MONSOON – ANALYSIS OF AN APT CAMPAIGN
monsoon-analysis-apt-campaign?utm_source=Labs&utm_medium=blog&utm_content=monsoon_whitepaper&utm_campaign=monsoon
monsoon-analysis-apt-campaign?utm_source=Labs&utm_medium=blog&utm_content=monsoon_whitepaper&utm_campaign=monsoon
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
Forcepoint Security Labs | Special Investigations<br />
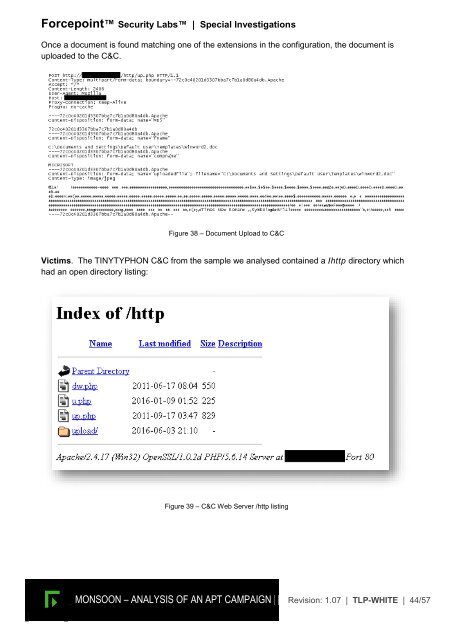
Once a document is found matching one of the extensions in the configuration, the document is<br />
uploaded to the C&C.<br />
Figure 38 <strong>–</strong> Document Upload to C&C<br />
Victims. The TINYTYPHON C&C from the sample we analysed contained a /http directory which<br />
had an open directory listing:<br />
Figure 39 <strong>–</strong> C&C Web Server /http listing<br />
<strong>MONSOON</strong> <strong>–</strong> <strong><strong>AN</strong>ALYSIS</strong> <strong>OF</strong> <strong>AN</strong> <strong>APT</strong> <strong>CAMPAIGN</strong> Revision: 1.07 | TLP-WHITE | 44/57