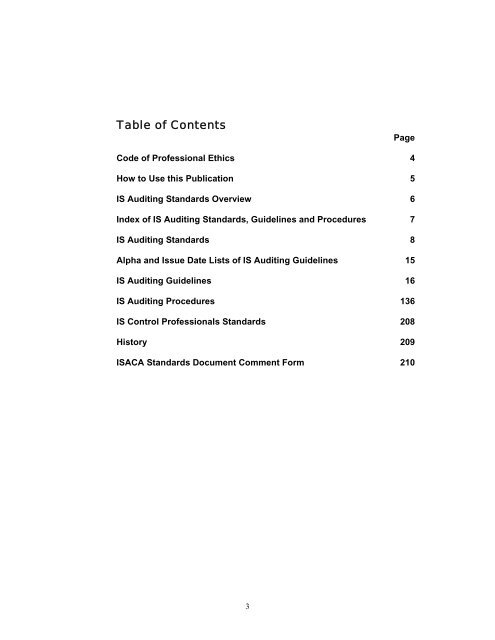
- Page 1: IS Standards, Guidelines and Proced
- Page 5 and 6: How to Use this PublicationRelation
- Page 7 and 8: Index of IS Auditing StandardsEffec
- Page 9 and 10: 02 The purpose of this IS Auditing
- Page 11 and 12: S7 ReportingIntroduction01 ISACA IS
- Page 13 and 14: 18 The risk of not detecting a mate
- Page 15 and 16: IS Auditing GuidelinesAlpha list of
- Page 17 and 18: G1 Using the Work of Other Auditors
- Page 19 and 20: G2 Audit Evidence Requirement conti
- Page 21 and 22: G3 Use of Computer Assisted Audit T
- Page 23 and 24: G4 Outsourcing of IS Activities to
- Page 25 and 26: G5 Audit Charter1. BACKGROUND1.1 Li
- Page 27 and 28: G6 Materiality Concepts for Auditin
- Page 29 and 30: G7 Due Professional Care1. BACKGROU
- Page 31 and 32: G9 Audit Considerations for Irregul
- Page 33 and 34: 6.2.2 Where external reporting is r
- Page 35 and 36: G10 Audit Sampling continued• The
- Page 37 and 38: G11 Effect of Pervasive IS Controls
- Page 39 and 40: G11 Effect of Pervasive IS Controls
- Page 41 and 42: G12 Organisational Relationship and
- Page 43 and 44: G13 Use of Risk Assessment in Audit
- Page 45 and 46: G13 Use of Risk Assessment in Audit
- Page 47 and 48: G14 Application Systems Review cont
- Page 49 and 50: G15 Planning continued2.5.1 Auditin
- Page 51 and 52: G16 Effect of Third Parties on an O
- Page 53 and 54:
G16 Effect of Third Parties on an O
- Page 55 and 56:
G17 Effect of Nonaudit Role on the
- Page 57 and 58:
G18 IT Governance1. BACKGROUND1.1 L
- Page 59 and 60:
G18 IT Governance continued• The
- Page 61 and 62:
G19 Irregularities and Illegal Acts
- Page 63 and 64:
G19 Irregularities and Illegal Acts
- Page 65 and 66:
G20 Reporting1.1 BACKGROUND1.1 Link
- Page 67 and 68:
G20 Reporting continued3.5.1 Where
- Page 69 and 70:
G21 Enterprise Resource Planning (E
- Page 71 and 72:
G21 Enterprise Resource Planning (E
- Page 73 and 74:
G21 Enterprise Resource Planning (E
- Page 75 and 76:
G21 Enterprise Resource Planning (E
- Page 77 and 78:
G21 Enterprise Resource Planning (E
- Page 79 and 80:
G22 Business-to-consumer (B2C) E-co
- Page 81 and 82:
G22 Business-to-consumer (B2C) E-co
- Page 83 and 84:
G22 Business-to-consumer (B2C) E-co
- Page 85 and 86:
G23 System Development Life Cycle (
- Page 87 and 88:
G23 System Development Life Cycle (
- Page 89 and 90:
G24 Internet Banking1. BACKGROUND1.
- Page 91 and 92:
G24 Internet Banking continued3.1.3
- Page 93 and 94:
G24 Internet Banking continued7.1.3
- Page 95 and 96:
G24 Internet Banking continued7.2.9
- Page 97 and 98:
G25 Review of Virtual Private Netwo
- Page 99 and 100:
G25 Review of Virtual Private Netwo
- Page 101 and 102:
7.2.3 Any key concerns of the stake
- Page 103 and 104:
• Use external experts, where nec
- Page 105 and 106:
G26 Business Process Reengineering
- Page 107 and 108:
G26 Business Process Reengineering
- Page 109 and 110:
G26 Business Process Reengineering
- Page 111 and 112:
G27 Mobile Computing continued2.3.1
- Page 113 and 114:
G27 Mobile Computing continuedCOBIT
- Page 115 and 116:
G28 Computer Forensics continued•
- Page 117 and 118:
G28 Computer Forensics continued6.1
- Page 119 and 120:
G28 Computer Forensics conitnued•
- Page 121 and 122:
G29 Post-implementation Review cont
- Page 123 and 124:
G29 Post-implementation Review cont
- Page 125 and 126:
G30 Competence1. BACKGROUND1.1 Link
- Page 127 and 128:
G30 Competence continued2.5.1 Gaps
- Page 129 and 130:
G31 Privacy1. BACKGROUND1.1 Linkage
- Page 131 and 132:
G31 Privacy continued4.1.1 An incre
- Page 133 and 134:
G31 Privacy continuedTable 2—CHEC
- Page 135 and 136:
G31 Privacy continued8.6.1 Reasonab
- Page 137 and 138:
IS Risk Assessment Measurement Proc
- Page 139 and 140:
IS Risk Assessment Measurement Proc
- Page 141 and 142:
IS Risk Assessment Measurement Proc
- Page 143 and 144:
IS Risk Assessment Measurement Proc
- Page 145 and 146:
IS Risk Assessment Measurement Proc
- Page 147 and 148:
IS Risk Assessment Measurement Proc
- Page 149 and 150:
Digital Signature and Key Managemen
- Page 151 and 152:
SpecificTechnicalAspect of a CATech
- Page 153 and 154:
Intrusion Detection Systems (IDS) R
- Page 155 and 156:
Intrusion Detection Systems (IDS) R
- Page 157 and 158:
OtherimportantcontrolissuesPerforma
- Page 159 and 160:
Virus and Other Malicious Code Proc
- Page 161 and 162:
Suggested Procedures for Preventing
- Page 163 and 164:
Suggested Techniques to Assess the
- Page 165 and 166:
Control Risk Self-assessment Proced
- Page 167 and 168:
Control Risk Self-assessment Proced
- Page 169 and 170:
Control Risk Self-assessment Proced
- Page 171 and 172:
Firewalls Procedure P61. BACKGROUND
- Page 173 and 174:
Firewalls Procedure P6 continued2.1
- Page 175 and 176:
Firewalls Procedure P6 continuedAdv
- Page 177 and 178:
Firewalls Procedure P6 continued•
- Page 179 and 180:
Firewalls Procedure #6 continued5.1
- Page 181 and 182:
Inherent risks ofpacket filteringHy
- Page 183 and 184:
Firewalls Procedure P6 continued7.
- Page 185 and 186:
Irregularities and Illegal Acts Pro
- Page 187 and 188:
Irregularities and Illegal Acts Pro
- Page 189 and 190:
Irregularities and Illegal Acts Pro
- Page 191 and 192:
Security Assessment-Penetration Tes
- Page 193 and 194:
Security Assessment-Penetration Tes
- Page 195 and 196:
PlanningcontinuedSkillsRequiredAgre
- Page 197 and 198:
InternetPenetrationTestingcontinued
- Page 199 and 200:
WirelesscontinuedWebApplicationSugg
- Page 201 and 202:
Security Assessment-Penetration Tes
- Page 203 and 204:
Evaluation of Management Control Ov
- Page 205 and 206:
Evaluation of Management Control Ov
- Page 207 and 208:
Aspects ofEncryptionDigitalSignatur
- Page 209 and 210:
HistoryStatements on Information Sy