IPv6 Security
IPv6 Security
IPv6 Security
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
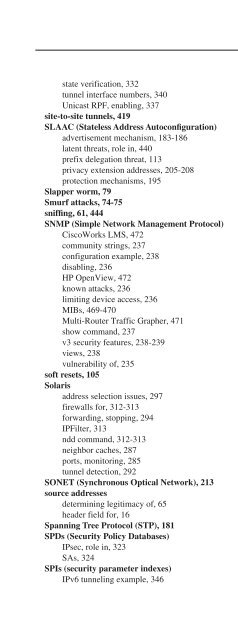
SVGs (Standby Virtual Gateways)537state verification, 332tunnel interface numbers, 340Unicast RPF, enabling, 337site-to-site tunnels, 419SLAAC (Stateless Address Autoconfiguration)advertisement mechanism, 183-186latent threats, role in, 440prefix delegation threat, 113privacy extension addresses, 205-208protection mechanisms, 195Slapper worm, 79Smurf attacks, 74-75sniffing, 61, 444SNMP (Simple Network Management Protocol)CiscoWorks LMS, 472community strings, 237configuration example, 238disabling, 236HP OpenView, 472known attacks, 236limiting device access, 236MIBs, 469-470Multi-Router Traffic Grapher, 471show command, 237v3 security features, 238-239views, 238vulnerability of, 235soft resets, 105Solarisaddress selection issues, 297firewalls for, 312-313forwarding, stopping, 294IPFilter, 313ndd command, 312-313neighbor caches, 287ports, monitoring, 285tunnel detection, 292SONET (Synchronous Optical Network), 213source addressesdetermining legitimacy of, 65header field for, 16Spanning Tree Protocol (STP), 181SPDs (<strong>Security</strong> Policy Databases)IPsec, role in, 323SAs, 324SPIs (security parameter indexes)<strong>IPv6</strong> tunneling example, 346Keys, 247purpose of, 324split tunneling, 370spoofingantispoofing measures, 128CEF tables for defense, 66determining legitimacy of source addresses, 65ingress/egress filtering to prevent attacks, 66Layer 3 and Layer 4, 65-69M<strong>IPv6</strong>, 388-389Neighbor Advertisements, 188-189policy for, 505redirection messages, 193Unicast RPF checks, 66-69spyware, 282SSH (Secure Shell)firewall configuration for, 153-154policing control protocols, 268remote access with, 226-228SSL (Secure Socket Layer)defined, 368IPsec as replacement, 502VPNs. See SSL VPNsSSL VPNsaddress pool usage, 371advantages of, 368AnyConnect, 369-373ASA configuration commands, 370-371client connection status, 371clientless style, 368configuration steps, 369dual-stack access, 373remote connections, 369split tunneling, 370stateless autoconfigurationdefined, 4Stateless Address Autoconfiguration. SeeSLAACstatic routing firewall configuration, 162-163static tunnelsdefined, 420securing, 447-448STP (Spanning Tree Protocol), 181Sun Solaris operating system. See SolarisSVC (SSL VPN client). See AnyConnectSVF (Standby Virtual Forwarders), 260SVGs (Standby Virtual Gateways), 260