A Scalable and Format-Compliant Encryption Scheme for H.264 ...
A Scalable and Format-Compliant Encryption Scheme for H.264 ...
A Scalable and Format-Compliant Encryption Scheme for H.264 ...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
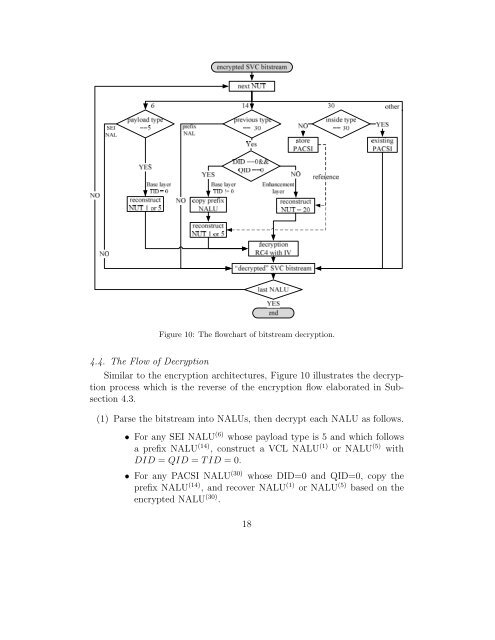
Figure 10: The flowchart of bitstream decryption.4.4. The Flow of DecryptionSimilar to the encryption architectures, Figure 10 illustrates the decryptionprocess which is the reverse of the encryption flow elaborated in Subsection4.3.(1) Parse the bitstream into NALUs, then decrypt each NALU as follows.• For any SEI NALU (6) whose payload type is 5 <strong>and</strong> which followsa prefix NALU (14) , construct a VCL NALU (1) or NALU (5) withDID = QID = TID =0.• For any PACSI NALU (30) whose DID=0 <strong>and</strong> QID=0, copy theprefix NALU (14) , <strong>and</strong> recover NALU (1) or NALU (5) based on theencrypted NALU (30) .18