Intel SGX Enclave Support in Windows 10 Fall Update (Threshold 2)
1ks6upt
1ks6upt
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
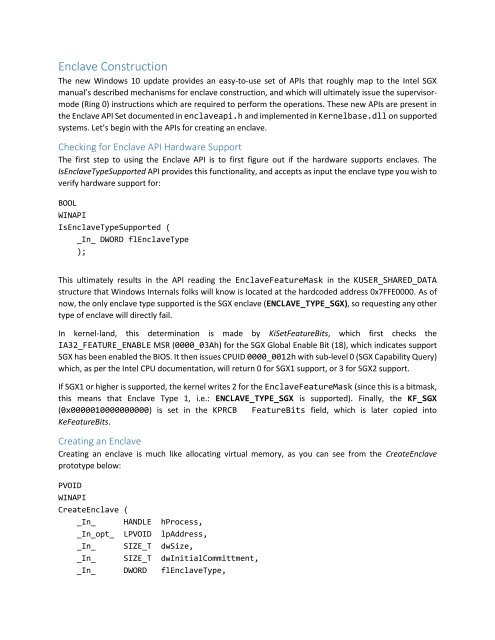
<strong>Enclave</strong> Construction<br />
The new W<strong>in</strong>dows <strong>10</strong> update provides an easy-to-use set of APIs that roughly map to the <strong>Intel</strong> <strong>SGX</strong><br />
manual’s described mechanisms for enclave construction, and which will ultimately issue the supervisormode<br />
(R<strong>in</strong>g 0) <strong>in</strong>structions which are required to perform the operations. These new APIs are present <strong>in</strong><br />
the <strong>Enclave</strong> API Set documented <strong>in</strong> enclaveapi.h and implemented <strong>in</strong> Kernelbase.dll on supported<br />
systems. Let’s beg<strong>in</strong> with the APIs for creat<strong>in</strong>g an enclave.<br />
Check<strong>in</strong>g for <strong>Enclave</strong> API Hardware <strong>Support</strong><br />
The first step to us<strong>in</strong>g the <strong>Enclave</strong> API is to first figure out if the hardware supports enclaves. The<br />
Is<strong>Enclave</strong>Type<strong>Support</strong>ed API provides this functionality, and accepts as <strong>in</strong>put the enclave type you wish to<br />
verify hardware support for:<br />
BOOL<br />
WINAPI<br />
Is<strong>Enclave</strong>Type<strong>Support</strong>ed (<br />
_In_ DWORD fl<strong>Enclave</strong>Type<br />
);<br />
This ultimately results <strong>in</strong> the API read<strong>in</strong>g the <strong>Enclave</strong>FeatureMask <strong>in</strong> the KUSER_SHARED_DATA<br />
structure that W<strong>in</strong>dows Internals folks will know is located at the hardcoded address 0x7FFE0000. As of<br />
now, the only enclave type supported is the <strong>SGX</strong> enclave (ENCLAVE_TYPE_<strong>SGX</strong>), so request<strong>in</strong>g any other<br />
type of enclave will directly fail.<br />
In kernel-land, this determ<strong>in</strong>ation is made by KiSetFeatureBits, which first checks the<br />
IA32_FEATURE_ENABLE MSR (0000_03Ah) for the <strong>SGX</strong> Global Enable Bit (18), which <strong>in</strong>dicates support<br />
<strong>SGX</strong> has been enabled the BIOS. It then issues CPUID 0000_0012h with sub-level 0 (<strong>SGX</strong> Capability Query)<br />
which, as per the <strong>Intel</strong> CPU documentation, will return 0 for <strong>SGX</strong>1 support, or 3 for <strong>SGX</strong>2 support.<br />
If <strong>SGX</strong>1 or higher is supported, the kernel writes 2 for the <strong>Enclave</strong>FeatureMask (s<strong>in</strong>ce this is a bitmask,<br />
this means that <strong>Enclave</strong> Type 1, i.e.: ENCLAVE_TYPE_<strong>SGX</strong> is supported). F<strong>in</strong>ally, the KF_<strong>SGX</strong><br />
(0x00000<strong>10</strong>000000000) is set <strong>in</strong> the KPRCB FeatureBits field, which is later copied <strong>in</strong>to<br />
KeFeatureBits.<br />
Creat<strong>in</strong>g an <strong>Enclave</strong><br />
Creat<strong>in</strong>g an enclave is much like allocat<strong>in</strong>g virtual memory, as you can see from the Create<strong>Enclave</strong><br />
prototype below:<br />
PVOID<br />
WINAPI<br />
Create<strong>Enclave</strong> (<br />
_In_ HANDLE hProcess,<br />
_In_opt_ LPVOID lpAddress,<br />
_In_ SIZE_T dwSize,<br />
_In_ SIZE_T dwInitialCommittment,<br />
_In_ DWORD fl<strong>Enclave</strong>Type,