CYBERSECURITY
32524_edentree_cybersecurity_2109_lr_single-pages
32524_edentree_cybersecurity_2109_lr_single-pages
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
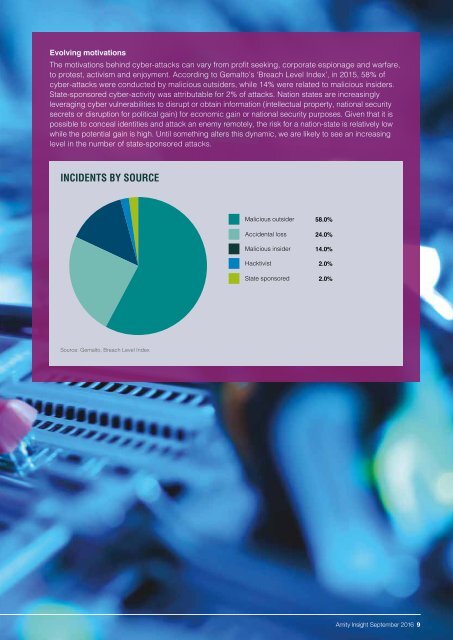
Evolving motivations<br />
The motivations behind cyber-attacks can vary from profit seeking, corporate espionage and warfare,<br />
to protest, activism and enjoyment. According to Gemalto’s ‘Breach Level Index’, in 2015, 58% of<br />
cyber-attacks were conducted by malicious outsiders, while 14% were related to malicious insiders.<br />
State-sponsored cyber-activity was attributable for 2% of attacks. Nation states are increasingly<br />
leveraging cyber vulnerabilities to disrupt or obtain information (intellectual property, national security<br />
secrets or disruption for political gain) for economic gain or national security purposes. Given that it is<br />
possible to conceal identities and attack an enemy remotely, the risk for a nation-state is relatively low<br />
while the potential gain is high. Until something alters this dynamic, we are likely to see an increasing<br />
level in the number of state-sponsored attacks.<br />
INCIDENTS BY SOURCE<br />
Malicious outsider 58.0%<br />
Accidental loss 24.0%<br />
Malicious insider 14.0%<br />
Hacktivist 2.0%<br />
State sponsored 2.0%<br />
Source: Gemalto, Breach Level Index<br />
Amity Insight September 2016 9