Security Jiujitsu
conf2015_DVeuve_Splunk_SecurityCompliance_SecurityJiujitsuBuildingCorrelation
conf2015_DVeuve_Splunk_SecurityCompliance_SecurityJiujitsuBuildingCorrelation
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
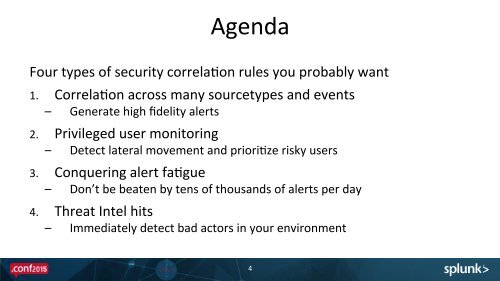
Agenda <br />
Four types of security correlaEon rules you probably want <br />
1. CorrelaEon across many sourcetypes and events <br />
– Generate high fidelity alerts <br />
2. Privileged user monitoring <br />
– Detect lateral movement and prioriEze risky users <br />
3. Conquering alert faEgue <br />
– Don’t be beaten by tens of thousands of alerts per day <br />
4. Threat Intel hits <br />
– Immediately detect bad actors in your environment <br />
4