Keypoint Matching Technique and Its Applications
Keypoint Matching Technique and Its Applications
Keypoint Matching Technique and Its Applications
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
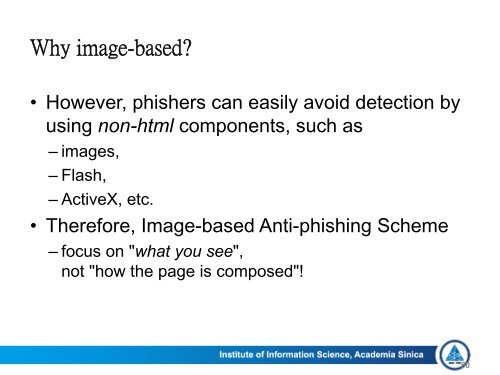
Why image-based<br />
• However, phishers can easily avoid detection by<br />
using non-html components, such as<br />
– images,<br />
– Flash,<br />
– ActiveX, etc.<br />
• Therefore, Image-based Anti-phishing Scheme<br />
– focus on "what you see",<br />
not "how the page is composed"!<br />
50