Video intypedia001en EXERCISES - Criptored
Video intypedia001en EXERCISES - Criptored
Video intypedia001en EXERCISES - Criptored
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
<strong>Video</strong> <strong>intypedia001en</strong><br />
LESSON 1: HISTORY OF CRYPTOGRAPHY AND ITS EARLY STAGES IN EUROPE<br />
<strong>EXERCISES</strong><br />
Dr. Arturo Ribagorda Garnacho, Carlos III University of Madrid, Spain.<br />
EXERCISE 1<br />
The discovery that in each language the letters appeared with a different frequency, allowed<br />
the deciphering of Caesar type ciphertexts and, specially, monoalphabetic ciphertexts.<br />
For this reason, since the Renaissance, cryptographers exerted in finding new ciphering<br />
methods and hence came up with the polyalphabetic systems. These use several alphabets for<br />
ciphering, so that each ciphertext letter of another letter depends on the position of the<br />
plaintext letter. The simplest of these methods uses two cipher alphabets: one for letters<br />
occupying even positions of the plaintext and the other alphabet for the letters in odd<br />
positions.<br />
An example of this would be:<br />
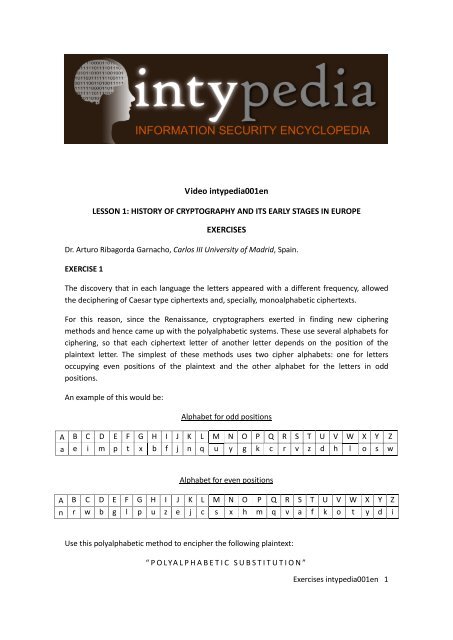
Alphabet for odd positions<br />
A B C D E F G H I J K L M N O P Q R S T U V W X Y Z<br />
a e i m p t x b f j n q u y g k c r v z d h l o s w<br />
Alphabet for even positions<br />
A B C D E F G H I J K L M N O P Q R S T U V W X Y Z<br />
n r w b g l p u z e j c s x h m q v a f k o t y d i<br />
Use this polyalphabetic method to encipher the following plaintext:<br />
“ POLYALPHABETIC SUBSTITUTION”<br />
Exercises <strong>intypedia001en</strong> 1
SOLUTION<br />
Following the given instructions leads to this substitution:<br />
P O L Y A L P H A B E T I C S U B S T I T U T I O N<br />
k h q d a c k u a r p f f w v k e a z z z k z z g x<br />
So the final result would be:<br />
k h q y a c k u a r p f f w v k e a z z z k z z g x<br />
EXERCISE 2<br />
1.- A transposition method, which was commonly used in ancient times, was the COLUMNAR<br />
TRANSPOSITION. First of all, the plaintext is written out, from left to right and top to bottom, in<br />
a table with a certain amount of columns. Each letter fits into a cell of the table, which has as<br />
many rows as necessary. Then, the ciphertext is obtained by writing the letters in the first<br />
column, afterwards the letters in the second column, and so on, until all the letters in the table<br />
have been written.<br />
Using the columnar transposition method, with five columns, encipher the following plaintext:<br />
“A COLUMNAR TRANSPOSITION EXERCISE”<br />
2.- In order to complicate this process a little, a keyword formed by non-repeating letters and<br />
as many letters that you wish the table to have can be used. By writing the keyword on top of<br />
the table –the first letter of the keyword on top of the first column, the second letter on top of<br />
the second column, etc…- the ciphertext is obtained by writing out the column whose first<br />
letter (that of the keyword) is first in alphabetical order, then the column whose first letter is<br />
the following in alphabetical order and so on.<br />
Using the columnar transposition method, with the keyword “CIPHER”, encrypt the following<br />
plaintext: “ I HAVE A COMPLETE EXAM WITH SOLUTION”<br />
SOLUTION<br />
1.- The plaintext is written in a table with five columns:<br />
A C O L U<br />
M N A R T<br />
R A N S P<br />
O S I T I<br />
O N E X E<br />
Exercises <strong>intypedia001en</strong> 2
R C I S E<br />
Extracting the letters following the column order (first the letters in the first column, then the<br />
letters in the second column, then the ones in the third and so on) the ciphertext reads as<br />
follows:<br />
“a m r o o r c n a s n c o a n i e i l r s t x s u t p i e e”<br />
2.- Since the keyword has six letters, there should also be six columns. So the plaintext written<br />
out in six columns looks as follows:<br />
With the keyword written on top:<br />
C I P H E R<br />
I H A V E A<br />
C O M P L E<br />
T E E X A M<br />
W I T H S O<br />
L U T I O N<br />
So writing the letters of the columns, according to the alphabetical order of the letters of the<br />
keyword (first the C, then the E, then the H, then the I, then the P and finally the R), the<br />
ciphertext should look like this:<br />
“i c t w l e l a s o v p x h i h o e i u a m e t t a e m o n”<br />
EXERCISE 3<br />
I H A V E A<br />
C O M P L E<br />
T E E X A M<br />
W I T H S O<br />
L U T I O N<br />
With the monoalphabetic substitution methods broken by the Arabs’ discovery of<br />
cryptanalysis, at the end of the Late Middle Ages, specifically since the Renaissance, new<br />
encryption methods began to arise, like the polyalphabetic and nomenclator methods. The<br />
latter consisted of a catalogue of names that were going to be ciphered, so each one of them<br />
appeared associated with a word, a number or a group of symbols that would substitute the<br />
original name in the ciphertext.<br />
Exercises <strong>intypedia001en</strong> 3
Often, polyalphabetic and nomenclator methods were combined, like in the Alberti cipher disk.<br />
Looking at the following Alberti cipher disk:<br />
and the nomenclator:<br />
Phillip II 123<br />
King 124<br />
Walshingam 122<br />
Decipher the following text:<br />
“b aavqnpgnvsvoiycekcel”<br />
NOTE 1: For each ten deciphered letters, the outer ring (the one with the uppercase alphabet)<br />
has to rotate two positions clockwise.<br />
NOTE 2: When enciphering with the Alberti disk, the u corresponds to the v. And when<br />
deciphering, the meaning of the sentence is used to figure out which of the letters should it be.<br />
SOLUTION:<br />
With the rings in their original position:<br />
b a a v q n p g n v<br />
1 2 2 I S D E A D I<br />
With the outer ring rotated 2 positions clockwise:<br />
s v o i y c e k c e<br />
N F O R M 1 2 4 1 2<br />
With the outer ring rotated another 2 positions clockwise:<br />
l<br />
3<br />
This way, the plaintext (without taking into account the nomenclator) results in:<br />
Exercises <strong>intypedia001en</strong> 4
“122ISDEADINFORM124123”<br />
So, if we take the nomenclator into account (and adding a space between words in order to<br />
read it properly) the deciphered text reads as follows:<br />
“ Walshingam is dead Inform King Phillip II ”<br />
EXERCISE 4<br />
Substitution methods like Caesar replace each letter of the alphabet in the plaintext for<br />
another letter in a fixed position down the alphabet (in the Caesar methods this number is<br />
three).<br />
Knowing that the following ciphertext was obtained using the Caesar method, decipher the<br />
message knowing that the English letter frequency is as shown in the table below:<br />
“ drscsckxohkwzvoypmkockbdizoypwyxykvzrklodsmmszrob”<br />
E T A O I N<br />
10% 7% 6,5% 6% 5,6% 5,5%<br />
SOLUTION<br />
First of all we have to find the ciphertext letter that corresponds to the “e”, so we can know<br />
how many positions down the alphabet are the ciphertext letters in relation to the plaintext<br />
letters. Then the deciphering will be nearly automatic.<br />
If we count how many times the letters appear in the ciphertext, there are:<br />
O K S Y Z<br />
6 6 4 4 4<br />
The cipher letter “o” (the one that appears most times, along with the “k”) corresponds to the<br />
plaintext letter “e”. So the alphabet used must be:<br />
A B C D E F G H I J K L M N O P Q R S T U V W X Y Z<br />
k l m n o p q r s t u v w x y z a b c d e f g h i j<br />
Exercises <strong>intypedia001en</strong> 5
This is confirmed, because the following most frequent ciphertext letter is “k” which<br />
corresponds to the “a”. Since the ciphertext is very short, the rest of the letters don’t follow the<br />
typical frequency. The bigger the text, the closer it is to the aforementioned percentage.<br />
Considering the ciphertext:<br />
drscsckxohkwzvoypk mkockbdizoypwyxykvzrklodsmmszrob<br />
And using the attained alphabet:<br />
D R S C S C K X O H K W Z V O Y P K M K O C K B<br />
T H I S I S A N E X A M P L E O F A C A E S A R<br />
D I Z O Y P W Y X Y K V Z R K L O D S M M S Z R O B<br />
T Y P E O F M O N O A L P H A B E T I C C I P H E R<br />
Results in the following plaintext:<br />
“This is an example of a Caesar type of monoalphabetic cipher”<br />
EXERCISE 5<br />
When cryptanalysing a ciphertext, one of the first problems we face is finding out whether a<br />
transposition or substitution method has been used. In the first case, the letters haven’t<br />
changed their meaning, only the position, so the number of times each letter appears will<br />
probably correspond to the frequency in which it appears in the relevant language. Therefore,<br />
the method would be transposition.<br />
Knowing that the distribution of letters in Spanish is approximately:<br />
E A O L S N<br />
15 13 9 8 8 7<br />
Please reason out if the following ciphertext has been produced using a monoalphabetic<br />
substitution method or a permutation method:<br />
“Is modí es unovedad porquean te slos hombrñe spodan divid irs es encillamf, igu rac i nhum<br />
an asi nparentoda l ahist, oriaele. Sp ecial ist ano ssi rveheaquunpór ecioso eje mpl ar dees te<br />
extraoho. Mb renuevoquehe int entad ente ensabiose igénorantesen ms omenoss a biosymso<br />
men osig no rantesoporu na yo tradesu. Sverti entes yha cesdefi niríhe dichoquee,<br />
raunaconparac, on cretar e nrgicament, el aáe s pecie yhacer n oás v ertod oelradical”.<br />
Exercises <strong>intypedia001en</strong> 6
SOLUTION<br />
There is approximately the following amount of letters:<br />
e = 49<br />
a = 44<br />
o =32<br />
l =9<br />
s =29<br />
n =28<br />
Total letters = 368<br />
That makes: e= 13%; a=12%; 0=9%; l=2%; s= 8%; n = 8%, which is more or less the same as the<br />
natural frequency of letters in Spanish, therefore, this is a transposition cipher.<br />
Madrid, Spain, September 2010<br />
http://www.intypedia.com<br />
http://twitter.com/intypedia<br />
Exercises <strong>intypedia001en</strong> 7