Business Solutions Vol 5 Issue 1
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
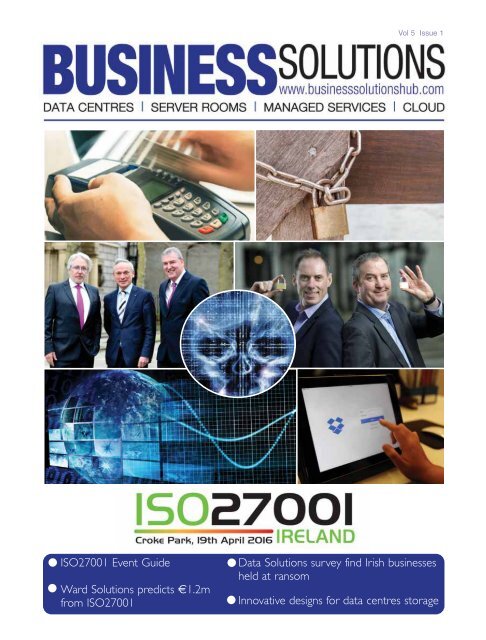
<strong>Vol</strong> 5 <strong>Issue</strong> 1<br />
ISO27001 Event Guide<br />
Ward <strong>Solutions</strong> predicts €1.2m<br />
from ISO27001<br />
Data <strong>Solutions</strong> survey find Irish businesses<br />
held at ransom<br />
Innovative designs for data centres storage
Driven By The Need For<br />
Information Security In Ireland<br />
Data is one of the most valuable<br />
assets any business has today. Our<br />
dependence on information systems<br />
and services means organisations<br />
are more vulnerable to security<br />
threats than ever before. Keeping<br />
your data secure – whether its<br />
customer, staff or supplier data – is<br />
critical in most businesses, but most<br />
especially those dealing with<br />
sensitive data. Data security is a hot<br />
topic in the media so ISO 27001 not<br />
only protects your business against<br />
hackers but also safeguards your<br />
reputation.<br />
For further information please contact<br />
BoxMedia<br />
616 Edenderry <strong>Business</strong> Campus,<br />
Edenderry,<br />
Co Offaly<br />
Tel: +353 (0) 46 977 3434<br />
Website : www.iso27001ireland.com<br />
ronan@boxmedia.ie<br />
susan@boxmedia.ie<br />
KEY BENEFITS TO YOUR BUSINESS<br />
• Improves and maintains competitive edge.<br />
• Win more business particularly where procurement<br />
specifications require higher IT security<br />
credentials.<br />
• Compliance with legal, statutory, regulatory and<br />
contractual requirements.<br />
• Provide assurance to stakeholders, such as clients<br />
and shareholders.<br />
• <strong>Business</strong> continuity is assured through<br />
management of risk, security issues and concerns.
C ONTENTS<br />
-5-<br />
Ward <strong>Solutions</strong><br />
Predicts €1.2M from ISO27001.<br />
-28-<br />
Electronic Payments<br />
Say goodbye to the cheque book<br />
x<br />
-7-<br />
Atlantic Bridge<br />
€140M fund for tech companies.<br />
-8-9-10-<br />
Deciphering<br />
The puzzling future of data security.<br />
PAGE 5<br />
Ward <strong>Solutions</strong>.<br />
-29-<br />
Data <strong>Solutions</strong><br />
New jobs and €5M investment<br />
PAGE 28<br />
Cheque books a thing of<br />
the past.<br />
PAGE 30<br />
CyberBunker.<br />
-12-<br />
Zinopy<br />
Launches “inSlght”.<br />
PAGE 7<br />
Atlantic Bridge.<br />
-31-<br />
Data Protection<br />
3 issues defining data protection<br />
in Ireland<br />
PAGE 31<br />
Data Protection.<br />
-13-19-<br />
ISO 27001<br />
Event Guide & Workshop.<br />
Managing Editor: Ronan McGlade<br />
Sub Editor: Mark Collins<br />
<strong>Business</strong> Development: Susan Doyle<br />
Production: Helen King<br />
Production/Operations: Paula Dempsey<br />
Sales & Marketing: Alan Carolan<br />
Sales & Marketing: Ciaran Hurley<br />
IT Department: Thomas McCarthy<br />
-23-<br />
AdaptiveMobile<br />
80% do not have adequate security<br />
measures in place.<br />
-25-<br />
VPN<br />
Do you need one.<br />
PAGE 8<br />
Deciphering.<br />
PAGE 12<br />
Zinopy.<br />
<strong>Business</strong> <strong>Solutions</strong> is published by BoxMedia and its Directors.<br />
616 Edenderry <strong>Business</strong> Campus, Edenderry, Co Offaly<br />
Tel: + 353 46 9773434<br />
Email: ronan@boxmedia.ie<br />
Website: www.businesssolutionshub.com<br />
BoxMedia and its Directors can accept no responsibility for the accuracy of contributors’ articles or statements<br />
appearing in this magazine. Any views or opinions expressed are not necessarily those of BoxMedia and its<br />
Directors. No responsibility for loss or distress occasioned to any person acting or refraining from acting as a<br />
result of the material in this publication can be accepted by the authors, contributors, editor and publisher. A<br />
reader should access separate advice when acting on specific editorial in this publication!<br />
BoxMedia is a Premier <strong>Business</strong> Media Ltd Company<br />
Design, Origination and Separations by Fullpoint Design (057) 8680873<br />
Printed by GPS Colour Graphics.<br />
VOL 5 ISSUE 1<br />
1
Half of Irish (47 per cent) find endless<br />
junk mail more annoying than their<br />
commute to work<br />
New research reveals one in three consumers in Ireland and the UK will even<br />
move their custom elsewhere if this trend of irrelevant overcommunication persists<br />
New research reveals the<br />
standard of communication -<br />
inundation of irrelevant<br />
whether paper-based or digital,<br />
communications and<br />
to ensure consumer loyalty.”<br />
junk mail is pushing<br />
A majority of consumers in<br />
consumer loyalty in the UK and<br />
Ireland to breaking point, with the<br />
majority (84 per cent) ready to take<br />
action against brands.<br />
The research, commissioned by<br />
global IT services company Ricoh and<br />
carried out by Coleman Parkes,<br />
examined the relationship between<br />
Ireland and the UK (65 per cent)<br />
believe more could be done to<br />
tailor communications to their<br />
individual circumstances. Three<br />
quarters (76 per cent) would<br />
even be willing to share personal<br />
data to make this happen,<br />
including occupation, salary,<br />
brand communications and<br />
Internet browsing habits and<br />
customer loyalty.<br />
Irrelevant communications, both<br />
online and paper-based, are a huge<br />
bug-bear for more than two-thirds of<br />
consumers in Ireland and the UK,<br />
health records.<br />
Consumers also increasingly<br />
view digital communications as<br />
their preferred method to receive<br />
information from brands and<br />
who consider a quarter of what they<br />
service providers: for new offers<br />
Chas Moloney, director, Ricoh Ireland & UK<br />
receive to be junk. Nearly half (47<br />
and upgrades (71 per cent),<br />
per cent) of consumers even see junk<br />
mail as more frustrating than their commute to work.<br />
Beyond the mere frustration factor, consumers are suffering<br />
from being unable to sift through the flood of irrelevant<br />
information and poor quality comms. Nearly one in five (17 per<br />
cent) have missed a payment deadline, and 22 per cent have<br />
been unsure how much they owe for a service or even missed<br />
offers they were entitled to (33 per cent).<br />
Brands need to beware that irrelevant communications are<br />
having a significantly detrimental impact on customer loyalty,<br />
trust and spend, and consumers are unafraid to bite back. Twothirds<br />
(69 per cent) of consumers in Ireland and the UK report<br />
feeling less loyal to a brand spamming with irrelevant<br />
information, whilst a similar number would also spend less (68<br />
per cent) and even go so far as to stop being a customer<br />
completely (57 per cent). Nearly a third (32 per cent) of<br />
consumers have moved their custom elsewhere, another fifth (22<br />
per cent) have complained to a service provider, and over one in<br />
ten (14 per cent) have taken their complaint to an authoritative<br />
body.<br />
Chas Moloney, director, Ricoh Ireland & UK, said: “Irish<br />
consumers are clearly saying ‘enough is enough’ when it comes<br />
to the irrelevance and high volume of communication sent out<br />
by brands and service providers. In the digital age, it has never<br />
been more convenient to instantly communicate with customers,<br />
but it is equally just as easy to spam.<br />
“Brands need to find that crucial middle ground -<br />
communicating regularly and effectively without alienating<br />
customers. In today’s competitive landscape, businesses must do<br />
more to listen to their customers and provide a tailored, quality<br />
statements and bills (66 per<br />
cent) and updates to terms and conditions (64 per cent).<br />
Moloney continued: “Consumers want to feel like a brand<br />
knows them and is creating the most tailored and bespoke<br />
communication to cater for their needs and interests. This should<br />
not be taken as an excuse to ‘spam’ though. Using consumer<br />
data correctly is imperative here. No matter whether they have a<br />
preference for digital communications – such as online bank<br />
statements – or a mix of electronic and paper-based, there is<br />
simply no excuse not to harness this insights to ensure<br />
communications are truly targeted, which in turn makes them<br />
effective and powerful.”<br />
The industries viewed as currently sending the most relevant<br />
communications to consumers are the public sector (39 per<br />
cent), financial services (37 per cent), utilities (45 per cent) and<br />
healthcare (32 per cent). With the exception of utilities, these<br />
industries were similarly seen to be the most trustworthy handlers<br />
of customer data. However, no single sector is viewed positively<br />
by more than half of consumers, which goes to show significant<br />
work still needs to be done by brands across all industries to<br />
bring confidence in their customer communications up to<br />
scratch.<br />
“<strong>Business</strong>es across Ireland have to streamline how they<br />
manage, distribute and collect data to ensure consistency across<br />
all channels. Information provided by customers should be used<br />
to create promotional offers and updates that are not only<br />
personal to the consumer, but also highly relevant to them. This<br />
results in the customer feeling truly valued, which ultimately<br />
drives loyalty and tangible benefits to the business,” concluded<br />
Moloney.<br />
2<br />
VOL 5 ISSUE 1
Data breach four-times worse than<br />
CEO quitting – BT study<br />
New research undertaken by Amárach for BT Ireland has shown that a company’s<br />
data protection is priority No 1, with a data breach considered four-times worse<br />
than a CEO quitting.<br />
The likelihood of a<br />
company suffering a data<br />
breach has increased tenfold<br />
in today’s age of heightened<br />
cyberattacks and an abundance<br />
of devices connected<br />
to the internet of things (IoT).<br />
In the last few days alone, three hospitals in the US have been<br />
the victims of ransomware attacks, with attackers demanding<br />
cash to allow the hospital’s IT staff to gain access once again to<br />
their servers.<br />
A recent poll conducted for BT Ireland has highlighted that<br />
data protection concerns are shared by both those at the coal<br />
face of a company’s security operation, and by those at the<br />
highest level of the company as well.<br />
Data protection more important than financial health<br />
The poll, of 115 senior Irish IT decision makers in companies with<br />
an average employee size of 300 staff, showed that fear of a data<br />
breach is now the biggest<br />
worry for a company, fourtimes<br />
bigger than the sudden<br />
departure of an influential<br />
CEO.<br />
Likewise, of those polled,<br />
67pc said they believe that a company’s statements to investors<br />
should specifically address data management capabilities in the<br />
future and, additionally, 62pc said they believe that future<br />
investors will use data management capabilities to assess a<br />
company’s financial health, just as they do with profits and assets<br />
currently.<br />
Shay Walsh, managing director of BT Ireland, said of the<br />
study’s findings: “Our research reveals that Ireland’s savvy IT<br />
leaders recognise and understand the need for their employers to<br />
invest in the right infrastructure now that will enable them to<br />
better manage and extract value from data and, ultimately,<br />
protect themselves from serious data management risk in the<br />
future.”<br />
Has your mouse been hacked?<br />
Wireless mice and keyboards are prime for hacking, with<br />
a “massive vulnerability” leaving “billions” of devices<br />
at risk, according to a new report.<br />
US cybersecurity company Bastille claims to have found<br />
the issue, calling it MouseJack, which sounds pretty cool,<br />
with the company saying the vulnerability is massive.<br />
Manufacturers like Logitech, Dell and Lenovo are<br />
namechecked as those affected by the issue, but most non-<br />
Bluetooth wireless dongles are vulnerable.<br />
Basically, hackers can take over a computer through a flaw<br />
in the dongles. Once paired, the MouseJack operator can<br />
insert keystrokes or malicious code with the full privileges of<br />
the PC owner and infiltrate networks to access sensitive data.<br />
The attack is at the keyboard level, therefore, PCs, Macs,<br />
and Linux machines using wireless dongles can all be<br />
victims.<br />
“MouseJack poses a huge threat, to individuals and<br />
enterprises, as virtually any employee using one of these<br />
devices can be compromised by a hacker and used as a<br />
portal to gain access into an organisation’s network,” said<br />
Chris Rouland, founder and CTO of Bastille.<br />
MouseJack, an IoT nightmare<br />
Take a step back from the millions of laptops around the<br />
world, and think of where we’re all going. An IoT world means<br />
tonnes more interconnected devices, tonnes more wireless<br />
interconnected devices. So, if what Bastille found is as bad as it<br />
says, we could be in a bit of bother.<br />
“The MouseJack discovery validates our thesis that wireless<br />
IoT technology is already being rolled out in enterprises that<br />
don’t realise they are using these protocols,” said Rouland.<br />
“As protocols are being developed so quickly, they have not<br />
been through sufficient security vetting.”<br />
Bastille says the top 10 wearables on the market have<br />
already been hacked, an ominous sign for those operating<br />
below that threshold.<br />
What’s worrying is the large amount of wireless mice and<br />
keyboards that can’t be updated, thus rendering any hope of a<br />
patch useless.<br />
“Consumers will need to check with their vendor to<br />
determine if a fix is available or consider replacing their<br />
existing mouse with a secure one,” said the company, with<br />
www.mousejack.com set up to help with this.<br />
VOL 5 ISSUE 1<br />
3
Data <strong>Solutions</strong> Survey finds 20% of<br />
Irish businesses have been held to<br />
ransom<br />
• Despite this 93% say they would never pay a ransom<br />
• 80% of businesses upgraded IT security in past year due to<br />
rise in cyberattacks<br />
• 55% expect to spend more on cyber security in 2016 than<br />
last year<br />
• More than 40% consider brand and reputation damage the<br />
biggest concern of an attack<br />
• Less than 10% are ‘absolutely confident’ their information<br />
security measures are effective<br />
• Full survey results to be announced at Data <strong>Solutions</strong>’<br />
Secure Computing Forum on 12th May.<br />
Data <strong>Solutions</strong>, the leading Irish distributor for IT<br />
solutions, has revealed the results of its 2016<br />
Information Security Survey. The survey found that<br />
20% of Irish businesses have fallen victim to<br />
ransomware attacks, a serious form of cybercrime that sees<br />
hackers hold a business’ sensitive and critical data for ransom.<br />
Despite the serious nature of such an attack, 93% of respondents<br />
stated that they would never pay a ransom to hackers.<br />
The survey was carried out in association with TechPro<br />
magazine among 137 senior IT decision makers in Irish businesses<br />
during February and March 2016. The full results of the research<br />
will be revealed at the Data <strong>Solutions</strong> Secure Computing Forum<br />
taking place in the Mansion House, Dawson Street, Dublin 2 on<br />
12th May.<br />
In a clear sign of the changing landscape of information<br />
security, and increased awareness of the threat of cybercrime, the<br />
survey also found that 80% of businesses upgraded their IT<br />
security in the past year, and that more than 55% of companies<br />
Pictured at the announcement of the 2016 Data <strong>Solutions</strong> survey results are: (l-r) Michael O'Hara,<br />
managing director, Data <strong>Solutions</strong>, and David Keating, security sales manager, Data <strong>Solutions</strong>.<br />
expect to spend more on security measures in 2016 than they<br />
did in the previous year.<br />
Despite this growing awareness, less than 10% of respondents<br />
stated that they were ‘absolutely confident’ that their information<br />
security measures are effective. More than 40% said that they<br />
considered brand and reputational damage to be the main risks<br />
of a data breach with just 0.8% saying they would consider job<br />
loss their primary concern. Brand protection from cybercrime will<br />
be an important discussion point at this year’s Secure Computing<br />
Forum.<br />
Other notable stats highlight that businesses are concerned<br />
about the risk of data loss or disclosure as a direct result of<br />
cybercrime, with 55% stating that this was their main concern.<br />
Other causes of concern were DDoS attacks – which recently<br />
plagued Irish government and public sector websites and the<br />
national lottery – social engineering and data destruction.<br />
Although almost half of respondents stated that they were<br />
concerned about attacks through the supply chain, nearly a<br />
quarter (23%) do not build specific requirements for information<br />
security into the contracts of third party suppliers. This is a 12%<br />
increase from last year’s research, and highlights that businesses<br />
are at even higher risk of a breach in the supply chain, the cause<br />
of many high profile breaches such as the attack on retail giant<br />
Target.<br />
Micheal O’Hara, group managing director, Data <strong>Solutions</strong>,<br />
said: “The results of this survey present an interesting and<br />
worrying picture of the current state of the Irish information<br />
security landscape and the approaches being taken by companies<br />
to protect themselves. The Secure Computing Forum will focus<br />
on where Irish businesses are falling short and what they need to<br />
do to ensure their infrastructure is safe.<br />
“The fact that 80% of businesses are upgrading and changing<br />
their security infrastructure is reassuring,<br />
but it begs the question what are the other<br />
20% doing? Cybercriminals are forever<br />
changing their approach and businesses<br />
need to constantly adapt to keep up.<br />
“93% say that they would never pay a<br />
ransom, but faced with the reality of an<br />
actual ransomware attack I think you’d find<br />
most would. Every business has sensitive or<br />
mission critical data and ultimately it would<br />
come down to a business decision if that<br />
was under threat. Less than 10% have<br />
complete confidence in their information<br />
security measures and this highlights the<br />
pressing need for companies to take the<br />
threat of these and other forms of<br />
cyberattacks more seriously.”<br />
Tickets for Ireland’s largest annual IT<br />
security event the Data <strong>Solutions</strong> Secure<br />
Computing Forum are available at<br />
http://securecomputingforum.ie/. The<br />
event takes place in the Round Room at the<br />
Mansion House, Dawson Street, Dublin 2 on<br />
12th May.<br />
4<br />
VOL 5 ISSUE 1
Ward <strong>Solutions</strong> predicts €1.2M<br />
revenue from new ISO 27001<br />
• Ward is first and only provider in Ireland recognised as an ISO 27001 Associate<br />
Consultant Partner by the British Standards Institution<br />
• Ward invested €50,000 in training staff for certification<br />
Pat Larkin, CEO, Ward <strong>Solutions</strong>.<br />
Ward <strong>Solutions</strong>, Ireland’s leading information security<br />
provider, today announces the launch of its new<br />
ISO 27001 consultancy service. It is forecasting<br />
that this service will lead to new revenues of<br />
€1.2M from its security consultancy business within the next<br />
year.<br />
The launch of the new service follows Ward’s investment of<br />
€50,000 in ISO 27001 certification training for staff. More than<br />
ten of Ward’s employees are now ISO 27001 accredited, and<br />
the provider has now been recognised as an Associate<br />
Consultant Partner by the British Standards Institution (BSI), the<br />
organisation that oversees the certification process.<br />
This partnership distinguishes Ward as the first and only<br />
information security provider in the Republic of Ireland certified<br />
to offer ISO 27001 consultation services to organisations hoping<br />
to receive the accreditation. Ward <strong>Solutions</strong> will be identified to<br />
new customers by the BSI as a specialist that can help with the<br />
certification procedure.<br />
Ward <strong>Solutions</strong> will offer two forms of consultation. The first<br />
will be for organisations testing if they are ready to be assessed<br />
by the BSI, and will consist of a review by Ward to establish this.<br />
The second will be offered to companies in the early stages of<br />
preparation towards becoming ISO 27001 compliant. Ward<br />
<strong>Solutions</strong> will offer these companies comprehensive step-by-step<br />
consultancy through the complex accreditation process.<br />
Pat Larkin, CEO, Ward <strong>Solutions</strong>, said: “Irish enterprises and<br />
government bodies are increasingly making ISO 27001<br />
accreditation a mandatory requirement to work with them as<br />
part of their supply chain assurance. As the only company in<br />
Ireland to be recognised as an Associate Consultant Partner by<br />
the BSI, Ward <strong>Solutions</strong> can provide clients with unique<br />
guidance towards accreditation, something that will provide us<br />
with a strong competitive advantage in Ireland.<br />
”This new service will also allow us to grow our security<br />
consultancy business significantly over the next year as we<br />
forecast new revenues of €1.2M from this service alone. Our<br />
pipeline is very strong as a large number of new and existing<br />
customers are looking to become accredited this year.”<br />
John Whyte of the British Standards Institution said, “Prior to<br />
last year we didn’t have any ISO 27001 Associate Consultant<br />
Partners in the Republic of Ireland and we’re delighted to offer<br />
this to Ward <strong>Solutions</strong>. This accreditation highlights Ward’s indepth<br />
and unique expertise in the Irish market to provide<br />
consulting services to companies seeking to become ISO 27001<br />
compliant.”<br />
“ISO 27001 is the international benchmark for information<br />
security management systems. It offers a way for companies to<br />
set themselves apart from their competition by exceeding the<br />
industry standard. Ward’s new consulting service will remove<br />
the complexity associated with achieving this standard and will<br />
enable more Irish organisations to become ISO 27001<br />
compliant.”<br />
About Ward <strong>Solutions</strong><br />
Ward <strong>Solutions</strong> is Ireland and Northern Ireland’s largest<br />
information security provider with offices in Dublin, Belfast<br />
and Ennis. It provides a comprehensive range of security<br />
services including security auditing, consulting, incident<br />
response, secure managed services and software<br />
development services. It has the largest team of<br />
information security specialists in Ireland providing a<br />
highly responsive service to more than 300 leading private<br />
and public sector organisations. www.ward.ie<br />
About BSI<br />
BSI (British Standards Institution) is the business standards<br />
company that equips businesses with the necessary<br />
solutions to turn standards of best practice into habits of<br />
excellence. Formed in 1901, BSI was the world’s first<br />
National Standards Body and a founding member of the<br />
International Organization for Standardization (ISO). Over<br />
a century later it continues to facilitate business<br />
improvement across the globe by helping its clients drive<br />
performance, manage risk and grow sustainably through<br />
the adoption of international management systems<br />
standards, many of which BSI originated. Renowned for its<br />
marks of excellence including the consumer recognized<br />
BSI Kitemark, BSI’s influence spans multiple domains<br />
including Aerospace, Automotive, Built Environment,<br />
Food, Healthcare and IT. With 80,000 clients in 182<br />
countries, BSI is an organization whose standards inspire<br />
excellence across the globe. To learn more, please visit<br />
www.bsigroup.com<br />
VOL 5 ISSUE 1<br />
5
MHC Tech Law: What will the<br />
General Data Protection Regulation<br />
mean for business?<br />
Mason Hayes & Curran introduces the General Data Protection Regulation, which<br />
was agreed upon at the end of last year, and looks at what it will mean for businesses.<br />
In December 2015, three years after the first draft was proposed,<br />
and almost 20 years since the Data Protection Directive was<br />
adopted, EU lawmakers came to agreement on the reform of data<br />
protection law. The new General Data Protection Regulation<br />
(GDPR) was agreed upon and is currently in the process of<br />
formalisation and translation.<br />
The General Data Protection Regulation is expected to come into<br />
force in 2018. Let’s take a look at this piece of legislation and some<br />
of the implications for businesses.<br />
What is the General Data Protection Regulation?<br />
The GDPR will replace the current Data<br />
Protection Directive.<br />
As a Regulation, and unlike the preceding<br />
Directive, it applies directly. This means that<br />
the GDPR does not need to be implemented<br />
through each member state’s national law.<br />
This should reduce the level of national<br />
variation in relation to data protection law,<br />
though it will not eliminate it entirely, as<br />
member states retain some discretion in<br />
certain areas<br />
The GDPR will comprehensively regulate<br />
data protection throughout the EU (with the<br />
exception of data processed for law<br />
enforcement purposes). The GDPR builds<br />
upon familiar concepts and rules in the Data<br />
Protection Directive, but in many ways it goes further. It has wider<br />
scope, standards have been raised, and sanctions are much higher.<br />
What does it mean for businesses?<br />
With a greater level of harmonisation of laws across the EU, it should<br />
be easier for businesses that sell goods or services across the EU to<br />
take a unified approach in multiple EU states. However, the<br />
compliance burden is generally greater than that currently in place,<br />
so many organisations will have to review and enhance their existing<br />
practices.<br />
In particular, the introduction of the ‘accountability’ principle<br />
means that affected organisations will have to work on their internal<br />
compliance, including record keeping and, for some, the<br />
appointment of a data protection officer.<br />
<strong>Business</strong>es have some time before the GDPR comes into effect.<br />
However, getting to grips with a new compliance framework takes<br />
time and, when developing any new products or projects, an eye<br />
should be kept to the future.<br />
Why is it important?<br />
The GDPR represents the future of the regulation of data protection<br />
in the EU. It is particularly important for two reasons. First, the GDPR<br />
has a very wide scope and will capture both data and companies<br />
that previously fell outside the realm of EU data protection<br />
Under the GDPR, a failure to adequately protect<br />
data could lead to large fines.<br />
regulation. Second, the potential fines under the GDPR are<br />
extremely high.<br />
The GDPR provides for a two-tier system of fines, depending on<br />
the type of non-compliance. For the lower tier of offences, a fine up<br />
to the higher of €10m or 2pc of the organisation’s total worldwide<br />
annual turnover in the previous year may be imposed. The lower tier<br />
of offences includes breach of privacy by design obligations, the<br />
rules relating to processor contracts, record-keeping obligations and<br />
processing security requirements.<br />
For the upper tier of offences, there is potential for fines up to the<br />
greater of €20m or 4pc of the organisation’s total worldwide annual<br />
turnover in the previous year. Offences that<br />
attract the higher level of sanction include<br />
breaches of the basic principles for<br />
processing, including conditions for consent,<br />
infringing data subjects’ rights and unlawful<br />
transfers to countries outside the European<br />
Economic Area.<br />
For group companies, the percentage fine<br />
seems to attach to the turnover of the group,<br />
not just the individual company in question.<br />
For large multinationals, this is a particularly<br />
significant deterrent.<br />
There are a number of factors that the data<br />
protection authority must consider when<br />
deciding the amount of the fine to be<br />
imposed, including:<br />
• The nature, seriousness and duration of the infringement<br />
• Whether the infringement was intentional or negligent<br />
• Actions taken to mitigate the damage suffered by data subjects<br />
• Relevant previous infringements<br />
• Whether the wrongdoer co-operated with the data protection<br />
authority<br />
• The categories of personal data affected.<br />
What next?<br />
As the finalisation and translation of the GDPR is currently in<br />
progress, we can expect the GDPR to be formally adopted in the<br />
coming months.<br />
The Article 29 Working Party (the group of EU data protection<br />
regulators) has released a statement indicating that its priorities will<br />
be:<br />
Setting up the new European Data Protection Board. The Board<br />
will replace the Article 29 Working Party and have an enhanced role<br />
under the GDPR<br />
Preparing the one-stop shop and consistency mechanism.<br />
Issuing guidance, in particular on data portability, the notion of<br />
‘high risk’ and data protection impact assessments, data protection<br />
officers and certification.<br />
Communication relating to the new European Data Protection<br />
Board and the GDPR.<br />
6<br />
VOL 5 ISSUE 1
Atlantic Bridge Capital confirms a<br />
new €140m fund for tech<br />
companies<br />
Atlantic Bridge Capital has confirmed the<br />
first close of Atlantic Bridge III, a €140m<br />
fund for technology companies with the<br />
potential to scale globally in the areas of<br />
big data, internet of things (IoT), robotics and cloud<br />
computing.<br />
The Dublin-based fund will invest in up to 20<br />
European companies.<br />
Investments are already closing in seven<br />
companies.<br />
The fund will focus on scaling Irish and European<br />
companies in high-growth enterprise technology<br />
sectors such as cloud, big data, augmented and<br />
virtual reality software, robotics and IoT.<br />
“We already have a number of pipeline<br />
investments identified for the fund and are<br />
confident that this will build on the track record of<br />
success of our previous Funds,” explained Brian<br />
Long, managing partner of Atlantic Bridge.<br />
“As a growth equity stage fund, Atlantic Bridge III<br />
will focus on taking companies with a solid and<br />
exciting business model to the next level, scaling<br />
them into key international markets like the US and<br />
China.”<br />
The project is supported by the Department of<br />
Jobs through Enterprise Ireland.<br />
Participants in the new fund include existing Atlantic Bridge<br />
investors, the Ireland Strategic Investment Fund, Enterprise<br />
Ireland and the European Investment Fund, along with new<br />
institutional investors, including British <strong>Business</strong> Bank Investments<br />
Limited, the commercial arm of the British <strong>Business</strong> Bank, and a<br />
number of institutional pension funds.<br />
Dublin's Atlantic Bridge has closed a major fund worth €140m which it will use<br />
to invest in companies in cloud, big data, robotics and internet of things.<br />
Brian Long, managing partner, Atlantic Bridge Capital, with Minister for Jobs, Enterprise and<br />
Innovation Richard Bruton ,TD, and Kevin Sherry, executive director at Enterprise Ireland. Photo:<br />
Maxwell Photography.<br />
AIB is also a new investor in the Atlantic Bridge<br />
III fund.<br />
In February, we reported that the organisation was close to<br />
closing a major fund.<br />
Atlantic Bridge Capital is a global technology fund with more<br />
than €400m of assets under management across four funds,<br />
investing in technology companies in Europe. Headquartered in<br />
Dublin, it has offices and staff based in London, Silicon Valley,<br />
Beijing and Hong Kong.<br />
Using its international platform and “Bridge model”, the<br />
venture capital firm has scaled a range of European companies<br />
into the US and Chinese markets<br />
Examples of scaled Atlantic Bridge portfolio companies<br />
include Movidius, FieldAware, PolarLake, Metaio, Swrve and<br />
Glonav.<br />
Atlantic Bridge currently has more than 20 companies in its<br />
funds’ portfolio and has achieved 12 realisations with proceeds<br />
totaling over €1.7bn.<br />
“The Atlantic Bridge model of connecting Irish technology<br />
companies with key global markets makes it a key component<br />
of the funding landscape and we are excited to continue our<br />
partnership with Atlantic Bridge for Fund III, following the<br />
strong performance achieved by Fund II,” said Eugene<br />
O’Callaghan, director of the Ireland Strategic Investment Fund.<br />
“This investment aligns with our dual objectives of generating<br />
economic impact and financial returns and we look forward to<br />
seeing it support rapidly growing Irish companies in accessing<br />
customers, investors and partners in global markets in the US,<br />
China and Europe.”<br />
VOL 5 ISSUE 1<br />
7
Deciphering the puzzling<br />
future of data security<br />
From hackers to unencrypted smartphones and the<br />
spectre of full-scale cyber warfare, the future of data<br />
security is set to be a complex one that will affect us all.<br />
What is the future of data security?<br />
The question is both naïve and unfathomable. Asking the<br />
question in the first place means being ignorant of the reality<br />
that the battle between victims and those who threaten us is a<br />
neverending one. There will never be a full stop.<br />
The World Economic Forum named cyberattacks one of the<br />
greatest threats to businesses and ranked it as a risk higher<br />
than terrorist attacks, explained Theresa Payton, who was CIO<br />
for the White House during the Bush administration from 2006<br />
to 2008 and is now one of America’s leading cybersecurity<br />
experts and CEO of Fortalice <strong>Solutions</strong>. “The world’s leaders<br />
know that attacks on private sector companies will damage a<br />
country’s economic wellbeing,” she said.<br />
In February 2016, US president Barack Obama gained<br />
Capitol Hill support for a budget increase of $5bn in additional<br />
cybersecurity spending. This brings the cybersecurity budget<br />
to $19bn in 2017 for the US government. “President Obama<br />
said that data breaches and cybercrime are, ‘among the most<br />
urgent dangers to America’s economic and national security’,”<br />
explained Payton.<br />
Backdoors are bad ideas. Weakening<br />
encryption is an old-school argument<br />
and I’m not sure that’s even what the<br />
FBI wants’<br />
Theresa Payton, Former White House<br />
CIO.<br />
“Up until recently, most data<br />
Theresa Payton, former<br />
breaches did not result in a long-term<br />
White House CIO and CEO<br />
financial impact on the victim. Once<br />
of Fortalice <strong>Solutions</strong><br />
the victim cleaned up the breach and<br />
accounted for expenses, usually stock prices or market<br />
reputation returned to previous levels. The status quo will<br />
change and the financial impact going forward is very real and<br />
morphing with today’s threats,” she warned.<br />
Payton cited IBM’s latest study, which revealed the average<br />
cost of a breach rose to $3.8m in 2015. A recent study by<br />
SkyHigh Networks asked companies if they would pay cybercriminals<br />
in the event of a ransomware attack and almost 25pc<br />
said yes, and 14pc of those said they would pay more than<br />
$1m to get their data back.<br />
Under constant threat<br />
Terry Greer-King, the director of cybersecurity at Cisco UK and<br />
Ireland, revealed that there are 3bn Google searches daily and<br />
19.7bn threats detected in the wild every day. The tech sector<br />
is trying to pare down the current industry benchmark for<br />
threat detection but, at the moment, the bad guys have an<br />
average of 100 days to do their worst before a threat is<br />
discovered. Considering that the world in 2030 may have<br />
500bn connected devices through the evolution of the internet<br />
of things (IoT), the threats are only going to skyrocket.<br />
“We are now in the realm of shadow IT where the internet<br />
and devices from fridges to phones and thermostats are all<br />
connected to clouds of clouds, and organisations don’t know<br />
what apps employees are downloading, and businesses are<br />
buying services without talking to IT,” said Greer-King. “The<br />
truth is IT can’t control any bit of technology anymore.”<br />
Paraphrasing Cisco chairman John Chambers, Greer-King<br />
added: “There are only two organisations in the world today:<br />
those that have been hacked and those that don’t know<br />
they’ve been hacked.”<br />
‘There are only two organisations in<br />
the world today: those that have been<br />
hacked and those that don’t know<br />
they’ve been hacked’<br />
– TERRY GREER-KING, CISCO<br />
According to Cisco’s Annual Security<br />
Report for 2016, cyberattacks continue Terry Greer-King, Cisco’s<br />
to be a profitable business for cybercriminals,<br />
who are refining the way security.<br />
European expert on IT<br />
they attack back-end infrastructure.<br />
Last year, Cisco, with the help of Level 3 Threat Research and<br />
Limestone Networks, identified the largest Angler exploit kit<br />
operation in the US, which targeted 90,000 victims every day<br />
and generated tens of millions of dollars a year by demanding<br />
ransoms off victims. Cisco estimates that, currently, 9,515<br />
users in the US are paying ransoms every month, amounting to<br />
an annual revenue of $34m for certain cybercrime gangs.<br />
The public face of a breach<br />
Greer-King explained that 60pc of the “bad stuff” occurs<br />
within the first few hours of an attack happening, when the<br />
cyber-thieves gain access to a company system and accounts<br />
get stolen or compromised. But remember, the industry<br />
average for detecting a breach is 100 days, long after this<br />
damage has been done.<br />
At the rate at which attacks are accelerating, it is going to<br />
be a case of when, and not if, an organisation’s capacity for<br />
crisis management will be tested. How an organisation reacts<br />
in the first 48 hours of detecting an attack or breach will be<br />
revealing, not only for customers, but employees and<br />
shareholders alike.<br />
“It is like that old military analogy: even the best-laid plans<br />
fall apart after the first five minutes of contact. Cool heads are<br />
important and, unless people are tested and attacks are<br />
simulated, you will never know what is going to happen in the<br />
heat of the moment,” said Kris McConkey, PwC’s partner-incharge<br />
of cybersecurity.<br />
8<br />
VOL 5 ISSUE 1
It is like that old military analogy, even<br />
the best-laid plans fall apart after the<br />
first five minutes of contact’<br />
– KRIS MCCONKEY, PWC<br />
Evidently, the march of technology is<br />
creating chaos for CIOs and CSOs to<br />
keep on top of, but the narrative is Kris McConkey, partner-incharge<br />
of cybersecurity,<br />
changing. CEOs and boards are now the<br />
fall guys rather than IT professionals. PwC<br />
McConkey posited that cyberattacks are<br />
now a boardroom issue, citing the high-profile attack on Talk<br />
Talk’s servers last year.<br />
“In the UK, breaches like [the Talk Talk breach] have seen the<br />
CEOs of companies suddenly propelled onto [current affairs<br />
show] Newsnight and radio shows,” said McConkey. “This was a<br />
seminal moment because it made boards realise that breaches are<br />
no longer something that can be offloaded to the chief security<br />
officer, but it is actually the boards themselves that are on the<br />
spot when things can go wrong.”<br />
You are the weakest link<br />
Ultimately, the triggers for the biggest attacks and vulnerabilities<br />
are people. No matter what elaborate security defences are put in<br />
place, Accenture’s Bill Phelps explained that it is people – AKA the<br />
‘wet firewall’ – who let the intruders in.<br />
“There were con artists long before technology was ever on the<br />
scene,” said the managing director and global lead for Accenture<br />
Security, who tracks a natural evolution from this to the infamous<br />
emails from Nigerian royalty and, today on social media, where<br />
users try to persuade others to transfer money. “Today, we are<br />
seeing mid-level executives being conned into allowing the bad<br />
people in using phishing attacks.”<br />
‘100pc defence is impossible, but it is<br />
good to constantly test yourself against<br />
mock adversaries’<br />
– BILL PHELPS, ACCENTURE<br />
Even senior US government officials<br />
who ought to have been at the pinnacle<br />
Bill Phelps, managing of awareness and protection – such as<br />
director and global lead for the head of the CIA, John Brennan –<br />
Accenture Security. were compromised and embarrassed<br />
by amateur hackers. Individuals, as well<br />
as businesses, need to be street smart, but also realise they<br />
can’t protect everything.<br />
“The battle space is so vast and takes in every person and<br />
organisation,” said Phelps.“There are criminal gangs out to<br />
steal your information or credit card numbers. Organisations<br />
are staving off industrial espionage and front-running trading.<br />
There are attacks on banks just to understand M&A activity,<br />
and all of this is very specialised.”<br />
And yet, all of the sophisticated defences in the world can<br />
still be undermined by a human weakness, like falling prey to a<br />
spear-phishing attack.<br />
“It is an asymmetrical problem in which the defender has to<br />
close every loophole, but the attacker has to only find one way<br />
in. 100pc defence is impossible, but it is good to constantly<br />
test yourself against mock adversaries.”<br />
The devil is in the data<br />
Mark Hughes, president of BT Security, said he believes<br />
organisations need to prioritise what it is they are trying to<br />
defend rather than locking down everything. He warned that<br />
the era of security beyond the firewall will require granular<br />
controls and privileges that define who can do what with the<br />
data and where they can go with it.<br />
“We are at a juncture where there is only a nuanced<br />
understanding of the differences between sophisticated and<br />
unsophisticated attacks,” he said. “Organisations are often so<br />
busy trying to protect against mainstream, everyday malicious<br />
activity that they are unprepared for the more sophisticated<br />
targeted attacks.”<br />
‘Organisations are often so busy trying<br />
to protect against mainstream,<br />
everyday malicious activity that they<br />
are unprepared for the more<br />
sophisticated targeted attacks’<br />
– MARK HUGHES, BT SECURITY<br />
The head of enterprise at Dropbox, Mark Hughes, president, BT<br />
Ross Piper, is responsible for driving the Security.<br />
US company’s growth in the enterprise<br />
market, building on its presence in 97pc of Fortune 500<br />
companies. Like Hughes, he believes the perimeter is no longer<br />
the defensible part of the network. It’s all about the data.<br />
Cloud services like Dropbox allow everyone from small teams<br />
of creators right up to thousands of individuals in a corporation<br />
to collaborate and share data on any device. In the past, this<br />
would have given a CEO or CIO a heart attack, but the<br />
productivity benefits and the inherent security to protect data<br />
in the cloud have evolved in ways that could frustrate attackers.<br />
‘This is a precursor to a fundamental<br />
shift in security models that we’ve been<br />
talking about for decades but which is<br />
finally coming to fruition’<br />
– ROSS PIPER, DROPBOX<br />
“If you take a 400MB video as an<br />
example. What we do when a user Ross Piper, head of<br />
saves that into Dropbox is we actually enterprise at Dropbox.<br />
break that into a hundred 4MB file<br />
blocks. Each of those file blocks is individually encrypted. They<br />
are stored at random within the storage service with 1bn new<br />
files per day. Imagine 1bn files – that’s well more than 10bn<br />
file blocks,” Piper explained.<br />
To illicitly access a specific file on this service, a hacker<br />
would have to get through the encryption tunnels, find the<br />
right 100 4MB blocks amongst tens of millions of file blocks<br />
saved that day, and individually unencrypt each one of them.<br />
This intelligent breaking up and sequencing of blocks of data<br />
represents the future of security in the cloud.<br />
“This is a precursor to a fundamental shift in security models<br />
that we’ve been talking about for decades but which is finally<br />
coming to fruition,” said Piper.<br />
Protection vs privacy<br />
It’s not just the growth of data that concerns security<br />
professionals and consumers, but the growth of datacollecting<br />
devices. “More devices will simply mean more ways<br />
to attack. Nothing is going to be safe,” said Cisco’s Greer-<br />
King. “There will be sensors everywhere to collect data,<br />
connect cities and ultimately change the way the world<br />
operates. But not every data point, not every sensor, will have<br />
a firewall.”<br />
With the advent of IoT and machine-to-machine (M2M)<br />
technology, threats against seemingly harmless consumer and<br />
industrial devices are already accelerating. According to PwC,<br />
the number of attacks on embedded IoT devices among<br />
companies it surveyed increased 152pc in 2015, yet only 36pc<br />
of these companies had a security strategy for IoT.<br />
VOL 5 ISSUE 1<br />
9
‘We have smart TVs that we didn’t<br />
realise had microphones built in. They<br />
are invisible to us and we don’t know<br />
who captures this data and what it is<br />
being used for’<br />
– DR DIRK PESCH, NIMBUS CENTRE<br />
Dirk Pesch, head of the Dr Dirk Pesch heads up the Nimbus<br />
Nimbus Centre, CIT. Centre at Cork Institute of Technology,<br />
where more than 80 researchers are<br />
working on the future of the internet of things. He believes the<br />
Stuxnet attack on industrial SCADA control systems in nuclear<br />
plants foreshadowed the world that is to come, but instead of<br />
factories and utilities being attacked, it will be the systems we<br />
invite into our homes.<br />
Pesch offered the example of remote meter readings, where an<br />
M2M device with a SIM sends your data to the electricity or<br />
water company. “If hackers know what they are doing and can<br />
breach the system, it won’t take long for an attacker to know if<br />
your house is occupied or not,” he said.<br />
“We have smart TVs that we didn’t realise had microphones<br />
built in. They are invisible to us and we don’t know who captures<br />
this data and what it is being used for. There are huge issues of<br />
privacy ahead.”<br />
How the information stored on the multitude of personal<br />
devices set to occupy our homes in the future will be treated<br />
could well be defined by the outcome of the present legal<br />
wrangle between Apple, the FBI and the US Department of<br />
Justice. The San Bernardino iPhone case could be the defining<br />
issue of our age, technologically and personally, but former<br />
White House CIO Payton said the issue may not be resolved to<br />
the satisfaction of Silicon Valley.<br />
“This is historic. The decision that comes out of this ultimately<br />
decides how we fight terrorism in this country,” she said.<br />
Payton said she thinks it is important to note that other<br />
industries compelled by a court order to produce records have<br />
implemented methods of compliance. “The banks had to create<br />
processes and systems to respond to anti-money laundering<br />
requests and more. The phone companies have had to create<br />
ways to respond,” she explained.<br />
While Apple CEO Tim Cook described the opening of<br />
backdoors into encrypted devices as the “software equivalent of<br />
cancer”, offering no guarantee that the keys will remain in the<br />
hands of the so-called good guys, Payton had a different view of<br />
this analogy.<br />
“Backdoors are bad ideas. Weakening encryption is an oldschool<br />
argument and I’m not sure that’s even what the FBI<br />
wants,” she said. “The FBI is not asking Apple to unlock the<br />
phone or to create a master key to use to unlock all phones.<br />
What the FBI is asking for is for Apple to remove a barrier, to<br />
remove one step, so the FBI themselves can attempt to unlock<br />
the phone.”<br />
Non-stop security<br />
It’s no surprise that a smartphone has<br />
taken a central role in defining<br />
information security, as millions of<br />
people are now living their lives<br />
through these devices. With the<br />
evolution of mobile wallets, fingerprint<br />
biometric security – once seen as sci-fi –<br />
Tim Cook, CEO of Apple.<br />
is now a reality, and companies from<br />
Amazon to MasterCard are<br />
experimenting with even more new ways to authenticate<br />
payments.<br />
“Payment technologies have never been safer, but criminals<br />
have never been smarter,” said Bob Reany, executive president<br />
of Identity <strong>Solutions</strong> at MasterCard. “Most of us can agree that<br />
passwords are a real problem. “People forget them often and<br />
it’s a pain to go through the retrieval process.”<br />
Conceding that there is no silver bullet to fight fraud, Reany<br />
said MasterCard implements multiple layers of protection to<br />
protect users every time they pay. Following a trial in the<br />
Netherlands, the credit card brand is rolling out a selfie security<br />
system in 14 territories this summer, in an effort to move away<br />
from the prevalence of passwords.<br />
“I wish passwords were passé!” said Payton, though she’s not<br />
yet satisfied with the proposed alternatives. “I am quite wary of<br />
biometric data until the vendor devices, the storage, and<br />
collection of biometrics are locked down and safe.”<br />
And even if biometrics technology is a step in the right<br />
direction, it is likely cyber-criminals are already working on a<br />
way to circumvent it. “The moment we roll out selfie and big<br />
data, behavioural-based analytics for authentication, it’s time to<br />
go back to the drawing board to invent the next approach,”<br />
concluded Payton.<br />
What<br />
makes<br />
Ireland<br />
the<br />
ultimate<br />
data<br />
centre<br />
capital of<br />
Europe?<br />
We regularly hear that Ireland has<br />
established itself as the ‘data capital<br />
of Europe’, with many of the world’s largest<br />
tech companies basing data centres here,<br />
but what exactly do we know about them?<br />
Ronan Harris, head of Google Ireland,<br />
recently described the country as the data<br />
capital of Europe and, going by industry<br />
reports, it’s hard to disagree.<br />
Specifically, a detailed report published<br />
by global data analyst group 451 Advisors<br />
in 2013 predicted that Ireland’s data centre<br />
industry would overtake the UK and<br />
mainland Europe locations, with a growth<br />
rate of 18pc over the coming years.<br />
What makes a good data centre?<br />
One of the key reasons Ireland is seen as a<br />
good location in which to establish vast<br />
warehouses full of servers is down to the<br />
cold weather that many of us complain<br />
about on a regular basis. Additionally, you’ll<br />
find most Irish data centres clustered along<br />
the M50 motorway, which mirrors the<br />
route of the T50 fibre trunking system<br />
running from north to west Dublin.<br />
While cooling and connectivity are<br />
essential for operations, there are other<br />
technical standards that comprise Irish,<br />
and, indeed, any, data centres.<br />
For example, square footage and energy<br />
usage contributes to what standard a data<br />
centre finds itself in. One such standard<br />
scrutinised by potential clients is power<br />
usage effectiveness (PUE), which divides<br />
the total facility energy into its IT<br />
equipment energy with the most ideal<br />
score being 1.0.<br />
10<br />
VOL 5 ISSUE 1
5 tips to help protect your business<br />
from cybercrime<br />
<strong>Business</strong>es of all sizes are at risk from the ongoing threat of cyberattacks and the theft<br />
of sensitive data. George O’Dowd from Novi Technology details the risks businesses<br />
face from cybercrime and the steps they can take to protect their business.<br />
Many businesses have fallen victim to security breaches<br />
without their knowledge. An ageing infrastructure and<br />
a growing trend in the automation of cyberattacks –<br />
making them smarter, harder to detect and more<br />
widespread – is contributing to the increasingly delicate security<br />
environment.<br />
SMEs in Ireland are taking risks with their reputation and their<br />
ability to conduct their business by overlooking the dangers of<br />
cybercrime. A recent survey by Zurich Insurance revealed that<br />
nearly half of SMEs surveyed didn’t feel that they needed to<br />
protect their business against cyberattacks, despite listing data<br />
protection as one of their biggest concerns.<br />
Small and medium-sized business owners need to become<br />
acutely aware that they are as likely to be hit with cybercrime as<br />
their bigger competitors but they are less equipped financially<br />
and operationally to absorb the impact.<br />
Below are some of the ways criminals can gain access to your<br />
data – and what you should do to protect yourself.<br />
1. Malware<br />
Using malware hackers can silently transfer your customer data or<br />
intellectual property to external servers where it is collected and<br />
sold for substantial gains. More often than not employees provide<br />
access to systems by clicking on a compromised email or a<br />
disguised file download.<br />
2. Unprotected systems<br />
Criminals can also get inside your network by targeting security<br />
vulnerabilities on unpatched devices. Many businesses have fallen<br />
victim to ransomware, whereby company data becomes<br />
encrypted, leaving the business paralysed unless a ransom is paid<br />
to criminals for the unlocking key.<br />
Nearly a quarter (23pc) of Irish organisations have been held to<br />
ransom by a hacker, and yet the vast majority (93pc) assert they<br />
would never pay a ransom.<br />
3. Exposed Wi-Fi access<br />
Poorly configured wireless access points are often an easy way to<br />
access corporate networks from outside the building, and in<br />
some situations guest access is not partitioned from internal<br />
systems, leaving company data exposed. Organisations, small<br />
and large, should implement more complex password policies<br />
that need to be regularly changed.<br />
4. Unsecured devices<br />
Laptops should be encrypted and you should be wary of the<br />
devices you allow to connect to your internal wireless network.<br />
5. Data storage<br />
If you are using cloud-based service providers ensure they are<br />
credible and that your data is encrypted and protected offsite.<br />
For online businesses it is important that you don’t store<br />
customer payment data on your servers, ensure servers are<br />
regularly patched and updated and consider implementing<br />
safeguards against distributed denial of service (DDoS) attacks. A<br />
DDoS attack consists of hundreds if not thousands of connections<br />
being made to your systems at the same time, causing them to<br />
become overwhelmed and unusable, which can lead to<br />
significant loss by forcing your website offline.<br />
Firms need more focus on detecting IT attacks, event hears<br />
The biggest information technology security challenge for<br />
companies is detecting and responding to threats, according to<br />
Rob Sadowski, director of marketing at security company RSA.<br />
However, many businesses are still wrongly focused on outdated IT<br />
security tactics, trying to prevent attacks by using antivirus software<br />
and firewalls rather than aiming to detect inevitable intrusions and<br />
then prevent or contain damage, he said in an interview at the<br />
company’s annual RSA Security Conference in San Francisco.<br />
“Defences are often built for yesterday’s IT,” he said.<br />
“Companies are warming to that idea that it now isn’t if, but<br />
when, they will be attacked. But for that not to be a fatalistic point of<br />
view, what do you do?”<br />
The goal is to have systems, and increasingly, well-trained IT<br />
specialists in the company that can recognise an attack when it is<br />
happening, and detect it as early as possible to limit loss, he said.<br />
A recent survey of companies by RSA indicated three out of four<br />
organisations were “very dissatisfied with their ability to detect and<br />
investigate those threats,” Mr Sadowski said.<br />
VOL 5 ISSUE 1<br />
11
Zinopy launches 'inSIght'<br />
To help organisations to manage, monitor and measure their IT Security<br />
posture and Systems performance.<br />
For over a decade, Zinopy has been<br />
Ireland’s Market leading <strong>Solutions</strong><br />
Advisor and Services Provider of<br />
Information Security and<br />
Virtualisation Technologies.<br />
We have used our experience and<br />
expertise to bring to the market Ireland’s<br />
first Managed Operational Service called<br />
“Zinopy InSIght”.<br />
Zinopy InSIght has been designed to<br />
deliver <strong>Business</strong> Outcomes through<br />
Operational Excellence in both<br />
Information Security and Citrix<br />
Virtualisation.<br />
Zinopy InSIght – Security<br />
Intelligence<br />
John Ryan, CEO, Zinopy: “We recognised<br />
there was a gap in the market based<br />
on security skills shortage, rise in<br />
cyber attacks – in both sophistication<br />
and volume – and an increase in the<br />
complexity of today’s security<br />
landscape. Our managed security<br />
service is founded on Security<br />
Intelligence and Analytics and it<br />
provides organisations with full<br />
visibility of their network so that they<br />
can detect intrusions in real time and<br />
respond to breaches effectively”.<br />
Zinopy InSIght – Systems<br />
Intelligence<br />
Book your FREE consultation & demo with Zinopy to discover how our<br />
managed security intelligence service can keep your organisation secure.<br />
Email: ibmsecurity@zinopy.ie stating code ZinopyISO-01<br />
Aidan McEvoy, Sales Director,<br />
Zinopy: “We have been Ireland’s<br />
Citrix Platinum Partner for over 10<br />
years and have consistently invested<br />
in the best and brightest talent in<br />
the country; we are uniquely placed<br />
to offer a world class service to our<br />
customers. “Our goal is to help our<br />
Customers deliver a consumer type<br />
experience to their IT users through<br />
the use of innovative tools, business<br />
oriented processes and an<br />
enthusiastic and experienced team<br />
of people with one common<br />
imperative - to deliver a great<br />
Customer Experience”.<br />
The Zinopy inSIght Centre is<br />
based at our dedicated facilities in<br />
Dublin using industryleading<br />
innovative technology, providing<br />
the backbone for Zinopy’s managed<br />
services.<br />
Contact Zinopy to discuss your<br />
business requirements:<br />
Phone: 01-8976750<br />
Email: info@zinopy.ie<br />
Web: www.zinopy.ie<br />
12<br />
VOL 5 ISSUE 1
EXHIBITOR DIRECTORY<br />
SPONSORED BY<br />
Arkphire &<br />
Edgescan<br />
Tel: +353 (0) 1 207 5700<br />
Email: rita.martin@arkphire.com<br />
Website: www.arkphire.com<br />
Certification<br />
Europe Ltd<br />
Tel: +353 (0) 1 642 9300<br />
Email:<br />
info@certificationeurope.com<br />
Website:<br />
www.certificationeurope.com<br />
Managed Security Service<br />
2015 was a year of serious security breaches;<br />
Arkphire with edgescan can help prevent you<br />
from getting hacked while continuously protecting<br />
your business and client data.<br />
Edgescan is a Managed Security Service<br />
providing full stack coverage on both network and<br />
applications with continuous vulnerability<br />
assessment. It detects technical vulnerabilities and<br />
weaknesses before the hackers do. This is a hybrid<br />
offering as a managed service with human<br />
validation (edgescan security analysts) supporting<br />
customers globally. The combination of Arkphire’s<br />
ICT expertise with edgescan will provide an overall<br />
comprehensive solution to address the growing risk<br />
from insecure web applications and hosting<br />
environments.<br />
Arkphire combines their Managed Service<br />
Certification Europe is an accredited ISO<br />
Certification Body serving a wide range of<br />
clients from SME's, Multinationals and<br />
Government bodies. Certification Europe<br />
awards certification against a range of ISO<br />
Standards giving you a competitive advantage<br />
as well as driving quality, innovation & cost<br />
savings. ISO standards have helped company’s<br />
open up export markets and increase brand<br />
recognition and prestige.<br />
Proud of our expertise, we are considered an<br />
authority in Energy Management (ISO 50001),<br />
Information Security (ISO 27001),<br />
Environmental (ISO 14001), providing<br />
assessments as well as public and bespoke<br />
offerings with edgescan’s SaaS-based vulnerability<br />
management platform. The edgescan family offers<br />
advanced scanning technology with expert website<br />
and server security analysis, to enable customers to<br />
identify, prioritise, manage and remediate<br />
vulnerabilities. With a SaaS solution, customers can<br />
focus time and resources on the execution of other<br />
information security and ICT activities.<br />
Of all the vulnerabilities discovered by in 2015,<br />
63% could have been mitigated via patch,<br />
configuration and component management<br />
combined. Edgescan detects security weakness<br />
non-stop.<br />
ISO27001 focuses on "continuous improvement",<br />
so does edgescan. Talk with us today and feel free<br />
to measure your cyber resiliency and posture<br />
improvement with the edgescan vulnerability<br />
management service<br />
training courses in these areas.<br />
We partner with our clients to ensure their<br />
ISO certification becomes a valuable asset.<br />
With headquarters located in Dublin, we have<br />
local offices in the United Kingdom, Italy,<br />
Turkey and Japan.<br />
CloudAssist<br />
Tel: +353 (0) 1 685 2556<br />
Email: info@cloudassist.ie<br />
Website: www.cloudassist.co<br />
CloudAssist is a certified Microsoft Cloud Depl<br />
oyment Partner and is an Office 365 migrator<br />
for Microsoft Exchange and Sha repoint with a<br />
user-centric approach for improved <strong>Business</strong><br />
Process efficien cies and cost savings while<br />
achieving ISO27001 level of IT security includi<br />
ng digital signatures and Mobile Device<br />
Management MDM.<br />
We assist our clien ts to adopt the many<br />
cloud features of Office 365 and 3rd party addons<br />
so that their users are more connected<br />
both internally in the organisation and with<br />
external users such as suppliers, partners and,<br />
most importantly, the ir customers. Our aim is<br />
to help our clients to get the most of their<br />
inves tment in Office 365 by understanding<br />
the business needs and their own cloud<br />
readiness. CloudAssist is eligible to provide<br />
Office 365 and SharePoint De ployment<br />
Planning services for clients with more than 50<br />
users which is wor th up to €3K towards their<br />
migration to Office 365 along with furth er<br />
grants for enterprises with more than 150<br />
Office 365 seats and clients w ith Enterprise<br />
Agreements. CloudAssist is the Proud sponsor<br />
of the non-pro fit initiative, Just Social, (Social<br />
Tech donations for Irish Charities) which<br />
includes Microsoft Office 365<br />
CalQRisk<br />
Tel: +353 (0) 61 477 888<br />
Email: enquiries@calqrisk.com<br />
Website: www.calqrisk.com<br />
CalQRisk was established to provide<br />
organisations with world class Enterprise-wide<br />
Risk Management software solutions-enabling<br />
them to identify and manage risks to the<br />
achievement of their objectives.<br />
Using CalQRisk, our flagship product, we<br />
provide access for clients to an extensive<br />
knowledgebase of risks and associated controls<br />
allowing them to measure and improve their<br />
risk management capability. Our<br />
knowledgebase is the product of the<br />
experience and wisdom of over forty subject<br />
matter experts. It continues to grow as<br />
additional sectors are addressed.<br />
Included in our rich knowledgebase are the<br />
risks and associated controls that would be<br />
expected to be in place in organisations that<br />
are ISO27001 compliant. If you are planning to<br />
seek accreditation to this standard you can<br />
carry out a self-assessment simply by<br />
answering the questions in our risk question<br />
sets. The CalQRisk Dashboard will quickly tell<br />
you those areas that need to be addressed to<br />
ensure you are compliant.<br />
For tools to support your Governance, Risk<br />
and Compliance efforts contact us today.<br />
16<br />
VOL 5 ISSUE 1
EXHIBITOR DIRECTORY<br />
SPONSORED BY<br />
Integrity360<br />
Tel: +44 (0) 1 2934 0207<br />
Email: info@integrity360.com<br />
Website: www.integrity360.com<br />
Now in its tenth year, Integrity360 has grown<br />
consistently year on year since its<br />
establishment in 2005, highlighting its position<br />
as the largest IT security specialist in Ireland,<br />
and the fastest growing in the UK.<br />
The company offers a complete 360 degree<br />
security services offering which includes<br />
Managed Security, Security Testing, Incident<br />
Handling, Security Integration and<br />
Governance, Risk & Compliance services.<br />
Its enterprise clients can be found in all<br />
business verticals and include some of the<br />
largest and most well-known brands in the<br />
country.<br />
IT Governance<br />
Ltd<br />
Tel: + 44 (0) 8450 701 750<br />
Email:<br />
servicecentre@itgovernance.co.uk<br />
Website: www.itgovernance.co.uk<br />
IT Governance is one of the foremost global<br />
providers of information security and ISO<br />
27001 solutions.<br />
Our strong focus on consultancy, training,<br />
penetration testing, software, tools, resources<br />
and guides, combined with flexible and costeffective<br />
delivery options, provide a unique,<br />
integrated alternative to the traditional<br />
information security provider.<br />
Having led ISO 27001 implementations since<br />
the inception of the Standard, our strong<br />
global presence gives us the knowledge and<br />
insight to provide valuable advice, tailored to<br />
meet any organisation’s specific needs and<br />
budget. We have helped hundreds of<br />
companies worldwide achieve ISO 27001<br />
certification, while many thousands of<br />
organisations use our products daily to help<br />
them tackle ISO 27001 implementation<br />
projects.<br />
Laztech IT<br />
Services<br />
Tel: +353 (0) 1 525 3627<br />
Email: carmel@laztech.ie<br />
Website: www.laztech.ie<br />
Laztech IT Services is an IT Managed Services<br />
provider.<br />
Our mission is to provide peace of mind to<br />
our clients. We consider ourselves to be the IT<br />
Department to our clients. Through<br />
collaboration we aim to ensure that IT systems<br />
are managed to the highest level of efficiency<br />
and performance, whilst maintaining data<br />
security. We are determined to deliver<br />
innovative, practical and cost-effective IT<br />
solutions that improve business performance.<br />
Our services include:<br />
• Telephone, Remote, Offsite & Onsite<br />
Support / Fully Managed Services<br />
• Data Encryption, Virus Protection & SPAM<br />
Filtering<br />
• Data Protection Compliance<br />
• Online Backup & Disaster Recovery / Cloud<br />
& Web Services<br />
• Hardware & Software Sales / Virtualisation<br />
• Consultancy & project Management<br />
Logicalis Ireland<br />
Tel: + 353 1 295 8966<br />
Email: info@ie.logicalis.com<br />
Website: www.ie.logicalis.com<br />
Logicalis is an international IT solutions and<br />
managed services provider with a breadth of<br />
knowledge and expertise in security services, data<br />
centre and cloud services, and managed services.<br />
Our IT security practice delivers a range of<br />
services that will help your organisation to reduce<br />
risk, ensure compliance, and secure sensitive data<br />
and systems across all platforms. We will protect<br />
your network, safeguarding the perimeter, critical<br />
internal assets, data, remote users, customers and<br />
partners. Our services provide key controls for<br />
regulations including PCI, ISO 27001 and 27002.<br />
Logicalis has specialised solutions for<br />
enterprise and medium-sized companies, across a<br />
range of vertical markets. Depending on your<br />
requirements, we can augment your existing<br />
security team or we can manage your entire<br />
security environment. Our services include<br />
security consultation, round-the-clock monitoring<br />
and management of intrusion detection systems<br />
and firewalls, overseeing patch management and<br />
upgrades, performing security assessments and<br />
security audits, and responding to emergencies.<br />
We maintain strong partnerships with<br />
technology leaders such as Cisco, IBM, HP, CA<br />
Technologies, NetApp, Microsoft, Oracle,<br />
VMware and ServiceNow on an international<br />
basis.<br />
For more information, visit<br />
www.ie.logicalis.com.<br />
VOL 5 ISSUE 1<br />
17
EXHIBITOR DIRECTORY<br />
SPONSORED BY<br />
MM Barcoding Ltd<br />
Tel: +353 (0) 1 846 2902<br />
Email: mrtnmulligan@gmail.com<br />
Website: www.mmbarcoding.com<br />
MM Barcoding (Ireland) Ltd is a long<br />
established company specialising in automatic<br />
identification.<br />
We supply a full range of barcode printers,<br />
scanners,verifiers,label making and asset<br />
tracking software as well as portable on line<br />
validation systems.<br />
In line with our policy of continuous product<br />
development,we have just launched our new<br />
unique printer with on board barcode<br />
verification which ensures that no barcodes are<br />
produced which will fall below the required<br />
quality.<br />
All products are backed by our in field<br />
service network supplying on site<br />
service,maintenance and parts.<br />
Sungard<br />
Availability<br />
Services<br />
Tel: +353 (0) 87 762 9861<br />
Email:<br />
ciara.conifrey@sungardas.com<br />
Website: www.sungardas.ie<br />
Sungard Availability Services (“Sungard AS”) is<br />
a leading provider of critical production and<br />
recovery services to global enterprise<br />
companies.<br />
Sungard AS partners with customers across<br />
the globe to understand their business needs<br />
and provide production and recovery services<br />
tailored to help them achieve their desired<br />
business outcomes.<br />
Leveraging 35 years of experience, Sungard<br />
AS designs, builds and runs critical IT services<br />
that help customers manage complex IT,<br />
adapt quickly and build resiliency and<br />
availability. Visit Sungard Availability Services at<br />
www.sungardas.ie or call (+353) 01 467 3650.<br />
Connect with us on Twitter and our Blog.<br />
Ward <strong>Solutions</strong><br />
Tel: +353 (0) 86 1843 722<br />
Email: info@ward.ie<br />
Website: www.ward.ie<br />
Ward <strong>Solutions</strong> are an information security<br />
consultancy and system integration company.<br />
We help organisations protect their brand,<br />
people, assets, intellectual property and profits<br />
by identifying the threats, and minimising the<br />
risks that they face.<br />
Zinopy<br />
Tel: : + 353 (0)1 897 6750<br />
Email: info@zinopy.ie<br />
Website: www.zinopy.ie<br />
Zinopy is one of Ireland’s leading IT solution<br />
and service providers and specialist in driving<br />
business agility through Security, Virtualisation,<br />
Mobility and Managed Services.<br />
Zinopy offers a unique blend of deep<br />
industry knowledge and specialist technology<br />
expertise to deliver real business value to<br />
organisations of all sizes across a wide range of<br />
commercial sectors.<br />
The company has 25+ years’ experience in<br />
delivering security solutions and managed<br />
security services to Irish businesses across a<br />
range of verticals in the Public and Private<br />
sectors, including Data Security, Data<br />
Classification, Identity and Access<br />
Management, Application Security, Email and<br />
Web Security, Advanced Threat Protection,<br />
SIEM, Intrusion Prevention and Detection and<br />
Secure File & Data Sharing.<br />
Zinopy is Ireland’s leading Citrix Platinum<br />
<strong>Solutions</strong> Advisor, an IBM Security <strong>Business</strong><br />
Partner and partners with an extensive range<br />
of other world-wide leading vendors in the<br />
virtualisation and security markets.<br />
See www.zinopy.ie for more information.<br />
18<br />
VOL 5 ISSUE 1
Panama Papers show there’s no place<br />
to hide in a data-centric world<br />
The only guarantee of secrecy in the 21st century will be to have no secrets. In<br />
what is the biggest data set to fall into the hands of journalists, a treasure trove of<br />
data on tax avoidance and dodgy dealings by the so-called great and good has<br />
been laid bare.<br />
The 2.6 terabyte leak of Panama-based shell company<br />
Mossack Fonseca has rocked the establishment<br />
worldwide, revealing a tawdry industry that involved<br />
banks, legal firms and asset management companies all<br />
centred on managing the estates of a motley crew of well-heeled<br />
types ranging from FIFA officials to politicians, celebrities,<br />
professional athletes, property developers and more.<br />
The revelations have even led to calls for the prime minister of<br />
Iceland Sigmundur Daví? Gunnlaugsson to step down and<br />
brought 10,000 protestors to the streets after leaked documents<br />
showed his wife owned a secret offshore company that had a<br />
potential claim on the country’s collapsed banks.<br />
It is a tawdry tale of offshore tax havens for rich and powerful<br />
individuals, including, it is alleged, Russian president Vladimir<br />
Putin and the late father of British prime minister David Cameron,<br />
and shows how Mossack Fonseca allegedly helped clients launder<br />
money and avoid paying taxes for 40 years.<br />
The unfolding drama could potentially touch nerves in every<br />
country.<br />
Panama Papers: the biggest data breach of its kind?<br />
The interesting thing about the Panama Papers is that it signals a<br />
new era in terms of data breaches and the impact they can have.<br />
This has been labelled by the media as the biggest data breach of<br />
its kind in history.<br />
This data, in turn, was quietly studied by more than 400<br />
journalists from more than 100 media organisations in over 80<br />
countries who were part of the International Consortium of<br />
Investigative Journalists.<br />
They have spent the past year studying more than 11.5m<br />
documents relating to Mossack Fonseca and the companies<br />
linked to it.<br />
What we are witnessing is merely the tip of the iceberg as more<br />
and more data will get analysed and deciphered by not only 400<br />
journalists but a growing army of volunteers on sites like Reddit<br />
who are only too happy to stick it to the man.<br />
For example, Reddit is currently recruiting translators who can<br />
help translate documents from Spanish, Dutch and Brazilian<br />
Portuguese.<br />
Crucially, the entire drama signals a new era for the<br />
whistleblower and could dwarf even the Snowden revelations or<br />
the Wikileaks Cablegate in 2010.<br />
What is unclear is how the data got out there, was it the work<br />
of an insider or whistleblower or the work of a sophisticated hack<br />
made possible by the most basic but insidious of phishing<br />
attacks?<br />
But what is very clear is this: a new benchmark in how data<br />
matters has been established. A digital trail can be a definitive<br />
trail.<br />
And the very notion of corporations, banks, legal firms and<br />
assorted advisers hiding a digital trail of sensitive breadcrumbs for<br />
no one to follow is a fairytale.<br />
A tawdry digital trail mulled over by hundreds of journalists and now a<br />
growing army of Reddit volunteers shows secrecy is a 21st-century<br />
fairy tale.<br />
20<br />
VOL 5 ISSUE 1
Staying In <strong>Business</strong><br />
Setting the Scene<br />
You arrive at work and everybody is standing in the car park,<br />
your building looks fine, but your neighbour’s building is<br />
billowing smoke and flames. The fire chief says nobody is<br />
allowed within 100 meters of the building. Your IT manager is<br />
there, looking pleased, you enquire. He says “Now aren’t you<br />
pleased we spent all that money on the remote backup and<br />
server replication. I just tested it last week and it’s all working<br />
fine”. “But”, you say, “Where will we go?” With no place to<br />
go how long will your customers wait for you?<br />
West of the Shannon<br />
For 9 years now Work Area<br />
Recovery <strong>Solutions</strong> (WARS) have<br />
been providing large and small enterprises with a “place to<br />
go”. The WARS recovery centre is located in Ennis Co Clare<br />
and includes an air-conditioned computer room with UPS and<br />
generator backup, 5 individual rooms with a total of 200<br />
desks, telephones and PCs. The model is simple; you pay an<br />
annual subscription /seat and you come and test your<br />
continuity plans. When disaster does strike, you are ready and<br />
you have a place to go to continue providing service to your<br />
customers.<br />
WARS continue to invest in their recovery centre. In March<br />
this year they completed the hardware re-fresh of the<br />
equipment. 206 new Dell Optiplex 3040 PCs were purchased<br />
and installed. This refresh ensures support for latest version of<br />
operating systems can be imaged onto the PCs.<br />
This refresh follows on from last year’s upgrade of the Cisco<br />
Unified Communications System. Gerard Joyce, CTO of WARS,<br />
says “Our customers tell us that their customers are asking<br />
them what their “disaster arrangements” are”. Don Kearns, IT<br />
Manager with Kneat <strong>Solutions</strong> and customer of WARS says<br />
“We were impressed with the range of services in the Disaster<br />
Recovery space that is provided by WARS. To find this gem in<br />
the Mid-West region was doubly impressive. We found Gerry<br />
and the team at WARS to be extremely helpful and flexible,<br />
providing first class support in the setup and operation of our<br />
DR solution.”<br />
Loss Events = Opportunities for Disaster<br />
Loss events come in many guises: fire, flood, storm damage,<br />
utility outage, systems loss, people loss and many more. Any<br />
loss event is an opportunity for disaster. A loss event turns<br />
into a disaster for an enterprise if the Maximum Tolerable<br />
Outage (MTO) is exceeded or the Minimum Essential Service<br />
is lost. The MTO is the point in time at which the loss event<br />
begins to damage your business. It depends on a number of<br />
factors driven by the enterprise objectives and its<br />
commitments. How long can you be “away from the market”<br />
before the objectives are materially impacted? How long<br />
before permanent un-recoverable damage is done to your<br />
revenue, reputation, or the things that matter to your<br />
enterprise? The MTO is a function of time, measured in<br />
minutes, hours or days, depending on the nature of your<br />
enterprise. The Minimum Essential Service (MES) is the<br />
degree to which the enterprise has to recover from a loss<br />
event in order to stem loss of revenue, reputation or the<br />
things that matter to your enterprise.<br />
VOL 5 ISSUE 1<br />
21
Now in its fifth year, Data Centres Ireland is the county’s leading event for all those<br />
involved with smaller server-rooms and coms-rooms through to to the staff<br />
responsible for Operations, NOC, IT, Networking and Facilities Management, at<br />
large co-location, corporate and cloud data centres.<br />
Data Centres Ireland will be held at the RDS, Dublin on<br />
the 8 – 9 November 2016. This refreshingly intimate<br />
venue adds to the quality of the conference - and the<br />
ability to have unhurried and high quality<br />
conversations with vendors and speakers which makes Data<br />
Centres Ireland well worth taking time to visit.<br />
Feedback received from exhibitors following the 2015 event,<br />
was that exhibitors were extremely impressed with the quality of<br />
attendees delivered and the professional atmosphere created, as<br />
they were able to spend time with clients, discussing their needs<br />
and potential solutions.<br />
“This is a business forum where all those involved can come<br />
together, share knowledge, see the latest in products, services<br />
and solutions which can assist them. As well as an opportunity for<br />
companies providing datacenter services to meet their customers<br />
and be seen to be supporting their industry and their suppliers.”<br />
Say Hugh Robinson, Event Director<br />
Visitors included senior level people from key target companies,<br />
as well as representatives from companies operating their own<br />
data centres and server rooms from across the country. These<br />
<strong>Business</strong> networking.<br />
included Microsoft, Intel, Ebay, Interxion, Facebook, Digital<br />
Realty, Amazon Web Services, Telecity, Apple, Trinity College,<br />
Boston Scientific and Primark to name but a few.<br />
Many repeat exhibitors, commented that this year’s event had<br />
delivered a greater number of senior level decision makers from<br />
leading organisations, compared to previous years, and that the<br />
opportunity to meet these people in person would not have<br />
occurred, if they had not been exhibiting.<br />
The Data Centres Ireland conference programme will address<br />
three main areas:<br />
Strategy – This will focus on the Development Drivers, Market<br />
Drivers, Finance, People and Opportunities, which Ireland offers.<br />
Operational <strong>Issue</strong>s – Covering the whole remit of design and<br />
operations from the latest updates on standards, the relevance<br />
(or otherwise) of PUE in smaller data centres and server rooms,<br />
and all of the hardware and services from cabling through<br />
cooling, power, UPS, monitoring, DCIM, Construction Products<br />
Regulation & how it applied to DCs, Codes and Standards.<br />
Data Storage – This will look at storage options whether using<br />
your own servers, co-location, managed services, outsourced and<br />
cloud based solutions.<br />
Call for Papers - Get involved<br />
“We would like to invite all those who have<br />
interesting case studies to submit a paper<br />
for consideration and potential inclusion in<br />
the Data Centres Ireland conference<br />
programme. Simply send a 200 word<br />
outline of your proposed paper detailing the<br />
key points it will address to<br />
datacentres@stepex.com. The deadline for<br />
paper submission is 10 July 2016.<br />
Attendees of Data Centres Ireland can<br />
expect the entire catalogue of high quality<br />
speakers as when the programme is<br />
announced in the coming months.<br />
Those interested in reserving a stand at<br />
the event or wanting to know more about<br />
the opportunities Data Centres Ireland can<br />
offer them should call Hugh Robinson on<br />
+44 (0) 1892 518877, email<br />
datacentres@stepex.com or visit the website<br />
www.datacentres-ireland.com.<br />
22<br />
VOL 5 ISSUE 1
AdaptiveMobile estimates up to 80% of<br />
‘connected’ devices do not have adequate<br />
security measures<br />
AdaptiveMobile, the world leader in<br />
mobile network security, predicts<br />
that up to 80% of connected<br />
devices currently deployed do not<br />
have adequate security measures in place,<br />
with four in five devices on the market<br />
vulnerable to malicious or inadvertent<br />
attacks and data breaches.<br />
As the level of connectivity between<br />
devices continues to grow, a new model<br />
using a ‘big security’ approach of<br />
harnessing big data, telemetry and security algorithms is going to<br />
be needed to effectively protect the billions of devices connected<br />
through the Internet of Things (IoT).<br />
Gartner’s research report, Predict 2016: Security Solution,<br />
discusses how the “security market will continue to evolve<br />
alongside new requirements from the Internet of Things, cloud<br />
computing and sophisticated targeted attacks…Gartner estimates<br />
that a new architectural model will evolve, alongside such<br />
demands, in which security technology and services will be made<br />
available at the device and network layer, characterizing the<br />
emergence of security solutions made within endpoints,<br />
gateways and IoT platform providers.”<br />
AdaptiveMobile’s CTO, Ciaran Bradley, explains, “A new<br />
security architecture is required to deal with the increasing<br />
connectivity of devices belonging to the Internet of Things. There<br />
will be billions of devices connected through IoT – many unable<br />
to run traditional endpoint security – and there is no definitive<br />
ruling on who has responsibility to enforce this security and who<br />
is liable when a vulnerability is exploited.” He continues, “We<br />
need to be able to detect threats at scale –<br />
using a combination of lightweight<br />
telemetry and anomaly detection to give<br />
early indicators of compromise – and then<br />
enforce protection at scale. Not only are<br />
consumer devices at risk but automotive<br />
and industrial categories need to ensure<br />
security is a critical consideration – we do<br />
not believe this will be solved through<br />
current approaches to security, particularly<br />
when it comes to legacy systems.”<br />
Given the increasing number of connected devices on the<br />
market, the frequency at which IoT vulnerabilities are being<br />
exploited and the pressure to keep costs of commercial devices<br />
low, manufacturers need to make security a priority. IoT security<br />
is complex, constantly evolving and needs to be a critical<br />
consideration.<br />
AdaptiveMobile’s NPP6 is the world’s first converged carrier<br />
security platform, providing consistent security irrespective of<br />
device, operating system or end-user’s technical expertise.<br />
Combining the latest data science techniques, machine learning<br />
and advanced anomaly detection algorithms, with the<br />
Company’s world-class threat intelligence services,<br />
AdaptiveMobile is increasingly working with existing customers<br />
and industry partners to bring its expertise to help secure the<br />
rapid growth of IoT connectivity.<br />
For more information on new IoT security demands and to read<br />
Gartner’s Predicts 2016: Security <strong>Solutions</strong> please visit<br />
https://www.gartner.com/technology/mediaproducts/newsletters/AdaptiveMobile/1-2TP3L1F/index.html<br />
Weekend takeaway: 10 tech stories you need to read right now<br />
Ten nuggets of knowledge to take away for the weekend,<br />
including: the future of security; cool and unusual data<br />
centre designs; and security issues over driverless cars.<br />
1. Deciphering the puzzling future of data security<br />
From hackers to unencrypted smartphones and the spectre<br />
of full-scale cyber warfare, the future of data security is set to<br />
be a complex one that will affect us all.<br />
2. Autonomous cars are terrifying some cybersecurity<br />
experts<br />
Driverless cars are on the way, of this we are sure. But,<br />
truthfully, how safe are they going to be? We asked some<br />
cybersecurity experts and the answers were pretty worrying.<br />
3. Check out 7 cool data centres with oddly innovative<br />
designs<br />
As the growth in data centres continues apace, we look at<br />
some of the more creative ways tech companies store their<br />
mounds and mounds of data.<br />
4. With great amounts of data comes great responsibility –<br />
and opportunity<br />
We are in danger of turning data and privacy into taboo<br />
subjects. Instead, we need to direct the conversation towards<br />
the potential opportunities of a data-centric world, writes<br />
John Kennedy.<br />
5. Are you ready to jump into hybrid cloud?<br />
Hybrid cloud is the major enterprise trend of today. But what<br />
is it, why does it matter and should you invest in it, asks John<br />
Kennedy.<br />
6. 3 issues defining data protection in Ireland today<br />
To mark Data Week, Mason Hayes & Curran looks at three<br />
areas surrounding data protection that are important both<br />
now and for the future.<br />
7. From the pinnacle of knowledge CIOs talk data<br />
management<br />
Leading CIOs and IT leaders give an insight into the data<br />
challenge, how to manage it and the kind of cutting-edge<br />
projects they are embarking upon.<br />
8. Leaders’ Insights: Bill Kearney, IBM Ireland Lab<br />
Bill Kearney is the vice-president of the IBM Ireland Lab and<br />
its Dublin Technology Campus.<br />
9. How will we store data in the zettabyte era? (Infographic)<br />
The amount of data we produce nowadays is truly mindboggling,<br />
so how will we store it?<br />
10. 4 top employers hiring for data management roles right<br />
now<br />
When it comes to the glittering world of data jobs, it’s often<br />
all about data science and data analytics. Data management,<br />
sadly, generally gets short shrift.<br />
VOL 5 ISSUE 1<br />
23
Protect your business online and<br />
offline<br />
Risk of physical attack will always be there, but new threats are emerging<br />
It used to be the case that if somebody tried to steal from<br />
your business, an alarm would go off and the authorities<br />
would act accordingly. In the 21st century however, the<br />
landscape is entirely different and changing rapidly.<br />
Of course, the threat of physical attack is much as it always<br />
has been, and the Garda has guidelines for business owners<br />
on its website as to how best to mitigate the risk to your<br />
business and what to do if the worst happens.<br />
These include keeping the premises well lit, utilising grilles<br />
or shutters at entrances and windows, keeping tills out of the<br />
sight of the public, employing anti-ram bollards outside, and<br />
investing in appropriate locks and CCTV.<br />
But how can you protect your business when the assailant is<br />
not barging through the front door with a spanner in hand<br />
but rather manipulating staff and covertly gaining access to<br />
sensitive information before you have even noticed.<br />
Protecting your business is about knowing what the risks<br />
are, how to recognise the signs when they appear and taking<br />
the necessary action to fend off attacks.<br />
The Irish Small and Medium Enterprises Association (Isme)<br />
produces a crime survey of its members each year. Last year,<br />
79 per cent of companies who responded said they had been<br />
targeted by computer-related criminal activity.<br />
Some 51 per cent said their business had fallen victim to a<br />
“virus infection”; 51 per cent to “hacking or electronic<br />
intrusion”; and 20 per cent to credit card fraud.<br />
Among the things to look out for is “ransomware”. One of<br />
the fastest-growing types of cyber threats, it encrypts data on<br />
infected machines before asking businesses to pay ransoms in<br />
hard-to-trace digital currencies to retrieve their data.<br />
Companies with an online presence are also facing what is<br />
called a “distributed denial of service” attack, which is when<br />
so much traffic is sent to a website that it cannot cope and<br />
legitimate users cannot gain access. Like ransomware, a sum<br />
of money is demanded before normal service can resume.<br />
“It’s become much more prevalent, and particularly with<br />
small- and medium-sized enterprises because they may not<br />
have the resources to dedicate to these types of issues,” says<br />
information security consultant Brian Honan.<br />
“If your website is of high value to your business, you need<br />
to make sure you’re talking to your host and provider to make<br />
sure you have appropriate protection in place.”<br />
In terms of a defence against blackmail or extortion,<br />
something as simple as backing up your data could make all<br />
the difference.<br />
There is also an attack called “CEO fraud”. This is when<br />
company employees receive emails or correspondence<br />
purporting to be from the chief executive or a senior member<br />
of staff requesting money transfers to specific accounts that<br />
are under the control of the perpetrators.<br />
“The emails will look like they come from the company’s<br />
CEO and sound like the company’s CEO in tone but in actual<br />
fact they’re coming from the criminals, who may have hacked<br />
the CEO’s email account,” says Honan.<br />
Among the most serious type of attack is what is known as<br />
Caption for image - Hacker attack: last year, 79 per cent of companies in an<br />
Isme survey said they had been targeted by computer-related criminal activity.<br />
an “advanced persistent threat”. This uses multiple phases to<br />
break into a network, avoid detection and harvest valuable<br />
information over the long term. Perpetrators will often<br />
employ a combination of social engineering, blackmail and<br />
malware to achieve their aims.<br />
Paul Dwyer, president of the International Cyber Threat<br />
Task Force, believes breaches are inevitable these days.<br />
Criminals, he says, want to “work under the radar” and<br />
detection is key to prevention.<br />
“Data is the new cash,” he says. “What bad guys want is to<br />
get your data. Once they have it, they can sell it a number of<br />
times on underground stock exchanges. All different types of<br />
data have different values.”<br />
Another safeguard is to employ proper anti-malware<br />
controls, and to carry out regular security checks to make<br />
sure the system is actually working.<br />
“People need to look from the inside out as well,” says<br />
Dwyer. “They need to look at whether, if somebody does get<br />
in, they do have any safeguards. If they are in, will we<br />
actually be able to detect them?”<br />
Whether you are protecting your business from physical or<br />
online attack, a key thing to do is identify what is most<br />
valuable to your business, whether that is information, cash<br />
or stock.<br />
Steal information<br />
“If you’re connected to the internet, you need to realise the<br />
internet is connected to you,” says Honan. “It doesn’t matter<br />
where you’re located, criminals can still reach out and attack<br />
you or steal information. The biggest and best way to fend<br />
against them is to identify what information it is you’re trying<br />
to protect, where it’s located, and how best to protect it.<br />
“If it’s on a mobile device, make sure it’s encrypted and<br />
that you have anti-virus software installed. On your company<br />
network, make sure you have appropriate firewalls to prevent<br />
malicious traffic getting into your network.”<br />
Another important defence is to train staff to be aware of<br />
the risks and how to identify suspect attacks before it is too<br />
late. Government website makeitsecure.ie provides more<br />
24<br />
VOL 5 ISSUE 1
information on how best to do this.<br />
On April 1st, the International Cyber Threat Task Force will<br />
host a conference in Dublin’s Shelbourne Hotel to discuss<br />
“cyber risk oversight”. The event is directed towards<br />
business leaders who wish to learn more about cyber<br />
attacks.<br />
Dwyer says this “collaborative approach” will be vital in<br />
terms of online security. “The criminals collaborate,” he says.<br />
“They share information, intelligence, techniques, and they<br />
assist each other. That’s what businesses need to do. We<br />
need to share intelligence and give each other the heads-up<br />
in terms of the modus operandi, what they do, and what<br />
they’re after, and that’s the best way to thwart these guys.<br />
“You can invest in tonnes of technology, but active<br />
intelligence that can prevent this stuff is far more beneficial,<br />
and it costs next to nothing for businesses to be in touch<br />
with one another on a sector by sector basis.”<br />
Isme estimates the direct cost of crime per enterprise has<br />
risen to €9,539 per annum and the annual cost of<br />
prevention is €4,652 per company. This gives a total<br />
average cost of €14,191 per company annually. Chief<br />
executive Mark Fielding says finding the necessary resources<br />
is often a key constraint preventing businesses from<br />
employing the necessary security measures.<br />
What is a VPN and do you<br />
need one<br />
blocked in their country (One of the common examples is Netflix<br />
which have restrictions in many countries).<br />
2. People who are active in grey or even in dark areas, such as users<br />
who want to watch porn and do not want their internet provider or<br />
Google to know about it (in some countries, this is a criminal act),<br />
terrorists dealing with weapons, criminals encrypting data about their<br />
activity, etc.<br />
3. Journalists or people who live in countries that are run by repressive<br />
regimes that want access to social media or blocked news content.<br />
VPN applications were originally designed for big organizations<br />
with more than one PC office. VPN is an acronym for Virtual<br />
Private Network.<br />
Originally, VPN was used by large companies to connect computers in<br />
distant locations and until today, the use of VPN is popular among<br />
organizations with more than one PC office.<br />
Imagine, for example, that the Coca-Cola Company in Atlanta has an<br />
office building where all of the computers are connected to the<br />
company’s server through cables, and there is little danger that hackers<br />
will break into Coca-Cola’s private network.<br />
Now Coca-Cola opens an office in Canada and its employees in<br />
Toronto need access to the private network. But running a cable from<br />
the office in Atlanta to Toronto is a bit too much just to maintain<br />
privacy. Therefore the company uses a VPN to virtually create a private<br />
network (hence the acronym “Virtual Private Network” or VPN).<br />
This is how a connection was formed between the computer in<br />
Toronto and the main server in Atlanta in a secure way (the different<br />
communication protocols of the VPN are responsible for the security,<br />
which is, of course, not as perfect as a real private network, but is close<br />
enough).<br />
This connection that is established between these computers without<br />
any real cables is, of course, made through the internet. That is why,<br />
many workers (working from home, working from a hotel, or people<br />
commuting) can connect to Coca-Cola’s virtual private network as long<br />
as they have proper credentials.<br />
The illustration (on right) demonstrates how a VPN works.<br />
What can be done with VPN?<br />
Some of the most common uses of VPN are listed below:<br />
1. Unblocking sites – Some countries block services like Facebook,<br />
YouTube, Twitter and more. A VPN service allows you to be in<br />
China but lets you surf as if you are in the USA. Similarly, some<br />
schools and organizations block the access to popular sites and social<br />
networks and the solution to this is VPN.<br />
2. Hide identify – With VPN you can impersonate a user from a foreign<br />
country for a handful of reasons. (This is very useful in the internet<br />
community.)<br />
Recommended VPN services<br />
Nowadays, numerous VPN services are available. It seems as if every<br />
website developer is maintaining servers in different countries and calling<br />
themselves a VPN service.<br />
Nevertheless, load management (so that your surfing will not be<br />
slowed down because many people are using the server), the ability to<br />
slip past Netflix and its counterparts (that constantly try to detect the<br />
VPN services and block them) and more parameters create a distinction<br />
between these VPN services.<br />
There are three main audiences for VPN services:<br />
1. Regular people who simply want to surf anonymously, be it for<br />
security reasons, or the will to watch content over the internet that is<br />
VOL 5 ISSUE 1<br />
25
‘Irresolvable tension’ exists in data<br />
retention<br />
Conference told Experts say governments want to collect data, but are not<br />
focused on adequately protecting it<br />
An “irresolvable tension” often exists between the<br />
desire of government bodies to collect and use<br />
personal data, and the need to adequately protect<br />
that data, say experts.<br />
According to a panel on the second day of the RSA Security<br />
Conference, government bodies also are unaware of all the<br />
data they are collecting because it isn’t properly tracked or<br />
inventoried.<br />
In addition, many private organisations, research groups and<br />
other bodies are eager to obtain these large data sets, but<br />
generally have not thought through privacy concerns or<br />
management, said the participants in a session entitled<br />
“Government in the Crossfire: Data Privacy in an Era of<br />
Growing Cyberthreats”.<br />
“In order for us to approach how to manage (DATA<br />
PRIVACY), we need to know where it is,” said Flint Waters,<br />
state chief information officer for the state of Wyoming.<br />
Data gathering<br />
Agencies have a long history of mandating various types of<br />
data gathering “and we truly do not know what has been<br />
gathered.”<br />
Wyoming was preparing legislation to change this and<br />
require datasets be inventoried, he said.<br />
Road toll authorities also have gathered large data sets that<br />
they have resisted destroying, because they’ve never had<br />
access to such a range of data and now want to mine it, said<br />
Lee Tien, senior staff attorney with the Electronic Frontier<br />
Foundation.<br />
For example, data from Fastrak devices used to automatically<br />
pay tolls has been of interest to law enforcement but they’ve<br />
had no specific reason for holding it.<br />
“We asked, ‘well, why are you holding all this trip data from<br />
Fastrak?’, and they said, well, just in case,” Mr Tien said,<br />
noting this view was a major problem across agencies as well<br />
as companies.<br />
However, JR Reagan, global chief<br />
information security officer with Deloitte,<br />
said that general privacy policies were too<br />
broad to cover the more nuanced uses<br />
people might desire their information to be<br />
used for, for example to to receive specific<br />
services.<br />
these blanket policies around privacy, so data can be used for<br />
uses that you would like, but also be protected.”<br />
One problem with government discussions of privacy and<br />
security – such as the current US case where the FBI is pushing<br />
Apple to give access to a terrorist’s iPhone – is that they are<br />
seen as separate when they are actually closely intertwined,<br />
said Mr Tien.<br />
“It doesn’t make sense to talk about either without talking<br />
about the other, especially as people see privacy as security in<br />
many ways,” he said.<br />
In the Congressional hearings for Apple versus the FBI, a lot<br />
of people were resisting any sort of suggestion that there’s any<br />
sort of tension between privacy and security.”<br />
Instead, the government has framed the discussion as<br />
differing approaches to a security debate, he said.<br />
Conundrum<br />
While Mr Reagan argued that privacy is essentially contextual,<br />
Mr Tien said he could not see technology solving that<br />
conundrum any time soon – for example, that people might<br />
someday be able to tag their own information to allow it to be<br />
used in different ways in different contexts.<br />
A large problem was potential misuse, or abuse of such data<br />
by law enforcement, which can be very hard to uncover.<br />
“They’re capturing data and leveraging it against other data<br />
sets only they have access to,” said Mr Waters, noting he<br />
comes from a law enforcement background.<br />
“Then the data goes to private companies. In going to<br />
private companies, we’re seeing partnerships we’ve never seen<br />
before”, and the implications haven’t been adequately<br />
analysed.<br />
“I don’t see any solutions, except for all sides to accept there<br />
are problems. Denial is the step where we’re at. There are a lot<br />
of folks that don’t want to acknowledge that there’s a privacy<br />
problem in the first place,” said Mr Tien.<br />
‘Yesterday’s privacy constructs’<br />
“We fall into the trap of thinking all issues are<br />
resolved around privacy if we solve for the<br />
bad thing,” he said, noting that to often we<br />
are “trying to apply yesterday’s privacy<br />
constructs to a digital world that keeps<br />
moving faster. We actually need to have<br />
different constructs to manage the data<br />
differently. We need to move away from<br />
26<br />
VOL 5 ISSUE 1
New FCC rules could require ISPs to<br />
get user permission about data sharing<br />
The US Federal Communications Commission (FCC) is proposing new rules that<br />
will require internet service providers (ISPs) to get permission from users before<br />
they can share data about customers’ online activities with advertisers.<br />
FCC chairman Tom Wheeler has called for broadband<br />
service providers to disclose how data is collected about<br />
users’ online browsing activities. He also wants to see<br />
companies bolster the security of customer data.<br />
This will significantly curb the ability of companies like Comcast<br />
and Verizon, for example, to share advertising data.<br />
In effect, the FCC is establishing privacy rules for companies<br />
that manage web traffic and this is the next major step change in<br />
US telecoms policy after net neutrality.<br />
‘This isn’t about prohibition; it’s about permission’<br />
– TOM WHEELER, FCC CHAIRMAN<br />
“We all know that the social media we join and the websites<br />
we visit collect our personal information, and use it for<br />
advertising purposes. Seldom, however, do we stop to realise that<br />
our ISP is also collecting information about us,” Wheeler said in<br />
an op-ed in the Huffington Post.<br />
“What’s more, we can choose not to visit a website or sign up<br />
for a social network, or choose to drop one and switch to<br />
another. Broadband service is different. Once you subscribe to an<br />
internet service provider – for your home or for your smartphone<br />
– you have little flexibility to change your mind or avoid that<br />
network.”<br />
Wheeler pointed out that because the ISP handles all network<br />
traffic it has a broad view of a user’s unencrypted online activity.<br />
ISPs have access to an unencrypted feed all about your<br />
private life<br />
“If you have a mobile device, your provider can track your<br />
physical location throughout the day in real time. Even when<br />
data is encrypted, your broadband provider can piece together<br />
significant amounts of information about you – including private<br />
information such as a chronic medical condition or financial<br />
problems – based on your online activity.”<br />
Wheeler said that strict regulations exist around what phone<br />
companies can do with such information and that similar rules<br />
are required for the information collected by ISPs.<br />
“I’m proposing to my colleagues that we empower consumers<br />
to ensure they have control over how their information is used by<br />
their ISP. Every broadband consumer should have the right to<br />
know what information is being collected and how it is used.<br />
Every broadband consumer should have the right to choose how<br />
their information bits should be used and shared. And every<br />
consumer should be confident that their information is being<br />
securely protected.<br />
“This is not to say network providers shouldn’t be able to use<br />
information they collect – only that since it is your information,<br />
you should decide whether they can do so. This isn’t about<br />
prohibition; it’s about permission.”<br />
Wheeler proposes users can opt in or opt out of the various<br />
uses ISPs could have with the rich trove of data they can glean<br />
from web traffic about users.<br />
“One of the most important things to remember about this<br />
proposal is that it is narrowly focused on the personal information<br />
collected by network providers. The privacy practices of the<br />
websites that you choose to visit are not covered by this<br />
proposal,” Wheeler said.<br />
National Broadband<br />
Plan: At least 10 firms<br />
bid to end Ireland’s<br />
digital divide<br />
T<br />
he Irish Government’s long overdue intervention to bring<br />
750,000 postal addresses into the 21st century is gaining<br />
impetus after it emerged that at least 10 players have bid for<br />
two State broadband contracts valued at between €300m<br />
and €500m.<br />
The plan – supported by EU state aid – will fund operators<br />
to compete to deliver a guaranteed minimum of 30Mbps<br />
download speeds and 6Mbps upload speeds with 99.95pc<br />
uptime.<br />
However, there are indications that bidding firms, which<br />
includeEir, Enet and the ESB/Vodafone joint venture SIRO,<br />
intend to go way beyond this to 1Gbps fibre-to-the-home<br />
services, potentially creating a scenario where rural dwellers<br />
could, in time, have better broadband than their urban<br />
counterparts<br />
VOL 5 ISSUE 1<br />
27
Move to electronic payments adds<br />
€1.8bn to Ireland’s coffers<br />
Ireland’s move from being a cheque and cash dependent economy to an electronic<br />
one has resulted in €1.8bn being added to the nation’s GDP in just the last four<br />
years, creating an average of 3,700 jobs each year in the process.<br />
“The cheque is in the post,” were usually the last<br />
words Irish business owners heard from a<br />
customer before having to go to the bank<br />
manager in order to make payroll or before the<br />
bailiffs came calling.<br />
Ireland’s dependence on cheques and cash<br />
payments were a thorn in the side for most business<br />
owners, even if they didn’t realise it themselves, and<br />
this made Ireland something of an anomaly<br />
compared with more progressive countries, especially<br />
Scandinavian ones.<br />
But, in the last few years, something has changed<br />
and, according to a new Visa-commissioned study by<br />
Moody’s Analytics, the move to electronic payments<br />
has added €1.8bn to Ireland’s GDP.<br />
The contribution of the growth of electronic<br />
payments in Ireland to Irish GDP was double the<br />
European average.<br />
Cheque-ing out<br />
Moody’s economists also estimated that an average<br />
of approximately 3,700 jobs were created per annum<br />
over the four-year period as a result of the increased<br />
card penetration.<br />
The Moody’s Analytics study, which analysed the<br />
impact of electronic payments on economic growth across 70<br />
countries between 2012 and 2015, found that increased use of<br />
electronic payment products, including credit, debit and<br />
prepaid cards, added $296bn to GDP globally. The 70<br />
countries in the study make up almost 95pc of global GDP.<br />
“Electronic payments are a major contributor to<br />
consumption, increased production, economic growth and<br />
employment creation,” noted Mark Zandi, chief economist,<br />
Moody’s Analytics.<br />
“Those countries which saw large increases in card usage<br />
also saw larger contributions to overall growth in their<br />
economies.”<br />
The study indicates that the<br />
electronification of payments benefits<br />
governments and contributed to a more<br />
stable and open business environment.<br />
Annual spending on Visa cards –<br />
debit, credit and prepaid – in Ireland<br />
reached a new record of €31.7bn last<br />
year.<br />
As a result, transactions with a Visa<br />
card – debit, credit and prepaid – now<br />
account for more than a third of Irish<br />
consumer spending.<br />
This is due to the continued shift from<br />
cash and cheque usage as consumers<br />
opt for the convenience and security of<br />
Caption for image - No longer a cheque-driven backwater, the contribution of the growth of<br />
electronic payments in Ireland to Irish GDP was double the European average.<br />
x<br />
card payments.<br />
New technology such as contactless payments for purchases<br />
up to €30 has increased overall card usage, with more than<br />
one million contactless transactions now being made in Ireland<br />
every week.<br />
“Over the last 50 years, the rapid proliferation of electronic<br />
payments has enabled and improved how consumers pay for<br />
goods and services, how merchants manage their businesses,<br />
and how governments make and collect all sorts of payments,”<br />
Philip Konopik, Ireland Country Manager for Visa Europe, said.<br />
“The report findings reinforce the positive benefits that<br />
electronic payments have brought to Ireland, as increased<br />
consumption has contributed to<br />
growth in Irish GDP and also seen firms<br />
expand in order to meet increased<br />
demand for goods and services.”<br />
“We ultimately want to see this<br />
positive trend continue and are<br />
working globally with governments,<br />
financial institutions, merchants and<br />
technology companies to develop<br />
innovative payment products and<br />
services that will accelerate electronic<br />
acceptance, grow commerce, and<br />
bring the benefits of card payments to<br />
more people everywhere,” Konopik<br />
said.<br />
28<br />
VOL 5 ISSUE 1
Data <strong>Solutions</strong> announces<br />
20 jobs and €5M investment to<br />
triple its business<br />
· Irish company aims to triple its business to €80M turnover<br />
· €5M investment involves new hires and expansion into the UK with new Reading<br />
offices<br />
· 20 jobs across Ireland and UK to be filled by 2018<br />
Data <strong>Solutions</strong> announced it is investing €5 million and<br />
creating 20 new jobs to bring its team to 40. The<br />
leading Irish IT solutions distributor aims to triple its<br />
business over the next three years to €80 million<br />
turnover on the back of this investment.<br />
Part of the investment will be used to penetrate the<br />
competitive UK market, with new offices in Theale, Reading. This<br />
expansion will be used to bring best-in-class IT solutions from<br />
leading vendors Nutanix and Skyfii to the UK market. Data<br />
<strong>Solutions</strong> expects its UK operations to grow to the same size as its<br />
Irish business by 2018 and is targeting £30 million in UK turnover<br />
by then.<br />
The 20 new positions are being divided evenly between Data<br />
<strong>Solutions</strong>’ Dublin headquarters and its new offices in Reading.<br />
Roles are spread across technical support, sales and marketing<br />
and will be filled by 2018. The company has already hired two<br />
new account managers in Ireland and a managing director and<br />
sales manager to run operations in the UK.<br />
Along with Nutanix and Skyfii, Data <strong>Solutions</strong> has also signed<br />
partnerships with leading vendors Arista, CommVault and<br />
Supermicro. Other vendors Data <strong>Solutions</strong> works with in Ireland<br />
include Aruba, Check Point, Citrix, Dell Wyse, RSA Security and<br />
ShoreTel. It also has channel partnerships with the likes of Capita,<br />
Trilogy Technologies and Integrity 360.<br />
Speaking about the announcement, Michael O’Hara, group<br />
Pictured at the announcement of Data <strong>Solutions</strong>' expansion at the company's<br />
new UK offices in Theale are (l-r) Michael O'Hara, managing director, Data<br />
<strong>Solutions</strong>; Andrew Brewerton, channel manager, Nutanix; and Sean Fane, UK<br />
managing director, Data <strong>Solutions</strong>.<br />
Pictured at the announcement of Data <strong>Solutions</strong>' expansion at the company's<br />
new UK offices in Theale are (l-r) Brian Davis, datacentre sales manager, Data<br />
<strong>Solutions</strong>; Andrew Brewerton, channel manager, Nutanix; Michael O'Hara,<br />
managing director, Data <strong>Solutions</strong>; and Sean Fane, UK managing director, Data<br />
<strong>Solutions</strong>.<br />
managing director, Data <strong>Solutions</strong> said: “We’ve achieved<br />
exponential growth in the Irish market over the past few years<br />
and now we want to do that in the UK. We have a strong<br />
network there already and we’re bolstered by our new<br />
partnerships to grow a real presence now.<br />
“Our value comes from being more than a distributor. We’re<br />
passionate for partner growth and our team has the in-depth<br />
sales and marketing skills that can only be developed from being<br />
a true IT specialist unit. We choose products that will grow<br />
quickly and fast-track the introduction of disruptive new<br />
technologies to the market.”<br />
Andrew Brewerton, channel manager, Nutanix added: “We are<br />
committed to establishing strong relationships with our<br />
distributors and partners to deliver the best experience for<br />
customers. With its strong channel and remarkable ability to<br />
bring new technologies to market, Data <strong>Solutions</strong> has given us<br />
access to top-tier resellers in Ireland, which has been instrumental<br />
to our own growth in the region. We see a lot of opportunities in<br />
delivering invisible infrastructure, where computers, storage and<br />
virtualisation can be converged at any scale. We look forward to<br />
seeing the success with Data <strong>Solutions</strong> replicated across the UK.”<br />
Data <strong>Solutions</strong> specialises in security, next generation data<br />
centres and unified communications. The company has achieved<br />
steady year-on-year growth over the past 25 years. Through its<br />
channel, it can mobilise a sales force of more than 600 enterprise<br />
sales specialists.<br />
VOL 5 ISSUE 1<br />
29
Check out 7 cool data centres with<br />
oddly innovative designs<br />
As the growth in data centres continues apace, we look at some of the more<br />
creative ways tech companies store their mounds and mounds of data.<br />
Last month, Microsoft trialled its first underwater data<br />
centre. It had been planning it for years, and the move<br />
beneath the depths is reflective of a growing need to find<br />
better ways to store data. Cloud storage is intangible in<br />
consumers’ eyes, but that mystical, vague concept evaporates<br />
once you see the behemoth centres popping up all over the<br />
world.<br />
Often ugly, often gargantuan, and often major energy<br />
consumers, companies are now searching for ways to do things<br />
more efficiently. The net result is a growing suite of very clever,<br />
very attractive approaches.<br />
Here are 7 of the more innovative centres:<br />
Microsoft<br />
We’ll start with<br />
Microsoft, which<br />
said its Leona Philpot<br />
data centre (a<br />
38,000-pound container,<br />
10ftx7ft) was<br />
a resounding success.<br />
“The shrimp<br />
exploring the seafloor<br />
made more<br />
Microsoft<br />
noise than the data<br />
centre inside the container, which consumed computing power<br />
equivalent to 300<br />
desktop PCs,” Microsoft<br />
said.<br />
ected by a steel<br />
door 40cm thick.<br />
Google<br />
Google has revealed<br />
more about its data<br />
centres than most<br />
Google<br />
major tech companies,<br />
with Street View<br />
tours of some of their facilities. Branding is important, even when<br />
its as simple as painting tubes. Council Bluffs, with added deer,<br />
below, and an overview<br />
of the Lenoir<br />
base beneath that.<br />
CyberBunker<br />
Now we’re into<br />
some seriously weird<br />
scenarios, with CyberBunker’s<br />
use of a<br />
pretty impenetrable<br />
NATO bunker in the<br />
CyberBunker<br />
Netherlands enjoying<br />
a colourful history.<br />
Because of its “many controv-ersial customers”, CyberBunker<br />
has seen police forces attempt to break into the bunker to shut it<br />
down multiple times. However, but for a bit of damage to the<br />
doors, nobody has gotten through. The cold water circulation<br />
(below) is almost as old-school as those immensely thick doors.<br />
Citigroup<br />
Citigroup’s Frankfurt<br />
data centre won a<br />
green award back in<br />
2008 for its use of<br />
spacing and plants to<br />
drastically cut down<br />
on its CO2 emissions.<br />
Bahnhof<br />
Citigroup<br />
Bahnhof<br />
Bahnhof has a<br />
selection of remarkable<br />
looking data<br />
centres, with this<br />
one in Pionen –<br />
located in a nuclear<br />
bunker from the<br />
Cold War – its best<br />
known location. The<br />
entrance is prot-<br />
Green Mountain<br />
MareNostrum<br />
Located in a former<br />
chapel, the MareNostrum<br />
supercomputer sits in a<br />
wonderful glass case in the<br />
Barcelona Supercomputing<br />
Centre.<br />
Green Mountain<br />
Green Mountain’s<br />
data centre in Stavanger<br />
is built into a<br />
former NATO ammunition<br />
store. Here it is<br />
before they packed in<br />
the servers, with those<br />
colourful inclus-ions<br />
below, via Knut Bry<br />
MareNostrum<br />
30<br />
VOL 5 ISSUE 1
3 issues defining data protection in<br />
Ireland today<br />
Mason Hayes & Curran looks at three areas surrounding data protection that are<br />
important both now and for the future.<br />
Data protection in Ireland is being ramped up, with<br />
companies failing to adhere to data laws now in<br />
greater danger of facing fines of up to €20m.<br />
Looking globally, there have been some high-profile<br />
examples of data protection and the legal rights to it being<br />
played out in the courtroom, including the Google Spain ‘right to<br />
be forgotten’ case.<br />
There is then, of course, the EU’s highest court declaring in<br />
2014 that the EU Data Retention Directive was invalid, resulting<br />
in uncertainty for the corresponding national laws across the EU.<br />
In an opinion piece from the European Parliament’s Legal<br />
Services, the organisation said it firmly believed that EU member<br />
states should examine their national data retention measures to<br />
see whether they complied with the decision of the court.<br />
So, what changes has Ireland undergone in recent years and<br />
what precedent has been set by decisions outside of our control?<br />
ISO 27018: Cloud computing privacy standard – one<br />
year on<br />
Last September marked the first anniversary of the publication of<br />
ISO 27018 – an international privacy standard governing the<br />
processing of personal data in the cloud – that has been well<br />
received by data protection experts, but has not been without<br />
challenges for both customers and cloud providers.<br />
The standard confused many analysts and cloud providers as it<br />
made a number of references to both physical storage media and<br />
hard-copy materials, which seems somewhat out of place on a list<br />
of requirements for online cloud services.<br />
However, as Mason Hayes & Curran explains, cloud customers<br />
have been welcoming of the decision in the face of a growing<br />
demand for total company transparency now and in the future.<br />
Personal data and your right to access it — Ireland vs<br />
the UK<br />
We might share much in common with our nearest neighbour<br />
but, in some instances, we can be worlds apart.<br />
Highlighted last September by Masan Hayes & Curran, one<br />
such instance of this is when it comes to the legal framework for<br />
data protection surrounding a person’s right to access data<br />
Dropbox is just one of the world’s major cloud service providers adopting ISO<br />
27018. Photo: Connor McKenna.<br />
relating to them in contentious cases.<br />
One area that the two nations differ on was highlighted in the<br />
case of Ali Babitu Kololo, who submitted a subject access request<br />
(SAR).<br />
Kenyan national Kololo was found guilty of robbery with<br />
violence and the kidnapping of British nationals and sentenced to<br />
death by a Kenyan court and, as part of a challenge to his<br />
conviction, lawyers for Kololo submitted a SAR to the UK<br />
Metropolitan Police Service (MPS), which assisted with the<br />
investigation, but the reasoning behind this request was<br />
challenged by the MPS.<br />
Under Ireland’s legal framework, however, there’s much more<br />
power in the hands of the individual<br />
IoT<br />
Regular readers will be<br />
familiar with the concept<br />
of the internet of things<br />
(IoT), believed to be the<br />
next step in technology<br />
that will connect billions<br />
of devices sharing vasts<br />
amount of information<br />
with one another.<br />
Unsurprisingly, within<br />
that, there are major<br />
implications for data protection, which led to think tanks and<br />
governmental organisations putting their minds at work to<br />
develop frameworks that could lead to a regulatory standard for<br />
IoT devices to follow.<br />
What came from this, among other things, was the Article 29<br />
Working Party – a collection of 28 EU national data protection<br />
authorities – which devised a list of 10 of the biggest challenges<br />
facing an IoT future.<br />
VOL 5 ISSUE 1<br />
31
Irish Government not budging<br />
from original National Broadband<br />
plan route<br />
The Department of Communications said last night that the intervention area in<br />
the National Broadband Plan remains at 750,000 premises, despite Eir’s plans to<br />
connect 300,000 homes to 1Gbps broadband.<br />
The issue of broadband in Ireland is<br />
a highly emotive one and it<br />
became an election issue in 2016<br />
as many people who are unable to<br />
receive adequate broadband feel they are<br />
missing out on the social and economic<br />
opportunities provided by it.<br />
Before Christmas, the Government began<br />
the procurement process for the ?275m EUbacked<br />
plan that aims to deliver at least<br />
30Mbps broadband to 1.8m people, or<br />
38pc of the population not served with<br />
broadband of 21st-century quality, by<br />
2020.<br />
Around the same time, Eir revealed its<br />
plans to connect 300,000 homes in<br />
broadband-deprived rural areas to its latest<br />
1Gbps service with the first 100,000 home<br />
to be connnected by March 2017.<br />
Such a move would require the<br />
Government to amend the rollout plan as<br />
EU state aid cannot be directed towards<br />
areas supplied by a private sector provider.<br />
Broadband intervention area won’t be<br />
altered… just yet<br />
But it appears the Department of Communications<br />
is sticking to its original plan as<br />
drawn up in 2015.<br />
Five companies had applied for the first stage of the formal<br />
procurement process by the deadline of 12 noon yesterday (31<br />
March).<br />
The department said that certain criteria would need to be<br />
met and a binding agreement signed before premises can be<br />
excluded from the broadband intervention area.<br />
The department said that so far it has assessed the commercial<br />
plans of six operators in 2015 in respect of its criteria and it has<br />
found no reason to alter its plans.<br />
“The department wishes to place on record that, to date, no<br />
company has satisfied all of the relevant criteria and signed a<br />
Commitment Agreement in respect of any proposed commercial<br />
plans,” the Department of Communications stated last night.<br />
“The High-Speed Broadband Map 2020, therefore, remains as<br />
it was when published in 2015, and the intervention area,<br />
therefore, also remains at more than 750,000 premises.<br />
“The Department is monitoring existing commercial rollout<br />
The Irish Government said it is sticking to its multi-million euro EU-backed plan to connect up to 38pc of<br />
the population to high speed broadband.<br />
plans to ensure that all of the 1.6m premises, which commercial<br />
operators indicated they would complete by end 2016, will have<br />
access to high-speed broadband of at least 30mbps by end<br />
2016.”<br />
The Department of Communications said that while it does<br />
not plan to change the intervention area during the<br />
procurement process, it reserves the right to do so.<br />
“In the event that the department becomes aware of an<br />
increase or decrease in planned private sector investment, the<br />
department may review such changes and if it considers it<br />
appropriate, it may update the High-Speed Broadband Map<br />
2020 and the intervention area. Any review and change to the<br />
intervention area will take account of public procurement rules<br />
as well as State Aid rules and guidelines.<br />
“In this way, the separtment aims to ensure that all<br />
commercial plans are fully assessed and validated, and that the<br />
Government’s commitment to delivering high-speed broadband<br />
to every premises in Ireland is fully realised.”<br />
32<br />
VOL 5 ISSUE 1
Fastest-ever data transfer<br />
clocked at incredible<br />
1.125Tbps<br />
Imagine being able to download all of Game of Thrones in one<br />
second? Well, researchers have achieved a data transfer speed<br />
that could do just that.<br />
The fastest-ever data transfer record, achieved by a team from<br />
University College London (UCL), clocked in at a blistering<br />
1.125Tbps, which, the team is quick to point out, is 50,000-<br />
times faster than the average UK household speed of 24Mbps.<br />
With its research published in Scientific Reports, the team<br />
undertook the challenge by building an entirely new optical<br />
system to transmit the data, as well as developing its own<br />
coding techniques to fine-tune the transfer speed to the ultrafast<br />
speed it achieved.<br />
The optical system contains 15 channels, each of which<br />
transmits at a different wavelength and is then combined and<br />
sent to a single optical receiver for detection.<br />
In doing this, the researchers say that it turns it into a ‘superchannel’,<br />
widely believed to be the future of high-capacity<br />
communication, but it is years from being commercially<br />
available.<br />
Looking for a longdistance<br />
relationship<br />
The project is part of a UK-funded programme called<br />
UNLOC, which gave the team access to state-of-the-art<br />
lab facilities.<br />
Explaining the super-channel concept further, lead<br />
researcher on the project, Dr Robert Maher, said: “Superchannels<br />
are becoming increasingly important for core<br />
optical communications systems, which transfer bulk data<br />
flows between large cities, countries or even continents.<br />
“However, using a single receiver varies the levels of<br />
performance of each optical sub-channel, so we had to<br />
finely optimise both the modulation format and code rate<br />
for each optical channel individually to maximise the net<br />
information data rate. This ultimately resulted in us<br />
achieving the greatest information rate ever recorded using<br />
a single receiver.”<br />
Having only achieved this speed in a lab, the researchers<br />
will now aim to expand their concept to long-distance<br />
transmissions up to thousands of kilometres in distance,<br />
which typically leads to data loss.<br />
A booming time for Cork<br />
“<br />
Communications infrastructure and the internet economy as a<br />
whole are developing fast in Cork,” said Barry Rhodes, INEX’s<br />
chief executive, when commenting on the news.<br />
“The arrival of the Hibernia Express subsea fibre cable, and the<br />
other international subsea fibre cables that are expected, has<br />
created a momentum in the city that the INEX Cork internet<br />
exchange will help to further stimulate. INEX celebrates its 20th<br />
anniversary in 2016 and we are delighted to be marking this<br />
milestone with the launch of INEX Cork.”<br />
The news today follows the announcement by Interxion that<br />
the group is to open its third data centre in Dublin to better cope<br />
with demand, with the centre to be built in Grange Castle<br />
<strong>Business</strong> Park.<br />
Short Stories<br />
New INEX internet<br />
exchange to open in Cork<br />
to boost region<br />
Ireland’s Internet Neutral Exchange Association (INEX) is to<br />
open its first regional internet exchange point in Cork to<br />
help facilitate faster internet in the region.<br />
Founded in 1996, INEX has been providing IP peering<br />
facilities to more than 100 members, with six data centres<br />
currently based in the Dublin region.<br />
This, however, will be the association’s first opening outside of<br />
the capital as it looks to expand its national capacity following a<br />
year in which its centres reached peak traffic levels of 110Gbps,<br />
with a total usage of 200 petabytes of data for 2015.<br />
To be designated INEX Cork, the new venture will be located<br />
in the CIX data centre located in Holyhill and is expected to<br />
begin operations by the beginning of Q2 this year.<br />
As part of its remit, INEX Cork will also be operated as a<br />
standalone exchange.<br />
Banking is undergoing its most<br />
disruptive era ever, with every<br />
aspect of its traditional<br />
business model under attack<br />
from outside forces<br />
– This is bad news for frontline staff<br />
Up to 30pc of employee numbers at traditional banks could<br />
go over the next decade, with growing automation<br />
rendering huge swathes of staff roles outdated.<br />
That’s according to Citi’s report into digital disruption in the<br />
banking world, with it claiming a fintech-driven automation<br />
‘tipping point’ is coming in the immediate future.<br />
Saying branches are soon to become about “advisory and<br />
consultation” rather than transaction, the loading of fintech<br />
investment towards the end-user experience means plenty of<br />
lower-end positions are on the ropes.<br />
“We believe that there could be another 30pc reduction in staff<br />
during 2015-2025, shifting from the recent 2pc per year decline<br />
to 3pc per year, mainly from retail banking automation,” the<br />
report reads.<br />
Fintech feeding an Uber moment<br />
It’s worse news for countries like Greece and Ireland, where the<br />
financial crises were felt most, with the decline topping out at<br />
5pc per year according to Citi’s estimates.<br />
Fintech investment by financial institutions has risen from<br />
$1.8bn at the start of the decade to $19bn now, with 70pc of it<br />
focused on the customer experience. Given that this experience<br />
used to be ‘in-store’, you can see where the warning signs are.<br />
Calling the impending tipping point “banking’s Uber<br />
moment”, Citi claims it will specifically see a huge shift towards<br />
mobile banking, with it becoming customers’ primary mode of<br />
interaction with their banks.<br />
“Branches will be only one of the distribution channels. They<br />
will still play an important, albeit diminishing, role,” reads the<br />
report.<br />
Last December, the European research institute BearingPoint<br />
found that the vast majority (90pc) of banks’ new digitalisation<br />
prioritisation was needed, however, at that point just 17pc felt up<br />
to the task.<br />
Citi’s findings show that that low base is poised to skyrocket.<br />
VOL 5 ISSUE 1