LPE vulnerabilities exploitation on Windows 10 Anniversary Update
eJwXM6v
eJwXM6v
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
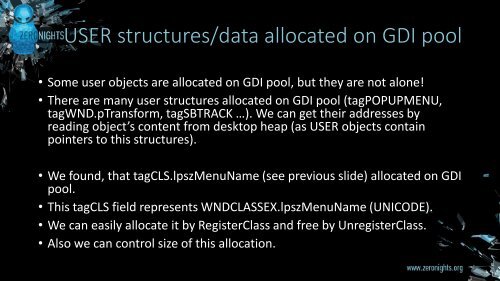
USER structures/data allocated <strong>on</strong> GDI pool<br />
• Some user objects are allocated <strong>on</strong> GDI pool, but they are not al<strong>on</strong>e!<br />
• There are many user structures allocated <strong>on</strong> GDI pool (tagPOPUPMENU,<br />
tagWND.pTransform, tagSBTRACK …). We can get their addresses by<br />
reading object’s c<strong>on</strong>tent from desktop heap (as USER objects c<strong>on</strong>tain<br />
pointers to this structures).<br />
• We found, that tagCLS.lpszMenuName (see previous slide) allocated <strong>on</strong> GDI<br />
pool.<br />
• This tagCLS field represents WNDCLASSEX.lpszMenuName (UNICODE).<br />
• We can easily allocate it by RegisterClass and free by UnregisterClass.<br />
• Also we can c<strong>on</strong>trol size of this allocati<strong>on</strong>.