BH_US_12_Tsai_Pan_Exploiting_Windows8_WP
BH_US_12_Tsai_Pan_Exploiting_Windows8_WP
BH_US_12_Tsai_Pan_Exploiting_Windows8_WP
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
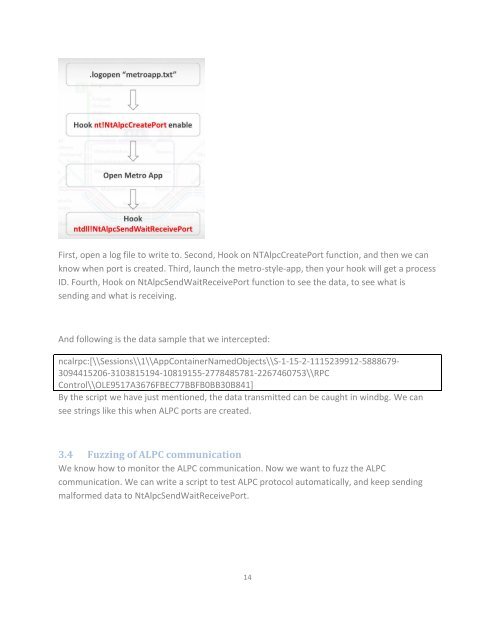
First, open a log file to write to. Second, Hook on NTAlpcCreatePort function, and then we can<br />
know when port is created. Third, launch the metro-style-app, then your hook will get a process<br />
ID. Fourth, Hook on NtAlpcSendWaitReceivePort function to see the data, to see what is<br />
sending and what is receiving.<br />
And following is the data sample that we intercepted:<br />
ncalrpc:[\\Sessions\\1\\AppContainerNamedObjects\\S-1-15-2-11152399<strong>12</strong>-5888679-<br />
3094415206-3103815194-10819155-2778485781-2267460753\\RPC<br />
Control\\OLE9517A3676FBEC77BBFB0BB30B841]<br />
By the script we have just mentioned, the data transmitted can be caught in windbg. We can<br />
see strings like this when ALPC ports are created.<br />
3.4 Fuzzing of ALPC communication<br />
We know how to monitor the ALPC communication. Now we want to fuzz the ALPC<br />
communication. We can write a script to test ALPC protocol automatically, and keep sending<br />
malformed data to NtAlpcSendWaitReceivePort.<br />
14