ACC 340 Final Exam Guide
To purchase this material click below link:- http://www.assignmentrank.com/acc-340/acc-340-final-exam-guide For More Tutorials Click Below link:- http://www.assignmentrank.com 1. The essential steps in performing a systems study are (in order of occurrence): a) Analysis, design, implementation and initial operation, follow up b) Design, planning, follow up, analysis, and implementation c) Planning, system specification, analysis, production, implementation d) Planning, analysis, design, implementation, and follow up
To purchase this material click below link:-
http://www.assignmentrank.com/acc-340/acc-340-final-exam-guide
For More Tutorials Click Below link:-
http://www.assignmentrank.com
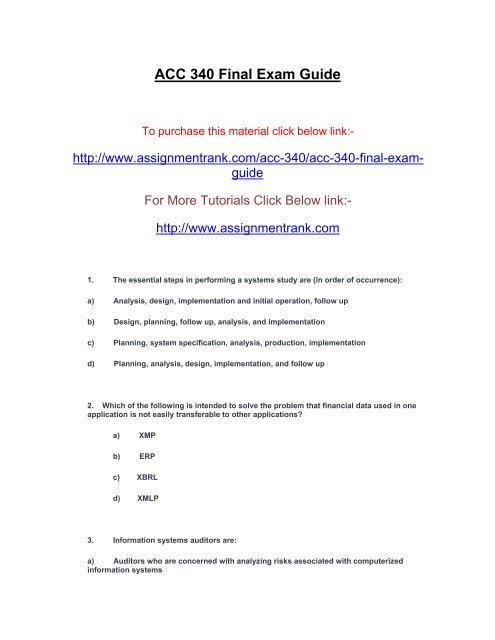
1. The essential steps in performing a systems study are (in order of occurrence):
a) Analysis, design, implementation and initial operation, follow up
b) Design, planning, follow up, analysis, and implementation
c) Planning, system specification, analysis, production, implementation
d) Planning, analysis, design, implementation, and follow up
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
<strong>ACC</strong> <strong>340</strong> <strong>Final</strong> <strong>Exam</strong> <strong>Guide</strong><br />
To purchase this material click below link:-<br />
http://www.assignmentrank.com/acc-<strong>340</strong>/acc-<strong>340</strong>-final-examguide<br />
For More Tutorials Click Below link:-<br />
http://www.assignmentrank.com<br />
1. The essential steps in performing a systems study are (in order of occurrence):<br />
a) Analysis, design, implementation and initial operation, follow up<br />
b) Design, planning, follow up, analysis, and implementation<br />
c) Planning, system specification, analysis, production, implementation<br />
d) Planning, analysis, design, implementation, and follow up<br />
2. Which of the following is intended to solve the problem that financial data used in one<br />
application is not easily transferable to other applications?<br />
a) XMP<br />
b) ERP<br />
c) XBRL<br />
d) XMLP<br />
3. Information systems auditors are:<br />
a) Auditors who are concerned with analyzing risks associated with computerized<br />
information systems
) Individuals who often work closely with financial auditors<br />
c) Auditors who have a lot of technical expertise related to information technology<br />
d) all of the above<br />
4. Which of the following is not an ability of client/server computing?<br />
a) Alter data stored elsewhere on the network<br />
b) Process a transaction that may affect data stored on both client and server computers<br />
c) Query or manipulate the warehoused data on the server<br />
d) Increased networking capabilities between different file formats on multiple systems<br />
5. Software that enables businesses and government agencies to transmit and manipulate<br />
financial data on an organization-wide basis best describes:<br />
a. Communication software<br />
b. CAD software<br />
c. Enterprise resource planning (ERP) software<br />
d. Programming software<br />
6. All of the following are programming languages except:<br />
a. Java<br />
b. HTML<br />
c. C++<br />
d. COBOL<br />
e. ERP<br />
7. Data flow diagrams:<br />
a) Accomplish the same purpose as system flowcharts
) Are different from system flowcharts since they focus on a logical view of the<br />
information system<br />
c) Are useless for planning a new system<br />
d) Are never used in analyzing an existing system<br />
8. All of the following are controls for end-user computing except:<br />
a) Formally evaluate large projects<br />
b) Formalize documentation standards<br />
c) Limit the number of employees authorized to create end-user applications<br />
d) all of the above are important controls<br />
9. The textbook identified seven reasons why documentation of an AIS is important. For<br />
which of the following reasons would the user guides, procedure manuals and operating<br />
instructions be most important?<br />
a) Depicting how the system works<br />
b) Training users<br />
c) Designing new systems<br />
d) Standardizing communications with others<br />
10. Business organizations are recognizing the value of sales data and are purchasing<br />
software solutions to gather, maintain, and use these data to provide better service and<br />
promote customer loyalty. These software solutions are called:<br />
a) Customer relations data solutions<br />
b) Customer relationship management solutions<br />
c) Sales data management solutions<br />
d) none of the above<br />
11. Which of the following statements best describes business process outsourcing?
a) A company focuses on its core business processes and contracts with another firm to<br />
do the other processes<br />
b) Companies frequently outsource core business processes<br />
c) Due to networked enterprises and advanced technology, more employees may work<br />
from their homes or alternate locations<br />
d) Initially, companies engaged in business process outsourcing to offer employees more<br />
opportunities to travel and more career choices for advancement<br />
12. Networked enterprises and globalization have enabled a new business model called<br />
“business-without-boundaries.” Which of the following statements describes this business<br />
model?<br />
a) Companies no longer have all of their employees in one location<br />
b) It is called offshoring and companies contract with firms in other countries to do such<br />
business processes as human resources, payroll, and accounting<br />
c) Companies are under a great deal of scrutiny to manage costs and generate revenue so<br />
they contract with foreign firms to do various business processes at a lower cost to the<br />
company<br />
d) all of the above statements describe this model<br />
13. Which of the following is not a concern of the financing process?<br />
a) Effective cash management<br />
b) Optimizing an organization’s cost of capital<br />
c) Minimizing an organization’s borrowings<br />
d) Projecting cash flows<br />
14. Business process reengineering efforts sometimes fail because:<br />
a. Management gets too involved in the process<br />
b. Management is too optimistic regarding its expectations from its implementation<br />
c. Management support can never overcome employee resistance<br />
d. Employees will never accept change
15. Which of the following technologies are now used in conjunction with automated<br />
production process systems to increase efficiencies?<br />
a) Radio frequency technology<br />
b) Bar code scanners<br />
c) RF IDs and advanced electronic tags<br />
d) all of the above<br />
e) none of the above<br />
16. According to the textbook, which of these statements is most accurate?<br />
a) Most computer abuse is performed as retaliation against employers<br />
b) Very little computer crime is committed for personal gain<br />
c) Some computer abuse is performed simply to meet a challenge<br />
d) We catch most computer abusers with good accounting controls<br />
17.Which of the following is probably the primary reason accountants should be concerned<br />
about computer crime and abuse?<br />
a) They might lose their job if they don’t detect computer crime or abuse in their<br />
organization<br />
b) They might lose their professional credibility and license if computer crime or abuse<br />
continues for a long time in their organization and they do not detect it<br />
c) They are responsible for designing, implementing, and monitoring the control<br />
procedures for AISs<br />
d) none of the above<br />
18.One of the major crimes identified by the Computer Fraud and Abuse Act of 1986 is intent to<br />
illegally obtain information or tangible property through the use of computers. Which of the<br />
following methods might accomplish this type of crime if the perpetrator can change data<br />
before, during, or after they are entered into a computer system?<br />
a) Salami technique
) Data diddling<br />
c) Shoulder surfing<br />
d) Trojan horse program<br />
19.Regarding a company's audit trail, which of the following statements is true?<br />
a) Because of the complexities involved in establishing an audit trail, a good audit trail<br />
normally makes it more difficult for an individual to follow the flow of a company's business<br />
transactions through the company's information system<br />
b) In actuality, the audit trail established within a company's information system is an<br />
unimportant element of the company's internal control system<br />
c) When a company's audit trail becomes more difficult to follow, this causes an increase<br />
in the risk of errors or irregularities taking place in the processing of accounting transactions<br />
and not being detected<br />
d) A company's policies and procedures manual should not be part of its audit trail since<br />
confidential information is included within this manual<br />
20.Which of the following statements is true regarding timely performance reports?<br />
a. In many companies, these reports are the major means of providing information to<br />
management concerning the actual operations of the companies’ internal control systems<br />
b. These reports should only include monetary data<br />
c. Since these reports fail to provide feedback to management on the operations of<br />
previously implemented internal control procedures, other techniques are needed to provide<br />
this feedback to managers<br />
d. The complexity that a computer introduces into a company's information system will<br />
typically prevent the preparation of timely performance reports for the company's management<br />
21. _________________ describes the policies, plans, and procedures implemented by a<br />
firm to protect its assets.<br />
a) Internal control<br />
b) SAS No. 94<br />
c) SOX, Section 404
d) Enterprise risk management<br />
22. General controls within IT environments that affect personnel include:<br />
a) Use of computer accounts<br />
b) Separation of duties<br />
c) Informal knowledge of employees<br />
d) all of the above affect personnel<br />
23. Which of the following best describes a fundamental control weakness often associated<br />
with automated data processing systems?<br />
a. Automated¬ data processing equipment is more subject to systems error than manual<br />
processing is subject to human error<br />
b. Automated data processing equipment processes and records similar transactions in a<br />
similar manner<br />
c. Automated data processing procedures for detection of invalid and unusual<br />
transactions are less effective than manual control procedures<br />
d. Functions that would normally be separated in a manual system are combined in an<br />
automated data processing system<br />
24. The textbook identifies a number of issues that should be considered when developing a<br />
security policy. One of the issues is “identify threats”. Which of the following is not an<br />
example of this issue?<br />
a) What assets need to be protected<br />
b) What are the sources of potential security problems<br />
c) External threats are viruses, worms, retaliations from former employees<br />
d) Internal threats are misuse of assets by employees and embezzlement<br />
25 Which of these is not a phase in the life cycle of an information system?<br />
a) Planning
) Analysis<br />
c) Control<br />
d) Implementation<br />
26. A poorly-planned information system can result in:<br />
a) Employee resistance and even sabotage<br />
b) Inflexible systems that are hard to maintain or modify<br />
c) Systems that solve the wrong problems<br />
d) all of these<br />
27. Which of the following is not a general objective in the design of an information system?<br />
a) A system should provide information which is timely and relevant for decision making<br />
by management and operating personnel<br />
b) The output of a system should be highly accurate<br />
c) A system should have sufficient capacity to accommodate levels of normal activity; any<br />
additional capacity proves too costly in the long run<br />
d) A system should be as simple as permitted so that its structure and operation can be<br />
easily understood and its procedures easily accomplished<br />
e) A system should be flexible to accommodate changes of a reasonable magnitude when<br />
required<br />
28. A computerized AIS is harder to audit than a manual system for all of the following<br />
reasons except:<br />
a) The file information is not human readable<br />
b) The volume of transaction records and master file records is usually much larger in<br />
computerized systems than in manual systems<br />
c) An audit trail does not exist in a computerized AIS<br />
d) Computerized systems often use remote real-time data processing, thus complicating<br />
the tracing of transaction records to their sources
29. Which of the following is not one of the groups of SOX compliance requirements?<br />
a) requirements to use an IT auditor to evaluate controls<br />
b) regulations governing executive reporting and conduct<br />
c) rules about financial statement reporting<br />
d) audit committee/corporate governance requirements<br />
30. Three common techniques auditors use to test computer programs are:<br />
a) Test data, integrated test facilities, and parallel simulation<br />
b) Test data, edit checks, and integrated test facilities<br />
c) Test data, program change control, and parallel simulation<br />
d) Program change control, edit checks, and parallel simulation<br />
31. The term data encryption refers to:<br />
a) Storing data in safe places called “crypts”<br />
b) Transforming data into secret codes<br />
c) Scrambling data in random ways that cannot be unscrambled<br />
d) none of these<br />
32. The term key in the context of data encryption refers to:<br />
a) A physical key similar to a house key<br />
b) A logical key similar to the primary key of a data file<br />
c) A mathematical function used for encryption purposes<br />
d) A computer function key that can be found on keyboards<br />
33. All of the following are benefits of XBRL except:
a) Companies can file financial information in one format, avoiding the errors that may<br />
come from reentering data multiple times<br />
b) The SEC accepts XBRL-format for electronic filing of financial statement reports<br />
c) XBRL permits the automatic and reliable exchange of financial information across all<br />
software formats and technologies, including the Internet<br />
d) all of the above are benefits of XBRL<br />
e) none of the above are benefits of XBRL<br />
34. All of these are reasons why databases are important to AISs except:<br />
a) AIS databases store valuable information<br />
b) Many AISs are large and therefore potentially unwieldy<br />
c) The databases of some organizations are very complex<br />
d) The hard disk space used to store AIS databases is comparatively expensive<br />
e) all of these are reasons why databases are important to AISs<br />
35. A major advantage of relational databases is:<br />
a) All records are stored together<br />
b) No pointers are used<br />
c) An expandable index is used<br />
d) It closely resembles a flat file<br />
36. In recent years many businesses have formed a common information source within their<br />
business organization called a database. One of the advantages of building databases is the<br />
simultaneous updating of files with common data elements. Another major advantage of the<br />
database concept is that:<br />
a) Database systems can be used in microcomputers as well as on large computers<br />
b) Database systems are simple to install and maintain<br />
c) Database systems are generally less expensive than separate file maintenance systems
d) Less duplication of data occurs with a database system<br />
e) Fewer skilled people are required to run a database system than any other system<br />
37. The process of data normalization refers to:<br />
a) Eliminating data errors and other problems from “normal data”<br />
b) Scaling data to values between zero and one<br />
c) Storing data in normal storage media such as hard disks<br />
d) none of these<br />
38. Database management systems are important to accountants because:<br />
a) They automate file storage tasks and enable managers to generate worthwhile financial<br />
reports<br />
b) They eliminate data redundancy<br />
There are no reviews for this product.