LPE vulnerabilities exploitation on Windows 10 Anniversary Update
Win10LPE
Win10LPE
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
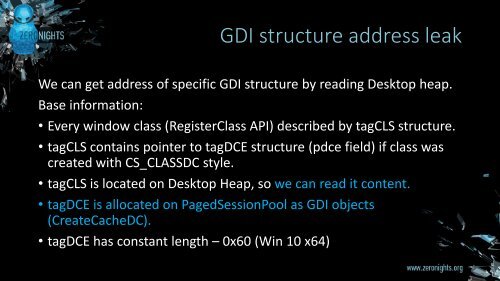
GDI structure address leak<br />
We can get address of specific GDI structure by reading Desktop heap.<br />
Base informati<strong>on</strong>:<br />
• Every window class (RegisterClass API) described by tagCLS structure.<br />
• tagCLS c<strong>on</strong>tains pointer to tagDCE structure (pdce field) if class was<br />
created with CS_CLASSDC style.<br />
• tagCLS is located <strong>on</strong> Desktop Heap, so we can read it c<strong>on</strong>tent.<br />
• tagDCE is allocated <strong>on</strong> PagedSessi<strong>on</strong>Pool as GDI objects<br />
(CreateCacheDC).<br />
• tagDCE has c<strong>on</strong>stant length – 0x60 (Win <strong>10</strong> x64)