BH_US_12_Tsai_Pan_Exploiting_Windows8_WP
BH_US_12_Tsai_Pan_Exploiting_Windows8_WP
BH_US_12_Tsai_Pan_Exploiting_Windows8_WP
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
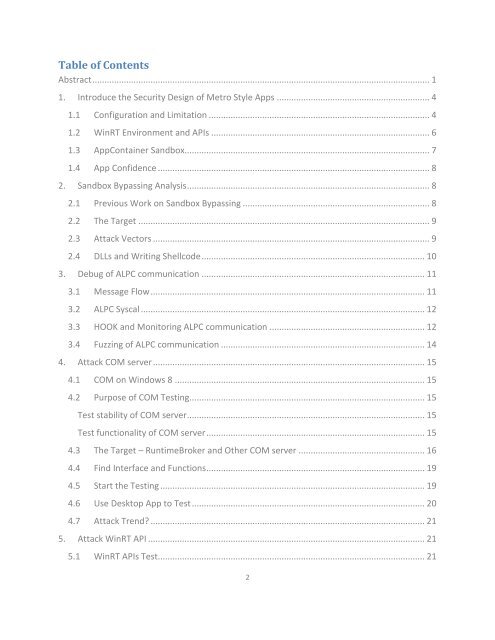
Table of Contents<br />
Abstract ........................................................................................................................................... 1<br />
1. Introduce the Security Design of Metro Style Apps ............................................................... 4<br />
1.1 Configuration and Limitation ........................................................................................... 4<br />
1.2 WinRT Environment and APIs .......................................................................................... 6<br />
1.3 AppContainer Sandbox..................................................................................................... 7<br />
1.4 App Confidence ................................................................................................................ 8<br />
2. Sandbox Bypassing Analysis .................................................................................................... 8<br />
2.1 Previous Work on Sandbox Bypassing ............................................................................. 8<br />
2.2 The Target ........................................................................................................................ 9<br />
2.3 Attack Vectors .................................................................................................................. 9<br />
2.4 DLLs and Writing Shellcode ............................................................................................ 10<br />
3. Debug of ALPC communication ............................................................................................ 11<br />
3.1 Message Flow ................................................................................................................. 11<br />
3.2 ALPC Syscal ..................................................................................................................... <strong>12</strong><br />
3.3 HOOK and Monitoring ALPC communication ................................................................ <strong>12</strong><br />
3.4 Fuzzing of ALPC communication .................................................................................... 14<br />
4. Attack COM server ................................................................................................................ 15<br />
4.1 COM on Windows 8 ....................................................................................................... 15<br />
4.2 Purpose of COM Testing................................................................................................. 15<br />
Test stability of COM server .................................................................................................. 15<br />
Test functionality of COM server .......................................................................................... 15<br />
4.3 The Target – RuntimeBroker and Other COM server .................................................... 16<br />
4.4 Find Interface and Functions .......................................................................................... 19<br />
4.5 Start the Testing ............................................................................................................. 19<br />
4.6 Use Desktop App to Test ................................................................................................ 20<br />
4.7 Attack Trend ................................................................................................................. 21<br />
5. Attack WinRT API .................................................................................................................. 21<br />
5.1 WinRT APIs Test.............................................................................................................. 21<br />
2