Attacking Hypervisors via Firmware and Hardware
nd5ln5n
nd5ln5n
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
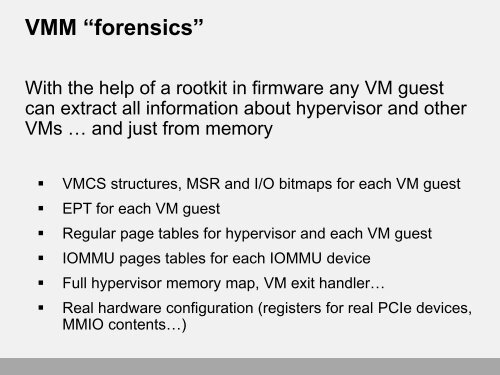
VMM “forensics”With the help of a rootkit in firmware any VM guestcan extract all information about hypervisor <strong>and</strong> otherVMs … <strong>and</strong> just from memory• VMCS structures, MSR <strong>and</strong> I/O bitmaps for each VM guest• EPT for each VM guest• Regular page tables for hypervisor <strong>and</strong> each VM guest• IOMMU pages tables for each IOMMU device• Full hypervisor memory map, VM exit h<strong>and</strong>ler…• Real hardware configuration (registers for real PCIe devices,MMIO contents…)


![Exploring Your System Deeper [with CHIPSEC] is Not Naughty](https://img.yumpu.com/58104997/1/190x107/exploring-your-system-deeper-with-chipsec-is-not-naughty.jpg?quality=85)