NC1607
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
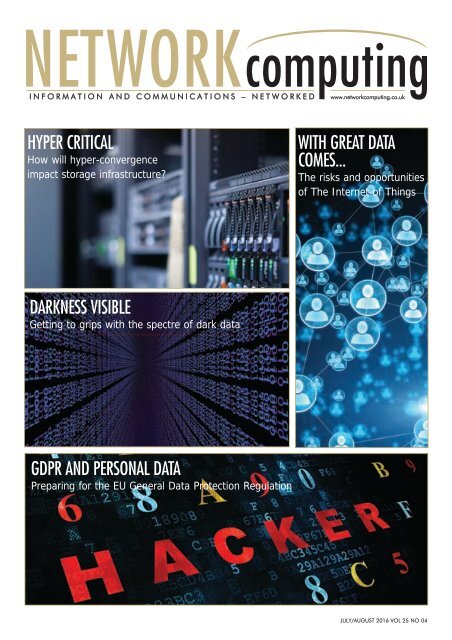
NETWORKcomputing<br />
I N F O R M A T I O N A N D C O M M U N I C A T I O N S – N E T W O R K E D www.networkcomputing.co.uk<br />
HYPER CRITICAL<br />
How will hyper-convergence<br />
impact storage infrastructure?<br />
WITH GREAT DATA<br />
COMES...<br />
The risks and opportunities<br />
of The Internet of Things<br />
DARKNESS VISIBLE<br />
Getting to grips with the spectre of dark data<br />
GDPR AND PERSONAL DATA<br />
Preparing for the EU General Data Protection Regulation<br />
JULY/AUGUST 2016 VOL 25 NO 04
You<br />
cannot<br />
keep up<br />
with data<br />
explosion.<br />
Manage data<br />
expansion with SUSE<br />
Enterprise Storage.<br />
SUSE Enterprise Storage, the<br />
leading open source storage<br />
solution, is highly scalable and<br />
resilient, enabling high-end<br />
functionality at a fraction of<br />
the cost.<br />
suse.com/storage<br />
Data
COMMENT<br />
COMMENT<br />
#TECHXIT OR OPPORTUNITY?<br />
BY RAY SMYTH, EDITOR<br />
Well, it happened. On the 23rd of June 2016, the United Kingdom, through a<br />
national referendum, voted to leave the EU. Already the Science and<br />
Research sector has spoken, generally forecasting disaster as EU funding and<br />
personal mobility is threatened.<br />
But what of the IT and technology sector? Organisationally we are already a very<br />
international bunch and of course the Internet is a foundation for this. Vendors supply<br />
goods and services on a global basis and their customers exercise every aspect of<br />
internationalism that is possible. Trade agreements will follow but no one is going to<br />
allow their business or personal life to slip into reverse.<br />
The EU has done some important work and the recent agreement around the<br />
General Data Protection Regulation (GDPR) is featured in this edition of Network<br />
Computing, and we plan substantial coverage up to and beyond its implementation as<br />
it's not going away. Best practice and doing things properly don't need additional<br />
labelling or sponsorship, and while no one says that GDPR is the ultimate tool for the<br />
job in hand, it must surely represent the best starting point that we currently have?<br />
As I suggested in my last introduction, it is important that vendors and IT professionals<br />
start a discussion that will ultimately build your plan: your plan not just for Brexit,<br />
but for the next five challenging years, in order to make sure that you can best serve,<br />
even dare I say, lead, the needs of your business. In this respect, please email me or<br />
Tweet me using #Techxit to share your thoughts and let's get the conversation started.<br />
EDITOR: Ray Smyth<br />
(ray.smyth@btc.co.uk)<br />
REVIEWS:<br />
Dave Mitchell<br />
Ray Smyth<br />
SUB EDITOR: Mark Lyward<br />
(netcomputing@btc.co.uk)<br />
PRODUCTION: Abby Penn<br />
(abby.penn@btc.co.uk)<br />
DESIGN: Ian Collis<br />
(ian.collis@btc.co.uk<br />
SALES:<br />
David Bonner<br />
(david.bonner@btc.co.uk)<br />
Lyle Boenke<br />
(lyle.boenke@btc.co.uk<br />
SUBSCRIPTIONS: Christina Willis<br />
(christina.willis@btc.co.uk)<br />
PUBLISHER: John Jageurs<br />
(john.jageurs@btc.co.uk)<br />
Published by Barrow & Thompkins<br />
Connexion Ltd (BTC)<br />
35 Station Square,<br />
Petts Wood, Kent, BR5 1LZ<br />
Tel: +44 (0)1689 616 000<br />
Fax: +44 (0)1689 82 66 22<br />
SUBSCRIPTIONS:<br />
UK £35/year, £60/two years,<br />
£80/three years;<br />
Europe:<br />
£48/year, £85/two years £127/three years;<br />
ROW:<br />
£62/year, £115/two years, £168/three years;<br />
Subscribers get SPECIAL OFFERS — see subscriptions<br />
advertisement; Single copies of<br />
Network Computing can be bought for £8;<br />
(including postage & packing).<br />
© 2015 Barrow & Thompkins<br />
Connexion Ltd.<br />
All rights reserved.<br />
No part of the magazine may be<br />
reproduced without prior consent, in<br />
writing, from the publisher.<br />
Ray Smyth - Editor, Network Computing.<br />
Ray.Smyth@BTC.CO.UK | https://twitter.com/ItsRay?<br />
GET FUTURE COPIES FREE<br />
BY REGISTERING ONLINE AT<br />
WWW.NETWORKCOMPUTING.CO.UK/REGISTER<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
JULY/AUGUST 2016 NETWORKcomputing 3
CONTENTS<br />
CONTENTS<br />
J U L Y / A U G U S T 2 0 1 6<br />
EU GDPR.............................10<br />
The EU General Data Protection Regulation<br />
is coming, Brexit or not - but what are its<br />
legislative and security implications for<br />
businesses in the UK? We asked some<br />
leading IT vendors for their thoughts<br />
EDITOR’S COMMENT......................3<br />
Techxit or opportunity<br />
COMPANY NEWS............................6<br />
Market Dynamics: making sense of the market<br />
NETWORK NEWS............................7<br />
Moves, adds and changes<br />
VERSION X......................................8<br />
The latest networking news<br />
INSIDE TRACK..................................23<br />
Getting to know the vendors<br />
ARTICLES<br />
GDPR AND PERSONAL DATA..........10<br />
By James Wickes at Cloudview<br />
RIGOROUS AUDIT............................11<br />
By Roman Foeckl at CoSoSys<br />
THE INTERNET OF THINGS..17<br />
This issue's feature on The Internet of Things<br />
offers some practical guidance for<br />
implementing IoT, warns of the increased<br />
security risk it brings to the network, and<br />
considers what the technology will mean for<br />
businesses and consumers alike<br />
HYPER CRITICAL.....................22<br />
Hyper-convergence is gaining traction.<br />
Sushant Rao, Director of Product and<br />
Solutions Marketing at DataCore considers<br />
its effect on storage infrastructure<br />
BEYOND TODAY’S LIMIT.......20<br />
Network testing and diagnostics needs a<br />
rethink as engineers need greater visibility,<br />
according to Tyson Supasatit, Product<br />
Marketing Manager at ExtraHop<br />
INFOSEC: WHAT NEXT?........30<br />
With the Infosecurity show now behind us<br />
for another year, where should professional<br />
visitors be engaging their minds? Our<br />
Editor, Ray Smyth, offers a view - with the<br />
help of some key vendors<br />
TAMING THE GDPR..........................13<br />
By Brian Chappell at BeyondTrust<br />
THE KNACK OF GDPR READINESS....14<br />
By Paul Donovan at Pulse Secure<br />
PRIVACY BY DESIGN.........................16<br />
By Ross Woodham at Cogeco Peer 1<br />
THE IOT SECURITY CHALLENGE.......17<br />
By Kathy Schneider at Level 3<br />
Communications<br />
WITH GREAT DATA COMES..............18<br />
By Larry Augustin at SugarCRM<br />
AN IOT ECOSYSTEM..........................19<br />
By Ryan Lester at Xively<br />
TAMING DARK DATA..........................24<br />
By Julian Cook at M-Files<br />
ASLEEP AT THE WHEEL........................26<br />
By Homan Haghighi at Alsbridge<br />
IOT SPELLS DANGER...........................34<br />
By Amit Ashbel at Checkmarx<br />
MASTERCLASS<br />
CERTES NETWORKS........................27<br />
Overcoming segmentaton fragmentation<br />
when enabling borderless applications<br />
PRODUCT REVIEW<br />
UNIFIED SECURITY SERVICE.....................15<br />
4 NETWORKcomputing JULY/AUGUST 2016 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
NEWS FROM NETVIZURA<br />
NETVIZURA - FREE NETFLOW ANALYZER FOR ACADEMIC INSTITUTIONS<br />
NetVizura was originally developed<br />
in close relation with academic<br />
environments in the area of<br />
research and testing. It was tailored to<br />
support flexible monitoring of large,<br />
complex and high-speed National<br />
Research and Education Networks<br />
(NRENs), which consists of many<br />
universities, faculties and research<br />
institutions, with numbers of smaller<br />
departments<br />
NetVizura NetFlow Analyzer provides<br />
flexible view of traffic statistics in such a<br />
complex network, based on NetFlow data<br />
exported even from a single central point<br />
(core router). By analysing total traffic<br />
from that point, or just a partition of<br />
traffic, i.e. custom traffic of interest,<br />
defined by concept of Traffic Patterns, it<br />
allows full statistics and monitoring of all<br />
subnets (nodes) through IP address<br />
hierarchy. It allows logical view to traffic<br />
structure in the network in addition to<br />
commonly used approach of monitoring<br />
traffic on physical level (per link or router).<br />
Another important demand was the<br />
ability to perform deep forensics, tacking<br />
analysis down to individual user traffic<br />
activity for investigating security incidents.<br />
For that reason NetVizura NetFlow<br />
Analyzer provides a searchable archive of<br />
all collected flow records, while a newly<br />
developed feature provides full statistics<br />
for each end user registered on corporate<br />
Windows domain or VPN server.<br />
These needs and demands in network<br />
monitoring from the academic community<br />
are today common to any professional<br />
network, especially large corporate<br />
networks. For this reason NetVizura<br />
NetFlow Analyzer is used by National<br />
Research and Education Networks<br />
(NRENs), such as Academic Network of<br />
Serbia (AMRES), universities and research<br />
institutions, as well as other commercial<br />
customers as a part of their network<br />
monitoring system. It provides efficient<br />
web based user interface with some of the<br />
most unique features, such as custom<br />
traffic monitoring, end user monitoring<br />
and deep forensics based on long-term<br />
archive of all flow records.<br />
NetVizura wants to give back to the<br />
academic community by offering a full<br />
NetFlow Analyzer license free of charge.<br />
In strengthening the ties with academic<br />
institutions we seek the possibility to<br />
improve both our software and the quality<br />
of academic network services. For those<br />
public funded academic institutions that<br />
wish to get involved, the Free Academic<br />
License Program (FALP) is available. By<br />
entering FALP they receive the full license,<br />
initial start-up support and software<br />
upgrades in order to enhance NetFlow<br />
Analyzer experience. As respected<br />
partners they also receive ongoing<br />
support, however these support tickets will<br />
be handled as secondary priority (after<br />
regular commercial customers).<br />
To apply for the Free Academic License<br />
Program, fill in the form at:<br />
https://www.netvizura.com/products/netfl<br />
ow-analyzer/get-quote/free-academiclicense-program.<br />
ABOUT NETVIZURA<br />
NetVizura provides easy-to-use, flexible<br />
and affordable network monitoring,<br />
forensics and security solutions - NetFlow<br />
Analyzer, EventLog Analyzer, MIB Browser<br />
and DNS Checker. NetVizura is a division<br />
of the company Soneco d.o.o. that<br />
specialises in software, networks and ICT<br />
consulting since 2006. To read more<br />
about the products, customers and<br />
company go to vendor website:<br />
https://www.netvizura.com.<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
JULY/AUGUST 2016 NETWORKcomputing 5
COMPANYNEWS<br />
MARKET DYNAMICS: MAKING SENSE OF THE MARKET<br />
IN A REGULAR LOOK AT RESULTS AND KEY BUSINESS ANNOUNCEMENTS FOR SUPPLIERS INTO THE<br />
NETWORKING AND IT MARKET, NETWORK COMPUTING SUMMARISES THE EDITORS SELECTIONS<br />
There is a lot happening in the<br />
networking market at the moment, and<br />
frankly anyone who claims to know<br />
how any of it will pan out should order their<br />
throne now. That said, there continues to be<br />
very strong evidence that the security sector<br />
is going through a very welcome and<br />
extremely vital evolution phase.<br />
IT services company Samsung SDS, an<br />
affiliate of Samsung Group, is<br />
accelerating investment in global startups.<br />
They have confirmed investment in<br />
UK based cyber security company<br />
Darktrace and Blocko, a Korean<br />
blockchain platform company.<br />
Commenting, a Samsung SDS<br />
spokesperson said, "Through these<br />
investments, Samsung SDS will be able to<br />
retain leading-edge technology in cyber<br />
security and blockchain. The company<br />
plans to collaborate closely with these<br />
start-ups to drive business growth.<br />
Samsung SDS will increase<br />
competitiveness of its cybersecurity<br />
business and services by promoting sales<br />
of the differentiated cyber threat defence<br />
solution by Darktrace to Korean<br />
companies, as well as work with Blocko to<br />
support commercialisation of emerging<br />
blockchain technology in various sectors<br />
including IoT."<br />
Darktrace is apparently one of the<br />
fastest growing cyber security companies<br />
in the world, and relies on advanced<br />
machine learning technology for detecting<br />
and responding to cyber threats. Samsung<br />
considers differentiated core technology<br />
as very important and invests in global<br />
start-ups in sectors such as AI, analytics,<br />
and IoT to secure disruptive technologies.<br />
It has been said that UK tech businesses<br />
often fail to scale in the way that many US<br />
businesses do. Managed services provider<br />
IT Lab has confirmed that ECI has agreed<br />
to acquire the majority shareholding in<br />
the company. This transaction will support<br />
IT Lab in its goal of becoming the UK's<br />
leading managed service, platform and<br />
business performance services provider,<br />
so there is some hope that this may buck<br />
that trend.<br />
Commenting on the news, Peter<br />
Sweetbaum, CEO of IT Lab said, "We<br />
provide vital IT services to SME and midmarket<br />
companies that are the backbone<br />
of the UK economy …IT Lab is in a very<br />
exciting growth phase with tremendous<br />
potential to expand our capability and<br />
reach [and] partnering with ECI will allow<br />
us to deliver a greater focus on clients."<br />
IDC has recently updated its DDI market<br />
report and identified EfficientIP as the DDI<br />
player with the highest growth rate.<br />
EfficientIP, the youngest company in the<br />
study, achieved a growth rate of 50 per<br />
cent year on year in 2015. The global<br />
DDI market sustained steady growth<br />
during 2015 due to growing market<br />
awareness, DNS security innovations,<br />
renewed vendor energy and the<br />
continuing digital transformation of the<br />
enterprise, adds IDC. David Williamson,<br />
CEO at EfficientIP remarked that "We're<br />
delighted to have been recognised. It<br />
proves our DDI solutions offer what the<br />
market needs."<br />
Talking of the market and inward<br />
investment, a new cloud-enabled<br />
enterprise Wi-Fi brand is coming to the<br />
UK. IgniteNet, already an established and<br />
growing supplier of indoor/outdoor<br />
hardware & cloud services in the US &<br />
Asia, plans to offer cost-effective cloudenabled<br />
networking to the UK market. The<br />
range comprises business-grade indoor<br />
Access Points and outdoor products with<br />
wireless AC starting from just £54, and<br />
includes robust Point-to-Point and Pointto-Multipoint<br />
radio antennas for<br />
connecting buildings up to 1.5kms away.<br />
Cloud managed layer 2 POE and fibre<br />
switches will launch later this year.<br />
What goes around... Southampton<br />
based law firm Moore Blatch have said<br />
that they are advising on the £57 million<br />
sale of Trustmarque Solutions Ltd to<br />
Capita. Trustmarque, a Microsoft LSP and<br />
the provider of software and cloud<br />
technology solutions for both public and<br />
private sector organisations, employs 620<br />
people across five UK locations. This sale<br />
takes place less than two years after<br />
Moore Blatch advised on the purchase of<br />
Trustmarque by the Liberata group. NC<br />
Disclaimer - all information published in this article is based upon fuller submissions provided under general release. Any interested party is urged to verify<br />
any information printed here, prior to using it in any way. Neither Network Computing nor it publishers accepts any responsibility for the accuracy of the<br />
information contained in this article.<br />
6 NETWORKcomputing JULY/AUGUST 2016 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
NETWORKNEWS<br />
NETWORK NEWS - MOVES, ADDS AND CHANGES<br />
A REGULAR LOOK AT THE STORIES INVOLVING PEOPLE, COMPANIES AND SOLUTIONS<br />
Is it possible that as Cyber criminals<br />
increase their scope and penetration<br />
they will consider introducing the concept<br />
of Customer Service? Well based on<br />
a report recently released by F-Secure, it<br />
seems so. The report found that three<br />
out of four criminal gangs practising<br />
Ransomware were willing to negotiate<br />
the fee for release.<br />
They evaluated the customer experience<br />
of five current crypto-ransomware<br />
variants, beginning with the initial ransom<br />
screen through to interacting with<br />
the criminals behind them. Apparently<br />
the most professional user interface did<br />
not necessarily offer the best customer<br />
experience and on average a 29 per<br />
cent discount can be negotiated with evidence<br />
that deadlines are not always set<br />
in stone. Because of the need to establish<br />
a degree of 'trust' with the victim<br />
many are ready to offer a certain level of<br />
service in order to realise payment.<br />
There is much regulation influencing<br />
the data residency decision. However,<br />
the Russian Government has recently<br />
passed a law that may compound this<br />
further. It makes Internet and Telecom<br />
user data storage mandatory and now<br />
calls, texts, chats and web browsing<br />
activity will be monitored and stored. The<br />
resulting information can then be<br />
accessed by authorities and some government<br />
agencies without a warrant.<br />
In response, NordVPN has taken a<br />
number of steps to ensure that Russian<br />
Internet user data is encrypted, notlogged<br />
and inaccessible even if their<br />
Russian servers are seized. Those servers<br />
are using advanced security protocols<br />
OpenVPN and IKEv2/IPsec as default<br />
and they operate a strict no log policy<br />
and store no data on any NordVPN<br />
servers. Finally VPN traffic on a server is<br />
encrypted and if a Russian service<br />
provider tracked the data, they would<br />
only see NordVPN servers' IP address<br />
and not the user's.<br />
There are other threats to data; using<br />
the Fidelis Cybersecurity Network solution,<br />
Exatel has found that a web browser<br />
developed by Chinese company,<br />
Maxthon has been collecting sensitive<br />
user data. Apparently, it transmitted endpoint<br />
information such as the OS version,<br />
screen resolution, CPU type/speed<br />
and amount of memory installed, location<br />
of Maxthon executable, status of<br />
adblock (enabled or not, number of ads<br />
blocked) and the homepage URL, which<br />
they say could indicate a reconnaissance<br />
operation.<br />
Justin Harvey, chief security officer at<br />
Fidelis Cybersecurity explains, "By knowing<br />
the exact operating system and<br />
installed applications, as well as browsing<br />
habits, it would be relatively trivial to<br />
send a perfectly crafted spear phishing<br />
attack to a target, or perhaps set up a<br />
watering hole attack on one of their<br />
most frequently visited websites." As a<br />
result, Harvey reminds us that<br />
"Organisations need to note two things.<br />
To be aware of the potentially egregious<br />
data capture happening through<br />
installed applications and leaving their<br />
organisation as well as their endpoints<br />
and secondly, software is frequently<br />
installed on endpoints at home and<br />
work, but that code is often not verified<br />
and may not be doing what it purports to<br />
do. Ultimately, it's only with visibility into<br />
both the network and endpoints that the<br />
Maxthon discovery was made, so it's vital<br />
that enterprises monitor both."<br />
There is more evidence that organisations<br />
are preparing themselves for the<br />
IoT opportunity. Tech Data Corporation<br />
has created a new Internet of Things<br />
(IoT) business practice called Smart IoT<br />
Solutions. It will be led by company veteran<br />
Victor Paradell who is currently VP<br />
IoT Solutions, Europe.<br />
According to Gartner, IoT endpoints<br />
are predicted to grow at a 32 per cent<br />
compound annual growth rate from<br />
2013 through 2020, reaching an<br />
installed base of 21 billion units, with<br />
almost two-thirds of them consumer<br />
applications. With such explosive growth,<br />
solution providers need clarity, education<br />
and an effective route to market. NC<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
JULY/AUGUST 2016 NETWORKcomputing 7
PRODUCTNEWS<br />
VERSION X<br />
VERSION X<br />
VERSION X<br />
VERSION X<br />
VER<br />
WITH PRODUCT ANNOUNCEMENTS RANGING FROM THE TRIVIAL TO THE BIZARRE, THE EDITOR<br />
DISTILS THE ESSENCE OF THOSE THAT ARE OF INTEREST TO THE NETWORKING COMMUNITY<br />
Claiming that it is the first mobile<br />
zero client solution based on standard<br />
laptops, Toshiba Europe<br />
GmbH has been explaining the purpose<br />
of its Toshiba Mobile Zero Client (TMZC).<br />
Using no operating system or hard drive,<br />
TMZC allows users to access their own<br />
virtual desktop, whether at work or at<br />
home, with no data hosted locally on<br />
either the HDD or solid state drive. All<br />
functionality and data is available<br />
through a cloud-based virtual desktop<br />
infrastructure, eliminating the possibility<br />
of malware being stored on the device<br />
and minimising the risk of data theft if<br />
PCs are lost or stolen. TMZC based computing<br />
leaves no footprint and is highly<br />
compatible with most existing IT infrastructure.<br />
51Degrees has introduced an NGINX<br />
(pronounced enginex) module to allow<br />
customers to integrate its fastest, most<br />
accurate device detection solution into<br />
existing NGINX frameworks. NGINX, an<br />
open source reverse proxy load balancer,<br />
is currently used by more than 40 per<br />
cent of the busiest websites, including<br />
Netflix, Pinterest, and WordPress.com.<br />
This module has been created from customer<br />
demand to provide seamless integration<br />
of its services. NGINX is known<br />
for its high performance, stability, rich<br />
feature set, simple configuration and low<br />
resource consumption.<br />
Commenting, James Rosewell, CEO and<br />
founder of 51Degrees said "We continuously<br />
strive to evolve in line with customer<br />
requests. The NGINX module allows customers<br />
to seamlessly integrate our device<br />
detection solution to improve the user<br />
experience and simplify their networks."<br />
Data centres don't always convey the<br />
image of a safe and pleasant working<br />
environment, and so the introduction of<br />
energy efficient, flexible to install LED<br />
Tubes optimised for aisle containment<br />
infrastructure might help. Minkels, who are<br />
part of the publicly traded company<br />
Legrand, have announced the LED tubes in<br />
two variants. In the first situation the LED<br />
Tubes are on 24/7, but in the second they<br />
are activated by means of a PIR movement<br />
sensor, meaning that they turn off automatically<br />
as the corridor is vacated.<br />
The high luminosity (335 LUX) combined<br />
with energy efficiency means that the LED<br />
Tubes are very useful when applied in the<br />
aisles of free standing corridors or next<br />
generation corridors, especially when<br />
using black coloured racks and corridors.<br />
Staying in the aisle, Dataracks has been<br />
talking about its latest fire detection and<br />
suppression solutions. They are now partnering<br />
with Nobel Fire Systems and<br />
Optex to produce the latest fire safety<br />
solutions. The Optex HSSD dust particles<br />
sensor sets new standards for the early<br />
warning of fires, with exceptional sensitivity<br />
and a built-in fan to provide active<br />
sampling. It can be easily mounted inside<br />
cabinets and racks to ensure rapid detection,<br />
which can potentially avoid a fire<br />
from breaking out in the first place.<br />
Dataracks also supplies Nobel Fire<br />
Systems' Stat-X range of fire suppression<br />
systems, which can also be installed into<br />
virtually any rack. Each compact, selfcontained<br />
aerosol unit offers strategic fire<br />
control to prevent escalation and limits<br />
the damage associated with whole-room<br />
fire suppression.<br />
Jeremy Hartley, Managing Director of<br />
Dataracks, comments, "As an innovationfocused<br />
company we are pleased to offer<br />
these fire safety solutions. Our new<br />
agreements with Optex and Nobel Fire<br />
Systems will ensure that we remain at the<br />
forefront of data centre improvement."<br />
Amazon Web Services (AWS) has<br />
enjoyed legendary success and now it is<br />
available from global interconnection and<br />
data centre company Equinix. The (AWS)<br />
Direct Connect cloud service in Equinix's<br />
Amsterdam International Business<br />
Exchange data centres means that companies<br />
can connect their customer-owned<br />
and managed infrastructure directly to<br />
AWS, establishing a private connection to<br />
the cloud that can reduce costs, increase<br />
performance and deliver a more consistent<br />
network experience. The Equinix<br />
Amsterdam location brings the total number<br />
of Equinix metros offering the Direct<br />
Connect service to eleven, globally.<br />
France-IX, the international Internet<br />
exchange based (unsurprisingly) in France<br />
and offering IPv4 & IPv6 public and private<br />
peering to Internet services<br />
providers, content delivery networks and<br />
8 NETWORKcomputing JULY/AUGUST 2016 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
PRODUCTNEWS<br />
SION X<br />
other types of Internet networks, has<br />
announced that Online.net, a French web<br />
hosting provider has joined the growing<br />
number of its peering members to<br />
upgrade to 100Gbps ports. The migration<br />
from four 10Gbps ports to two<br />
100Gbps ports has significantly boosted<br />
capacity at Online and is enabling the<br />
company to deliver increased performance<br />
benefits to its customers. Part of the<br />
Iliad Group, which also owns the operator<br />
Free, Online has been providing hosting<br />
services since 1999 and now hosts<br />
several hundred thousand websites across<br />
three data centres, offering a range of<br />
services including domain names, dedicated<br />
servers and web hosting to Internet<br />
stakeholders of all sizes, worldwide.<br />
Eric Schwartz, EMEA president for<br />
Equinix confirmed that "Our goal is to<br />
help enterprises realise the full benefits of<br />
the cloud, while helping to eliminate concerns<br />
of application latency or cost. By<br />
providing access to AWS via the Direct<br />
Connect service, we are empowering our<br />
customers to achieve improved performance<br />
of cloud-based applications."<br />
Ipswitch is launching the most significant<br />
update to its network monitoring<br />
portfolio in years. WhatsUp Gold 2017<br />
has been designed to alleviate the growing<br />
pressure on IT professionals, allowing<br />
them to visualise and interact with their<br />
network like never before, including the<br />
ability to troubleshoot faster with intuitive<br />
maps, workflows and dashboards, and<br />
monitor their entire environment with one<br />
flexible license. Commenting, Michael<br />
Hack, Senior Vice President of EMEA<br />
Operations said, "WhatsUp Gold 2017<br />
leverages advanced visualisation technology<br />
to intuitively map the user experience<br />
directly to the environment that the IT<br />
team created. The interface will be immediately<br />
familiar, allowing team members<br />
to easily understand irregularities at a<br />
high level and then drill down to detailed<br />
device level information, keeping them in<br />
front of potential issues."<br />
Prague based Avast Software has updated<br />
its flagship product, which can now<br />
deliver new technology to fight threats in<br />
a lightweight, high-speed solution that<br />
uses the cloud to identify and analyse<br />
threats. Avast Antivirus Nitro Update arms<br />
users with security software that is smaller<br />
in size and designed to improve speed,<br />
boot time, download time and system<br />
performance, while providing state-ofthe-art<br />
protection from never-ending<br />
attacks. Along with the Nitro Update<br />
comes security and performance<br />
enhancements to Avast's SafeZone browser,<br />
which isolates browsing sessions and<br />
gives users a much safer and more private<br />
browsing experience than a standard<br />
browser.<br />
Independent research conducted by testing<br />
institution AV-Comparatives found<br />
that PCs run faster with the Avast Antivirus<br />
Nitro Update than with Windows<br />
Defender, which is on by default on<br />
Windows 10 PCs. Avast CEO Vince<br />
Steckler says, "Our priority has always<br />
been to provide users with the best possible<br />
protection by staying on top of new<br />
and emerging threats. With the Nitro<br />
update we are bringing to users a tool<br />
that has minimum system impact and<br />
actually helps PCs perform faster, with the<br />
same strong protection they have grown<br />
to associate with Avast."<br />
With so many other things to think<br />
about, network downtime seems a somewhat<br />
archaic concept, but of course it is<br />
a real issue and to be avoided. Mindful<br />
of this, IDEAL Networks has upgraded its<br />
LanXPLORER Pro network troubleshooter.<br />
Alongside new diagnosis and connectivity<br />
features, technicians using LanXPLORER<br />
Pro can now transfer test data to mobile<br />
devices directly from the work site using<br />
the IDEAL AnyWARE app. The app allows<br />
users to quickly and simply share PDF or<br />
CSV test reports with colleagues or clients<br />
in order to enhance collaboration and<br />
troubleshooting capabilities and help<br />
boost productivity.<br />
The device minimises network downtime<br />
by quickly finding and diagnosing problems<br />
in networks, cabling and Ethernet<br />
devices using copper, fibre and Wi-Fi<br />
interfaces. By connecting directly to a<br />
specific point rather than scanning an<br />
entire network, the device can quickly<br />
verify status and connectivity and then<br />
monitor the total network bandwidth,<br />
analysing the top 10 bandwidth talkers<br />
and listeners to identify devices which<br />
may be impeding overall network performance.<br />
NC<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
JULY/AUGUST 2016 NETWORKcomputing 9
FEATUREGDPR<br />
GDPR AND<br />
PERSONAL DATA<br />
WITH GDPR INEVITABLE FOR ALL<br />
EU MEMBER STATES, URGENT<br />
ACTION AND MINDFUL<br />
PREPARATION IS AN ESSENTIAL<br />
IMPERATIVE. JAMES WICKES,<br />
CEO AND CO-FOUNDER OF<br />
CLOUDVIEW EXPLAINS<br />
The recently approved General Data<br />
Protection Regulation (GDPR) is<br />
described by legal firm Wright Hassall as<br />
the biggest shake-up of data protection law<br />
for 20 years. It will be directly applicable to<br />
EU member states without further<br />
implementation and serious breaches could<br />
see organisations facing fines from the<br />
Information Commissioner's Office (ICO) of<br />
up to 20 million euros or 4 per cent of<br />
turnover, whichever is higher, for serious<br />
breaches of the Act.<br />
To help clarify its impact we asked Wright<br />
Hassall to comment, and they highlighted two<br />
main points:<br />
Organisations whose core activity consists<br />
of processing special categories of data or<br />
the systematic large scale monitoring of<br />
individuals, must appoint a Data<br />
Protection Officer to monitor and ensure<br />
compliance.<br />
Organisations must ensure an individual's<br />
consent to the processing of their personal<br />
data is 'freely given, specific, informed and<br />
unambiguous' and in most cases, implied<br />
consent will not suffice.<br />
There could be even more at stake, however.<br />
The Culture, Media and Sport Committee's<br />
investigation into cyber security, which was<br />
triggered by the cyber-attack on TalkTalk, was<br />
published in June 2016. It makes two<br />
recommendations with major implications for<br />
those senior executive with legal responsibility<br />
for their organisation's behaviour.<br />
First, it suggests that a portion of CEO<br />
compensation should be linked to effective<br />
cyber-security. It then goes on to say: "We<br />
concur with the ICO that whilst the<br />
implementation of the GDPR will help to focus<br />
attention on data protection, it would be<br />
useful to have a full range of sanctions,<br />
including custodial sentences." So clearly,<br />
executives could face jail as well as fines for<br />
substantial breach of regulations.<br />
The increased fines will apply immediately<br />
after the GDPR is implemented, so it is vital to<br />
begin implementing GDPR compliant policies<br />
and processes as soon as possible. The first<br />
step is to carry out a Privacy Impact Assessment<br />
(PIA) to identify the most effective way to<br />
comply with data protection obligations and to<br />
meet individuals' expectations of privacy: this<br />
includes ensuring that all data is being<br />
gathered for a legitimate purpose and the ICO<br />
has produced a useful guide.<br />
Other factors that should be considered<br />
include secure storage of data along with<br />
safeguards to prohibit interception and<br />
unauthorised access; whether there is a<br />
published information retention policy which is<br />
documented and understood by those<br />
handling data collection; whether data is<br />
deleted when it no longer serves a purpose;<br />
and whether staff know how to respond to<br />
requests from individuals for access to their<br />
personal data.<br />
Finally, organisations need to understand<br />
that personal information is not just written text<br />
but includes photos, video and - a surprise to<br />
many - CCTV recordings. CCTV is often used<br />
to monitor communal areas, manufacturing<br />
sites and warehouses, but if footage enables<br />
individuals to be identified then it is covered<br />
by the GDPR. Adding sound to CCTV is a<br />
further concern, as CCTV surveillance systems<br />
should not normally be used to record<br />
conversations between members of the public<br />
or staff in a working environment. Recording<br />
conversations is highly intrusive and unlikely to<br />
be justified, and this is an example of that<br />
which would be identified by carrying out a<br />
thorough PIA.<br />
One potential solution for GPDR compliance<br />
is to hold information in the cloud, as this<br />
retains data securely off-site and many cloud<br />
systems already have all the required security<br />
and encryption in place. However,<br />
organisations still have to take responsibility<br />
for ensuring that their cloud provider is<br />
compliant with the new regulations, so there is<br />
no possibility of ignoring this responsibility, just<br />
better ways to achieve it. NC<br />
A briefing note, 'Is your use of CCTV<br />
compliant with data protection legislation', is<br />
available from the Wright Hassall website:<br />
www.wrighthassall.co.uk<br />
10 NETWORKcomputing JULY/AUGUST 2016 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
FEATUREGDPR<br />
RIGOROUS AUDIT<br />
WHATEVER THE IMPACT OF BREXIT ON EU LEGISLATION, ROMAN<br />
FOECKL, CEO AT COSOSYS EXPLAINS WHY A 'BY THE BOOK'<br />
AUDIT IS THE ESSENTIAL FIRST STEP TO DATA COMPLIANCE<br />
Two years may seem like a long time,<br />
but for EU organisations, particularly<br />
those that deal with data pertaining<br />
to European citizens, it will pass quickly as<br />
they battle to implement the mandated<br />
procedures and tools that will ensure their<br />
compliance with the reformed GDPR.<br />
Actually, given the strict rules and the fact<br />
that very few companies already have<br />
clear guidelines and policies for data<br />
security, especially referring to data in the<br />
cloud, two years may not be enough.<br />
Then, there's the specific character of this<br />
form of regulation such as it being<br />
ambiguous or leaving space for<br />
interpretation: it's not going to be easy.<br />
The highest success rate will be achieved<br />
by organisations that have a systematic<br />
approach based around the three steps of<br />
planning, execution and evaluation and<br />
usefully reinforced by some established<br />
policies. Whatever the case, chances will<br />
be maximised by starting immediately with<br />
an audit.<br />
The reformed EU Data Protection<br />
regulation is like a tribute to individuals'<br />
private data, forcing companies to<br />
increase measures to protect data, to<br />
ensure its integrity and to respect an<br />
individual's right for data deletion. The<br />
audit will establish exactly what data is<br />
collected and processed, and to whom<br />
and where it is transferred, especially if it's<br />
leaving the EU. The importance of the<br />
audit is clear and the entire outcome of<br />
the process of becoming compliant<br />
depends on it.<br />
There are several information audit<br />
management tools that can help with the<br />
audit, but they should always be<br />
accompanied by close supervision of key<br />
decision makers in the company, like CSOs,<br />
HR managers and other departmental<br />
managers that can advise on the business<br />
processes and the information flow.<br />
Data Loss Prevention is also a key tool<br />
that helps the audit process. It offers<br />
detailed reports on data being transferred,<br />
by whom, through what applications or<br />
what removable devices. Research recently<br />
conducted at Infosecurity Europe revealed<br />
that USB devices still represent a big<br />
threat, with 61 per cent of respondents<br />
saying that they are not forced to use<br />
encrypted USB devices and 21 per cent<br />
admitting to the loss of a USB device<br />
containing sensitive data.<br />
So you can see, knowing what data is<br />
being transferred to removable devices, on<br />
online services and applications, and the<br />
associated data, is vital for the audit and a<br />
first step in protecting data and complying<br />
with the revised data protection rules. DLP<br />
is the technology to help with this and<br />
since data controllers are responsible if<br />
data transferred outside of the EU is lost<br />
via a non-EU cloud provider, DLP will be<br />
even more important to detect sensitive data<br />
like personally identifiable information being<br />
transferred to online and cloud applications.<br />
The three essential steps of audit are:<br />
Detect and define what sensitive<br />
information about employees,<br />
customers, and other stakeholders your<br />
organisation stores and processes. This<br />
step is crucial for later steps, when the<br />
actual implementation of the data<br />
security policies will take place.<br />
Check and review your privacy<br />
notices, especially in your direct<br />
marketing activities. Consent has to be<br />
expressed explicitly for any piece of<br />
information collected which should<br />
only be used for the mentioned<br />
purpose; also, data controllers must<br />
be able to prove valid consent.<br />
Extend the audit to the information<br />
security software and hardware your<br />
organisation uses. The audit should<br />
reveal if the systems are updated with<br />
the latest security patches, if they cover<br />
all aspects included in the GDPR, if all<br />
threats vectors are somehow<br />
addressed, etc.<br />
During the audit, all actions and data<br />
should be carefully documented. Next, the<br />
corrective and restrictive measures to<br />
support the new regulations and update<br />
the incident response plan are needed. It<br />
is only at this point that a solid foundation<br />
will be established for the future. NC<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
JULY/AUGUST 2016 NETWORKcomputing 11
5-6 October 2016, ExCeL London<br />
SIX IT EVENTS UNDER ONE ROOF<br />
CLOUD<br />
EUROPE<br />
CYBER<br />
SECURITY<br />
EUROPE<br />
NETWORKS &<br />
INFRASTRUCTURE<br />
EUROPE<br />
DATA<br />
ANALYTICS<br />
EUROPE<br />
DEVOPS<br />
EUROPE<br />
OPEN<br />
SOURCE<br />
EUROPE<br />
Powering the Digital Enterprise<br />
Securing the Digital Enterprise<br />
Hosting the Digital Enterprise<br />
Insight into the Digital Enterprise<br />
Enabling Continuous Delivery<br />
Future of Collaborative Code<br />
IP EXPO Europe is Europe’s<br />
number ONE Enterprise IT event<br />
for those looking to find out how<br />
the latest IT innovations can<br />
drive their business forward<br />
REGISTER FREE<br />
ipexpoeurope.com
FEATUREGDPR<br />
TAMING THE GDPR<br />
IF YOU HAVE TAKEN THE<br />
APPROPRIATE MEASURES TO<br />
PROTECT YOUR DATA, AND<br />
HAVE CONSIDERED ALL OF<br />
THE RELEVANT LEGISLATION,<br />
THEN YOU HAVE NOTHING<br />
TO FEAR FROM THE EU GDPR,<br />
WRITES BRIAN CHAPPELL,<br />
DIRECTOR OF TECHNICAL<br />
SERVICES FOR BEYONDTRUST<br />
The EU General Data Protection<br />
Regulation (GDPR) extends data<br />
protection law to all companies<br />
processing the data of EU residents,<br />
irrespective of where the data processor is<br />
based. It means these companies have a<br />
simpler task: to comply with only one data<br />
protection approach across the whole of<br />
Europe. The penalties for non-compliance<br />
could be severe with substantial fines based<br />
on annual company turnover.<br />
The regulation has clearly been designed<br />
with social networks and mobile apps at its<br />
core, but the wording of the law means that<br />
it can be applied everywhere. That means<br />
everyone has to take this seriously and, with<br />
less than two years until it comes into force<br />
(even if you aren't an EU member), it's time<br />
to start getting ready for 23rd April 2018.<br />
As always with something new, radical<br />
and mandatory, making an early and<br />
effective start is critical.<br />
Security First: Data protection (DP) by<br />
design and by default is a key tenet of the<br />
new legislation, which means that data<br />
protection safeguards will be baked into<br />
products and services from the very earliest<br />
stages. In fact they should be considered as<br />
first principles. Don't start any new IT<br />
project, software development or service<br />
without having data protection at the front<br />
and centre of the activity. Anything<br />
underway but not yet released should be<br />
reviewed to ensure that DP is covered.<br />
Prevention is better than a cure: My first<br />
piece of practical advice is to address the<br />
preventative actions first when looking at<br />
your DP strategy. Privileged Password<br />
Management should be your first port of<br />
call; make sure that no-one has direct,<br />
unmonitored access to the data stores.<br />
From there, look to Least Privilege as a<br />
best practice to prevent anyone gaining<br />
inadvertent access to sensitive data<br />
through rights granted for an unrelated<br />
requirement. Good least privilege<br />
solutions allow you to know exactly what<br />
the user can do, and don't forget<br />
vulnerabilities. Just as you wouldn't forget<br />
a broken lock on your office building,<br />
don't forget to scan regularly (at least once<br />
a week) and fix those vulnerabilities that<br />
have published exploits.<br />
Detection, mitigation, protection: When<br />
you've got the preventative measures<br />
covered, look to technologies that will help<br />
you to detect, mitigate and protect against<br />
attacks. No preventative solution is 100 per<br />
cent effective, but with effective post<br />
compromise technologies you will get as<br />
close as is possible. Early detection will be<br />
important in avoiding some of the heftier<br />
fines that the GDPR threatens, and the less<br />
data that is exposed and the better your<br />
prevention and detection, the better it is for<br />
everyone. Don't get drawn in by allencompassing<br />
solutions (in anything other<br />
than reporting and dashboards). A<br />
carpenter doesn't carry one tool with all the<br />
attachments they need.<br />
Other Regulations: Use all the<br />
regulatory requirements with security<br />
concerns published, even if they don't<br />
specifically apply to your organisation.<br />
They can often provide good frameworks<br />
to shape your approach and will help you<br />
focus on the gaps.<br />
Be Honest: Review your security honestly.<br />
If you don't have the skills then use external<br />
resources to test your security and engage<br />
your local hacking community to help you<br />
craft better defences and detection. The<br />
only failure in IT security is in thinking that<br />
you've done it.<br />
In essence the GDPR doesn't demand that<br />
you do anything you shouldn't already be<br />
doing. It makes sure that those who haven't<br />
taken necessary precautions, or haven't<br />
been open about being breached, are held<br />
accountable. Having just one DP regulation<br />
for the entire EU, as opposed to the 28<br />
current sets, will undoubtedly be easier to<br />
comply with. The fines are scary, but we<br />
should welcome the simplification. NC<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
JULY/AUGUST 2016 NETWORKcomputing 13
FEATUREGDPR<br />
THE NAC OF GDPR<br />
READINESS<br />
What role might existing<br />
technology play as the GDPR<br />
unfolds? Paul Donovan of Pulse<br />
Secure considers how NAC can<br />
help to protect corporate data<br />
and help compliance with the<br />
new legislation<br />
There is a distinct lack of official guidance<br />
for organisations who should be<br />
preparing for the GDPR, but with the<br />
potential threat of huge fines organisations<br />
can't wait and must act now. Regardless of<br />
your industry sector, you need to ensure that<br />
your organisation's data is secure, both on<br />
and off-premise. Policies such as BYOD and<br />
remote working can make securing data more<br />
complicated, which has resulted in a<br />
resurgence of interest in Network Access<br />
Control (NAC). No one knows what GDPRcompliance<br />
looks like yet, but securing access<br />
to the network is the first step to securing<br />
access to data, and thus aligning your<br />
organisation with the sentiment of the GDPR.<br />
MARKET FORCES<br />
With new collaborative working practices and<br />
the prevalence of BYOD and remote working,<br />
controlling access to the network has become<br />
increasingly complicated which, in turn,<br />
means that protecting the data both on and<br />
off premise is itself more complicated.<br />
Nowadays, employees expect to be able to<br />
work from home, bring their own devices to<br />
work and even connect other personal<br />
devices to corporate Wi-Fi.<br />
In addition to BYOD, the Internet of Things<br />
(IoT) and cloud applications mean that there<br />
are more endpoints, all with distinct<br />
operating systems and all accessing the<br />
network, than ever before.<br />
As well as being able to connect offpremise,<br />
employees also expect to be able to<br />
connect from a point in the building other<br />
than their allocated desk. For example, if they<br />
are hosting a meeting with partners, they will<br />
expect for themselves and their visitors to<br />
seamlessly connect to the network.<br />
TODAY'S NAC SOLUTIONS<br />
All of these elements present a huge threat<br />
to the security of an organisation's data and<br />
they articulate what's putting NAC back on<br />
the agenda. A 2014 ESG research report on<br />
network security claimed that 40 per cent of<br />
organisations were enforcing NAC<br />
"extensively across the enterprise," and an<br />
additional 44 per cent using NAC to a<br />
lesser degree.<br />
Previously, NAC was overly complicated and<br />
expensive but technological advances make it<br />
a much more attractive proposition today.<br />
NAC solutions now give the IT department<br />
much more control to grant access based on<br />
contextual information (e.g. user ID, role,<br />
device type, security posture, location). This<br />
kind of visibility and control effectively means<br />
that only authorised employees have access<br />
to corporate data depending on their role,<br />
location, and even the time of day.<br />
THE RISE OF DATA BREACHES<br />
A Frost & Sullivan report last year expected<br />
NAC revenues to more than double from<br />
$552.8 million in 2014 to $1.46 billion by<br />
2018 and it suggests the resurgence of<br />
NAC is very much underway. This<br />
expectation could be because the increasing<br />
number of data breaches has put network<br />
access on the boardroom agenda as well as<br />
IT departments.<br />
Recent research from IBM and The<br />
Ponemon Institute claims that the<br />
organisational cost of a data breach has<br />
increased from £2.37 million in 2015 to<br />
£2.53 million in 2016. This is due to a<br />
combination of resources that are deployed<br />
to deal with the breach and the reputational<br />
and customer losses which directly impact on<br />
an organisation's bottom line. With the<br />
impending EU GDPR, this cost could<br />
potentially increase to include a fine based<br />
on global annual turnover.<br />
While the fallout from the GDPR remains<br />
unclear, the ability to prevent devices or<br />
users without the right credentials from<br />
accessing the network, regardless of where<br />
they are, illustrates to the Information<br />
Commisoner's Office (ICO) that an<br />
organisation is taking its data security<br />
seriously. Of course, a breach may still occur<br />
as it's impossible to account for all<br />
eventualities, but having policies, processes<br />
and technologies in place, sponsored by<br />
senior management, will help should the<br />
worst happen. NC<br />
14 NETWORKcomputing JULY/AUGUST 2016 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
PRODUCTREVIEW<br />
Unified Security<br />
Service from<br />
CensorNet<br />
PRODUCT REVIEW<br />
PRODUCT<br />
REVIEWPRODUCT RE<br />
Companies depending on web and<br />
cloud applications for their business<br />
operations are going to have to<br />
rethink their security strategies. Despite the<br />
range of solutions available on the market,<br />
few currently offer the level of control required<br />
to keep users and data safe, while still<br />
allowing them to efficiently do their jobs.<br />
The Unified Security Service (USS) from<br />
CensorNet offers a sophisticated approach<br />
providing real-time discovery, analysis and<br />
control for a huge range of web and cloud<br />
applications. USS also provides<br />
comprehensive URL filtering and optional<br />
email protection, all easily managed from a<br />
single cloud portal.<br />
Deployment was simple as CensorNet<br />
agents for Windows and OS X can be<br />
downloaded directly from the portal. Prior to<br />
pushing them to test systems we created agent<br />
profiles that set details such as SSL<br />
interception, a captive portal for BYOD users<br />
and enforced password protection to stop<br />
agents being modified.<br />
For LAN protection the CensorNet USS<br />
Gateway component provides a web proxy<br />
based on Ubuntu 14.04. Delivered as an ISO<br />
file it runs on a physical or virtual server and<br />
for the latter supports hosts such as VMware,<br />
Hyper-V, VirtualBox and XenServer.<br />
We were able to swiftly deploy proxy settings<br />
using methods such as Group Policy, default<br />
gateway or WPAD (web proxy auto-detection).<br />
The SSL Interception feature requires that a<br />
root CA certificate be installed onto each<br />
system. It can be downloaded from the<br />
gateway but installation is automatic when a<br />
windows agent is deployed.<br />
The USS web portal opens with a<br />
customisable dashboard offering a complete<br />
graphical overview of all web and application<br />
activity. We added graphs and charts to show<br />
the top domains and cloud applications being<br />
accessed, along with blocked domains plus<br />
general web browsing activity, and we could<br />
change the views for each one to display<br />
different time periods.<br />
Web and cloud application activity is<br />
monitored and controlled using policies.<br />
These employ the CensorNet rules engine<br />
which uses types, conditions, logic and actions<br />
to determine whether an activity is permitted.<br />
This makes USS highly flexible as policies can<br />
be applied to Active Directory OUs, security<br />
groups and users, devices and groups, device<br />
types such as PCs, smartphones and<br />
wearables, and also time periods. For web<br />
browsing control USS offers over 140<br />
categories to choose from, while the cloud<br />
application list includes 30 classes with<br />
multiple activities within each one.<br />
We tested with a range of cloud applications<br />
including LinkedIn, Facebook, Twitter, Gmail,<br />
Dropbox, OneDrive, Google Drive, Google<br />
Apps plus WebEx and were bowled over by<br />
the level of control available. Look no further<br />
if you want total Facebook control, as USS<br />
can identify 113 different activities such as<br />
joining groups, editing profiles, sharing posts,<br />
unfriending, uploading files or creating pages.<br />
The reports tab provides an incredible amount<br />
of information about web and cloud<br />
application usage as each entry showed us<br />
precisely what our users were doing, along<br />
with links to web sites being accessed. For<br />
Gmail, we could see when users logged in,<br />
who they emailed, if they read or trashed<br />
emails and the action that USS applied to<br />
activities.<br />
MSPs will like USS as its Partners feature<br />
allows them to create customer accounts and<br />
provide various levels of access by defining<br />
roles by account. Message protection also<br />
comes under its remit and the CensorNet<br />
Email Security cloud solution provides antispam,<br />
anti-virus, anti-phishing and content<br />
filtering, which can be managed directly from<br />
the USS web portal.<br />
CensorNet USS impressed us hugely during<br />
testing. It offers a remarkable insight into web<br />
and cloud application usage within the<br />
workplace, is very easy to manage, and its<br />
versatile policies and rules engine deliver the<br />
granular controls that today's cloud-savvy<br />
businesses urgently need. NC<br />
Product: Unified Security Service<br />
Supplier: CensorNet<br />
Web site: www.censornet.com<br />
Phone: +44 (0)845 230 9590<br />
Email: marketing@censornet.com<br />
Price: Per user per year subscription<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
JULY/AUGUST 2016 NETWORKcomputing 15
FEATUREGDPR<br />
PRIVACY BY DESIGN<br />
ROSS WOODHAM, DIRECTOR<br />
OF LEGAL AFFAIRS AND<br />
PRIVACY AT COGECO PEER 1<br />
EXPLAINS THE IMPORTANCE OF<br />
ADDRESSING PRIVACY AT THE<br />
DESIGN STAGE OF PRODUCTS<br />
AND SERVICES<br />
The General Data Protection Regulation<br />
(GDPR) is a positive development<br />
because its impact will help to lessen<br />
the tremendous damage that can be<br />
inflicted following a major cyber-attack. It<br />
may even help to disarm the vulnerability in<br />
the first place.<br />
Some IT departments may not be keen<br />
though, believing that the GDPR will place an<br />
onerous burden on them. They may also think<br />
that Brexit will let them off the hook. In reality<br />
though, and even with the news of the UK's<br />
exit from the EU, if we wish to continue to be a<br />
close trading partner with the EU then UK<br />
businesses will need to adopt a broadly<br />
similar framework of standards to protect the<br />
data of EU citizens, along with other EU<br />
trading partners such as the US and Canada.<br />
STANDARDISING DATA<br />
REQUIREMENTS<br />
The GDPR marks the beginning of widespread<br />
unification and standardisation of data privacy<br />
requirements both within the EU and arguably<br />
on an extra-territorial basis, at least in respect<br />
of EU citizens' data. Given that data is<br />
growing exponentially with the increasing use<br />
of big data, cloud, mobile and the Internet of<br />
Things applications, the challenges of<br />
managing, securing and processing<br />
information becomes ever more complex.<br />
Within this context and that of the GDPR, a<br />
privacy by design approach to new<br />
applications, platforms and services will help<br />
to focus on data management issues and<br />
benefit from these sensible requirements.<br />
EMBEDDING PROTECTION<br />
The concept of privacy by design is an<br />
approach that bakes privacy processes into<br />
the design specifications of technologies and<br />
other practices. For instance, a central GDPR<br />
requirement is establishing when it is<br />
appropriate to delete personal data - or<br />
equally only retaining information that is<br />
strictly necessary for a well-defined purpose.<br />
Such requirements should be factored into the<br />
design of the technology or system.<br />
The right to be forgotten is also a central<br />
tenet in the GDPR. It allows individuals a<br />
qualified right to request that their data be<br />
erased. Designing a system to enable you to<br />
manage data in this way will be essential to<br />
enabling compliance and avoiding<br />
cumbersome manual processes.<br />
THE FUTURE IS NOW<br />
Given that the lifecycle of new products and<br />
services can span several years, it makes<br />
sense to address privacy at the beginning of<br />
product and service development, rather than<br />
reactively retro-fitting to meet regulation.<br />
Organisations should start planning privacy<br />
requirements now because in 2018 they will<br />
be challenged by these rigorous obligations.<br />
In this way, as new products and services<br />
progressively move online over time,<br />
organisations will already be compliant<br />
when the GDPR takes hold. What's more,<br />
the privacy by design blueprint will already<br />
have been established and put into<br />
practice, making compliance a matter of<br />
routine and a critical operational element<br />
of business as usual.<br />
CLEAR BENEFITS<br />
In the US, there is a growing groundswell of<br />
strong public opinion demanding greater<br />
privacy and reacting to media coverage of<br />
government snooping. Some progressive US<br />
organisations understand that being ahead of<br />
the curve on these issues is good for business<br />
and are already incorporating the concept of<br />
differential privacy into their artificial<br />
intelligence endeavours. Their approach<br />
suggests that they will obscure big data results<br />
in order to mask individual inputs while still<br />
extracting useful information on larger trends.<br />
These instances are real life examples of the<br />
core principle of privacy by design which is at<br />
the heart of the GDPR.<br />
While on this side of the pond advances in<br />
privacy might be being driven initially by<br />
regulation rather than market forces, it is very<br />
likely that those organisations that take an<br />
active and responsible approach to secure<br />
their customer data will be rewarded with<br />
consumer favour, which will of course have<br />
positive implications for both reputation and<br />
revenue. NC<br />
16 NETWORKcomputing JULY/AUGUST 2016 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
FEATURETHE INTERNET OF THINGS<br />
THE IOT SECURITY<br />
CHALLENGE<br />
IOT DEPLOYMENT INCREASES<br />
THE POTENTIAL NETWORK<br />
ATTACK SURFACE. KATHY<br />
SCHNEIDER OF LEVEL 3<br />
COMMUNICATIONS SAYS<br />
THAT WE NEED TO ADDRESS<br />
THIS BEFORE ADOPTING IOT<br />
The Internet of Things (IoT) continues to<br />
generate debate and interest amongst<br />
businesses and consumers alike. Frost &<br />
Sullivan estimate that by 2020 there will be 80<br />
billion connected devices worldwide: IoT is set<br />
to transform our lives. However, this<br />
transformation requires careful management in<br />
order to arrive smoothly at our destination,<br />
and security is one of the most pertinent issues<br />
that those entrusted with this transformation<br />
must address.<br />
A few months ago, a non-malicious hack of a<br />
children's toy company proved that extracting<br />
photos and personal information from innocent<br />
consumers was possible. The hacker illustrated<br />
that the company was not secure and in turn<br />
sent all businesses a warning. This case - not<br />
the first of its kind - and related issues continue<br />
to make the news as the global IoT security<br />
challenge evolves and grows.<br />
As more devices become connected, the<br />
access perimeter, essentially the danger zone,<br />
widens. With millions of malware strains and<br />
thousands of new families of viruses identified<br />
each year, the old-fashioned trio of anti-virus<br />
software, a firewall and intrusion detection will<br />
simply not do.<br />
Enterprises tend to focus on Bring Your Own<br />
Device (BYOD) security in relation to mobile<br />
phones and tablets, but they must now also<br />
consider all other connected devices entering<br />
the work domain every day, as they provide<br />
effective doorways to their data. Such devices<br />
include increasingly popular fitness trackers as<br />
well as devices that exist on employee Wi-Fi<br />
networks at home and provide VPN access to<br />
the corporate server. They create security<br />
loopholes that are ripe for exploitation by<br />
malicious actors. According to a recent study<br />
from HP, 6 out of 10 IoT devices had common<br />
cyber-vulnerabilities and 70 per cent did not<br />
encrypt their internet communications.<br />
Security becomes an even bigger concern<br />
when one considers the volume of data<br />
collected by connected devices every day. To<br />
tackle this, a network-based security solution is<br />
required that establishes protection at the<br />
network perimeter. Businesses are then in the<br />
best position to mitigate threats from entering<br />
their network in the first place. Network-based<br />
security will not only simplify things for<br />
businesses, but the ability to manage security<br />
from a single viewpoint will lead them to<br />
financial savings as separate, software-based<br />
solutions will no longer be required. In short,<br />
enterprises will need a simplified, easy-toupdate<br />
ecosystem that provides a holistic view<br />
of their security posture.<br />
To start with, it is essential that organisations<br />
deploying IoT devices conduct rigorous<br />
analyses of built-in and external security<br />
controls for all connected devices and services<br />
currently in use and those planned.<br />
An audit of the following elements is a vital<br />
starting point, in securing any IoT connection:<br />
Communication channels<br />
Use of encryption<br />
Analysis of data collected, stored and<br />
transmitted<br />
Security of the communication endpoint(s)<br />
Given rapid IoT adoption and the broadening<br />
of the cyber-attack surface, organisations must<br />
be increasingly vigilant in conducting<br />
comprehensive risk analysis and implement<br />
proper governance structures. A risk-based<br />
approach is the best way to balance the<br />
challenges of using IoT with its impressive<br />
productivity benefits.<br />
Businesses must ensure that core networks are<br />
robust. Looking beyond security in the current<br />
computing environment, resource-intensive<br />
and internet-connected devices will also need<br />
virtualised servers and reliable cloud storage.<br />
Migration to these systems can incur its own<br />
security issues. However, in employing a<br />
network-based security approach, businesses<br />
should also be able to simplify this process.<br />
The great potential offered by IoT has been<br />
discussed at length, with businesses and<br />
consumers excited for what the future will bring.<br />
However, increased security concerns are valid<br />
and pressing, and no one wants to see their<br />
data compromised. A strong and secure<br />
network is paramount in supporting an effective<br />
and safe IoT environment. NC<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
JULY/AUGUST 2016 NETWORKcomputing 17
FEATURETHE INTERNET OF THINGS<br />
WITH GREAT<br />
DATA COMES…<br />
THE INTERNET OF THINGS<br />
PROMISES GREAT DATA, BUT IT<br />
ALSO BRINGS SUBSTANTIAL<br />
RESPONSIBILITY. LARRY<br />
AUGUSTIN, CEO OF<br />
SUGARCRM CONSIDERS THE<br />
WAY BUSINESSES UNDERSTAND<br />
AND SERVICE THEIR<br />
CONSUMERS<br />
When Samsung announced that it<br />
would be investing $1.2 billion into<br />
the Internet of Things (IoT), the tech<br />
world sat up and took notice. There has been<br />
a persistent buzz around IoT for years, with<br />
the showcasing of new IoT developments<br />
often the main attraction at the technology<br />
shows I attend, all year round. However,<br />
Samsung's news heralds the start of a<br />
revolution in the way devices interact with<br />
each other and how they generate<br />
meaningful customer data for businesses.<br />
The technology industry is thinking about the<br />
consumer in more detail than ever before, and<br />
it is finding innovative ways to integrate the<br />
daily routine with devices to create an<br />
interconnected world. The potential for<br />
businesses to amass a huge volume of<br />
consumer data is endless. But with great data<br />
comes great responsibility, and businesses<br />
must have robust security measures in place to<br />
avoid costly cybersecurity breaches.<br />
Cloud networks, infrastructure, applications<br />
and data need to be as secure as possible to<br />
make IoT a success. For global enterprises, the<br />
size and complexity of their customer data can<br />
be challenging to manage in the public cloud.<br />
Organisations should have the freedom to<br />
implement the systems and architectures that<br />
best address their needs for security,<br />
compliance, and data integration.<br />
Most cloud solutions are available only in<br />
proprietary, multi-tenant, shared<br />
infrastructure, single cloud configurations.<br />
There's little or no opportunity for companies<br />
to decide where they want their applications<br />
and data to reside. The options are many -<br />
public, and private, within your own country's<br />
borders, on-premise or a hybrid combination<br />
- but often, the only choice is the vendor's<br />
proprietary cloud.<br />
It isn't just consumer data that needs to be<br />
taken care of. The modern working world<br />
means that sensitive business and employee<br />
data now spans an ever-increasing number of<br />
devices. Modern CRM solutions can support<br />
these complex security requirements by<br />
providing a nimble and powerful service<br />
which allows businesses to thrive in a<br />
connected world.<br />
But of course, terabytes of data are only<br />
useful in the business world if you possess a<br />
means to make sense of them. CRM<br />
technology can form an important part of this<br />
sense-making process and its very powerful<br />
when deployed in support of an IoT network.<br />
The IoT offers huge potential for CRM<br />
platforms to build a single view of the<br />
customer and create a frictionless, positive,<br />
customer experience.<br />
We have already begun exploring how to<br />
integrate the IoT into our CRM technology.<br />
We worked with VetAdvisor, the US-based<br />
holistic care provider for military veterans, to<br />
integrate Fitbit bands into its CRM<br />
deployment. This enabled VetAdvisor to track<br />
veterans' progress towards personalised<br />
fitness goals and provide real-time coaching<br />
via SMS messaging.<br />
From geo-location insight to knowing what<br />
time the customer puts the heating on, IoT is<br />
capable of providing microscopic insight into<br />
consumers' lives. But the wealth of data is as<br />
overwhelming as it is exciting. A new channel<br />
means another level of customer expectation:<br />
they want to know that every touchpoint they<br />
have with a company is unified. Businesses<br />
must learn how to incorporate new channels<br />
of data into an already complex web.<br />
As the technology world looks to the future<br />
and the potential that the IoT holds, the need<br />
for businesses to maintain a secure<br />
infrastructure is set to increase, exponentially.<br />
Perhaps the future of IoT is best summed up<br />
by WP Hong, President of Solution Business<br />
Unit at Samsung, who stated in his keynote<br />
address at January's Las Vegas Consumer<br />
Electronics Show, "The age of the Internet of<br />
Things has begun. It will be a success, but<br />
only if we get the fundamentals right:<br />
openness, interoperability and close industry<br />
collaborations." NC<br />
18 NETWORKcomputing JULY/AUGUST 2016 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
FEATURETHE INTERNET OF THINGS<br />
AN IOT ECOSYSTEM<br />
RYAN LESTER, DIRECTOR OF IOT STRATEGY AT XIVELY<br />
OFFERS SOME PRACTICAL GUIDANCE FOR<br />
SUCCESSFULLY IMPLEMENTING IOT<br />
The Internet of Things (IoT) is an<br />
attractive proposition for many<br />
businesses. Making devices smart and<br />
connecting them to an ecosystem can<br />
provide large amounts of data that can be<br />
used to better understand customers and<br />
their product use, which can then drive<br />
development and marketing.<br />
Unfortunately it is not as simple as cobbling<br />
devices together into an existing network.<br />
There are a whole range of issues that need<br />
to be considered to ensure that both the<br />
business and its users achieve what they want<br />
from an investment in IoT. In fact, the<br />
complexity and number of considerations<br />
that need to be addressed means that going<br />
it alone can pose high risks and high costs to<br />
any business unfamiliar with the technology.<br />
Worst case, IoT can open up a business to<br />
network vulnerabilities that could result in<br />
loss of data, system functionality, customers<br />
and reputation.<br />
Even with partners in place, those looking to<br />
implement an IoT solution should be aware of<br />
how to proceed in a structured way. Indeed, it<br />
is necessary to ensure they are working hand<br />
in hand with their partners to ensure the best<br />
possible outcome. The following ideas could<br />
help to start in the right place.<br />
SECURITY AND IDENTITY<br />
MANAGEMENT<br />
Security is undoubtedly the biggest issue<br />
facing IoT - or any technology for that<br />
matter. Every device that is network<br />
connected provides a potential entry point<br />
for a cybercriminal. When thinking about<br />
IoT security, businesses should explore these<br />
three elements:<br />
The board. The<br />
physical security of the<br />
device: can it be<br />
tampered with?<br />
The wire. How are<br />
messages secured when<br />
transmitted across the<br />
network?<br />
The cloud. What<br />
authentication and<br />
identification procedures<br />
exist to control those who<br />
have access?<br />
MAINTAINING, UPGRADING<br />
AND GROWING<br />
Any network that is initially successful will<br />
need ongoing work to cope with new<br />
developments in technology, standards and<br />
threats, as well as connections from more<br />
and more devices. Both onboarding of new<br />
devices and network maintenance needs to<br />
be carefully managed around the clock to<br />
minimise user downtime, service interruption<br />
and productivity loss.<br />
DATA MANAGEMENT AND STORAGE<br />
The IoT is causing an explosion in the<br />
amount of data businesses need to store<br />
and manage. It is likely that devices will<br />
transmit data on a regular basis reporting on<br />
a whole range of variables and producing<br />
10s or even 100s of data points each day.<br />
Scale that by the number of devices that<br />
could be connected to the network and it<br />
could easily equate to terabytes of data. This<br />
information needs to be stored securely<br />
whether it's situated on premise or at a<br />
remote location. It must also be collated into<br />
useful data types so that it can be analysed<br />
and leveraged to create business value.<br />
STANDARDS<br />
As the IoT develops, so too will the<br />
standards and certifications that regulate<br />
devices, networks, and so on. These will<br />
help to improve interoperability while<br />
providing reassurance to consumers that<br />
their data is safe. Being aware of these<br />
developments and building them into the<br />
IoT infrastructure are important for longterm<br />
viability.<br />
However, in this new arena there are<br />
likely to be a number of competing<br />
standards, particularly in the short term.<br />
For instance, Google recently opensourced<br />
its Thread protocol, thereby taking<br />
a significant step to win the standards war.<br />
As such, knowing which standards are<br />
likely to succeed is also a significant factor,<br />
perhaps even an advantage.<br />
These are just some of the many<br />
considerations for those looking to<br />
implement an IoT solution. Whether<br />
working alone or with partners, it's<br />
important to get a firm grip on all of them<br />
if you really want to ensure a longstanding<br />
and successful IoT business<br />
advantage. NC<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
JULY/AUGUST 2016 NETWORKcomputing 19
OPINION<br />
BEYOND TODAY’S LIMIT<br />
NETWORK TESTING AND<br />
DIAGNOSTICS NEEDS A<br />
RETHINK AS ENGINEERS NEED<br />
GREATER VISIBILITY,<br />
ACCORDING TO TYSON<br />
SUPASATIT, PRODUCT<br />
MARKETING MANAGER AT<br />
EXTRAHOP<br />
Network testing and diagnostics is<br />
often thought of as a way to<br />
efficiently get packets from point A<br />
to point B. However, for the network<br />
engineer, it's not just about the delivery of<br />
packets, but efficient interaction between<br />
the network and its applications. After all,<br />
the network can deliver packets very<br />
quickly, only to encounter an overloaded<br />
server that cannot respond. For the user,<br />
there is no difference between network<br />
performance and application performance:<br />
the service is just slow.<br />
A better definition of network testing and<br />
diagnostics should take into account<br />
application behaviour. Efficient remediation<br />
of performance problems requires network<br />
engineers to understand not just how the<br />
network is delivering applications, but how<br />
those applications utilise the network:<br />
Are database backups conveniently<br />
scheduled?<br />
Is a logging script copying the same files<br />
and repeatedly transmitting them over<br />
the network?<br />
Are device DNS settings misconfigured,<br />
leading to waste and noise?<br />
What streaming media is running?<br />
To help answer such questions, network<br />
engineers require application-level detail to<br />
diagnose network saturation and understand<br />
usage. Traditional network testing and<br />
diagnostic tools provide analysis for Layer 2<br />
through Layer 4 but no visibility at Layer 7,<br />
where application detail resides. This<br />
information includes request messages,<br />
response messages, status codes, error<br />
messages, queries, methods, stored<br />
procedures, file names, login failures,<br />
certificates, URLs and more.<br />
Correlation of the information across the<br />
layers allows engineers to characterise the<br />
network's traffic profile and make datadriven<br />
decisions concerning adjustments to<br />
network settings, or if the network<br />
infrastructure requires an upgrade. Without<br />
this application-level visibility, money can be<br />
wasted purchasing new equipment to scale<br />
up to a demand that may not exist.<br />
Correlating network traffic from Layer 2<br />
through Layer 7 is no trivial task, especially<br />
at today's traffic speeds. Reliance on packet<br />
capture tools such as tcpdump to obtain<br />
application-level visibility used to be feasible<br />
when network speeds were measured in<br />
Mbps. This will not work today with<br />
enterprises looking toward 40 Gbps and<br />
100 Gbps services.<br />
Instead of using packet capture to analyse<br />
network traffic at rest, network testing and<br />
diagnosis solutions need to provide a<br />
stream analysis approach that reassembles<br />
packets into full transactions, flows, and<br />
sessions. With this full-stream reassembly,<br />
these solutions will be able to extract the<br />
details that are valuable to network<br />
engineers without having to store the<br />
packets and analyse them retrospectively.<br />
Storing metadata instead of full packets also<br />
provides network teams with visibility into<br />
historical traffic patterns, not just packet rates<br />
and throughput, but what applications those<br />
packets represent. This in turn facilitates<br />
better long-term capacity planning, which<br />
benefits the organisation in terms of costs<br />
and performance.<br />
Stream analysis would also by necessity<br />
require the reconstruction of the TCP<br />
endpoints for every client and receiver.<br />
Analysis of client-server interaction at Layer 4<br />
(TCP) would also reveal behaviours such as<br />
slow starts, receive window throttling, tiny<br />
grams and Nagle delays, which can be<br />
difficult to identify using traditional network<br />
testing and diagnostics tools. Network<br />
engineers need visibility of these metrics when<br />
deciding whether to turn on Nagle's algorithm<br />
or how to adjust the Maximum Transmission<br />
Unit (MTU) sizes on their core services.<br />
For those looking for a better way to carry<br />
out network testing and diagnostics, thinking<br />
about the task more broadly than just<br />
measuring bandwidth and latency is a start.<br />
Instead of just focusing on Layer 2 through<br />
Layer 4, consider the importance of what is<br />
happening at Layer 7 and its association with<br />
the end-user experience.<br />
A more holistic view of network activity will<br />
enable smarter decision making when<br />
optimising performance and planning capacity,<br />
ultimately resulting in better service to IT<br />
customers and the business they support. NC<br />
20 NETWORKcomputing JULY/AUGUST 2016 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
OPINION<br />
HYPER CRITICAL<br />
HYPER-CONVERGENCE IS GAINING TRACTION. SUSHANT RAO,<br />
DIRECTOR OF PRODUCT AND SOLUTIONS MARKETING AT<br />
DATACORE CONSIDERS ITS EFFECT ON STORAGE INFRASTRUCTURE<br />
There is a widespread growth of<br />
hyper-convergence taking place and<br />
it has led some vendors to opine<br />
that it is the cure-all that data centres<br />
have been waiting for. But while hyperconvergence<br />
sounds great it has its pros<br />
and cons, and IT professionals need to<br />
understand these if they are to really<br />
utilise its technologies and achieve<br />
optimal results.<br />
First, let's try and establish some<br />
definition of the term hyper-converged.<br />
Typically, hyper-converged technology<br />
takes separate tiers of compute, network<br />
and storage and combines them into a<br />
single tier. The storage is direct-attached<br />
to each node and software pools the<br />
storage of each node into shared<br />
storage. There is a virtualisation layer on<br />
each node so that the applications are<br />
running in VMs. The hyper-converged<br />
software can run in either the hypervisor<br />
or as a VM on top of the hypervisor.<br />
From a hardware perspective it's pretty<br />
simple. From a software perspective, it's<br />
more complicated.<br />
So what about the advantages? With<br />
just 2 or 3 nodes, hyper-convergence<br />
offers higher levels of availability<br />
compared to a small deployment of 2<br />
servers and shared storage, which is<br />
typically low-end and creates multiple<br />
single points of failure. By removing the<br />
low-end storage hardware and leveraging<br />
multiple nodes, hyper-converged can<br />
sustain a failure to one of the nodes but<br />
the applications will be able to recover.<br />
In Remote Office/Branch Office (ROBO)<br />
environments without dedicated IT staff<br />
this is a huge advantage.<br />
Another advantage is the ability to just<br />
add more nodes in order to scale, which<br />
makes sense for VDI. For example, a<br />
company may start with a pilot of 2<br />
hyper-converged nodes for 50 users. If<br />
they want to grow to 100 or 500 users,<br />
they will add 2 or 8 more nodes to<br />
handle the additional users. This makes it<br />
easy for IT.<br />
So far so good - but what about the<br />
disadvantages? The first is performance.<br />
You may think that having data on the<br />
same node as the application will<br />
increase both I/O and application<br />
performance, but this hasn't been proven.<br />
The best benchmark to measure I/O<br />
performance is available from the<br />
Storage Performance Council (SPC). The<br />
major storage vendors have run and<br />
published the benchmarks so that<br />
customers can compare the latency, IOPS<br />
and price of their products, but to date<br />
only one hyper-converged product has<br />
run the SPC benchmark. If you are<br />
expecting to quote major performance<br />
improvement figures by moving to hyperconverged<br />
then you may be disappointed.<br />
Another disadvantage is that hyperconverged<br />
offerings are typically 'walled<br />
gardens', meaning that when companies<br />
want to expand they can only use<br />
equipment from their hyper-converged<br />
vendor. There will be more options if their<br />
hyper-converged product is a software-only<br />
solution, as opposed to appliance based.<br />
Lastly, hyper-converged conflates<br />
storage and compute. This may seem<br />
obvious but it is worth addressing up<br />
front. Is your data growing at the same<br />
rate as your compute? For most<br />
companies the answer will be no. Data is<br />
mostly growing much faster than<br />
compute. When you go hyper-converged,<br />
you are taking a gamble that your data<br />
needs and your compute needs are<br />
roughly in line.<br />
Too many companies that have deployed<br />
hyper-converged realise they need to<br />
grow their storage capacity for additional<br />
data without growing their compute, and<br />
so quickly become stuck. It's much better<br />
to seek a software solution that offers the<br />
ability to scale storage capacity in a<br />
hyper-converged deployment that is<br />
independent of compute and can<br />
leverage your existing storage.<br />
In summary, hyper-converged makes sense<br />
for small environments or VDI. But if you<br />
need proven performance and you want to<br />
integrate with your existing environment, or<br />
you have data growth that outpaces your<br />
compute, then there are better ways to<br />
optimise your infrastructure. NC<br />
22 NETWORKcomputing JULY/AUGUST 2016 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
INTERVIEW<br />
INSIDE TRACK<br />
INSIDE<br />
INSIDE TRACK<br />
INSIDE TRACK - GETTING TO KNOW THE<br />
VENDORS…<br />
RAY SMYTH EXPLORED A NEW APPROACH TO AN OLD<br />
PROBLEM DURING A RECENT DISCUSSION WITH TIM<br />
LONSDALE, CEO OF SPEARSEC<br />
INSIDE TRACK<br />
In the fast moving and relatively young IT<br />
security sector it's reasonable to expect<br />
threat vectors to arrive, be remediated<br />
and usurped. When you add to this the<br />
evolution of technologies that prevent,<br />
thwart and remediate the attendant threats,<br />
you can see that things can change fast and<br />
often. This doesn't amount to a flawed<br />
conclusion but it does explain why one<br />
attack vector - Phishing - is all the more<br />
remarkable.<br />
Phishing used to be nothing more than a<br />
convenient term for the theft of information.<br />
But as a security threat vector, Phishing has<br />
evolved, expanding its scope, reach and, to<br />
those actors with malevolent intent, its<br />
usefulness and value.<br />
Tim Lonsdale is the CEO and main<br />
developer of a new to market company,<br />
SpearSec. From the outset of our<br />
conversation Tim presented some interesting<br />
statistics, explaining that while technology<br />
can be considered highly effective at<br />
preventing Phishing attacks, 10 per cent of<br />
attacks succeed. While a 90 per cent<br />
success rate would be considered successful<br />
in many contexts, a Phishing campaign only<br />
needs one successful attack for it to triumph.<br />
Tim explained that Phishing is now<br />
considered a gateway attack vector, and<br />
therefore not an end in itself. With the initial<br />
breach complete, it's not long before the<br />
attacker is moving laterally and assembling<br />
the means to facilitate deeper network<br />
penetration: this all too often leads to the<br />
launch of a Ransomware attack. Such an<br />
attack can totally disable business<br />
operations in an instant, and without some<br />
specialised recovery capability in place the<br />
only option is to pay the ransom. And<br />
remember, this happens because just one<br />
human being clicked on, for example, a<br />
phishing email link.<br />
Focused on those attacks that technology<br />
does not prevent, SpearSec has created a<br />
service that aims to challenge and train<br />
employees in a realistic but totally safe way.<br />
Tim explains, "We decided to build a service<br />
that could engage safely with users while at<br />
the same time expose them to a range of<br />
realistic Phishing attacks, in real-time and<br />
critically, on a continuous basis." This<br />
approach is in sharp contrast to more<br />
formal training. Tim adds, "It is live training<br />
delivered as needed. Clicking a safe link<br />
means that our service can present some<br />
quick, relevant, and highly effective training<br />
so that users can understand what they did<br />
wrong and the alternatives." Clearly, this is<br />
about changing behaviour.<br />
It is commonly accepted that in a<br />
successful cyberattack, regardless of vector,<br />
the success will have been assisted by, if not<br />
caused by, the action of a human being. Tim<br />
says, "Technology alone cannot address<br />
everything - we need to change the culture<br />
and help users to learn and change their<br />
behaviour in a safe, non-threatening<br />
environment."<br />
As well as delivering relevant in the<br />
moment training, the SpearSec service is<br />
building a profile so that a company can<br />
measure its vulnerability to Phishing, its<br />
progress in reducing that risk and activity<br />
trends. In the case that an individual or<br />
group are showing an unacceptably high<br />
level of risk, a more focused and constructive<br />
training response can be crafted.<br />
As you can see this response is targeted at<br />
people not technology and it is clear to see<br />
its potential to drive significant cultural<br />
reform because HR, departmental<br />
managers, suppliers and staff will all<br />
understand the power of working together in<br />
this way. The SpearSec approach enables<br />
people to experience a range of highly<br />
specific Phishing attacks without the risk,<br />
augmented by timely, specific training to<br />
change human behaviour and create the<br />
correct human reflex. The bold claim is that<br />
in this way 100 per cent of Phishing attacks<br />
can be blocked. NC<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
JULY/AUGUST 2016 NETWORKcomputing 23
OPINION<br />
TAMING DARK DATA<br />
MANAGING DATA IS A<br />
GROWING CHALLENGE AND<br />
THE SPECTRE OF DARK DATA IS<br />
PARTICULARLY TROUBLING.<br />
JULIAN COOK, DIRECTOR OF<br />
UK BUSINESS AT M-FILES<br />
EXPLAINS HOW ECM CAN HELP<br />
With ongoing digital<br />
transformation meaning that<br />
businesses are handling everincreasing<br />
volumes of documents and<br />
information, the issue of dark data is one<br />
that has becoming impossible to ignore. It<br />
poses a threat to compliance and<br />
business efficiency, if left unchecked. To<br />
tackle this problem, businesses need to<br />
develop the ability to identify and<br />
efficiently manage information through all<br />
phases of its lifecycle.<br />
The emergence of dark data has created<br />
a lot of debate amongst industry<br />
practitioners, and it is creating some<br />
significant challenges for organisations.<br />
Many have defined dark data as<br />
information assets that are created and<br />
used only once. While not wrong, it is a<br />
deeper issue than this definition would<br />
imply. Even content that is actively used<br />
for a period of time can turn into dark<br />
data when organisational and project<br />
priorities change, as they do. Active<br />
information that becomes inactive is<br />
typically left where it was last used and<br />
can be easily forgotten. To make matters<br />
worse, employees are resourceful and will<br />
often resort to recreating data when they<br />
can't quickly find their own copy. This<br />
process of duplication and recreation<br />
multiplies the incremental volume of data<br />
that can subsequently become dark.<br />
Without active management, such<br />
information can negatively impact<br />
business productivity. Employees waste<br />
excessive amounts of time searching for<br />
misplaced or lost information and this in<br />
turn reduces the quality of their work, and<br />
it can contribute towards an organisation<br />
not fulfilling its potential. In addition, the<br />
current business climate requires thorough<br />
and accurate record keeping and the<br />
requirement to produce evidence for<br />
quality control, compliance, legal actions,<br />
risk mitigation and many other purposes is<br />
only likely to increase.<br />
In order to address this, businesses need<br />
to develop the ability to identify and<br />
efficiently manage information at all<br />
phases of its lifecycle. Some proactive<br />
businesses are doing this by deploying an<br />
enterprise content management (ECM)<br />
solution.<br />
These solutions can help to simplify the<br />
classification and identification of dark<br />
data as opposed to active information<br />
assets. ECM systems enable content to be<br />
managed in a manner which enables it to<br />
be accessed and synchronised between<br />
various systems and devices, without the<br />
duplication of files. In this way,<br />
information is not tethered to a specific<br />
location and as a result it is freed from<br />
the traditional confines of applications,<br />
platforms, and information silos.<br />
Some information should go dark once it<br />
has served its purpose. With an ECM<br />
solution in place, documents and data<br />
can be archived appropriately based on<br />
selected retention rules. This helps to<br />
simplify future discovery requests while<br />
ensuring that information is stored and<br />
processed based on predetermined<br />
document lifecycle management policies.<br />
The identification of legitimate dark data<br />
also allows it to only remain visible to<br />
authorised individuals. For example, if an<br />
information asset contains sensitive<br />
information about employees or<br />
confidential activity then it can be<br />
protected using access control.<br />
ECM solutions essentially inject more<br />
intelligence into a company's data and<br />
ensure that the right content is in the right<br />
hands, at the right time. In turn this<br />
enables organisations to focus on using<br />
information to drive business growth,<br />
value, and innovation.<br />
In an increasingly digital age, it is<br />
crucial that companies maintain a strong<br />
grip on their data, for efficiency,<br />
productivity as well as for regulatory<br />
compliance. Deploying an enterprise<br />
content management system can be the<br />
answer to the dark data predicament<br />
many companies will increasingly face.<br />
The business benefits and saved time<br />
quickly add up: decision makers can<br />
achieve better results as they are able to<br />
find and use relevant information, and<br />
productivity goes up for employees, since<br />
everyone will spend less time searching<br />
for misplaced information. NC<br />
24 NETWORKcomputing JULY/AUGUST 2016 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
OPINION<br />
ASLEEP AT THE WHEEL<br />
WITH A FEW EXCEPTIONS, TELECOMS FIRMS HAVE BEEN<br />
SLOW TO ADDRESS THE IOT BUSINESS OPPORTUNITY, IN<br />
PARTICULAR THE RESULTING DATA ANALYTICS AND<br />
CUSTOMER INSIGHT, ACCORDING TO HOMAN HAGHIGHI,<br />
MANAGING DIRECTOR AT ALSBRIDGE<br />
At a recent investor briefing I<br />
attended, a major global telecoms<br />
firm expounded on its expertise in<br />
the cloud and detailed its plans related to<br />
mobile platforms. Conspicuously absent<br />
though was any reference to the Internet<br />
of Things (IoT), and in particular a vision<br />
for leveraging the significant business<br />
opportunity it presents.<br />
The omission was characteristic of a<br />
general industry malaise. Many carriers<br />
seem to assume that their role in IoT is to<br />
provide the connectivity for the IoT<br />
devices to communicate. The trouble is<br />
that the revenue arising from this<br />
connectivity will quickly erode into a<br />
commodity offering of very little value.<br />
Knowledge, meanwhile, is power and<br />
the real value of IoT lies in mining the<br />
data it generates, especially where<br />
devices are used by consumers. Consider<br />
the Tesla, which gleans data on a driver's<br />
taste in music and places visited; this is of<br />
value to media, holiday, traffic and<br />
insurance companies. Or the smart home<br />
that collects information on everything<br />
from what people cook for dinner to what<br />
they watch on television. Businesses are<br />
seeking, and willing to pay for, access to<br />
the data that can yield detailed insight<br />
into consumer behaviour. From this<br />
insight, they can develop compelling,<br />
bespoke and individualised services. This<br />
will be the battleground of the future as<br />
retailers seek to increase the wallet share<br />
of their consumers.<br />
To compete effectively in the big data<br />
space, telecoms companies need to play a<br />
role at that end-device level of customer<br />
interaction. Consider Vodafone, one of the<br />
few telecoms innovators in the space, and<br />
its data logging devices that can, among<br />
other things, monitor the electricity meter<br />
in a home. Vodafone's utility customers<br />
benefit by monitoring temperature and<br />
usage and eliminating the need to send<br />
meter-readers to customer premises.<br />
Vodafone, meanwhile, gains a critical and<br />
valuable data collection foothold within<br />
the utility's business operations and the<br />
consumer's home.<br />
While the opportunity is immense, so too<br />
are the challenges, especially those of<br />
managing the IoT supply chain: specifically<br />
security, reliability and control. No one<br />
wants their car to be hacked and privacy<br />
issues in the home are a real concern. More<br />
ominously, the growth of smart power grids<br />
expands the potential vulnerability points<br />
from electricity substations to far-reaching<br />
connected power networks, raising fears of<br />
catastrophic, prolonged power outages<br />
resulting from cyber terrorism. Fear of<br />
hacking and breaches are a major obstacle<br />
to the accelerated use of IoT devices.<br />
Telecoms firms can play a leading role in<br />
addressing IoT security challenges. By<br />
virtue of their traditional expertise in<br />
managing communication touchpoints and<br />
overseeing networks, they are well<br />
positioned to identify where breaches might<br />
occur and can take appropriate action.<br />
Another area concerns enhancing<br />
standards to enable seamless<br />
communication across different types of<br />
devices. At present, a smart home's stereo<br />
system typically can't communicate with<br />
the heat sensors or the fire alarm or the<br />
surveillance camera, as all these devices<br />
are made by different manufacturers using<br />
different standards. This lack of<br />
standardisation leads to consumer<br />
confusion as well as reluctance to<br />
commit. Again, the heritage of telecoms<br />
firms in driving communication protocols<br />
and integrating disparate data types can<br />
be brought to bear.<br />
To succeed, simply providing internet<br />
connectivity and deferring to manufacturers<br />
to build the smart devices just won't do.<br />
Telecoms firms must coordinate and<br />
develop and drive standards as well as<br />
being involved in developing the<br />
communication protocols for the IoT<br />
devices. Through that involvement, they<br />
can play a role in defining the standards<br />
that can drive deployment. The alternative<br />
is to lose control and become a commodity<br />
player as opposed to a leader in the<br />
connected world. NC<br />
26 NETWORKcomputing JULY/AUGUST 2016 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
MASTERCLASS<br />
The Network Computing Masterclass series…<br />
… GOING BEYOND TECHNOLOGY AND PRODUCT.<br />
THIS MASTERCLASS SERIES IS IN ASSOCIATION WITH CERTES<br />
NETWORKS. IN THIS EDITION THEY EXPLORE THE CHALLENGE OF<br />
OVERCOMING SEGMENTATION FRAGMENTATION WHEN ENABLING<br />
BORDERLESS APPLICATIONS.<br />
Every organisation has sensitive and<br />
confidential data to protect, from<br />
patient data kept by hospitals, to credit<br />
card data stored by retailers: no one can<br />
risk compromise. Worst still, it seems that no<br />
organisation is immune from being the next<br />
data breach victim, and governments that<br />
recognise this are investing heavily to<br />
protect vital services and infrastructure.<br />
Traditional security technologies just aren't<br />
enough anymore. Simply put, the security<br />
perimeter has all but eroded, and all of the<br />
other aspects of network segmentation<br />
focus too heavily on infrastructure, which<br />
impedes day-to-day business. More<br />
importantly, managing these complex<br />
security environments introduces a new<br />
layer of risk. After all, week after week, the<br />
world watches hackers infiltrate government<br />
agencies, corporate retailers and healthcare<br />
providers, proof if it were needed that<br />
traditional data and application security<br />
strategies alone cannot prevent breach.<br />
This is not just presenting security<br />
challenges but segmentation challenges<br />
also, as sensitive data is regularly shared<br />
everywhere and anywhere, especially<br />
beyond the perimeter. One approach in<br />
particular that is failing badly is traditional<br />
segmentation. The outdated segmentation<br />
tool of the firewalled perimeter is entirely<br />
obsolete as hackers exploit gaps and stolen<br />
credentials to bypass it with ease. Siloed,<br />
perimeter-based, infrastructure-dependent,<br />
fragmented segmentation tools are just<br />
complex webs that complicate risk, not<br />
mitigate it.<br />
What is needed is a complete reboot of<br />
segmentation and adoption of a nextgeneration<br />
IT security model that is easy to<br />
manage: one that is fit for the 21st century<br />
borderless digital business.<br />
ENTER CRYPTOGRAPHIC<br />
SEGMENTATION<br />
Cryptographic segmentation establishes<br />
segmentation lines around applications, not<br />
network devices and grants user access<br />
based on business-centric policies. In<br />
essence, it protects application traffic by<br />
taking a business-centric approach to<br />
network segmentation, using strong<br />
cryptography alongside user role-based<br />
access controls. With a software-defined<br />
approach to application security, enterprises<br />
can protect that which really matters:<br />
mission-critical, sensitive data.<br />
With cryptographic segmentation,<br />
networked applications are protected in<br />
virtual application overlays, which are<br />
cryptographically isolated using logical,<br />
policy-driven segmentation controls - and<br />
each virtual segment is only accessible with<br />
a user assigned key. In other words,<br />
employee and partner roles combined with<br />
business policies determine access. This<br />
means that cryptographic segmentation<br />
stops hackers from moving laterally even if<br />
one device, credential or staff member is<br />
compromised.<br />
In this way, cybercriminals will not be able<br />
to move to other networks or applications<br />
because access will not be granted to any<br />
additional virtual segments, limiting<br />
damage by default.<br />
THE LAST LINE OF DEFENCE<br />
Cryptographic segmentation is the last line<br />
of defence in many cases, but in theory it<br />
could have prevented the biggest data<br />
breaches of recent years including Ashley<br />
Madison, the Office of Personnel<br />
Management, JPMorgan Chase and<br />
Anthem. This approach to network<br />
segmentation is essential for frictionless<br />
enterprises that take advantage of, even rely<br />
upon, the cloud, mobile technology and<br />
big data. This is especially so when<br />
considering the number of threats that<br />
businesses face when connecting internal<br />
systems to the public Internet.<br />
A NEW MINDSET<br />
Cryptographic segmentation requires a new<br />
way of thinking. While organisations have<br />
worked hard at creating robust security<br />
strategies, with security experts across the<br />
globe now recommending a containment<br />
policy based on clearly defined<br />
infrastructure segments, it is clearly time to<br />
change. However, those organisations<br />
simply opting to impose segmentation at the<br />
network level are failing to recognise the<br />
true threat landscape; a reliance on network<br />
based controls will add, not mitigate, risk. It<br />
is simply too easy to bypass the controls.<br />
It is only by following a user and<br />
application based cryptographic<br />
segmentation approach that an<br />
organisation can address the heart of this<br />
threat. With the breach firmly contained<br />
within one specific segment, a system wide<br />
disaster is confidently avoided. NC<br />
This is the last in the current series of the<br />
Certes Networks Masterclass.<br />
Any reader comments and questions<br />
relating to this series should be addressed<br />
to Ray.Smyth@BTC.co.uk<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
JULY/AUGUST 2016 27<br />
NETWORKcomputing
FOCUSINFOSECURITY 2016<br />
INFOSEC: WHAT NEXT?<br />
WITH INFOSECURITY 2016 NOW FIRMLY IN THE PAST, WHERE SHOULD PROFESSIONAL VISITORS BE<br />
ENGAGING THEIR MINDS? OUR EDITOR, RAY SMYTH, OFFERS A VIEW - WITH THE HELP OF SOME<br />
KEY VENDORS<br />
Often there is a lot of media noise before a trade show but what about after? I am<br />
interested in what security professionals will do after this year's Infosec, and so I went<br />
in search of some vendors who might be able to shape the thinking, action and evolution<br />
that a show like Infosec should provoke in anyone creating a defensible security posture.<br />
SIZE DOES NOT MATTER<br />
In ICT security, size definitely does not matter: small organisations need similar protection to<br />
their larger counterparts and there is a credible range of solutions available from the smallest<br />
to the largest vendors. What does matter is accurately understanding exactly what defences<br />
your organisation requires and finding the best way to effectively deliver and manage them.<br />
BUSINESS DRIVEN SECURITY<br />
With an unlimited budget you may be tempted to buy one of everything, just to be sure. Two<br />
things are certain: there would still be vulnerability in your system and you would have wasted<br />
a lot of money. Amit Ashbel works for Checkmarx and describes himself as a Technology<br />
Evangelist. He starts us off by saying that "While it all depends on the services you provide as<br />
a business, a generic information security framework should start by considering how to prevent<br />
security incidents, how to protect your assets in the face of attack and then how to remediate<br />
and minimise breach impact." So a mantra of Prevent, Protect, Detect and Remediate in<br />
your business context sounds compelling doesn't it?<br />
APPLICATIONS BOLTED DOWN<br />
There is it seems to me evidence that organisations are increasingly adopting a more proactive<br />
approach to the security challenge, having realised that a reactive stance won't even close<br />
the door after the horse is bolted, such is the speed and severity of the current threat. Amit<br />
continues, "It all starts by knowing where the sensitive assets you hold are held and the level of<br />
risk they are exposed to." For example a financial organisation delivering online banking has<br />
sensitive assets which include customer data and of course money, so clearly both the web<br />
and mobile access channels should be built and maintained securely. Amit says that, "The<br />
most prominent category concentrating on prevention of attacks is Application Security<br />
(AppSec) which breaks down into multiple categories. For example, SAST (Static Application<br />
Security Testing) and DAST (Dynamic Application Security Testing) are at the core of AppSec<br />
and they should be included in every organisation's security framework."<br />
THE END OF CAT AND MOUSE<br />
Beyond the acknowledgment of a basic framework there is the ever changing risk profile and<br />
this is driven by the ease (perceived and actual) with which the average cybercriminal can<br />
maximise their success rate. The seminar topics at Infosecurity provided an insight with topics<br />
including ransomware, employee education, risk management and vulnerabilities in applications,<br />
devices and the network. But Guy Caspi, CEO at Deep Instinct noticed that, "A common<br />
28 NETWORKcomputing JULY/AUGUST 2016 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
FOCUSINFOSECURITY 2016<br />
thread ran throughout the entire event: the constant cat and mouse game of catching up with<br />
the latest malware and zero-day exploits." Sound familiar?<br />
Protecting against the millions of new malware variants launched daily seems like a pointless<br />
and unwinnable way to credible security, but once you realise that most of these malware variants<br />
are tiny mutations of pre-existing malware, perhaps some traction can be made. Guy<br />
says, "Despite this fact, currently available solutions, even the advanced ones which use<br />
dynamic analysis and traditional machine learning, have great difficulty detecting a large portion<br />
of the new malware, especially in real-time."<br />
It is in this context that I am noticing a new breed of solution that augment existing security<br />
elements such as the firewall, AV, IDP etc. Artificial intelligence and machine learning are<br />
terms that are coyly referred and even the marketing professionals seem to be practising caution.<br />
Guy Caspi explains, "Deep learning is an advanced form of artificial intelligence, also<br />
known as deep neural networks. It is the first family of algorithms within machine learning that<br />
do not require manual feature engineering and instead learn by processing and learning from<br />
raw data, similar to how our brain learns. This groundbreaking capability has become available<br />
thanks to major algorithmic improvements and their implementation on graphical processing<br />
units (GPUs), which provide tremendously enhanced computational capabilities."<br />
It seems to me that such an approach focuses heavily on behavioural traits as opposed to<br />
identifying features, such as signature definitions. This seems to make good sense and identifying<br />
elements of behaviour that seem suspicious or aberrant helps to focus rare talent and limited<br />
resources in the right area.<br />
CONNECTED IGNORANCE<br />
Another important driver of security design is determined by business use and related connectivity<br />
trends, so we simply cannot overlook the Internet of Things. Portnox CEO Ofer Amitai<br />
thinks that "IoT security was quite rightly a hot topic for Infosec 2016. Where there is confusion,<br />
there is talk, and there's certainly a lot of confusion regarding IoT: what is it, do I have<br />
IoT devices connected, device authentication and device security."<br />
Provisioning of network devices has become so easy that users can do it for themselves.<br />
Unfortunately this, combined with the potential scale of IoT connections, only escalates the<br />
risk. Remember, a malevolent actor only requires one point of access to build a highly profitable<br />
path to your assets.<br />
It's not necessarily the case that what is required is technically or intellectually challenging,<br />
and in many instances it will be more about awareness and the ability - and especially time -<br />
to respond. IoT devices generally fall into three categories: class 1, dumb devices, class 2,<br />
smart devices and class 3, which are server class devices. Ofer points out that "Not all IoT<br />
devices actually connect to the internet. They may communicate locally inside their own segment<br />
to a local server or with a cloud server and the risks stem from their architecture, so<br />
common security challenges must include device authentication and protection against a<br />
breached IoT device."<br />
And to avoid being too device centric, other risks include securing data in transit and at rest,<br />
and this will vary with device type and function. Ofer explains, "To authenticate IoT devices a<br />
profiling mechanism should be used. This means taking a digital picture of device properties<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
JULY/AUGUST 2016 NETWORKcomputing 29
FOCUSINFOSECURITY 2016<br />
and confirming that its properties are correct once connected. If it is not as expected you can<br />
alert or block that device. Other methods such as digital certificates are too complicated and<br />
resource demanding for IoT devices."<br />
Without doubt, IoT will bring new security challenges: for example, patching IoT devices.<br />
Ofer concludes that, "…to protect against a breached device, organisations should use VLAN<br />
assignment based on device type to create micro segmentation. This essentially splits where<br />
these IoT devices reside and therefore lowers the risk of a breach or its impact to a specific<br />
segment." One thing is certain - the IoT threat can be easily ignored, and it mustn't be.<br />
POWERED BY PEOPLE<br />
Traditionally trade shows have focused mainly on products and then solutions, but increasingly<br />
I see commentary on and problems pertaining to an emerging skills gap; a skills gap that<br />
might be influenced in some way by the UK Government's Brexit negotiations.<br />
While it is a sweeping generalisation, it seems to me that there is a viable technologybased<br />
solution available to tackle most known threats. Underpinning this is a wealth of<br />
knowledge and skill, but the resulting deficit increasingly looks like a skills shortage.<br />
Montana Williams, who is Senior Manager of Cybersecurity Practices at ISACA as well as a<br />
cyber-evangelist, reflects that, "One of the key points of interest for me at Infosecurity Europe<br />
was the evident gap between the practical security skills required and the skills available to<br />
the majority of IT teams." Something noticed by more than one person was the underlying<br />
theme that the basic difficulty is finding skilled people who are adequately trained in the<br />
evolving theatre of cyber security.<br />
If Brexit in any way affects the right of overseas residents to work in the UK, then the UK will<br />
surely have an unwelcome worsening of this skills shortage. But the underlying cause is likely<br />
to be much more fundamental. Montana notes, "The current skills shortage is not due to a<br />
lack of ambition or desire on the part of individuals. We are seeing a skills shortage due to a<br />
current training and educational system that prioritises the accumulation of knowledge and<br />
skills, rather than the experience and practice of these skills in the real world. This has resulted<br />
in a glut of people with vast theoretical grounding and plenty of initials after their names, but<br />
in reality, very little practical experience in operating, maintaining and defending complex integrated<br />
business systems." Well that's clear, credible, and a source of great concern…<br />
In offering a way forward, Montana summarises that, "There are four solutions that we continually<br />
discussed over the course of the three-day show." They are:<br />
Secondary School Education: teachers must be educated and able to integrate cybersecurity<br />
hands-on tools and theories into their lessons.<br />
External Youth Engagement: this must offer an extra-curricular level of education.<br />
Role Models: we need some heroes to inspire future generations.<br />
Post-Secondary Encouragement: the US schemes such as DHS/NSA Centres of Academic<br />
Excellence programmes develop skills through skills-based training and performancebased<br />
assessment.<br />
As serious as this problem seems to be, it, along with IoT devices can never be used as an<br />
excuse for increased risk or as a defence for a breach. Somehow, each professional will have<br />
to fix their own challenges, and these will be wide and varied.<br />
30 NETWORKcomputing JULY/AUGUST 2016 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
FOCUSINFOSECURITY 2016<br />
PHYSICIAN, HEAL THYSELF<br />
So, we got this far without talking about the insider threat. It's something that seems to have been<br />
around since the beginning, and of course it has been, as we are still talking about people: people<br />
with a heavy focus on the user community. Often I hear vendors go out of their way to<br />
explain that that the insider threat is not an implication that users are bad and should not be<br />
trusted, and this is true. Essentially it's a problem because people are human and fallible.<br />
Rui Melo Biscaia, Director of Product Management at Watchful Software comments, "Whether<br />
at Infosecurity or in the wider industry and media, the narrative of data security is still too caught<br />
up in the idea of external threats. While criminal gangs and bedroom hackers create a popular<br />
image for cyber threats, businesses must do more to get their own house in order before looking<br />
outward." Good data management should be at the heart of any security strategy and this<br />
means that you need to know where it is kept. Rui tells me that surprisingly large organisations<br />
are still unable to fully account for where key data is located or who can access it.<br />
With big data firmly on the boardroom replete with its promise of unique business advantage,<br />
there is going to be real pressure on IT professionals to deliver what is needed. According to<br />
Merrill Lynch more than 80 per cent of most organisation's data is unstructured, consisting of elements<br />
like email and user-created text files, and it is here that a data classification solution could<br />
enable organisation to automatically assess their unstructured data and assign a security classification<br />
based on predefined parameters.<br />
Rui explains that "Once the initial classification is complete, all other files are automatically classified<br />
at the point of creation, removing the chance of it being overlooked. Role-Based Access<br />
Controls (RBAC) are then used to ensure that only users who have been assigned access rights to<br />
a particular classification of file can view it, with encryption preventing access by unauthorised<br />
users. Additionally, files can be classified to various customised levels, for example, internal use<br />
only, files that cannot be moved or copied, or top secret files which can only be accessed by<br />
those with the highest clearance."<br />
It all requires a bit of effort and as can be clearly seen, these measures combine to make it difficult<br />
for both malicious insiders and external hackers to access and remove classified information.<br />
Rui concludes by saying, "There needs to be a stronger drive from the security industry to get<br />
organisations to focus on data management best practice, addressing the essentials before<br />
budgeting for advanced external security."<br />
TECHNOLOGY ALONE IS NOT THE ANSWER<br />
Because of the stakes (big money) cybercrime will grow and innovate at a rate that will continue<br />
to outstrip and challenge all organisations and individuals for the foreseeable future.<br />
Changing the locks and closing the windows alone will not be enough. Beyond the skills deficit<br />
referred to earlier, people must become a greater part of our future strength: they are part of<br />
the solution as well as part of the problem. Because of the skills gap a clinically focused and<br />
extremely tactical approach to the use of technology is essential. And if business needs change<br />
then you must make the case for what is needed - even if, on the face it, it seems like money is<br />
being wasted. There are no excuses.<br />
In the final analysis, don't be found wanting in the face of a successful threat. Listen to<br />
your conscience and make the case for what you know can work: you know it's what your<br />
business needs. NC<br />
32 NETWORKcomputing JULY/AUGUST 2016 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
PRODUCTREVIEW<br />
Titania PAWS Studio<br />
2.4.4<br />
PRODUCT REVIEW<br />
PRODUCT<br />
REVIEWPRODUCT RE<br />
SMBs that want to show compliance with<br />
data protection regulations will like<br />
Titania's PAWS Studio a lot. Capable of<br />
auditing any Windows or Linux system, it<br />
offers an impressive range of highly detailed<br />
compliance reports and all at a very<br />
affordable price.<br />
With costs as low as £2 per device, it beats<br />
most enterprise solutions hands-down for<br />
value. PAWS Studio doesn't compromise on<br />
features either, as it comes with predefined<br />
policies for all the major compliance<br />
regulations and provides a policy editor,<br />
so you can easily create your own.<br />
The latest version introduces a range of new<br />
features with existing policies for PCI-DSS,<br />
SANS, NSA, NERC and STIG, complimented<br />
with two extra ones for OVAL (Open<br />
Vulnerability and Assessment Language).<br />
These are important, as they give PAWS<br />
Studio new powers to scan for system<br />
vulnerabilities, as well as compliance.<br />
Titania has added a converter tool, so<br />
you can download the latest DISA STIG<br />
compliance files and OVAL vulnerability<br />
repositories, and update PAWS Studio<br />
with them. There's more, as the new<br />
configuration report provides detailed<br />
hardware and software inventory for each<br />
audited system.<br />
The PAWS Studio console also gets a<br />
design refresh, making it even easier to<br />
create and run audits. The first step is to<br />
choose local and remote target systems, and<br />
options are provided to manually add a<br />
device, run a network discovery routine or<br />
scan an IP address range. We could select<br />
single or multiple systems from the list and<br />
apply a set of universal authentication<br />
credentials. The next step is to choose any or<br />
all available reports and leave PAWS Studio<br />
to generate them.<br />
Leaving no footprint, it pushes a Data<br />
Collector to each system, which gathers the<br />
requested information and sends it back to<br />
the host for report creation. You can also<br />
export the Data Collector tool, along with the<br />
required audit policies, run it directly on a<br />
system and import the results back into the<br />
PAWS Studio host.<br />
Along with our Windows 7 host, we ran<br />
audits of the lab's Windows Server 2012 R2<br />
domain controller, plus Exchange 2013 and<br />
SQL Server 2014 hosts. Report generation is<br />
fast, with a combined NSA, PCI-DSS and<br />
OVAL audit on our Exchange 2013 system<br />
taking a mere 12 seconds.<br />
On completion, PAWS Studio displayed the<br />
report for our approval, which can then be<br />
saved in a variety of formats, including HTML<br />
and PDF. The viewer also provides tools to<br />
customise the report where we could change<br />
the title, add our company logo, decide<br />
which files to display and then regenerate it.<br />
The reports are highly detailed and the<br />
information presented is very accessible.<br />
They provide clear descriptions and impact<br />
assessments for each compliance check, so<br />
widening their appeal from technician to<br />
board member. We could see clearly which<br />
compliance checks had failed and the<br />
reports provided sage advice on remedial<br />
action. User access security is always a<br />
critical area and, for our AD controller, we<br />
could view the status of all domain accounts,<br />
password policies etc., and see those that<br />
needed action.<br />
Windows update and patch status are<br />
checked and verified, along with the status of<br />
essential anti-virus software. We found the<br />
system inventories to be very accurate, with<br />
PAWS Studio correctly identifying installed<br />
OSes, CPUs, used and available memory<br />
and hard disk space, installed software and<br />
much more.<br />
SMBs handling sensitive or personal data<br />
can't make light of regulatory compliance, as<br />
it will mean the difference between success<br />
and failure. PAWS Studio is an ideal auditing<br />
solution, as it provides highly detailed and<br />
comprehensible reports covering all the<br />
major compliance policies, and it is<br />
remarkably good value. NC<br />
Product: PAWS Studio 2.4.4<br />
Supplier: Titania Ltd<br />
Telephone: +44 (0)1905 888785<br />
Web site: www.titania.com<br />
Price: From £12 to £2 per device (exc. VAT)<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
JULY/AUGUST 2016 NETWORKcomputing 33
OPINION<br />
IOT SPELLS DANGER<br />
BY ANY MEASURE IOT IS NEW, BUT COULD A LACK OF EXPERIENCE<br />
COMBINED WITH POOR SOFTWARE DESIGN CREATE THE PERFECT<br />
SECURITY STORM? AMIT ASHBEL, CYBER SECURITY EVANGELIST AT<br />
CHECKMARX, EXPLORES THE ISSUES<br />
The catchy Hive jingle about<br />
controlling your heating at home is a<br />
great example of the benefits that IoT<br />
can offer. Such benefits are arguably the<br />
reason why IoT has been adopted with<br />
such voraciousness by manufacturers and<br />
consumers alike. Unfortunately, this has<br />
also resulted in IoT devices and<br />
applications being released on to the<br />
market largely unsecured (consider the<br />
University of Michigan's recent study into<br />
the vulnerabilities in Samsung's<br />
SmartThings platform). Meanwhile, the<br />
proliferation of BYOD, remote working<br />
and the always-on employee makes these<br />
unsecured applications, even if confined to<br />
the home, a huge risk to the enterprise<br />
network. So why is IoT largely unsecured,<br />
and how can this change?<br />
ONE CHINK IN THE ARMOUR<br />
A regular home today can have an array<br />
of connected products, from heating<br />
controls, to Smart TV, kitchen appliances<br />
and baby monitors. Each connected<br />
device presents an attack surface. In<br />
reality, once inside the home network,<br />
hacking the corporate network becomes a<br />
distinct possibility. Because of the<br />
connected nature of IoT, it only takes a<br />
small vulnerability, such as an unsecured<br />
fridge, to compromise the network.<br />
BOLTED-ON SECURITY<br />
In an environment where IoT products and<br />
updates are released at a furious rate,<br />
developers are measured on how fast they<br />
can produce code, meaning security can<br />
be an afterthought. Too often security is<br />
considered so late that there is only time<br />
to fix either bugs that could impact the<br />
user experience, or vulnerabilities that<br />
impact application security.<br />
In the competitive technology<br />
marketplace, the vendor often chooses to<br />
fix the bug and come back to the<br />
vulnerability later, rather than delay the<br />
release. It is this unsecured root<br />
application code in IoT devices and<br />
applications that presents the risk.<br />
Moreover, many new IoT vendors lack the<br />
painful experience the IT industry has gone<br />
through in the past 20 years. Vendors<br />
building household appliances are<br />
newcomers to cyber security and while<br />
they may employ external development<br />
firms to build in required functionality, the<br />
lack of regulation combined with<br />
inexperience is creating a lack of<br />
awareness concerning security.<br />
THE ONLY LEADERSHIP IN TOWN<br />
One of the main reasons why this<br />
continues to happen is because there are<br />
no regulations or industry standards when<br />
it comes to writing secure code. The<br />
closest thing to leadership is the Open<br />
Web Application Security Project (OWASP)<br />
which publishes a top ten IoT list of<br />
vulnerabilities on an ongoing basis and<br />
provides recommendations on how to<br />
develop IoT applications that are more<br />
difficult to hack. For example, it suggests<br />
that IoT hardware be programmed to insist<br />
on a default password change to a strong<br />
password during setup. But the underlying<br />
application code still needs to be secure.<br />
CHANGING THE SOFTWARE<br />
DEVELOPMENT LIFE CYCLE (SDLC)<br />
The normal process for software<br />
development or the software development<br />
lifecycle (SDLC) has 5 main stages:<br />
design, development (coding), testing,<br />
deployment and maintenance. As already<br />
mentioned, most testing is conducted late<br />
in the cycle, such as pen-testing, which is<br />
a black box testing method. But vendors<br />
who use white box testing methods such<br />
as Static Application Security Testing<br />
(SAST) can build a comprehensive<br />
understanding of the potential risks in the<br />
code early on, putting developers in a<br />
position to start addressing vulnerabilities<br />
in the same way that they address<br />
functional bugs, and transforming an<br />
SDLC into a Secure-SDLC (sSDLC). When<br />
security is at the core of the SDLC,<br />
vendors have a much better chance of<br />
preventing vulnerabilities that hackers can<br />
capitalise on and that, in turn, makes the<br />
network less vulnerable to attack.<br />
From this it's clear that those deploying<br />
IoT need to be aware of the security risks<br />
and ensure that they ask the most probing<br />
questions of all potential partners. NC<br />
34 NETWORKcomputing JULY/AUGUST 2016 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
WWW.TITANIA.COM<br />
www.t itania.com