2-Extended Analysis-Full
2-Extended Analysis-Full
2-Extended Analysis-Full
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
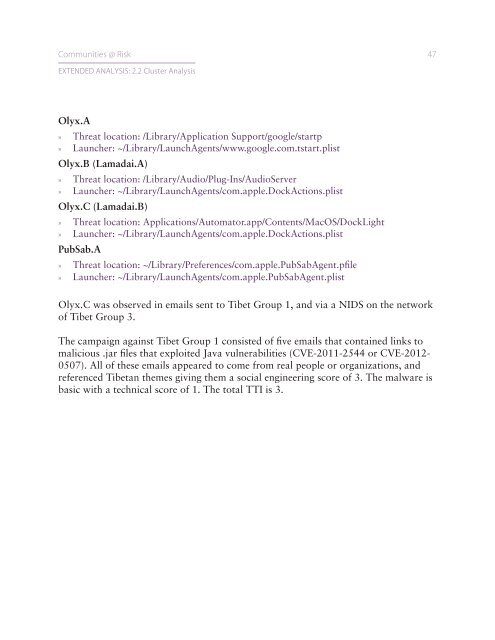
Communities @ Risk 47EXTENDED ANALYSIS: 2.2 Cluster <strong>Analysis</strong>Olyx.A»»Threat location: /Library/Application Support/google/startp»»Launcher: ~/Library/LaunchAgents/www.google.com.tstart.plistOlyx.B (Lamadai.A)»»Threat location: /Library/Audio/Plug-Ins/AudioServer»»Launcher: ~/Library/LaunchAgents/com.apple.DockActions.plistOlyx.C (Lamadai.B)»»Threat location: Applications/Automator.app/Contents/MacOS/DockLight»»Launcher: ~/Library/LaunchAgents/com.apple.DockActions.plistPubSab.A»»Threat location: ~/Library/Preferences/com.apple.PubSabAgent.pfile»»Launcher: ~/Library/LaunchAgents/com.apple.PubSabAgent.plistOlyx.C was observed in emails sent to Tibet Group 1, and via a NIDS on the networkof Tibet Group 3.The campaign against Tibet Group 1 consisted of five emails that contained links tomalicious .jar files that exploited Java vulnerabilities (CVE-2011-2544 or CVE-2012-0507). All of these emails appeared to come from real people or organizations, andreferenced Tibetan themes giving them a social engineering score of 3. The malware isbasic with a technical score of 1. The total TTI is 3.