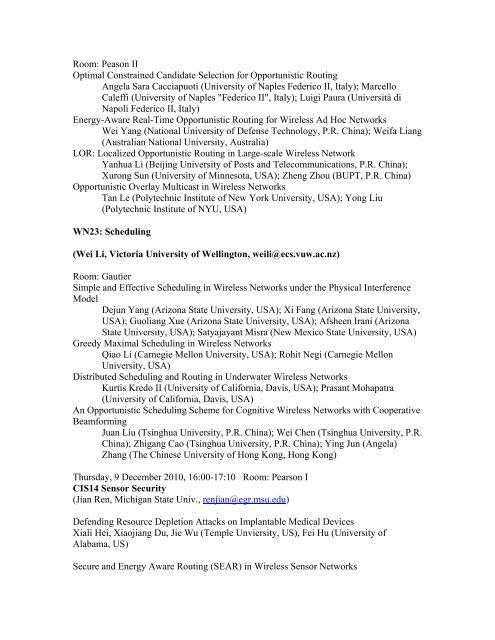
Room: Peason IIOptimal Constrained Candidate Selection for Opportunistic RoutingAngela Sara Cacciapuoti (University of Naples Federico II, Italy); MarcelloCaleffi (University of Naples "Federico II", Italy); Luigi Paura (Università diNapoli Federico II, Italy)Energy-Aware Real-Time Opportunistic Routing for Wireless Ad Hoc NetworksWei Yang (National University of Defense Technology, P.R. China); Weifa Liang(Australian National University, Australia)LOR: Localized Opportunistic Routing in Large-scale Wireless NetworkYanhua Li (Beijing University of Posts and Telecommunications, P.R. China);Xurong Sun (University of Minnesota, USA); Zheng Zhou (BUPT, P.R. China)Opportunistic Overlay Multicast in Wireless NetworksTan Le (Polytechnic Institute of New York University, USA); Yong Liu(Polytechnic Institute of NYU, USA)WN23: Scheduling(Wei Li, Victoria University of Wellington, weili@ecs.vuw.ac.nz)Room: GautierSimple and Effective Scheduling in Wireless Networks under the Physical InterferenceModelDejun Yang (Arizona State University, USA); Xi Fang (Arizona State University,USA); Guoliang Xue (Arizona State University, USA); Afsheen Irani (ArizonaState University, USA); Satyajayant Misra (New Mexico State University, USA)Greedy Maximal Scheduling in Wireless NetworksQiao Li (Carnegie Mellon University, USA); Rohit Negi (Carnegie MellonUniversity, USA)Distributed Scheduling and Routing in Underwater Wireless NetworksKurtis Kredo II (University of California, Davis, USA); Prasant Mohapatra(University of California, Davis, USA)An Opportunistic Scheduling Scheme for Cognitive Wireless Networks with CooperativeBeamformingJuan Liu (Tsinghua University, P.R. China); Wei Chen (Tsinghua University, P.R.China); Zhigang Cao (Tsinghua University, P.R. China); Ying Jun (Angela)Zhang (The Chinese University of Hong Kong, Hong Kong)<strong>Thursday</strong>, 9 <strong>December</strong> 2010, 16:00-17:10 Room: Pearson ICIS14 Sensor Security(Jian Ren, Michigan State Univ., renjian@egr.msu.edu)Defending Resource Depletion Attacks on Implantable Medical DevicesXiali Hei, Xiaojiang Du, Jie Wu (Temple Unviersity, US), Fei Hu (University ofAlabama, US)Secure and Energy Aware Routing (SEAR) in Wireless Sensor Networks
Di Tang (Michigan State University, US), Tingting Jiang (Virginia Tech, US), Jian Ren(Michigan State University, US)Secure Cooperation Incentive Scheme with Limited Use of Public Key Cryptography forMulti-hop Wireless NetworkMohamed Mahmoud, Sherman Shen (University of Waterloo, CA)Robust State Estimation Under False Data Injection in Distributed SensorNetworksShanshan Zheng, Tao Jiang, John Baras (University of Maryland College Park,US)<strong>Thursday</strong>, 9 <strong>December</strong> 2010 16:00-17:10 Room: Merrick IICSSMA11: Multimedia Streaming(Honggang Wang, University of Massachusetts, USA, hwang1@umassd.edu)Collaborative ISP-CP Live StreamingHim Cheng (The Hong Kong University of Science and Technology, HK);Gary Chan (The Hong Kong University of Science and Technology, CN);Guangyu Shi (Huawei Technologies Co., Ltd, CN);Jian Chen (Huawei Technologies Co., Ltd, CN);Hongbo Zhang (Huawei Technologies Co., Ltd, CN)Optimal Pricing for Mobile Video Streaming Using Redistribution Behavior AnalysisWanyi Lin (University of Maryland, US);K. J. Ray Liu (Department of Electrical and Computer Engineering, University ofMaryland, US)Robust Cooperation Strategies for Wireless Video Streaming Social NetworksWanyi Lin (University of Maryland, US);Hong Zhao (University of Alberta, CA);K. J. Ray Liu (Department of Electrical and Computer Engineering, University ofMaryland, US)Multi-Source Latency Variation Synchronization for Collaborative ApplicationsAbhishek Bhattacharya (Florida International University, US);Zhenyu Yang (Florida International University, US);Deng Pan (Florida International University, US)<strong>Thursday</strong>, 9 <strong>December</strong> 2010 16:00-17:10 Room: Merrick ICSSMA14: Networks and Services Architecture and Engineering(Fabrizio Granelli, University of Trento, Italy; granelli@disi.unitn.it)CommuSearch: Small-World Based Semantic Search Architecture in P2P NetworksFeiteng Xue (Unversity of Electronic Science and Technology of China, China)Gang Feng (University of Electronic Science and Technology of China, China)Yide Zhang (University of Electronic Science and Technology of China, China)
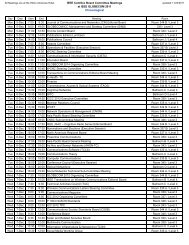
- Page 1 and 2: Thursday, December 910:00 - 11:10AH
- Page 3 and 4: Information-theoretic methods for t
- Page 5 and 6: Power Allocation for Distributed Tu
- Page 7 and 8: Peer-Assisted Caching for Scalable
- Page 9 and 10: Thursday, 7 December 2010 10:00-11:
- Page 11 and 12: (Mario Marchese, University of Geno
- Page 13 and 14: Thursday, 9 December 2010 10:00-11:
- Page 15 and 16: Guido Dietl, Olivier Labrèche (DOC
- Page 17: Aravind M Canthadai (University of
- Page 22 and 23: A Network Management System for a H
- Page 24 and 25: On the Complexity of Power Minimiza
- Page 26 and 27: Vehicle-to-Roadside Multihop Data D
- Page 28 and 29: Rolf Winter (NEC Network Labs, DE)H
- Page 31: Thursday, December 916:00 - 17:10AH
- Page 36 and 37: On Minimizing Network Wide Node Upd
- Page 38 and 39: Shuntaro Kashihara (KDDI R&D Labora
- Page 40 and 41: Azzedine Boukerche (Univ. of Ottawa
- Page 42 and 43: Zhiping Cai (National University of
- Page 44 and 45: Khoa Phan, Jaeok Park, Mihaela van
- Page 46 and 47: AHSN36: Modelling and Analysis(Zhi
- Page 48 and 49: (Marcello Caleffi, University of Na
- Page 50 and 51: Renata Teixeira (CNRS and Universit
- Page 52 and 53: Simple Protocol Enhancements of Rap
- Page 54 and 55: Thursday, 9 December 2010 17:20-18:
- Page 56 and 57: Thursday, 9 December 2010 17:20-18: