- Page 1 and 2: Mac OS XSecurity ConfigurationFor V
- Page 3 and 4: 1 ContentsPreface 11 About This Gui
- Page 5 and 6: 52 PowerPC-Based Systems52 Using th
- Page 7 and 8: 130 Encrypting Home Folders131 Over
- Page 9 and 10: 172 Securing Network Sharing Servic
- Page 11 and 12: About This GuidePrefaceThis guide p
- Page 13 and 14: Â Chapter 13, “Advanced Security
- Page 15 and 16: This guide...User ManagementWeb Tec
- Page 17 and 18: For additional security-specific in
- Page 19 and 20: 1 Introductionto Mac OS X SecurityA
- Page 21 and 22: Apple built the foundation of Mac O
- Page 23 and 24: These functions are used when the s
- Page 25 and 26: Parental ControlsParental controls
- Page 27 and 28: Other commercial smart card vendors
- Page 29 and 30: 2 InstallingMac OS X2Use this chapt
- Page 31 and 32: 9 In the “Install Summary screen,
- Page 33 and 34: Avoid names and short names like
- Page 35 and 36: From the Command Line:# Updating fr
- Page 37 and 38: From the Command Line:# Updating Ma
- Page 39 and 40: When you use Disk Utility to verify
- Page 41 and 42: 3 ProtectingSystem Hardware3Use thi
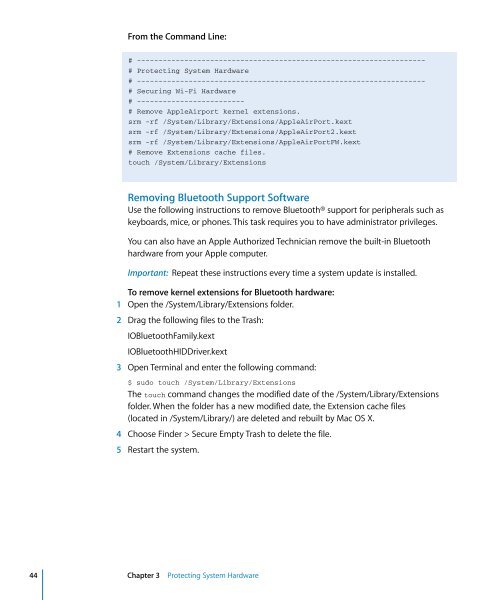
- Page 43: OS ComponentsMac OS X provides kern
- Page 47 and 48: From the Command Line:# Securing Vi
- Page 49 and 50: From the Command Line:# Securing Fi
- Page 51 and 52: 4 SecuringGlobal System Settings4Us
- Page 53 and 54: You can test your settings by attem
- Page 55 and 56: Intel-based and PowerPC-based compu
- Page 57 and 58: When an application requests author
- Page 59 and 60: 5 SecuringAccounts5Use this chapter
- Page 61 and 62: It is risky to assign the same user
- Page 63 and 64: To securely configure an account wi
- Page 65 and 66: Securing Administrator AccountsEach
- Page 67 and 68: 3 In the Defaults specification sec
- Page 69 and 70: The authentication and contacts sea
- Page 71 and 72: Â FIPS-181 compliant: According to
- Page 73 and 74: Before the smart card processes inf
- Page 75 and 76: You can create multiple keychains,
- Page 77 and 78: 2 Enter a name, select a location f
- Page 79 and 80: Using Portable and Network-Based Ke
- Page 81 and 82: 6 SecuringSystem Preferences6Use th
- Page 83 and 84: Securing .Mac Preferences.Mac is a
- Page 85 and 86: 3 Don’t register your computer fo
- Page 87 and 88: To securely configure Accounts pref
- Page 89 and 90: To securely configure Appearance pr
- Page 91 and 92: This does not prevent users from re
- Page 93 and 94: 4 Choose a time zone.From the Comma
- Page 95 and 96:
From the Command Line:# Securing De
- Page 97 and 98:
2 From the Sleep pane, set “Put t
- Page 99 and 100:
From the Command Line:# Securing Ex
- Page 101 and 102:
To securely configure Network prefe
- Page 103 and 104:
If the account you want to manage i
- Page 105 and 106:
To securely configure Print & Fax p
- Page 107 and 108:
You can find and install third-part
- Page 109 and 110:
FileVault SecurityMac OS X includes
- Page 111 and 112:
 “Set access for specific servi
- Page 113 and 114:
You can change your computer’s na
- Page 115 and 116:
To securely configure Software Upda
- Page 117 and 118:
The following shows the Text to Spe
- Page 119 and 120:
By placing specific folders or disk
- Page 121 and 122:
To enter Target Disk Mode, hold dow
- Page 123 and 124:
7 SecuringData and UsingEncryption7
- Page 125 and 126:
Interpreting POSIX PermissionsTo in
- Page 127 and 128:
In this example, the folder named s
- Page 129 and 130:
Not all applications recognize the
- Page 131 and 132:
If you want to protect file or fold
- Page 133 and 134:
This provides network management of
- Page 135 and 136:
Make sure the size of the image is
- Page 137 and 138:
A zero-out erase sets all data bits
- Page 139 and 140:
Using Secure Empty TrashSecure Empt
- Page 141 and 142:
8 SecuringSystem Swap andHibernatio
- Page 143 and 144:
9 AvoidingMultiple SimultaneousAcco
- Page 145 and 146:
10 EnsuringData Integrity withBacku
- Page 147 and 148:
11 InformationAssurance withApplica
- Page 149 and 150:
 NTLM Kerberos Version 5 (GSSAP
- Page 151 and 152:
Safari supports server-side and cli
- Page 153 and 154:
Before they are opened, the followi
- Page 155 and 156:
Website forms can include items tha
- Page 157 and 158:
iChat AV Encryption leverages a PKI
- Page 159 and 160:
When you and your buddy have the .M
- Page 161 and 162:
IPSec requires security certificate
- Page 163 and 164:
Mac OS X includes a firewall. If yo
- Page 165 and 166:
4 Click Advanced.5 Select the Enabl
- Page 167 and 168:
12 InformationAssurance withService
- Page 169 and 170:
Before using Bonjour to connect to
- Page 171 and 172:
Securing the Back to My Mac (BTMM)
- Page 173 and 174:
Screen Sharing (VNC)Screen Sharing
- Page 175 and 176:
From the Command Line:# Disable Fil
- Page 177 and 178:
Enabling an SSH ConnectionTo enable
- Page 179 and 180:
5 On the client, enter a complex pa
- Page 181 and 182:
$ mkdir ~/.ssh/2 If ~/.ssh/known_ho
- Page 183 and 184:
You can add a specific host and opt
- Page 185 and 186:
The first time you connect, you hav
- Page 187 and 188:
From the Command Line:# Remote Appl
- Page 189 and 190:
From the Command Line:# Internet Sh
- Page 191 and 192:
13 AdvancedSecurity Management13Use
- Page 193 and 194:
When a program asks for a right, Au
- Page 195 and 196:
The Security Server requests authen
- Page 197 and 198:
Validating File IntegrityWhen downl
- Page 199 and 200:
To inspect a specific requirement,
- Page 201 and 202:
The following sample line specifies
- Page 203 and 204:
If auditing is enabled, the /etc/rc
- Page 205 and 206:
Intrusion Detection SystemsAn intru
- Page 207 and 208:
ASecurity ChecklistAAppendixUse the
- Page 209 and 210:
Account Configuration Action ItemsF
- Page 211 and 212:
Action Items Completed? NotesSecure
- Page 213 and 214:
Action Item Completed? NotesInstall
- Page 215 and 216:
BSecurity ScriptsBAppendix# Updatin
- Page 217 and 218:
# Securing Global System Settings#
- Page 219 and 220:
# Securing Energy Saver Preferences
- Page 221 and 222:
defaults write "com.apple.speech.re
- Page 223 and 224:
GlossaryGlossaryThis glossary defin
- Page 225 and 226:
computational cluster A group of co
- Page 227 and 228:
FTP File Transfer Protocol. A proto
- Page 229 and 230:
NetBoot server A Mac OS X server yo
- Page 231 and 232:
public key One of two asymmetric ke
- Page 233 and 234:
streaming Delivery of video or audi
- Page 235 and 236:
IndexIndex.Mac preferences 83-85, 1
- Page 237 and 238:
Gglobal file permissions 128-129gri
- Page 239 and 240:
SSafari preferences 150, 152-156san