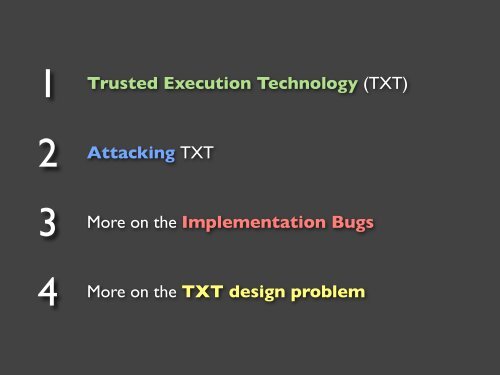
- Page 1: Attacking Intel ® Trusted Executio
- Page 5 and 6: Trusted Computing
- Page 7 and 8: PCR registers
- Page 9 and 10: TPM: Seal/Unseal Operation 0x123456
- Page 11 and 12: TPM: Quote Operation (Remote Attest
- Page 13 and 14: Static Root of Trust Measurement (S
- Page 15 and 16: SRTM in practice
- Page 17 and 18: But the key k must be present in th
- Page 19 and 20: Two ways to solve it...
- Page 21 and 22: Example #3: Remote Attestation Each
- Page 23 and 24: COMPLETENESS — we need to measure
- Page 25 and 26: Attempt to address the SRTM’s wea
- Page 27 and 28: SENTER — one of a few new instruc
- Page 29 and 30: TXT implementation: tboot
- Page 31 and 32: Xen + tboot example
- Page 34: Now we boot “untrusted” Xen (co
- Page 37 and 38: Now some live demos...
- Page 40: Tboot Demo #2: booting an untrusted
- Page 43 and 44: So what is this all for?
- Page 45 and 46: It’s all about TPM PCRs and secre
- Page 47 and 48: Launch time protection vs. runtime
- Page 49 and 50: Theoretically runtime-protection sh
- Page 51 and 52: Attacking TXT
- Page 53 and 54:
Q: What is more privileged than a h
- Page 55 and 56:
Q: Is this SMM some new thing? A: N
- Page 57 and 58:
SMM gets loaded before Late Launch.
- Page 59 and 60:
Q: Does TXT reload SMM on SENTER ex
- Page 61 and 62:
Oh...
- Page 63 and 64:
Let’s have a look at the actual S
- Page 65:
... and the shorter version...
- Page 69 and 70:
Wait! But how to infect the SMM han
- Page 71:
Let’s take a look at the live dem
- Page 74 and 75:
So how we can get into SMM memory (
- Page 76 and 77:
2006: Loic Duflot (not an attack ag
- Page 78 and 79:
So, how did we get around this vici
- Page 83 and 84:
Meet Atmel 26DF321 SPI-flash
- Page 85 and 86:
Looks promising, but...
- Page 87 and 88:
So, we used a different approach…
- Page 89 and 90:
Memory Remapping on Q35 chipset TOU
- Page 91:
#define TSEG_BASE 0x7e500000 u64 ta
- Page 96 and 97:
Intel patched the bug in August 200
- Page 98 and 99:
VU#127284
- Page 100 and 101:
We have provided Intel with the det
- Page 102 and 103:
We suspect it might affect all rece
- Page 104 and 105:
Intel contacted CERT CC informing t
- Page 106 and 107:
We plan to discuss the details of t
- Page 108 and 109:
More on the TXT Design Problem
- Page 110 and 111:
SMM Transfer Monitor (STM) Communic
- Page 112 and 113:
Intel Who should write an STM? OEMs
- Page 114 and 115:
Intel told us they do have STM spec
- Page 116 and 117:
Intel might be right claiming that
- Page 118 and 119:
We cannot make our mind on this unt
- Page 120 and 121:
Summary
- Page 122:
http://invisiblethingslab.com