Prevention of SQL injection in E- Commerce
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
<strong>Prevention</strong> <strong>of</strong> <strong>SQL</strong> <strong><strong>in</strong>jection</strong>…<br />
After review<strong>in</strong>g numerous electronic journals, articles from IEEE/FCI journals and gathered <strong>in</strong>formation<br />
provides sufficient knowledge about <strong>SQL</strong> <strong><strong>in</strong>jection</strong>, it‟s attack<strong>in</strong>g methodology and its prevention. The<br />
successive review <strong>of</strong> dist<strong>in</strong>ctive papers is presented herewith.<br />
Gregory T. Buehrer, Bruce W. Weide, and Paolo A. G. Sivilotti, <strong>in</strong> the research paper “Us<strong>in</strong>g Parse<br />
Tree Validation to Prevent <strong>SQL</strong> Injection Attacks” publishes there commendable work <strong>in</strong> 2005. The techniques<br />
for sql <strong><strong>in</strong>jection</strong> discovery seems impressive as this paper also covered the <strong>SQL</strong> parse tree validation very<br />
specifically which is mentionable.<br />
Zhendong Su and Gary Wassermann, <strong>in</strong> 2006 published their research <strong>in</strong> <strong>SQL</strong> <strong><strong>in</strong>jection</strong> entitled “The<br />
Essence <strong>of</strong> Command Injection Attacks <strong>in</strong> Web Applications” and covered the specific methods to check and<br />
sanitize <strong>in</strong>put query us<strong>in</strong>g <strong>SQL</strong>CHECK, it use the augmented questions and <strong>SQL</strong>CHECK grammar to validate<br />
query.<br />
Stephen Thomas and Laurie Williams, worked so long <strong>in</strong> the field <strong>of</strong> <strong>SQL</strong> <strong><strong>in</strong>jection</strong> and <strong>in</strong> 2007, <strong>in</strong> their<br />
research paper, entitled “Automated Protection <strong>of</strong> PHP Applications aga<strong>in</strong>st <strong>SQL</strong>-<strong><strong>in</strong>jection</strong> Attacks” they<br />
covered an authentic scheme to protect application automatically from <strong>SQL</strong> <strong><strong>in</strong>jection</strong> <strong>in</strong>trusion. This authentic<br />
approach comb<strong>in</strong>es static, dynamic analysis and <strong>in</strong>telligent code re-eng<strong>in</strong>eer<strong>in</strong>g to secure exist<strong>in</strong>g properties.<br />
Ke Wei, M. Muthuprasanna & Suraj Kothari <strong>in</strong> 2007, published their work entitled “Prevent<strong>in</strong>g <strong>SQL</strong> Injection<br />
Attacks <strong>in</strong> Stored Procedures” and through this they provides a novel approach to shield the stored procedures<br />
from attack and detect <strong>SQL</strong> <strong><strong>in</strong>jection</strong> from websites. Their method <strong>in</strong>cludes runtime check with subsequent<br />
application code analysis to elim<strong>in</strong>ate vulnerability to attack. The key method beh<strong>in</strong>d this vulnerability attack is<br />
that it modifies the composition <strong>of</strong> the orig<strong>in</strong>al <strong>SQL</strong> statement and identifies the <strong>SQL</strong> <strong><strong>in</strong>jection</strong> attack. The<br />
process is divided <strong>in</strong> two <strong>in</strong>stalments, one is <strong>of</strong>f-l<strong>in</strong>e and another one is run-time <strong>in</strong> real time basis. In the <strong>of</strong>fl<strong>in</strong>e<br />
phase, previously stored procedures uses a parser to pre-process and detect <strong>SQL</strong> statements <strong>in</strong> the work<strong>in</strong>g<br />
call for run-time analysis but <strong>in</strong> the run-time phase, the technique monitors all run-time generated <strong>SQL</strong> queries<br />
related with the user <strong>in</strong>put and checks these with the orig<strong>in</strong>al structure <strong>of</strong> the <strong>SQL</strong> statement after gett<strong>in</strong>g <strong>in</strong>put<br />
from the user.<br />
III. Pr<strong>in</strong>ciple<br />
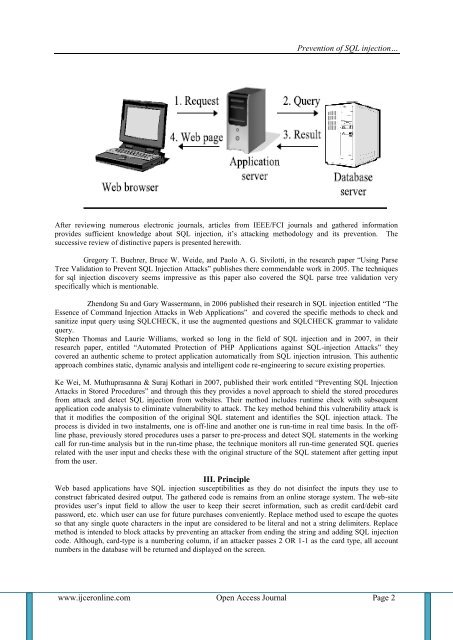
Web based applications have <strong>SQL</strong> <strong><strong>in</strong>jection</strong> susceptibilities as they do not dis<strong>in</strong>fect the <strong>in</strong>puts they use to<br />
construct fabricated desired output. The gathered code is rema<strong>in</strong>s from an onl<strong>in</strong>e storage system. The web-site<br />
provides user‟s <strong>in</strong>put field to allow the user to keep their secret <strong>in</strong>formation, such as credit card/debit card<br />
password, etc. which user can use for future purchases conveniently. Replace method used to escape the quotes<br />
so that any s<strong>in</strong>gle quote characters <strong>in</strong> the <strong>in</strong>put are considered to be literal and not a str<strong>in</strong>g delimiters. Replace<br />
method is <strong>in</strong>tended to block attacks by prevent<strong>in</strong>g an attacker from end<strong>in</strong>g the str<strong>in</strong>g and add<strong>in</strong>g <strong>SQL</strong> <strong><strong>in</strong>jection</strong><br />
code. Although, card-type is a number<strong>in</strong>g column, if an attacker passes 2 OR 1-1 as the card type, all account<br />
numbers <strong>in</strong> the database will be returned and displayed on the screen.<br />
www.ijceronl<strong>in</strong>e.com Open Access Journal Page 2