x86-64 buffer overflow exploits and the borrowed code chunks - SuSE
x86-64 buffer overflow exploits and the borrowed code chunks - SuSE
x86-64 buffer overflow exploits and the borrowed code chunks - SuSE
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
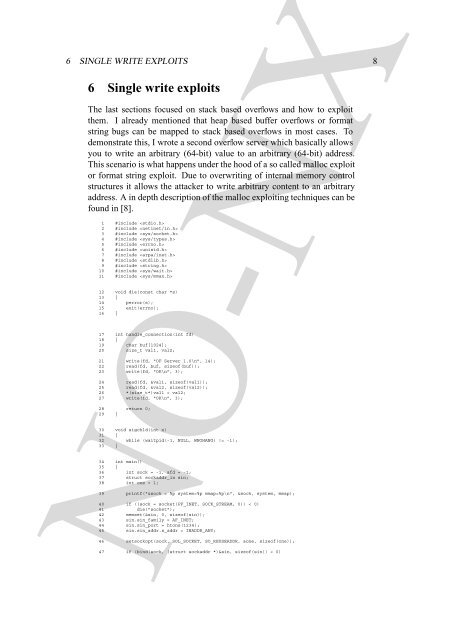
6 SINGLE WRITE EXPLOITS 8<br />
6 Single write <strong>exploits</strong><br />
The last sections focused on stack based <strong>overflow</strong>s <strong>and</strong> how to exploit<br />
<strong>the</strong>m. I already mentioned that heap based <strong>buffer</strong> <strong>overflow</strong>s or format<br />
string bugs can be mapped to stack based <strong>overflow</strong>s in most cases. To<br />
demonstrate this, I wrote a second <strong>overflow</strong> server which basically allows<br />
you to write an arbitrary (<strong>64</strong>-bit) value to an arbitrary (<strong>64</strong>-bit) address.<br />
This scenario is what happens under <strong>the</strong> hood of a so called malloc exploit<br />
or format string exploit. Due to overwriting of internal memory control<br />
structures it allows <strong>the</strong> attacker to write arbitrary content to an arbitrary<br />
address. A in depth description of <strong>the</strong> malloc exploiting techniques can be<br />
found in [8].<br />
1 #include <br />
2 #include <br />
3 #include <br />
4 #include <br />
5 #include <br />
6 #include <br />
7 #include <br />
8 #include <br />
9 #include <br />
10 #include <br />
11 #include <br />
12 void die(const char *s)<br />
13 {<br />
14 perror(s);<br />
15 exit(errno);<br />
16 }<br />
17 int h<strong>and</strong>le_connection(int fd)<br />
18 {<br />
19 char buf[1024];<br />
20 size_t val1, val2;<br />
21 write(fd, "OF Server 1.0\n", 14);<br />
22 read(fd, buf, sizeof(buf));<br />
23 write(fd, "OK\n", 3);<br />
24 read(fd, &val1, sizeof(val1));<br />
25 read(fd, &val2, sizeof(val2));<br />
26 *(size_t*)val1 = val2;<br />
27 write(fd, "OK\n", 3);<br />
28 return 0;<br />
29 }<br />
30 void sigchld(int x)<br />
31 {<br />
32 while (waitpid(-1, NULL, WNOHANG) != -1);<br />
33 }<br />
34 int main()<br />
35 {<br />
36 int sock = -1, afd = -1;<br />
37 struct sockaddr_in sin;<br />
38 int one = 1;<br />
39 printf("&sock = %p system=%p mmap=%p\n", &sock, system, mmap);<br />
40 if ((sock = socket(PF_INET, SOCK_STREAM, 0)) < 0)<br />
41 die("socket");<br />
42 memset(&sin, 0, sizeof(sin));<br />
43 sin.sin_family = AF_INET;<br />
44 sin.sin_port = htons(1234);<br />
45 sin.sin_addr.s_addr = INADDR_ANY;<br />
NO-NX<br />
46 setsockopt(sock, SOL_SOCKET, SO_REUSEADDR, &one, sizeof(one));<br />
47 if (bind(sock, (struct sockaddr *)&sin, sizeof(sin)) < 0)