LPE vulnerabilities exploitation on Windows 10 Anniversary Update
Win10LPE
Win10LPE
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
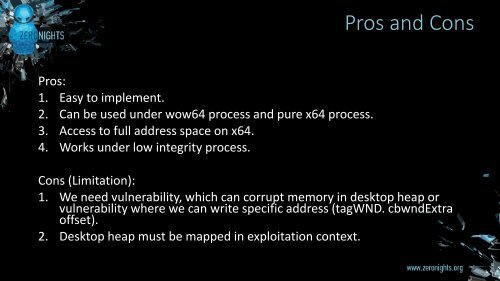
Pros and C<strong>on</strong>s<br />
Pros:<br />
1. Easy to implement.<br />
2. Can be used under wow64 process and pure x64 process.<br />
3. Access to full address space <strong>on</strong> x64.<br />
4. Works under low integrity process.<br />
C<strong>on</strong>s (Limitati<strong>on</strong>):<br />
1. We need vulnerability, which can corrupt memory in desktop heap or<br />
vulnerability where we can write specific address (tagWND. cbwndExtra<br />
offset).<br />
2. Desktop heap must be mapped in <str<strong>on</strong>g>exploitati<strong>on</strong></str<strong>on</strong>g> c<strong>on</strong>text.