- Page 1 and 2: Sophos XG Firewall v 15.01.0 - Rele
- Page 3 and 4: | Contents | 3 Web Categories......
- Page 5 and 6: | Contents | 5 Remote Users........
- Page 7 and 8: | Introduction | 7 Introduction Sop
- Page 9 and 10: | Using Admin Console | 9 Using Adm
- Page 11 and 12: | Using Admin Console | 11 The navi
- Page 13 and 14: | Using Admin Console | 13 You can
- Page 15 and 16: | Control Center | 15 IconStatus No
- Page 17 and 18: | Control Center | 17 Once Security
- Page 19 and 20: | Control Center | 19 Report Name N
- Page 21 and 22: | Policies | 21 Understanding Icons
- Page 23 and 24: | Policies | 23 Figure 1: About Thi
- Page 25 and 26: | Policies | 25 For example: If the
- Page 27 and 28: | Policies | 27 Figure 8: Policy fo
- Page 29 and 30: | Policies | 29 A new service can b
- Page 31 and 32: | Policies | 31 Figure 16: Routing
- Page 33 and 34: | Policies | 33 Decimal DSCP Descri
- Page 35 and 36: | Policies | 35 Redirect HTTP (Appl
- Page 37 and 38: | Policies | 37 Figure 23: Access P
- Page 39 and 40: | Policies | 39 The business applic
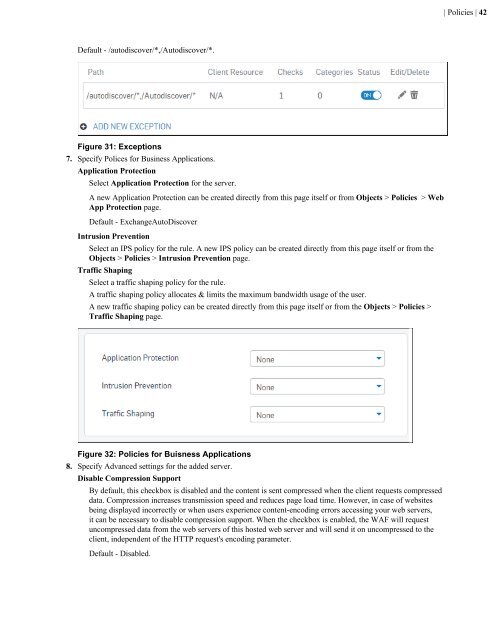
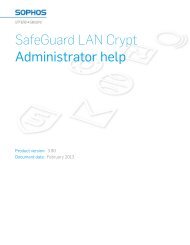
- Page 41: | Policies | 41 Default - /autodisc
- Page 45 and 46: | Policies | 45 Figure 35: Hosted S
- Page 47 and 48: | Policies | 47 Figure 38: Exceptio
- Page 49 and 50: | Policies | 49 Figure 41: About Th
- Page 51 and 52: | Policies | 51 Figure 43: Protecte
- Page 53 and 54: | Policies | 53 Figure 46: Policies
- Page 55 and 56: | Policies | 55 requests.IP Range -
- Page 57 and 58: | Policies | 57 Intrusion Preventio
- Page 59 and 60: | Policies | 59 start of the range
- Page 61 and 62: | Policies | 61 Figure 57: Access P
- Page 63 and 64: | Policies | 63 1. Click Policies a
- Page 65 and 66: | Policies | 65 Figure 63: Protecte
- Page 67 and 68: | Policies | 67 or if internal link
- Page 69 and 70: | Policies | 69 Figure 69: Hosted S
- Page 71 and 72: | Policies | 71 Figure 72: Exceptio
- Page 73 and 74: | Policies | 73 Enable hot-standby
- Page 75 and 76: | Policies | 75 SQL Injection Attac
- Page 77 and 78: | Policies | 77 Non-HTTP Based Poli
- Page 79 and 80: | Policies | 79 External Port Type
- Page 81 and 82: | Policies | 81 Zone Select the all
- Page 83 and 84: | Policies | 83 Timeout Specify the
- Page 85 and 86: | Policies | 85 Intrusion Preventio
- Page 87 and 88: | Policies | 87 Figure 89: Source 4
- Page 89 and 90: | Policies | 89 Figure 91: Routing
- Page 91 and 92: | Protection | 91 Protection From t
- Page 93 and 94:
| Protection | 93 Separate Zone The
- Page 95 and 96:
| Protection | 95 MAC hosts added u
- Page 97 and 98:
| Protection | 97 To create a mesh
- Page 99 and 100:
| Protection | 99 Table 1: Name Sta
- Page 101 and 102:
| Protection | 101 Group MAC Access
- Page 103 and 104:
| Protection | 103 • Terms of use
- Page 105 and 106:
| Protection | 105 Password Creatio
- Page 107 and 108:
| Protection | 107 General variable
- Page 109 and 110:
| Protection | 109 ... • For a
- Page 111 and 112:
| Protection | 111 Signal Strength
- Page 113 and 114:
| Protection | 113 Figure 101: Conf
- Page 115 and 116:
| Protection | 115 Figure 102: Gene
- Page 117 and 118:
| Protection | 117 The section disp
- Page 119 and 120:
| Protection | 119 Figure 107: Add
- Page 121 and 122:
| Protection | 121 Figure 109: Add
- Page 123 and 124:
| Protection | 123 bar.com Figure 1
- Page 125 and 126:
| Protection | 125 1. Enter a Name
- Page 127 and 128:
| Protection | 127 Figure 114: Appl
- Page 129 and 130:
| Protection | 129 Technology Displ
- Page 131 and 132:
| Protection | 131 Name Enter a des
- Page 133 and 134:
| Protection | 133 Note: You can fi
- Page 135 and 136:
| Protection | 135 Figure 119: Add
- Page 137 and 138:
| Protection | 137 Note: Sometimes
- Page 139 and 140:
| Protection | 139 1. Navigate to O
- Page 141 and 142:
| Protection | 141 Valid From and V
- Page 143 and 144:
| Protection | 143 Download Certifi
- Page 145 and 146:
| Protection | 145 2. Click on the
- Page 147 and 148:
| Protection | 147 Email Signature
- Page 149 and 150:
| Protection | 149 POP/S and IMAP/S
- Page 151 and 152:
| Protection | 151 • POP3/S and I
- Page 153 and 154:
| Protection | 153 Select the MIME
- Page 155 and 156:
| Protection | 155 Contains: Specif
- Page 157 and 158:
| Protection | 157 Outbound Spam):
- Page 159 and 160:
| Protection | 159 Default: 10 days
- Page 161 and 162:
| Protection | 161 The Device autom
- Page 163 and 164:
| Protection | 163 Figure 141: Data
- Page 165 and 166:
| Protection | 165 Email being one
- Page 167 and 168:
| Protection | 167 Figure 144: Quar
- Page 169 and 170:
| Protection | 169 Figure 146: Spam
- Page 171 and 172:
| System | 171 interfaces, interfac
- Page 173 and 174:
| System | 173 Available Options: S
- Page 175 and 176:
| System | 175 Note: Rapid commit s
- Page 177 and 178:
| System | 177 Override MSS Select
- Page 179 and 180:
| System | 179 MTU is the largest p
- Page 181 and 182:
| System | 181 Connect APN (Access
- Page 183 and 184:
| System | 183 Available Options:If
- Page 185 and 186:
| System | 185 Figure 163: VLAN Det
- Page 187 and 188:
| System | 187 • DHCP Only: In th
- Page 189 and 190:
| System | 189 Figure 167: Global S
- Page 191 and 192:
| System | 191 Figure 170: Advanced
- Page 193 and 194:
| System | 193 your RED does not ha
- Page 195 and 196:
| System | 195 Configure DHCP Enabl
- Page 197 and 198:
| System | 197 the only way to unlo
- Page 199 and 200:
| System | 199 Description Type Pro
- Page 201 and 202:
| System | 201 Status Status of the
- Page 203 and 204:
| System | 203 Figure 176: Add Wire
- Page 205 and 206:
| System | 205 On the System > Netw
- Page 207 and 208:
| System | 207 Description Optional
- Page 209 and 210:
| System | 209 Format: HH:MM::SS Fi
- Page 211 and 212:
| System | 211 4. Click Save. The I
- Page 213 and 214:
| System | 213 Gateway Failover Tim
- Page 215 and 216:
| System | 215 Figure 183: Backup G
- Page 217 and 218:
| System | 217 Figure 186: Network
- Page 219 and 220:
| System | 219 If both IPv6 and IPv
- Page 221 and 222:
| System | 221 You can also add IP
- Page 223 and 224:
| System | 223 Gateway Enable to us
- Page 225 and 226:
| System | 225 Specify the host nam
- Page 227 and 228:
| System | 227 Figure 197: Add DHCP
- Page 229 and 230:
| System | 229 Prefix / 64 Provide
- Page 231 and 232:
| System | 231 Figure 199: Advanced
- Page 233 and 234:
| System | 233 Figure 200: Neighbor
- Page 235 and 236:
| System | 235 4. DynAccess 5. Soph
- Page 237 and 238:
| System | 237 • Routing Informat
- Page 239 and 240:
| System | 239 This address range i
- Page 241 and 242:
| System | 241 Figure 208: IPv6 Uni
- Page 243 and 244:
| System | 243 • V2 Timers Update
- Page 245 and 246:
| System | 245 Interface Select the
- Page 247 and 248:
| System | 247 • IBM • Shortcut
- Page 249 and 250:
| System | 249 Available Options: N
- Page 251 and 252:
| System | 251 Figure 219: Override
- Page 253 and 254:
| System | 253 PIM-SM Configuration
- Page 255 and 256:
| System | 255 Tag Time Status Indi
- Page 257 and 258:
| System | 257 Database Database sh
- Page 259 and 260:
| System | 259 Area Indicates the I
- Page 261 and 262:
| System | 261 Internal/External Li
- Page 263 and 264:
| System | 263 0.0.0.0 indicates th
- Page 265 and 266:
| System | 265 protected even when
- Page 267 and 268:
| System | 267 1. Once the connecti
- Page 269 and 270:
| System | 269 DER ASN1 DN(X.509) N
- Page 271 and 272:
| System | 271 IP Family Select IP
- Page 273 and 274:
| System | 273 If there is a mismat
- Page 275 and 276:
| System | 275 • Remote Access
- Page 277 and 278:
| System | 277 Select remote certif
- Page 279 and 280:
| System | 279 On the User Authenti
- Page 281 and 282:
| System | 281 Cisco VPN Client CIS
- Page 283 and 284:
| System | 283 DNS Server 2 Provide
- Page 285 and 286:
| System | 285 Connection Status De
- Page 287 and 288:
| System | 287 PPTP Idle session ti
- Page 289 and 290:
| System | 289 Lease Mode Select if
- Page 291 and 292:
| System | 291 Status Displays if t
- Page 293 and 294:
| System | 293 Use HTTP Proxy Serve
- Page 295 and 296:
| System | 295 5. Make the followin
- Page 297 and 298:
| System | 297 Type URL Displays th
- Page 299 and 300:
| System | 299 Select the authentic
- Page 301 and 302:
| System | 301 This page provides o
- Page 303 and 304:
| System | 303 Generate Certificate
- Page 305 and 306:
| System | 305 • Regenerate CA Do
- Page 307 and 308:
| System | 307 1. Navigate to Prote
- Page 309 and 310:
| System | 309 Figure 241: Login Se
- Page 311 and 312:
| System | 311 Network Services - P
- Page 313 and 314:
| System | 313 Figure 247: Add Loca
- Page 315 and 316:
| System | 315 API Configuration AP
- Page 317 and 318:
| System | 317 Type Displays the th
- Page 319 and 320:
| System | 319 Backup & Restore Bac
- Page 321 and 322:
| System | 321 • Preserve existin
- Page 323 and 324:
| System | 323 Messages The Message
- Page 325 and 326:
| System | 325 Figure 261: Authenti
- Page 327 and 328:
Figure 262: SMTP Predefined Message
- Page 329 and 330:
| System | 329 • STARTTLS - SMTP
- Page 331 and 332:
| System | 331 Use Custom NTP Serve
- Page 333 and 334:
| System | 333 Manager Port Remote
- Page 335 and 336:
| System | 335 Authentication Authe
- Page 337 and 338:
| System | 337 Add Active Directory
- Page 339 and 340:
| System | 339 Version Select the v
- Page 341 and 342:
| System | 341 • Accounting stop
- Page 343 and 344:
| System | 343 Server IPv4 Port Ent
- Page 345 and 346:
| System | 345 3. Register user The
- Page 347 and 348:
| System | 347 Figure 279: Administ
- Page 349 and 350:
| System | 349 Figure 282: STAS Set
- Page 351 and 352:
| System | 351 User Portal Link Ena
- Page 353 and 354:
| System | 353 The Add Group page a
- Page 355 and 356:
| System | 355 Users The Users page
- Page 357 and 358:
| System | 357 You can also create
- Page 359 and 360:
| System | 359 View Usage Note: You
- Page 361 and 362:
| System | 361 3. Click Save. Reset
- Page 363 and 364:
| System | 363 Figure 289: Policies
- Page 365 and 366:
| System | 365 The Add Multiple Use
- Page 367 and 368:
| System | 367 Simultaneous Logins
- Page 369 and 370:
| System | 369 Figure 292: Color Sc
- Page 371 and 372:
| System | 371 Figure 294: Guest Us
- Page 373 and 374:
| System | 373 Response Format Resp
- Page 375 and 376:
| System | 375 Figure 297: Test Con
- Page 377 and 378:
| System | 377 • None (IP Address
- Page 379 and 380:
| System | 379 4. Click Save. Note:
- Page 381 and 382:
| System | 381 If Section Mea
- Page 383 and 384:
| System | 383 Note: You can enable
- Page 385 and 386:
| System | 385 4. Auxiliary Device
- Page 387 and 388:
| System | 387 • User can release
- Page 389 and 390:
| System | 389 Figure 298: Configur
- Page 391 and 392:
| System | 391 Click the add icon t
- Page 393 and 394:
| System | 393 If RADIUS server aut
- Page 395 and 396:
| System | 395 Global Settings Maxi
- Page 397 and 398:
| System | 397 Data Transfer Thresh
- Page 399 and 400:
| System | 399 Size - 700 X 80 pixe
- Page 401 and 402:
| System | 401 Guest User Registrat
- Page 403 and 404:
| System | 403 Response Format Resp
- Page 405 and 406:
| System | 405 DoS attacks are typi
- Page 407 and 408:
| System | 407 Zone LAN WAN DMZ WiF
- Page 409 and 410:
| System | 409 ICMP/ICMPv6 Flood IC
- Page 411 and 412:
| System | 411 • Optional fields:
- Page 413 and 414:
| System | 413 Enable Pharming Prot
- Page 415 and 416:
| System | 415 Figure 320: HTTP/HTT
- Page 417 and 418:
| System | 417 Traffic Shaping Sett
- Page 419 and 420:
| System | 419 Figure 325: Enable R
- Page 421 and 422:
| System | 421 The administrator ca
- Page 423 and 424:
| System | 423 Syslog is an industr
- Page 425 and 426:
| System | 425 Figure 332: Anti-Vir
- Page 427 and 428:
| System | 427 IP Address / Domain
- Page 429 and 430:
| System | 429 Current Activity The
- Page 431 and 432:
| System | 431 Downstream Bandwidth
- Page 433 and 434:
| System | 433 Click the icon to vi
- Page 435 and 436:
| System | 435 Out Interface Traffi
- Page 437 and 438:
| System | 437 Out Interface Traffi
- Page 439 and 440:
| System | 439 Malware Quarantine p
- Page 441 and 442:
| System | 441 Flooder Report You c
- Page 443 and 444:
| System | 443 Figure 354: Tracerou
- Page 445 and 446:
| System | 445 • Y-axis - % use L
- Page 447 and 448:
| System | 447 Disk Usage Graphs Gr
- Page 449 and 450:
| System | 449 Figure 362: WAN Data
- Page 451 and 452:
| System | 451 • Buffer used: 0 t
- Page 453 and 454:
| System | 453 Packet Information P
- Page 455 and 456:
| System | 455 Reason Select the re
- Page 457 and 458:
| System | 457 Connection ID Unique
- Page 459 and 460:
| System | 459 Available Options:IP
- Page 461 and 462:
| System | 461 Figure 371: Services
- Page 463 and 464:
| System | 463 Time Time when the e
- Page 465 and 466:
| System | 465 Message Message for
- Page 467 and 468:
| System | 467 Figure 378: Security
- Page 469 and 470:
| System | 469 View List of Admin E
- Page 471 and 472:
| System | 471 Figure 383: ATP Log
- Page 473 and 474:
| System | 473 3. From the drop-dow
- Page 475 and 476:
| Objects | 475 Domain/Admin Displa
- Page 477 and 478:
| Objects | 477 Search Queries Clic
- Page 479 and 480:
| Objects | 479 Expire Date Attribu
- Page 481 and 482:
| Objects | 481 Server IP/Domain Po
- Page 483 and 484:
| Objects | 483 Authentication Clie
- Page 485 and 486:
| Objects | 485 Access Point Overvi
- Page 487 and 488:
| Objects | 487 Name Enter a descri
- Page 489 and 490:
| Objects | 489 Figure 391: Add Web
- Page 491 and 492:
| Objects | 491 The Add IPS Pattern
- Page 493 and 494:
| Objects | 493 Figure 394: Add Web
- Page 495 and 496:
| Objects | 495 bar.com Figure 396:
- Page 497 and 498:
| Objects | 497 authority. It also
- Page 499 and 500:
| Objects | 499 Key Encryption Clic
- Page 501 and 502:
| Objects | 501 1. Navigate to Prot
- Page 503 and 504:
| Objects | 503 Organization Name S
- Page 505 and 506:
| Objects | 505 Name Provide a name
- Page 507 and 508:
| Objects | 507 • QoS policy whic
- Page 509 and 510:
| Objects | 509 1. Navigate to Syst
- Page 511 and 512:
| Objects | 511 Description Provide
- Page 513 and 514:
| Objects | 513 Reset User Accounti
- Page 515 and 516:
| Objects | 515 Available Options:E
- Page 517 and 518:
| Objects | 517 Quarantine digest i
- Page 519 and 520:
| Objects | 519 1. Edit the User ac
- Page 521 and 522:
| Objects | 521 Quarantine digest i
- Page 523 and 524:
| Objects | 523 Available Options:
- Page 525 and 526:
| Objects | 525 The Add Surfing Quo
- Page 527 and 528:
| Objects | 527 If you do not want
- Page 529 and 530:
| Objects | 529 Maximum Upload Netw
- Page 531 and 532:
| Objects | 531 Key life Lifetime o
- Page 533 and 534:
| Objects | 533 during authenticati
- Page 535 and 536:
| Objects | 535 Default - Disconnec
- Page 537 and 538:
| Objects | 537 • single policy f
- Page 539 and 540:
| Objects | 539 Default Select to v
- Page 541 and 542:
| Objects | 541 Each policy can fil
- Page 543 and 544:
| Objects | 543 8. Click Save. Traf
- Page 545 and 546:
| Objects | 545 It enables to assig
- Page 547 and 548:
| Objects | 547 Limit Upload/Downlo
- Page 549 and 550:
| Objects | 549 Note: You can find
- Page 551 and 552:
| Objects | 551 Figure 423: Add App
- Page 553 and 554:
| Objects | 553 Note: Sometimes use
- Page 555 and 556:
| Objects | 555 • You cannot dele
- Page 557 and 558:
| Objects | 557 The applications sh
- Page 559 and 560:
| Objects | 559 Technology Select t
- Page 561 and 562:
| Objects | 561 Add Hotspot Voucher
- Page 563 and 564:
| Objects | 563 Type Available Opti
- Page 565 and 566:
| Objects | 565 remembering the MAC
- Page 567 and 568:
| Objects | 567 Figure 435: Add FQD
- Page 569 and 570:
| Objects | 569 Figure 437: Add Cou
- Page 571 and 572:
| Objects | 571 Figure 439: Add Ser
- Page 573 and 574:
| Appendix A - Logs | 573 Message (
- Page 575 and 576:
| Appendix A - Logs | 575 Comp ID C
- Page 577 and 578:
| Appendix A - Logs | 577 Data Fiel
- Page 579 and 580:
| Appendix A - Logs | 579 6/9/2015
- Page 581 and 582:
| Appendix A - Logs | 581 Data Fiel
- Page 583 and 584:
| Appendix A - Logs | 583 Module-sp
- Page 585 and 586:
| Appendix A - Logs | 585 Message I
- Page 587 and 588:
| Appendix A - Logs | 587 Message I
- Page 589 and 590:
| Appendix A - Logs | 589 Log Compo
- Page 591 and 592:
| Appendix A - Logs | 591 Log Compo
- Page 593 and 594:
| Appendix A - Logs | 593 Log Compo
- Page 595 and 596:
| Appendix A - Logs | 595 Log Compo
- Page 597 and 598:
| Appendix A - Logs | 597 Log Compo
- Page 599 and 600:
| Appendix A - Logs | 599 Heartbeat
- Page 601 and 602:
| Appendix B - IPS - Custom Pattern
- Page 603 and 604:
| Appendix B - IPS - Custom Pattern
- Page 605 and 606:
| Appendix C - Default File Type Ca
- Page 607 and 608:
| Appendix C - Default File Type Ca
- Page 609 and 610:
| Appendix D - Supported Micro-Apps
- Page 611 and 612:
• Hit It Rich! Casino Slots • J