Keypoint Matching Technique and Its Applications
Keypoint Matching Technique and Its Applications
Keypoint Matching Technique and Its Applications
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
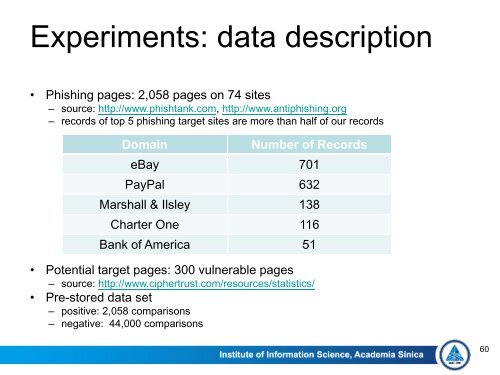
Experiments: data description<br />
• Phishing pages: 2,058 pages on 74 sites<br />
– source: http://www.phishtank.com, http://www.antiphishing.org<br />
– records of top 5 phishing target sites are more than half of our records<br />
Domain<br />
Number of Records<br />
eBay 701<br />
PayPal 632<br />
Marshall & Ilsley 138<br />
Charter One 116<br />
Bank of America 51<br />
• Potential target pages: 300 vulnerable pages<br />
– source: http://www.ciphertrust.com/resources/statistics/<br />
• Pre-stored data set<br />
– positive: 2,058 comparisons<br />
– negative: 44,000 comparisons<br />
60