CDOL1<br />
CDOL2<br />
CECS<br />
Chip Authentication Program. CAP is MasterCard's name for the process of producing a human readable form of cryptogram which can be<br />
used to authenticate a card in a CNP transaction. It is equivalent to Visa's DPA.<br />
A Cardholder it the name given to a person who is provided with a financial payment card. The cardholder's name is embossed on the front<br />
of the card and is also stored inside the chip application.<br />
Card Issuer Action Codes. A set of three data fields, Card IAC Denial, Card IAC On-line and Card IAC Default, defined in M/Chip and<br />
M/Chip Lite for use in the Card Risk Management (CRM) internal processing.<br />
Cipher Block Changing. CBC is an operational mode of a cipher that employs a simple feedback function. In the CBC mode a block of<br />
plain text data is XORed with the previous cipher block prior to encryption. Triple DES in CBC mode is employed in chip applications to<br />
create the cryptograms ARQC, ARPC, TC and ACC.<br />
Currency Conversation Factor. A CCF is used to convert between the Primary and Secondary Currency on a VIS chip card, as part of the<br />
Card Risk Management (CRM) process. Please refer to the explanation of CTTAL (dc) for further information.<br />
Card Risk Management Data Object List 1. CDOL1 is a list of data objects (Tags and Lengths) that are passed ROM the terminal to the<br />
chip application with the FIRST GENERATE AC command.<br />
Card Risk Management Data Object List 2. CDOL2 is a list of data objects (Tags and Lengths) that are passed from the terminal to the<br />
chip application with the SECOND GENERATE AC command.<br />
Chip Electronic Commerce Specification. The Transaction Processing for Chip Electronic Commerce defines the use of a chip application<br />
to conduct a credit or debit transaction in an electronic commerce environment using SET 1.0 complainant software covers the <strong>EMV</strong><br />
functions with the Secure Electronic Transaction (SET) Specification, to provide the foundation for secure, chip card based transaction<br />
over the Internet.<br />
CEPS<br />
Charge back<br />
Chip<br />
Chip Card<br />
Cipher<br />
Cipher Text<br />
Clear Text<br />
CNP<br />
Common Criteria<br />
Contact Chip Card<br />
Common Electronic Purse Specification. The Common Electronic Purse Specifications (CEPS) define requirements for all components<br />
needed by an organisation to implement a globally interoperable electronic purse program, while maintaining full accountability and audit.<br />
Charge-back is the process whereby a transaction is returned or charged back from the Issuer to the Acquirer for payment. Examples of<br />
chargeback include, transactions from cards that are listed as lost/stolen or unauthorised transactions with a value higher than a preagreed<br />
Merchant Floor Limit.<br />
A Chip is a single crystal of semiconductor (silicon), on which an integrated circuit is created.<br />
A Chip Card is a plastic card embedded with a chip; also known as a smart card or Integrated Circuit Card.<br />
A Cipher is a process or set of rules, in the form of a computer program, used to encrypt data. Ciphers are also referred to as<br />
cryptographic algorithms.<br />
Cipher Text is the output obtained by scrambling plain text, with a cipher.<br />
Clear text is the message to be scrambled with, or just recovered from, a cipher. Clear text is often referred to as plain text.<br />
Card Not Present (transaction). CNP transactions are transactions over an open network, e.g. telephone, internet, mail order where a<br />
terminal or retailer does not physically check the card.<br />
Common Criteria is a directory of criteria used to evaluate and certify computer systems globally. Common Criteria was published by NIST<br />
and is now an ISO standard (15408).<br />
A Contact Chip Card is a chip card that requires physical contact with an interface device power. A contact plate wired to the chip directly<br />
locates onto a power source.<br />
Mühlbauer AG <strong>EMV</strong> Seminar Newport News 2012 4/17
Contactless Chip Card<br />
CPU<br />
CRM<br />
Cryptanalysis<br />
Cryptography<br />
CTLico<br />
CTLicu<br />
CTTAL (d)<br />
CTTAL (dc)<br />
A Contactless Chip Card is a chip card that does not require physical contact with an interface device to receive power. Power is provided<br />
to the chip using electromagnetic induction. Contactless chip cards are particularly suitable for access control, transport and baggage<br />
handling applications.<br />
Central Processing Unit. The CPU is the brain of a microcontroller card.<br />
Card Risk Management. CRM is a process performed by the card to determine if a transaction should be sent on-line, approved off-line or<br />
declined off-line. The output from CRM is the setting of the CVR that is subsequently used in Card Action Analysis (CAA). CRM is not<br />
defined in <strong>EMV</strong> and is thus proprietary to the card specification.<br />
Cryptanalysis is the art and science of breaking cipher codes.<br />
Cryptography is the art and science of keeping data secure and is practised by cryptographers.<br />
Consecutive Transaction Limit (international country). The CTLico velocity checking allows the Issuer to request that, after a certain<br />
number of consecutive off-line transactions not in the card's country of issue, transactions should be completed on-line Typical values<br />
used to date in the UK are 2 or 3. The maximum permitted value is 255.<br />
Consecutive Transaction Limit (international country). The CTLicu velocity checking allows the Issuer to request that, after a certain<br />
number of consecutive off-line transactions not in the card's primary currency, transactions should be completed on-line Typical values<br />
used to date in the UK are 2 or 3. The maximum permitted value is 255.<br />
Cumulative Total Transaction Amount Limit (domestic). The CTTAL (d) velocity checking allows the Issuer to request that, after a certain<br />
amount of off-line spend in the card's primary currency, transactions should be completed on-line Typical value used in the UK is £250. A<br />
value should be chosen that does not prevent the LCOL from being ineffective.<br />
Cumulative Total Transaction Amount Limit (dual currency). The CTTAL (dc) velocity checking allows the Issuer to request that, after a<br />
certain amount of off-line spend in the card's primary and/or secondary currency, transactions should be completed on-line Typical value<br />
used in the UK is £250. A value should be chosen that does not prevent the LCOL from being ineffective.<br />
CVC (1)<br />
CVC2<br />
CVK<br />
CVM<br />
CVN<br />
Card Verification Code (1). CVC (1) is the name given to the three-digit field coded on the magnetic stripe of a MasterCard bank card. The<br />
value is generated using Triple DES (Single DES is no longer permitted) from the account number (PAN), expiry date and service code.<br />
Card Verification Code 2. CVC (2) is the name given to the three-digit field printed on the signature panel of a MasterCard bank card. The<br />
value is generated using Triple DES (Single DES is no longer permitted) from the account number (PAN), expiry date and service code set<br />
to 000. The CVC2 is used in CNP transactions to prove the presence of a legitimate card.<br />
Card Verification Key. The CVK is the Master Key used to Create the CVC (1) / CVV (1) and CVC2 / CVV2.<br />
Cardholder Verification Method. CVM is the method by which a cardholder is identified during a transaction e.g. PIN or signature.<br />
Cryptogram Version Number. CVN is a 1-byte hexadecimal field used to identify the cryptographic method used to generate cryptograms<br />
on an <strong>EMV</strong> chip card.<br />
CVV (1)<br />
CVV2<br />
Card Verification Value (1). CVV (1) is the name given to the three-digit field coded on the magnetic stripe of a Visa bank card. The value<br />
is generated using Triple DES (Single DES is no longer permitted) from the account number (PAN), expiry date and service code.<br />
Card Verification Value 2. CVV2 is the name given to the three-digit field printed on the signature panel of a Visa bank card. The value is<br />
generated using Triple DES (Single DES is no longer permitted) from the account number (PAN), expiry date and service coded set to<br />
000. The CVV2 is used in CNP transactions to prove the presence of a legitimate card.<br />
Mühlbauer AG <strong>EMV</strong> Seminar Newport News 2012 5/17
CVR<br />
Card Verification Results. The CVR is a proprietary data field that reports transaction processing information to the Issuer e.g. number of<br />
scripts processed successfully. The CVR is used in M/Chip and M/Chip Lite to perform Card Risk Management (CRM).<br />
D<br />
DDA<br />
Decryption<br />
Denary<br />
DES<br />
DFA<br />
Digital Certificate<br />
Digital Signature<br />
DKauth<br />
Dynamic Data Authentication. Dynamic Data Authentication is an off-line security check of the chip card. Specific data fields within the card<br />
(for example, PAN and Expiry Date) are combined with data from the terminal (unpredictable number) in real time and signed using the<br />
chip cards' unique ICCKPR. DDA is a strong security check, requiring a chip with an MCP, which is not subject to replay attacks.<br />
Decryption is the process whereby cipher text is unscrambled to reveal the original plain text data using a cryptographic algorithm.<br />
Denary numbers are used for counting in Base 10 using the digits 0 to 9. Denary in the number system used for everyday general<br />
counting.<br />
Data Encryption Standard. DES is an encryption standard, defined by the U.S. government. DES encrypts data by breaking it into 64-bit<br />
blocks of data and using a 56-bit key. Officially the algorithm should be referred to as DEA (Data Encryption Algorithm) but this term is<br />
normally replaced with DES. DES is a symmetric algorithm, as the keys used for encryption and decryption are identical. DES (Single) has<br />
a key space of 2. Triple DES is much stronger than Single DES, with a strength (key space) of 2<br />
Differential Fault Analysis. DFA is a theoretical attack on chip cards. Spurious faults are induced in the chip to change a single bit of the<br />
secret key whilst it is being used. This attack is repeated several times and the results mathematically analysed to reveal the value of the<br />
secret key. Although this attack is only theoretical chip cards do have preventive mechanisms against DFA, e.g. the cryptogram is<br />
computed twice and the two values compared before output.<br />
A Digital Certificate consists of data, unique to an organisation, scrambled with an asymmetric private key. In their simplest form,<br />
certificates contain a public key, a name of an organisation, an expiration date, the name of the certifying authority that issued the<br />
certificate and a serial number. Digital Certificates are used to identify legitimate organisations.<br />
A Digital Signature consists of data, unique to an individual, scrambled with the signer’s asymmetric private key. It is typically created<br />
through the use of a hash function and is used to identify legitimate individuals.<br />
Derived Authentication Key (unique). DKauth is a key unique to each card (derived from the Master Authentication Key, MKauth), which is<br />
loaded into each chip card during personalisation. The DKauth is used in real time to generate the ARQC and verify the ARPC. [The<br />
terminology used here is specific to our <strong>EMV</strong> Chip Implementation Training Courses. VIS refers to DKauth as 'Unique DEA Key' and<br />
M/Chip refers to DKauth as 'ICC Application Cryptogram Master Key' or MK.]<br />
DKenc<br />
Derived Encryption Key (unique). DKenc is a key unique to each card (derived from the Master Encryption Key, MKenc), which is loaded<br />
into each chip card during personalisation. The DKenc is used in real time to decrypt a data field after transmission to the card encrypted<br />
within a script, E.g. PIN. [The terminology used here is specific to our <strong>EMV</strong> Chip Implementation Training Courses. VIS refers to DKenc as<br />
'Data Encipherment DEA Key' and M/Chip refers to DKenc as 'ICC Master Key for Secure Messaging for Confidentiality' or MK.]<br />
DKmac<br />
Derived MAC Key (unique). DKmac is a key unique to each card (derived from the master MAC Key, MKmac), which is loaded into each<br />
chip card during personalisation. The DKmac is used to check the authenticity and integrity of a script, ensuring the script came from a<br />
valid Issuer and it has not been tampered with. [The terminology used here is specific to our <strong>EMV</strong> Chip Implementation Training Courses.<br />
VIS refers to DKmac as 'MAC DEA Key' and M/Chip refers to DKmac as 'ICC Master Key for Secure Messaging for Integrity' or MK.]<br />
Mühlbauer AG <strong>EMV</strong> Seminar Newport News 2012 6/17
DKman<br />
DKpers<br />
DKI<br />
DPA<br />
DPA<br />
Derived Manufacturer Key (unique). DKman is a key unique to each card, (derived from the Master Manufacturing Key, MKman), which is<br />
loaded into and locks each chip card during initialisation for transportation between the Initialiser and the Pre-Personaliser. [The<br />
terminology used here is specific to our <strong>EMV</strong> Chip Implementation Training Courses. Each chip card manufacturer defines a different<br />
name for this DKman.]<br />
Derived Personalisation Key (unique). DKpers is a key unique to each card, (derived from the Master Personalisation Key, MKpers), which<br />
is loaded into and locks each chip card during pre-personalisation for transportation between the Pre-Personaliser and the Personaliser.<br />
[The terminology used here is specific to our <strong>EMV</strong> Chip Implementation Training Courses. Each chip card manufacturer defines a different<br />
name for this DKman.]<br />
Derivation Key Index. DKI is a two digit, hexadecimal field located on the card and the Host system to identify a set of Master DES Keys<br />
used to generate cryptograms, MKauth and those used in secure messaging, MKenc and MKmac.<br />
Differential Power Analysis. DPA is non-destructive or passive attack on a chip to obtain details of the secret keys. DPA analyses very<br />
small variations in the power usage, using an analogue to digital converter, as the chip performs a transaction. Complex statistical analysis<br />
of the power profiles can be performed using modern computers to reveal information about secret keys in the chip. Most Bank cards are<br />
protected against DPA. Issuers must confirm with the chip manufacturers and the Schemes that within chips to be used for Bank cards<br />
DPA countermeasures are in place.<br />
Dynamic Passcode Authentication. DPA is Visa's name for the process of producing a human readable form of cryptogram which can be<br />
used to authenticate a card in a CNP transaction. It is equivalent to MasterCard's CAP.<br />
Dynamic Digital Signature<br />
The Dynamic Digital Signature is created by signing unique card and terminal data with the ICC Private Key, ICCKPR, for use in DDA.<br />
E<br />
EEPROM<br />
Electronic Purse<br />
Elliptic Curves<br />
Embedding<br />
<strong>EMV</strong><br />
<strong>EMV</strong>Co<br />
Encryption<br />
Electrically Erasable Programmable Read Only Memory. This type of memory is used in chip cards to store all personalisation data and<br />
other dynamic data, for example counters, used in the application. Data in the EEPROM is retained without power but can only be modified<br />
when power is available.<br />
An Electronic Purse contains pre-loaded electronic money that can be used as a form of payment for goods an service.<br />
Elliptic Curves are a type of asymmetric public key algorithm. Elliptic Curves are still in their infancy but have much potential due to their<br />
ability to provide as strong a cryptographic system as RSA for smaller key sizes. The use of smaller key sizes enables a faster<br />
cryptographic implementation of Elliptic Curves compared to RSA.<br />
Embedding is the name of the process where a recess is milled in the plastic card and a chip module is glued into this recess.<br />
Europay MasterCard Visa. <strong>EMV</strong>, the Integrated Circuit Card (ICC) Specification for Payment Systems defines the minimum functionality<br />
required of debit/credit chip cards and terminals to ensure correct operation and interoperability.<br />
<strong>EMV</strong>Co is the name of the non-profit organisation formed between Europay, MasterCard and Visa that maintains the <strong>EMV</strong> Standard. JCB<br />
also joined <strong>EMV</strong>Co.<br />
Encryption is the process whereby plain text data is scrambled into non-readable data, know as cipher text, using a symmetric<br />
cryptographic algorithm.<br />
EPI<br />
EPOS<br />
Europay International. EPI is a payment Scheme that is now part of MasterCard International and has been renamed 'MasterCard Europe'.<br />
Electronic Point of Sale. A point of sale (POS) or point of service device equipped with electronic equipment for pricing and recording<br />
transactions. EPOS systems are normally installed in large retailers, e.g. supermarkets.<br />
Mühlbauer AG <strong>EMV</strong> Seminar Newport News 2012 7/17
F<br />
Fallback<br />
FIPS<br />
Fallback is the process whereby a chip card transaction falls back to a magnetic stripe transaction due to either a faulty chip or faulty chip<br />
terminal. All fallback transactions have to be fully authorised by the Issuer/Scheme or they are subject to chargeback.<br />
Federal Information Processing Standards. National Institute of Standards and Technology (NIST), a division of the U.S. Department of<br />
Commerce, issues standards and guidelines such as FIPS intended to be adopted in all computer systems in the U.S.<br />
Flash EEPROM<br />
Float<br />
Frequency Analysis<br />
Flash EEPROM is a type of memory that has a faster write time at a lower voltage than standard EEPROM. Flash EEPROM is used to<br />
store not only customer data but also the programme code making Flash EEPROM an excellent replacement for mask programmed ROM.<br />
The term Float is used to describe the total real money, owned by the Bank operating an electronic purse scheme, which resides on<br />
electronic purses, in the form of electronic money.<br />
Frequency Analysis is a form of cryptanalysis. Frequency analysis uses the finer points of language construction to determine the plain text<br />
from the cipher text. For example, in the English language 'e', 't' and 'a' are the most commonly occurring letters. The letter 't' does not<br />
appear either directly before or after the letter 'j', etc.<br />
G<br />
GSM<br />
Global System for Mobile Communications. GSM is an international standard for terrestrial mobile telephone systems.<br />
H<br />
HASH<br />
Hexadecimal<br />
HSM<br />
A Hash is the output from a hashing function that takes variable length input data and converts it to a fixed length, normally shorter, value.<br />
Hashing functions are usually one-way; that is, the hash (output) cannot be manipulated to return back to the original input data. The<br />
hashing function most commonly used in creating digital signatures in SHA-1.<br />
Hexadecimal characters are used for outing in Base 16 using the digits 0 to 9 and A to F. hexadecimal is often referred to as Hex.<br />
Hardware Security Module. A HSM is a secure, tamper evident device used for generating keys (symmetric and asymmetric) and for<br />
performing cryptographic calculations.<br />
I<br />
IACs<br />
IC<br />
ICC<br />
ICCK<br />
ICCK<br />
Issuer Action Codes. IACs are a set of three data fields, IAC denial, IAC on-line and IAC default, defined in <strong>EMV</strong>, for use in the Terminal<br />
Risk Management (TRM) processing. IACs are set by the Issuer and programmed onto the chip card at personalisation.<br />
Integrated Circuit. An IC is an electronic circuit whose components, such as transistors and resistors, are etched or imprinted on a single<br />
slice of semiconductor material.<br />
Integrated Circuit Card. An ICC is a plastic card containing an integrated circuit; also known as smart cards or chip cards.<br />
ICC Private Key. The ICC Private Key is used to sign unique card an terminal data to create a Dynamic Digital Signature for use in DDA.<br />
The nomenclature used by <strong>EMV</strong> is S. this <strong>EMV</strong> nomenclature is not used in our <strong>EMV</strong> Chip Implementation Training courses to avoid<br />
confusion with the term 'secret' that is normally reserved for symmetric algorithms such as DES.<br />
ICC Public Key. The ICC Public Key is used to resolve the Dynamic Digital Signature used in DDA. The nomenclature used by <strong>EMV</strong> is P.<br />
Our <strong>EMV</strong> Chip Implementation Training courses do not use this <strong>EMV</strong> nomenclature.<br />
Mühlbauer AG <strong>EMV</strong> Seminar Newport News 2012 8/17
ICCK Exponent<br />
ICCK remainder<br />
ICC Digital Certificates<br />
IK<br />
IK<br />
IK Exponent<br />
IK Remainder<br />
Initialisation<br />
Initialiser<br />
Integrity<br />
Internet<br />
ICC Public Key Exponent. The ICCK Exponent is a field having the value of 3 or 2 + 1 used in the creation of the ICC Digital Certificate<br />
used in DDA.<br />
ICC Public Key Remainder. The ICCK Remainder is the right hand part of the ICCKPU that could not fit inside the ICC Digital Certificate.<br />
The ICCK Remainder is written to the chip card at personalisation.<br />
An ICC Digital Certificate is created by signing the ICC Public Key, ICCKPU, with the Issuer Private Key, IKPR.<br />
Issuer Private Key. The Issuer Private Key is used to sign unique card data to create Static Digital Signature for use in SDA. Issuer Private<br />
Key. The Issuer Private Key is used to sign the ICC Public Key, ICCKPU, to create an ICC Digital Certificate for use in DDA. The<br />
nomenclature used by <strong>EMV</strong> is S. This <strong>EMV</strong> nomenclature is not used in our <strong>EMV</strong> Chip Implementation Training courses to avoid confusion<br />
with the term 'secret' that is normally reserved for symmetric algorithms such as DES.<br />
Issuer Public Key. The Issuer Public Key is used to resolve the Static Digital Signature used in SDA. Issuer Public Key. The Issuer Public<br />
Key is used to resolve the ICC Digital Certificate used in DDA. The nomenclature used by <strong>EMV</strong> is P. Our <strong>EMV</strong> Chip Implementation<br />
Training courses do not use this <strong>EMV</strong> nomenclature<br />
Issuer Public Key Exponent. The IK Exponent is a field having the value of 3 or 2 + 1 use in the creation of the Static Digital Signature used<br />
in SDA and ICC Digital Certificate in DDA.<br />
Issuer Public Key remainder. The IK Remainder is the right hand part of the Issuer Public Key, IKPU, which could not fit inside the Issuer<br />
Digital Certificate. The IK Remainder is written to the chip card at personalisation.<br />
Initialisation is the first phase of programming a chip. During this phase the chip is tested by writing and reading data to the memory area,<br />
loading a serial number and locking the chip with a unique key derived from a Master Manufacturing Key.<br />
An Initialiser is the entity that performs initialisation of the chip.<br />
Proving the integrity of data is proving the data has not been altered accidentally or deliberately.<br />
The Internet is made from many networks that interconnect million of supercomputers, mainframes, workstations, personal computers,<br />
laptops, and even pocket radios. The networks that make use of the Internet, all use a standard set of communications protocols, thus<br />
allowing computers with distinctive software and hardware to communicate.<br />
ISO<br />
Issuer<br />
Issuer Digital Certificate<br />
ITSEC<br />
International Standards Organisation. The following ISO standards are referenced in <strong>EMV</strong> 4: ISO 639:1988 Codes for the representation of<br />
names and languages ISO/IEC 7811 - 1:1995 Identification cards - Recording technique Part 1: Embossing ISO/IEC 7811 - 3:1995<br />
Identification cards - Recording technique Part 3: Location of embossed characters on ID-1 cards ISO/IEC 7816 - 1:1998 Identification<br />
cards - Integrated circuit(s) cards with contacts - Part 1: Physical characteristics ISO/IEC 7816 - 2:1999 Identification cards - Integrated<br />
circuit(s) cards with contacts - Part 2: Dimensions and location of contacts ISO/IEC 7816 - 3:1997 Identification Cards - Integrated circuit(s)<br />
cards with contacts - Part 3: Electronic signals and transmission protocols ISO/IEC 7816 - 4:1995 Identification cards - Integrated circuit(s)<br />
cards with contacts - Part 4, Inter-industry commands for interchange ISO/IEC 7816 - 5:1994 Identification cards - Integrated circuit(s)<br />
cards with contacts - Part 5: Numbering system and registration procedure for application identifiers ISO/IEC 8859:1987 Information<br />
processing - 8-bit single-byte coded graphic character sets ISO/IEC 10373:1993 Identification cards - Test methods<br />
An Issuer is the entity that issues and retains ownership of payment cards to cardholders.<br />
The Issuer Digital Certificate is created by signing the Issuer Public Key, IKPU, with the Scheme Private Key, SKPR for use in both SDA<br />
and DDA.<br />
Information Technique System Criteria. ITSEC is a directory of criteria used to evaluate and certify computer systems in Europe to an<br />
agreed level of security. ITSEC has now been replaced by Common Criteria.<br />
Mühlbauer AG <strong>EMV</strong> Seminar Newport News 2012 9/17
J<br />
Java<br />
Java Card<br />
JVM<br />
Java is a trademark name for a simple object orientated programming language developed by Sun Microsystems. Java is designed for use<br />
over the Internet, providing a secure environment for writing and executing world wide web applications. One of the major advantages of<br />
Java is that it is platform independent and thus the phrase "write once, run anywhere" was invented to describe Java.<br />
Java Card is a subset of Java specifically designed for use on chip cards. Java normally takes up over 1 Megabyte of memory and thus a<br />
subset of Java is used for chip cards that have a lower memory capacity.<br />
Java Virtual Machine. JVM is a microcontroller simulated in software to run Java byte code.<br />
K<br />
KEK<br />
Key<br />
Key Management<br />
Key Space<br />
Key Encrypting Key. A KEK is the name given to a key that is used exclusively to encrypt other keys.<br />
A key is a alphanumeric (hexadecimal) string of characters used by a cryptographic algorithm to scramble plain text data. The key is not<br />
directly related to the algorithm but is at the heart of the security of the algorithm. The algorithm can be made publicly available, but without<br />
the key, scrambled data cannot be unscrambled.<br />
Key Management is the process of security managing keys throughout their life, including generation, storage, distribution, usage and<br />
destruction.<br />
The Key Space of an algorithm is the number of possible different cipher texts that can be produced from a single plain text. Generally, the<br />
larger the key space the stronger the algorithm.<br />
L<br />
LCOL<br />
LMK<br />
LOATC<br />
Lower Consecutive Off-line Limit. The LCOL is used to limit the number of consecutive off-line transactions before the Issuer decides to go<br />
on-line Typical values used to date in the UK are 4 or 5. Maximum value is 255.<br />
Local Master Key. A LMK is the highest-level administrative key, generated in clear in a Hardware Security Module (HSM). The LMK is<br />
used to encrypt all Zone Master Keys (ZMK) and Application Keys (for example, MKauth, MKmac and MKenc) used in cryptographic<br />
processing. Each self-contained system, housing one or more HSMs, should have an independent LMK value, as suggested by the word<br />
'Local' in the key name. Please note that IBM security devices refer to these keys as Master Keys.<br />
Last On-line Application Transaction Counter. The LOATC is a dynamic data field inside the chip card that is set equal to the ATC after a<br />
successful on-line transaction has taken place. The LOATC, in conjunction with the ATC can be used to detect a counterfeit chip card and<br />
highlight possible fraud patterns.<br />
M<br />
MAC<br />
Masking<br />
MasterCard Europe<br />
M/Chip (Select)<br />
Message Authentication Code. A MAC is cipher text that is used to provide integrity of data. MACs are used extensively in IT when<br />
transferring data files between two systems. MACing the file enables the data to be checked for accidental or deliberate corruption during<br />
the transfer. DES is often employed as the MACing algorithm due its speed of operation.<br />
Masking is the photo-lithographic process of burning the ROM mask (programme code) into the chip.<br />
MasterCard Europe is a payment Scheme, formerly known as EPI, hat is part of MasterCard International.<br />
M/Chip is the name of MasterCard's full specific implementation of an <strong>EMV</strong> credit/debit appication on chip cards.<br />
Mühlbauer AG <strong>EMV</strong> Seminar Newport News 2012 10/17
M/Chip Lite<br />
MCI<br />
MCP<br />
MEL<br />
Memory Card<br />
MFL<br />
MKauth<br />
MKenc<br />
MKmac<br />
M/Chip Lite is the name of MasterCard's 'light' specific implementation of an <strong>EMV</strong> credit/debit application on chip cards. M/Chip Lite is a<br />
subset of the full M/Chip specification. M/Chip Lite does not support DDA, combined DDA/AC generation, Off-line Transaction encrypted<br />
PIN.<br />
MasterCard International. MCI is an international payment Scheme that now incorporates EPI.<br />
Mathematical Co-Processor. An MCP is a special integrated unit for performing complex arithmetic calculations normally associated with<br />
RSA processing.<br />
Multos Executable Language. MEL is the computing language for writing applications that work on MULTOS.<br />
Memory cards do not have a CPU but consist of a simple chip that can be read or written to. Telephone cards are memory cards.<br />
Merchant Floor Limit. MFL is a traditional fraud prevention technique in the magnetic stripe to force transactions on-line MFLs are preagreed<br />
monetary values between an Issuer and a retailer/merchant, above which a transaction must be sent on-line for authorisation.<br />
Unauthorised transactions that are over the Merchant Floor Limit are subject to chargeback.<br />
Master Authentication Key. The MKauth is used to derive unique keys, DKauth, that are loaded into each chip card during personalisation.<br />
The DKauth is used to generate the ARQC and verify the ARPC.<br />
Master Encryption Key. The MKenc is used to derive unique keys, DKenc, that are loaded into each chip card during personalisation. The<br />
DKenc is used to decrypt a data field after transmission to the card in a script. E.g. PIN.<br />
Master MAC Key. The MKmac is used to derive unique keys, DKmac, that are loaded into each chip card during personalisation. The<br />
DKmac is used to check the authenticity and integrity of a script.<br />
MKman<br />
MKpers<br />
Mod 10<br />
Module<br />
MONDEX<br />
Mono-alphabetic Cipher<br />
Multi-application<br />
Multi-functional<br />
MULTOS<br />
Master Manufacturing Key. The MKman is used to derive unique keys, DKman, that are loaded into and lock each chip during initialisation.<br />
Master Personalisation Key. The MKpers is used to derive unique keys, DKpers, which are loaded into and lock each chip card during Pre-<br />
Personalising.<br />
Mod 10 or more correctly Modulo 10 is the name given to the process of generating the last digit of an PAN from all the other digits.<br />
A Module consists of the silicon chip wired to a contact plate, ready for insertion into a plastic card.<br />
MONDEX is the name of an electronic purse specification owned by MasterCard International.<br />
A Mono-alphabetic Cipher is a type of substitution cipher where only one character or symbol is used to replace a letter in the plain text.<br />
Mono-alphabetic Ciphers are open to a frequency analysis attack. The Caesar Cipher is a mono-alphabetic substitution cipher.<br />
A Multi-application chip card is one that contains more than one application; for example, debit and an electronic purse.<br />
A Multi-functional chip card is one that contains more than one application and has additional functionality to load and delete application<br />
remotely. Often the term 'multi-functional' is not used and such cards are referred to as multi-application chip cards.<br />
MULTOS is a multi-functional operating system for chip cards. MULTOS is a open standard with a high security architecture evaluated to<br />
ITSEC Level 6 (most secure).<br />
N<br />
NIST<br />
NSA<br />
National Institute of Standards and Technology. NIST is a American organisation responsible for the standardising Information Technology<br />
Systems. NIST publishes FIPS standards.<br />
National Security Agency. NSA is an American organisation responsible for communication security including the development of new<br />
cryptographic algorithms.<br />
Mühlbauer AG <strong>EMV</strong> Seminar Newport News 2012 11/17
Non-Volatile Memory<br />
Non-Volatile Memory is memory that does not need power to retain its contents; examples include ROM, EEPROM and Flash EEPROM.<br />
O<br />
Off-line PIN<br />
Off-line Transaction<br />
On-line PIN<br />
On-line Transaction<br />
Open Platform<br />
An Off-line PIN is held and verified inside the chip. The off-line PIN should be kept in synchronisation with the corresponding on-line PIN.<br />
There are two forms of off-line PIN - plain text and encrypted.<br />
An Off-line Transaction is an electronic transaction that is processed without authorisation from the Issuer or Scheme (STIP).<br />
An On-line PIN is held and verified on the Issuer Host system.<br />
An On-line Transaction is an electronic transaction that is processed on-line by either the Issuer or Scheme (STIP).<br />
Open Platform is Visa's preferred technology for multi-functional chip cards.<br />
P<br />
PAN<br />
PDOL<br />
PEK<br />
Personalisation<br />
Personalisation<br />
Pig Pen<br />
Primary Account Number. The PAN is a 16 to 19-digit number used to identify a cardholder (debit) or an account (credit) that may have<br />
one or more authorised users.<br />
Processing Options Data Object List. The PDOL is an <strong>EMV</strong> data field containing a list of Tags and Lengths that identify fields required if<br />
geographical restrictions are supported by the chip application. PDOL is processed at the start of the transaction via the Get Processing<br />
Potion command.<br />
PIN Encrypting Key. A PEK is the name given to a key that is used exclusively to encrypt PIN blocks.<br />
Personalisation is the third phase of programming the chip card. During this phase the cardholder specific data is loaded into the preprepared<br />
file locations. At the end of this phase the card is activated and ready for use in the field.<br />
A Personaliser is the entity that personalises the chip card.<br />
Pig Pen is a type of substitution cipher where individual letters are replaced by a symbol that corresponds to part of a grid. The<br />
Freemasons used Pig Pen in the 18th Century.<br />
PIN<br />
PIN Fallback<br />
PIX<br />
PKCS<br />
PKI<br />
Plain Text<br />
Personal Identification Number. A PIN is a string of numbers between 4 and 12 digits (<strong>EMV</strong>) used to provide cardholder verification, CVM.<br />
PIN fallback is a term used to identify the fallback of off-line PIN to signature as the CVM for a particular chip transaction. The ability of a<br />
card to perform PIN fallback is indicated in the card's CVM List.<br />
Proprietary Application Identifier Extension. A PIX is the second part of an Application Identifier or AID used to identify the specific<br />
application on the chip card. Credit/debit applications normally have a PIX of 1010.<br />
Public Key Cryptographic Standard. PKCS is a set of standards published by RSA containing rules relating to the use of asymmetric<br />
algorithms.<br />
Public Key Infrastructure. PKI is the term used to describe the total infrastructure used to deliver Public Key applications. Public Key<br />
applications use RSA cryptography to protect sensitive documentation over open networks (the Internet).<br />
Plain text is the message to be scrambled using cryptography. Plain text is often referred to as clear text.<br />
Mühlbauer AG <strong>EMV</strong> Seminar Newport News 2012 12/17
Poly-alphabetic Cipher<br />
POS<br />
PPM (Review)<br />
Pre-personalisation<br />
Pre-Personaliser<br />
Private Key<br />
PSE<br />
Public Key<br />
PVV<br />
A Poly-alphabetic Cipher is a type of substitution cipher where more than one character or symbol is used to replace a single letter in the<br />
plain text. The number of replacement characters or symbols for each letter is normally dependent on the frequency the plain text letter<br />
occurs in the language being used. Poly-alphabetic Ciphers are more resistant to frequency analysis than Mono-alphabetic Ciphers.<br />
Point of Sale. A POS device is a terminal used to process an electronic transaction in shops, restaurants etc. The POS device may go online<br />
for full authorisation by the Issuer/Scheme or stay off-line to conduct the transaction.<br />
Post PIN Maturity (Review). The term PPM(Review) indicates that once a mature off-line PIN environment has been established in the UK,<br />
off-line PIN card parameters should be reviewed.<br />
Pre-personalisation is the second phase of programming the chip card. During this phase a file structure is created inside the chip and it is<br />
locked with a unique key, DKpers, derived from a Master Personalisation Key, MKpers.<br />
A Pre-Personaliser is the entity that pre-personalises the chip card.<br />
A Private Key is a key from an asymmetric algorithm that must be kept secret. The Private Key is mathematically linked to a Public Key<br />
that does not have to be kept secret.<br />
Payment System Environment. PSE has a fixed name of 1PAY.SYS.DDF01 and contains a directory of all applications present on the<br />
card. PSE is optional in <strong>EMV</strong> 4.0. If there is space available on the chip it is recommended to code PSE.<br />
A Public Key is a key from an asymmetric algorithm that does not have to be kept secret. The Public Key is mathematically linked to a<br />
Private Key that has to be kept secret.<br />
Personalisation Verification Value. PCC is the name given to the three-digit field coded on the magnetic stripe of a bank card that can be<br />
used to validate an on-line PIN. The PCC is generated using Triple DES (Single DES is no longer allowed) from 11 digits of the account<br />
number (PAN, excluding the mod 10 check value), the PIN Verification Key Index (0-6) and the four leftmost digits of the PIN.<br />
Q<br />
R<br />
RAM<br />
Replay Attack<br />
Resolving<br />
RFU<br />
RID<br />
Rijndael<br />
ROM<br />
Random Access Memory. RAM is often referred to as working memory as it is used to store data that is modified during a calculation<br />
session. Data in the RAM is lost when the power is removed.<br />
A Replay Attack, in the context of bank chip cards, refers to the fraudulent reproduction of the data from a legitimate transaction without<br />
the card being present.<br />
Resolving is the process whereby cipher text is unscrambled to reveal the original plain text data using an asymmetric algorithm.<br />
Reserved for Future Use. RFU it the term often seen in many chip specifications/standards to represent space for a field that may be used<br />
in the future for new functionality.<br />
Registered Identifier. A RID is the first part of an Application Identifier, AID, used to identify the Scheme brand associated with a bank chip<br />
card.<br />
Rijndael it the name given to the Advanced Encryption Standard, AES. AES is an official US government FIPS 197 standard, which will<br />
eventually replace Triple DES. The two inventors of this cryptographic algorithm are Dr. Joan Daemen and Dr. Vincent Rijmen.<br />
Read Only Memory. ROM is the type of memory that can only be read, not written to. Data in the ROM is retained without power, as it is<br />
hard wired into the chip. This type of memory is used in chips to store the operating system, testing routines and the programme code. A<br />
photo-lithographic process is used to burn all the code into the chip.<br />
Mühlbauer AG <strong>EMV</strong> Seminar Newport News 2012 13/17
RSA<br />
Rivest-Shamir-Adleman. RSA is an asymmetric algorithm named after its three inventors.<br />
S<br />
Scheme<br />
Script<br />
A Scheme is an organisation that provides interoperability and global (normally) acceptance of payment cards via an electronic routing<br />
network for payment transactions between the Acquirer and the Issuer. Examples include MasterCard, Visa and American Express.<br />
A Script is a command sent to the card in the authorisation response message that changes data in the chip application, blocks/unblocks<br />
an application or blocks the chip entirely<br />
SDA<br />
Secrecy<br />
Secret Key<br />
SET<br />
SHA-1<br />
Signing<br />
SIM<br />
SK<br />
SK<br />
SK Exponent<br />
SK Index<br />
SSL<br />
Static Digital Signature<br />
STIP<br />
Substitution Cipher<br />
Static Data Authentication. Static Data Authentication is an off-line security check of the chip. Specific data fields within the card (Primary<br />
Account Number, Expiry Date and more) are checked to ensure that they have not been tampered with since the card was personalised by<br />
the Issuer. SDA is a weaker security check than DDA as the security data is static and is thus subject to replay attacks.<br />
Data requiring Secrecy never appears in clear but is scrambled using an algorithm and a key.<br />
A Secret Key is a key from a symmetric algorithm that must never appear in clear.<br />
Secure Electronic Transaction. SET is a protocol developed by Visa, MasterCard and other leading companies to allow secure payment<br />
over open networks (the Internet). SET in a complex secure protocol.<br />
Secure Hashing Algorithm. SHA-1 is a one-way Secure Hashing Algorithm designed by NIST and the NSA for use with the digital<br />
signatures standard. When any message of length
Symmetric Algorithm<br />
A Symmetric Algorithm is an algorithm that utilised the same key for scrambling and unscrambling the plain text. The key is referred to as a<br />
secret key as the value should never appear in clear.<br />
T<br />
TAA<br />
TAC<br />
TC<br />
TLV<br />
Transposition Cipher<br />
Triple DES<br />
TRM<br />
TVR<br />
Terminal Action Analysis. Following completion of Terminal Risk Management, TRM, and the setting of the TVR, the terminal performs<br />
TAA. TAA involves terminal analysis of the TRM processes and the request of an appropriate cryptogram (TC to accept off-line, ARQC to<br />
go on-line and AAC to decline off-line). Often TAA and TRM are used interchangeably.<br />
Terminal Action Codes. TACs are a set of three data fields, TAC denial, TAC on-line and TAC default, defined in <strong>EMV</strong>, for use in the<br />
Terminal Risk Management, TRM, processing. TACs are set by the Schemes and are located in the terminal.<br />
Transaction Certificate. A TC is the final cryptogram generated by the chip application, by the chip application, in response to a<br />
GENERATE AC command (FIRST or SECOND), if the transaction is accepted.<br />
Tag, Length and Value. TLV is a data format that uses a label (TAG) to uniquely identify the field. The Tag is followed by the Length, then<br />
the Value of the field.<br />
A Transposition Cipher is the name given to a cipher that rearranges the characters of the plain text to produce the cipher text, which is<br />
thus an anagram of the plain text.<br />
Triple DS uses the symmetric DES algorithm three times with two keys to encrypt a data block. Firstly, the data block is encrypted with the<br />
first key, the result is then decrypted using the second key and this result is finally encrypted using the first key again. Triple DES has a<br />
strength (key space) of 2 112, much stronger than single DES, 2 56.<br />
Terminal Risk Management. TRM is a process performed by the terminal to determine if a transaction should be sent on-line, approved<br />
off-line or declined off-line. The output from TRM is the setting of the TVR that is subsequently used in Terminal Action Analysis, TAA.<br />
Terminal Verification Results. The TVR is an <strong>EMV</strong> defined field that reports transaction processing information e.g. PIN failure to the<br />
Issuer. The TVR is also used in Terminal Action Analysis, TAA.<br />
U<br />
UCOL<br />
UKIS<br />
Upper Consecutive Off-line Limit. The UCOL is used to limit the maximum number of consecutive off-line transactions, after which the<br />
Issuer decides to decline the transaction in an off-line environment. Use of this field by UK Issuer has varied from lower values (e.g. 20) to<br />
much higher values up to the maximum of 255.<br />
United Kingdom Integrated Circuit Card Specification. UKIS is the UK's specific implementation of an <strong>EMV</strong> credit/debit application on chip<br />
cards. This specification was a subset of an early version (1.2) of VIS and used by the UK prior to the introduction of off-line PIN. UKIS is<br />
now obsolete for new card issuance, as it does not contain an off-line PIN.<br />
V<br />
VIS<br />
Visa Integrated Circuit Card Specification. VIS is Visa's specific implementation of an <strong>EMV</strong> credit/debit application on chip cards. This<br />
specification is often referred to as VSDC.<br />
Mühlbauer AG <strong>EMV</strong> Seminar Newport News 2012 15/17
Visa Early Option<br />
Visa Easy Entry<br />
Visa International<br />
VLP<br />
VLP Authorisation Code<br />
VLP Available Funds<br />
VLP Funds Limit<br />
VLP Single Transaction<br />
Limit<br />
Volatile Memory<br />
VSDC<br />
Visa Early Option is the term given to describe a system whereby Visa performs the CAM process (check ARQC, generate ARPC) on<br />
behalf on the Issuer. Visa passes a traditional magnetic stripe message with very minor modifications to the Issuer for authorisation<br />
Similarly the settlement message sent through the Base II system does not contain any additional chip information. Visa Early Option<br />
allows Issuers to phase in chip migration, concentrating on card Issuance first. However, if an Issuer wishes to support scripting (needed<br />
for off-line PIN) then Visa Early Option cannot be used.<br />
Visa Easy Entry is the term given to storing only the magnetic stripe information (PAN, CVV1, Service Code etc.) inside the chip. At a chip<br />
terminal the magnetic stripe information is read from the chip application and forwarded to the Issuer. Visa Easy Entry was introduced to<br />
avoid the major system changes required to issue and authorise full <strong>EMV</strong> chip cards. Visa Easy Entry is no longer allowed by the payment<br />
Schemes.<br />
Visa International is a payment Scheme.<br />
Visa Low Payment. VLP is a feature within VSDC that enables a pre-authorised amount on the cards to be used in offline low-value<br />
transactions. The transaction must be in the card's domestic currency.<br />
VLP Authorisation Code is the data element containing an authorisation code indication that the transaction was an approved VLP<br />
transaction.<br />
VLP Available Funds is the amount oft money available to spend in a VLP transaction subject to the VLP Single Transaction Limit.<br />
VLP Funds Limit is the maximum amount of money available to spend in VLP transactions. The VLP Available Funds are reset to the VLP<br />
Funds Limit after an online approved transaction when the Issuer's Authentication requirements are satisfied.<br />
VLP Single Transaction Limit is the maximum amount of money allowed in a single VLP transaction.<br />
Volatile memory is memory that needs power in order to retain its contents, for example RAM.<br />
Visa Smart Debit Credit. VSDC is a generic name for Visa's chip card debit/credit program. VSDC is often used to refer to the technical<br />
VIS specification.<br />
W<br />
X<br />
Wafer<br />
WFSC<br />
X509<br />
XOR<br />
A wafer is a high purity silicon disk on which chips are built. Wafers vary in diameter from 6 to 12 inches.<br />
Windows for Smart Cards. WFSC is an open standard (under licence) for multi-functional chip cards developed by Microsoft.<br />
X509 is a standard for Public Key Digital Certificates. This standard is used in public key applications used in digitally sign documents for<br />
transmission over open networks.<br />
XOR is a mathematical operation used to combine binary data. Like bits ('0', '0' and '1', '1') XOR to give '0' and unlike bits ('0', '1' and '1'<br />
and '0' XOR to give a '1'.)<br />
Y<br />
Y1<br />
Y3<br />
Y1 is an Authorization Response Code (ARC) issued by the terminal for an off-line approved transaction.<br />
Y3 is an Authorisation Response Code (ARC) issued by the terminal for an off-line approved transaction if the terminal is unable to go<br />
online.<br />
Mühlbauer AG <strong>EMV</strong> Seminar Newport News 2012 16/17
Z<br />
Z1<br />
Z3<br />
Z1 is an Authorisation Response Code (ARC) issued by the terminal for an off-line declined transaction<br />
Z3 is an Authorisation Response Code (ARC) issued by the terminal for an off-line declined transaction if the terminal is unable to go<br />
online.<br />
ZMK<br />
Zone Master Key. A ZMK is a high level administrative key established manually between two systems. Secret data including keys can be<br />
then be transferred securely between the two systems. Please note that Visa refer to Zone Master Keys as Zone Control Master Keys.<br />
Every effort has been made to ensure this document is correct, if you should find any mistakes please notify info@muehlbauer.de<br />
Mühlbauer AG <strong>EMV</strong> Seminar Newport News 2012 17/17