Attacking Hypervisors via Firmware and Hardware
nd5ln5n
nd5ln5n
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
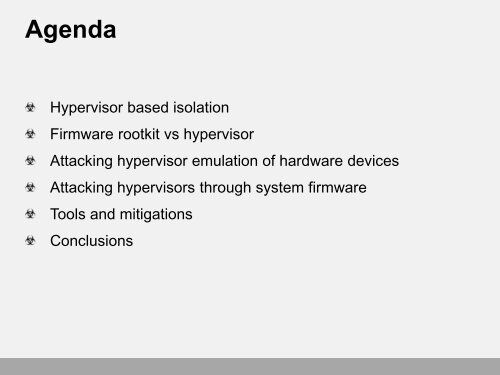
AgendaHypervisor based isolation<strong>Firmware</strong> rootkit vs hypervisor<strong>Attacking</strong> hypervisor emulation of hardware devices<strong>Attacking</strong> hypervisors through system firmwareTools <strong>and</strong> mitigationsConclusions


![Exploring Your System Deeper [with CHIPSEC] is Not Naughty](https://img.yumpu.com/58104997/1/190x107/exploring-your-system-deeper-with-chipsec-is-not-naughty.jpg?quality=85)