You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
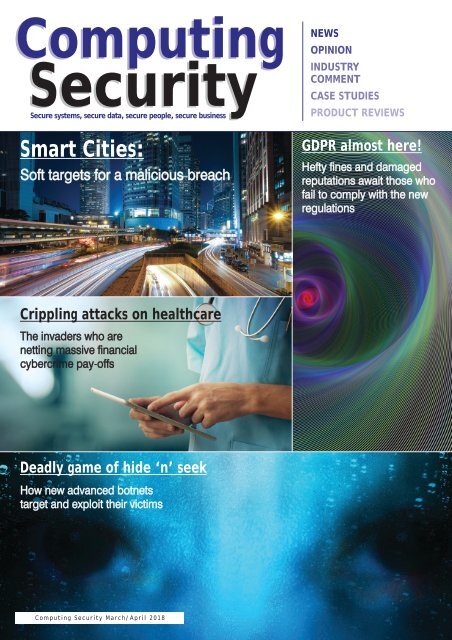
Computing<br />
Security<br />
Secure systems, secure data, secure people, secure business<br />
Smart Cities:<br />
Soft targets for a malicious breach<br />
NEWS<br />
OPINION<br />
INDUSTRY<br />
COMMENT<br />
CASE STUDIES<br />
PRODUCT REVIEWS<br />
GDPR almost here!<br />
Hefty fines and damaged<br />
reputations await those who<br />
fail to comply with the new<br />
regulations<br />
Crippling attacks on healthcare<br />
The invaders who are<br />
netting massive financial<br />
cybercrime pay-offs<br />
Deadly game of hide ‘n’ seek<br />
How new advanced botnets<br />
target and exploit their victims<br />
Computing Security March/April 2018
IT Asset Retirement Specialists<br />
Why Choose CDL?<br />
Since 1999, CDL has evolved into one of the UK’s leading IT asset retirement<br />
and data sanitisation specialists.<br />
Our aim is simply to take away the hassles associated with IT disposal and provide<br />
our customers with a complete peace of mind solution for the management and<br />
retirement of redundant IT equipment.<br />
Competitive pricing, an industry leading EU GDPR compliant disposal process<br />
and the highest level of customer service are reasons why we have retained over<br />
94% of our clients.<br />
Legal Expo - London Exel<br />
We are exhibiting at this years Legal Expo on the 21st & 22nd March. Come<br />
along to stand 464 to discuss any aspect of IT asset retirement for your<br />
business. We can also help ensure your business becomes EU GDPR<br />
compliant in a few easy steps.<br />
So what differentiates CDL from the competition?<br />
EU GDPR compliant service<br />
Full UK coverage with no minimum quantities<br />
Use own tracked vehicles and security vetted drivers<br />
Guaranteed collection within 5 working days<br />
94% client retention rate since 1999<br />
Multi award winning company<br />
All staff security vetted<br />
Data Sanitisation to the highest recognized standards<br />
On-site media destruction service<br />
ISO 9001, 14001, 18001 & 27001<br />
ADISA accredited with Distinction<br />
Investors in People Silver<br />
Safe Contractor accredited<br />
ICER member<br />
Cyber Security Insurance<br />
NHS IG Toolkit accredited<br />
set RetirementSpecialists
comment<br />
COUNCIL OF WAR<br />
Anew and deeply disturbing report from Big Brother Watch reveals that UK councils<br />
are severely unprepared for cybersecurity threats, with 25% of these authorities<br />
experiencing a data breach in the last five years.<br />
The report, 'Cyber attacks in local authorities: How the quest for big data is threatening<br />
cyber security', reveals that, based on Freedom of Information requests made by Big<br />
Brother Watch, UK local authorities have experienced in excess of 98 million cyberattacks<br />
in that five-year timeframe.<br />
"This means that there are at least 37 attempted breaches of UK local authorities every<br />
minute," the civil liberties and privacy campaigning organisation reports. "In addition, at<br />
least 1 in 4 councils experienced a cyber security incident - that is, an actual security<br />
breach - between 2013-2017."<br />
While some councils have taken measures to face the ever-growing threat from cyberattacks,<br />
the areas of staff training and reporting of successful cyber-attacks especially<br />
need urgent attention, it adds.<br />
"Surprisingly, our current investigation reveals that little action has been taken to<br />
increase staff awareness and education in these matters. We found that 75% of local<br />
authorities do not provide mandatory training in cyber security awareness for staff and<br />
16% do not provide any training at all. Considering that the majority of successful cyberattacks<br />
start with phishing emails aimed at unwitting staff, negligence in staff training is<br />
very concerning and only indicative of the low priority afforded to cyber security issues."<br />
Big Brother Watch's findings further reveal that 25 local authorities experienced losses<br />
or breaches of data in the past five years as a result of cyber security incidents. "Yet 56%<br />
of councils who failed to protect data from cyber security threats did not even report the<br />
incidents," it adds.<br />
Clearly, if this situation continues, the consequences for local authorities and all those<br />
whose information they hold are dire. What they need to do now, as a matter of<br />
urgency, is review their policies with a view to mitigating the risks of cyber security incidents<br />
that threaten the security of citizens' invaluable data. Anything less would be a<br />
clear breach of trust between those councils and the millions of people they are supposed<br />
to serve and whose sensitive personal data has been entrusted to them.<br />
Brian Wall<br />
Editor<br />
Computing Security<br />
brian.wall@btc.co.uk<br />
EDITOR: Brian Wall<br />
(brian.wall@btc.co.uk)<br />
PRODUCTION: Abby Penn<br />
(abby.penn@btc.co.uk)<br />
LAYOUT/DESIGN: Ian Collis<br />
(ian.collis@btc.co.uk)<br />
SALES:<br />
Edward O’Connor<br />
(edward.oconnor@btc.co.uk)<br />
+ 44 (0)1689 616 000<br />
Louise Hollingdale<br />
(louise.hollingdale@btc.co.uk)<br />
+ 44 (0)1689 616 000<br />
PUBLISHER: John Jageurs<br />
(john.jageurs@btc.co.uk)<br />
Published by Barrow & Thompkins<br />
Connexions Ltd (BTC)<br />
35 Station Square,<br />
Petts Wood, Kent, BR5 1LZ<br />
Tel: +44 (0)1689 616 000<br />
Fax: +44 (0)1689 82 66 22<br />
SUBSCRIPTIONS:<br />
UK: £35/year, £60/two years,<br />
£80/three years;<br />
Europe: £48/year, £85/two years,<br />
£127/three years<br />
R.O.W:£62/year, £115/two years,<br />
£168/three years<br />
Single copies can be bought for<br />
£8.50 (includes postage & packaging).<br />
Published 6 times a year.<br />
© 2018 Barrow & Thompkins<br />
Connexions Ltd. All rights reserved.<br />
No part of the magazine may be<br />
reproduced without prior consent,<br />
in writing, from the publisher.<br />
www.computingsecurity.co.uk March/April 2018 computing security<br />
@CSMagAndAwards<br />
3
Secure systems, secure data, secure people, secure business<br />
Computing Security March/April 2018<br />
contents<br />
CONTENTS<br />
Computing<br />
Security<br />
Smart Cities:<br />
Soft targets for a malicious breach<br />
Crippling attacks on healthcare<br />
The invaders who are<br />
netting massive financial<br />
cybercrime pay-offs<br />
NEWS<br />
OPINION<br />
INDUSTRY<br />
COMMENT<br />
CASE STUDIES<br />
PRODUCT REVIEWS<br />
GDPR almost here!<br />
Hefty fines and damaged<br />
reputations await those who<br />
fail to comply with the new<br />
regulations<br />
COMMENT 3<br />
Council of war<br />
Deadly game of hide ‘n’ seek<br />
How new advanced botnets<br />
target and exploit their victims<br />
EDITOR’S FOCUS 6<br />
• Evolving your security to the cloud<br />
ARTICLES<br />
PROTECTING DATA & PATIENTS 8<br />
Cyber criminals are netting huge financial<br />
returns from ransomware and other<br />
crippling cyberattacks against healthcare<br />
providers. Can they be stopped?<br />
IT DISPOSAL: BEST WAY FORWARD 10<br />
Legislation regarding IT recycling & disposal<br />
is complicated. How do you select the best<br />
disposal companies?<br />
EVERYONE IS AT RISK 17<br />
From spear phishing to ransomware and<br />
the ever-present threat of bots, businesses<br />
have good reason to lose sleep at night<br />
DEADLY GAME OF HIDE ‘N’ SEEK 20<br />
A botnet has been unearthed that uses<br />
advanced communication techniques to<br />
exploit victims and build its infrastructure<br />
AN URGENT CALL TO ARMS 12<br />
In Part 2 of our coverage on what might be<br />
in store for businesses as 2018 gets into its<br />
stride, Computing Security asked a number<br />
of experts to do some more future-gazing<br />
and to provide their top predictions for<br />
cybersecurity across the rest of the year<br />
RISK & REWARD IN THE BIG CITY 18<br />
Back in the 1960s, Disneyland had a ride<br />
called 'Utopia'. It was a glimpse into the<br />
future of 'human cities' and gave us a taste<br />
of just what smart cities might be like.<br />
Alastair Hartrup, Global CEO, Network<br />
Critical, takes up the story from there<br />
TASTE OF THINGS TO COME 22<br />
London-based technology start-up Red Sift<br />
singles out three major trends it thinks will<br />
dominate in the months to come<br />
REVIEWS<br />
• Titania Paws Studio 3.2.2 28<br />
MASTERCLASS 30<br />
Charlotte Gurney, group marketing<br />
manager at Brookcourt Solutions,<br />
provides key insights on a crucial issue that<br />
challenges so many enterprises<br />
4<br />
IT’S TIME TO BE VERY READY! 24<br />
The General Data Protection Regulation<br />
(GDPR) comes into force this May and will<br />
overhaul how organisations store, secure<br />
and manage their customers' data.<br />
Swingeing penalties await those who<br />
fail to comply<br />
DRIVING INTO THE UNKNOWN 32<br />
THE DARK DESTROYERS 31<br />
Connected cars are a reality; most modern<br />
Over one million leaked and hacked<br />
vehicles on the road nowadays have some<br />
credentials found on the Dark Web<br />
form of connectivity to the open world.<br />
This raises important challenges on multiple<br />
AI VERSUS A HUMAN HACKER 34<br />
software integration and cybersecurity<br />
How does machine learning and artificial<br />
intelligence (AI) impact cyber security?<br />
We find out from someone in the know<br />
computing security March/April 2018 @CSMagAndAwards www.computingsecurity.co.uk
helping our customers do great things<br />
we help our customers do great things<br />
IPEXPO<br />
manchester<br />
25-26 April 2018,<br />
Manchester Central<br />
REGISTER FREE<br />
• 95+ World-class speakers<br />
• 100+ Industry leading vendors<br />
• 9 Theatres<br />
• Live Demos<br />
• Everything you need<br />
under ONE roof<br />
CLOUD & IOT<br />
CYBER SECURITY<br />
MANCHESTER<br />
NETWORKS &<br />
INFRASTRUCTURE<br />
DATA & ANALYTICS DEVOPS AI<br />
www.ipexpomanchester.com<br />
SPONSORED BY<br />
helping you do great things
editor's focus<br />
EVOLVING YOUR SECURITY FOR THE CLOUD<br />
HOW DOES AN ORGANISATION MIGRATE TO THE CLOUD, WHILE KEEPING SECURITY TOP OF MIND AND<br />
STAYING SAFE?<br />
Maya Kaczorowski, product manager,<br />
Google Cloud.<br />
Global management consulting<br />
firm McKinsey recently released<br />
a report titled 'Making a secure<br />
transition to the public cloud', the result<br />
of interviews with IT security experts at<br />
nearly 100 enterprises around the world.<br />
Drawing on the expertise of Google<br />
Cloud and McKinsey security experts,<br />
the research presented a strategic<br />
framework for IT security in cloud<br />
and hybrid environments, and offered<br />
recommendations on how to migrate<br />
to the cloud, while keeping security top<br />
of mind.<br />
According to Maya Kaczorowski,<br />
product manager, Google Cloud, the<br />
research shows what many already<br />
know: that public cloud adoption is<br />
accelerating, thanks to increased<br />
technical flexibility, simpler scaling and<br />
lower operating costs. "What's exciting is<br />
that the research also reveals that many<br />
Chief Information Security Officers<br />
(CISOs) no longer view security as an<br />
inhibitor to adoption, but instead an<br />
opportunity," she states.<br />
In fact, the McKinsey report authors<br />
write that… "In many cases, [CISOs]<br />
acknowledge that cloud service<br />
providers' security resources dwarf their<br />
own" - and now these companies are<br />
focused on how to best adopt and<br />
configure cloud services for increased<br />
security." It's a launch pad from which<br />
Kaczorowski addresses several points<br />
about the global cloud and specifically<br />
the following:<br />
When implemented properly, publiccloud<br />
adoption can significantly reduce<br />
the total cost of ownership (TCO) for<br />
IT security<br />
This requires enterprises, cloud<br />
providers, and third-party service<br />
providers to work together<br />
collaboratively and transparently within<br />
a shared security model. Google Cloud<br />
has long believed in creating trust<br />
through transparency, previously<br />
releasing a detailed overview of our<br />
infrastructure security, explaining our<br />
shared responsibility model, and how we<br />
already protect our users and customers<br />
at the lower layers of the stack-and<br />
we're thrilled to see McKinsey's detailed<br />
endorsement of the same approach.<br />
Common security approaches and their<br />
trade-offs<br />
Every company has different IT needs,<br />
but the report found two common<br />
security decisions companies take when<br />
adopting cloud services: (1) defining the<br />
perimeter, and (2) deciding whether to<br />
re-architect applications for greater<br />
manageability, performance and security<br />
in the cloud (interestingly, only 27% of<br />
companies surveyed actually do thischange<br />
is hard).<br />
The research identifies three common<br />
archetypes for perimeter security, says<br />
Kaczorowski: backhauling, cleansheeting<br />
and adopting cloud provider controls<br />
by default.<br />
Backhauling allows companies to<br />
continue managing IT security onprem,<br />
with an external gateway<br />
connecting the data centre to the<br />
public cloud. Approximately half of<br />
the companies surveyed currently use<br />
this model, but only 11% plan to<br />
06<br />
computing security March/April 2018 @CSMagAndAwards www.computingsecurity.co.uk
editor's focus<br />
continue doing so, since it can keep<br />
companies from realising certain<br />
cloud benefits, such as agility.<br />
Cleansheeting requires greater<br />
investment and expertise, as it calls<br />
for redesigning IT security around<br />
a 'virtual perimeter', and leveraging<br />
multiple cloud-native tools and<br />
services.<br />
Using cloud provider controls is the<br />
most cost-effective solution, but -<br />
depending on the cloud provider -<br />
can limit autonomy and may offer<br />
limited capabilities.<br />
McKinsey uses these three models,<br />
comments Kaczorowski, along with the<br />
decision to re-architect applications for<br />
the cloud, to identify six 'archetypes' for<br />
cloud security. Each archetype has its<br />
own trade-offs, she points out, adding<br />
that there isn't a 'right answer' for<br />
security when making a move to the<br />
cloud-it depends on your company's<br />
expertise, flexibility and cost decisions.<br />
"And you don't have to use only one<br />
archetype," she adds, citing as an<br />
example how Evernote (the company<br />
behind the app designed for note taking,<br />
organising, tasks lists and archiving)<br />
describes its migration story to the<br />
Google Cloud platform thus:<br />
"For most of our controls, we found<br />
an equivalent, cloud platform version.<br />
For data encryption at rest, we gained<br />
a security control that we hadn't<br />
engineered on our own. For some<br />
controls, like IP whitelisting, we had to<br />
adapt our security architecture to not<br />
rely on traditional network controls."<br />
(Rich Tener, director of security,<br />
Evernote).<br />
The economics of cloud security<br />
Relying on cloud service provider security<br />
controls is "the most cost-effective<br />
approach," the authors write. "As<br />
organisations move more and more<br />
applications to the public cloud and<br />
lean towards using native CSP controls,<br />
a decrease in security operating and<br />
capex costs is likely." Eighty per cent of<br />
companies that choose to rely primarily<br />
on the cloud provider's controls and rearchitect<br />
their applications in parallel see<br />
cost savings.<br />
So, if you're planning a cloud<br />
migration, where should you focus your<br />
security efforts? That is the question<br />
Kaczorowski then homes in on.<br />
"McKinsey asked respondents about their<br />
approach to applying cloud security<br />
controls in several areas to find out what<br />
companies are doing," she reports:<br />
Identity & access management (IAM):<br />
60% of enterprises are using onpremises<br />
IAM solutions; in just three<br />
years respondents expect that<br />
number to be cut in half. At Google,<br />
we provide a tool called Google<br />
Cloud Directory Sync, which helps<br />
users bring existing identities to<br />
Google Cloud and manage cloud<br />
permissions natively with IAM.<br />
Encryption: The majority of<br />
respondents encrypt data both at<br />
rest and in transit - and even more<br />
(upwards of 80% in both categories)<br />
will do so three years from now.<br />
Google Cloud already encrypts data<br />
at rest by default, and in transit<br />
when it crosses a physical boundary.<br />
Perimeter security: Today, 40% of<br />
enterprises are backhauling data<br />
traffic and using existing on-premises<br />
network security controls - but that<br />
will decrease, with only 13%<br />
expecting to be using the same<br />
approach in three years' time.<br />
"To help enterprises make the move to<br />
cloud-based perimeter control, Google<br />
Cloud lets users connect to their onpremises<br />
environment using Dedicated<br />
Interconnect, as IPsec VPN tunnel, direct<br />
peering or carrier peering. Google Cloud<br />
users can also control their perimeter<br />
with a Virtual Private Cloud (VPC)," she<br />
points out, offering these insights:<br />
Application security: 65% of<br />
respondents define security<br />
configuration standards for cloudbased<br />
applications, but less than<br />
20% are using tools or templatebased<br />
enforcement. To address this,<br />
Google Cloud offers Cloud Security<br />
Scanner, an automated way to scan<br />
apps for common vulnerabilities.<br />
Operational monitoring: 64% of<br />
respondents use existing SIEM tools<br />
to monitor cloud applications rather<br />
than creating a new set for the<br />
cloud. Google Cloud users can export<br />
logs from Stackdriver to the SIEM of<br />
their choice.<br />
Server-side endpoints: 51% of<br />
respondents have a high level of<br />
confidence in their cloud service<br />
provider's approach to server-side<br />
endpoint security. Google Cloud<br />
customers can use a variety of<br />
partner tools for endpoint security.<br />
User endpoints: 70% of respondents<br />
believe public-cloud adoption will<br />
require changes to user endpoints.<br />
Google created the BeyondCorp<br />
enterprise security model to allow its<br />
employees to work from anywhere,<br />
and our customers can do the same<br />
with Identity Aware Proxy. In<br />
addition, Chromebooks provide<br />
automatic software updates and run<br />
applications in a restricted sandbox.<br />
Regulatory governance: When<br />
adopting public cloud, companies<br />
must navigate governance and<br />
compliance requirements, with data<br />
location and financial regulations<br />
topping respondents' list of concerns.<br />
Google Cloud has a broad spectrum<br />
of compliance, including PCI, SOX,<br />
and HIPAA.<br />
For those interested in finding out<br />
more, the report also includes a tactical<br />
10-step plan for successful cloud<br />
migration. Go to: http://bit.ly/2AnzWFh<br />
www.computingsecurity.co.uk @CSMagAndAwards March/April 2018 computing security<br />
07
healthcare<br />
PROTECTING DATA TO PROTECT PATIENTS<br />
CYBER CRIMINALS ARE NETTING MASSIVE FINANCIAL RETURNS FROM RANSOMWARE AND OTHER<br />
CRIPPLING CYBERATTACKS AGAINST HEALTHCARE PROVIDERS. HOW CAN THEY BE STOPPED?<br />
MARK SANGSTER, VP AND INDUSTRY SECURITY STRATEGIST WITH ESENTIRE, OFFERS HIS INSIGHTS<br />
Healthcare providers, support<br />
services and technology<br />
manufacturers have emerged as<br />
a favoured target of cyber criminals.<br />
Beyond the headlines of NHS shutdowns<br />
and delayed patient care, multiple<br />
studies, from the Information<br />
Commissioner's Office (ICO) to security<br />
research institute Ponemon, confirm<br />
healthcare as the industry's most<br />
vulnerable to cyber-attacks.<br />
Operational cyber-attack data generated<br />
from 24x7 monitoring of healthcare<br />
providers, insurers and equipment<br />
manufacturers indicate that these<br />
organisations face a significant exploit<br />
every hour of the day, which is four times<br />
more than financial services or law firms<br />
(2018 eSentire Security Operations Data).<br />
Such exploits vary in nature, but require<br />
security expert intervention, after the<br />
exploit evades standard prevention<br />
technologies, such as anti-virus, firewalls<br />
and intrusion prevention systems.<br />
"Headlines about systems hospital<br />
shutdowns only serve to paint healthcare<br />
as a lucrative target and invigorate<br />
criminal activities to develop industryspecific,<br />
contextually-accurate lures that<br />
yield higher success rates in network<br />
infiltration and malware infections," says<br />
Mark Sangster, VP and industry security<br />
strategist with eSentire. "Attacks today<br />
are more targeted and obtain payments<br />
through extortive negotiations.<br />
Ransomware attacks (malware that locks<br />
and encrypts files and then demands<br />
payment to unlock the files) have evolved<br />
to become denial-of-service attacks to<br />
threat medical service disruption and<br />
patient care interruption."<br />
CRIMINAL PROFITS<br />
Stolen medical records also yield tidy<br />
criminal profits. Whether public service<br />
or private practice, medical records are<br />
sold for 150% more than other personal<br />
data.<br />
"Healthcare organisations also face<br />
financial losses and penalties for<br />
mishandling confidential patient records.<br />
In 2016, the ICO fined Brighton & Sussex<br />
NHS Trust £325,000 for the loss of highly<br />
sensitive data including HIV positive<br />
patients. More recently in 2017, the ICO<br />
fined Lister Hospital, a facility owned<br />
by private health company HCA<br />
International, after patients' fertility<br />
records were not secured. Unencrypted<br />
audio recordings were sent to an Indian<br />
transcription company. The files, which<br />
had been stored on unsecured servers,<br />
were exposed to unrestricted internet<br />
searches." The worrying factor is that<br />
these sorts of fines and events will only<br />
increase with the implementation of<br />
8<br />
computing security March/April 2018 @CSMagAndAwards www.computingsecurity.co.uk
healthcare<br />
more stringent privacy laws, such as the<br />
European Union General Data Protection<br />
Regulation (GDPR) that comes into effect<br />
in May this year (see page 24).<br />
In the US, nearly £17 million was levied<br />
against healthcare providers who failed<br />
to meet the requirements of the Health<br />
Insurance Portability and Accountability<br />
Act (HIPAA) that provides data privacy<br />
and security provisions for safeguarding<br />
medical information, Sangster reveals.<br />
"Most notably, 21st Century Oncology,<br />
which operates nearly 200 treatment<br />
centres across 17 US states, was fined<br />
£1.6 million for exposing 2.2 million<br />
records and further incurred an<br />
additional £850,000 in Corrective<br />
Action Plan (CAP) expenses. Recently,<br />
a Washington area provider, MedStart,<br />
suffered a massive cyber-attack that<br />
crippled operations across 10 hospitals,<br />
250 outpatient clinics, and affected<br />
30,000 employees and hundreds of<br />
thousands of patients."<br />
The costs associated with cyber<br />
breaches go well beyond the immediate<br />
service disruption and clean-up costs.<br />
Victimised or negligent healthcare<br />
providers lose estimated millions to<br />
resulting employee training, enhanced<br />
security services, patient notifications,<br />
public relations fees, solicitor fees and<br />
potential legal actions. Fines and cleanup<br />
represent the proverbial tip of the<br />
fiscal iceberg.<br />
PREVENTING DATA BREACHES<br />
The collaborative nature of medical care<br />
leaves the industry vulnerable to elegant<br />
cyber attacks and data loss at the hands<br />
of employees, adds Sangster. "Much<br />
of this risk can be mitigated using<br />
standardised technologies and practices.<br />
The National Cyber Security Centre<br />
(a part of GCHQ) recently introduced<br />
Network and Information Systems<br />
(NIS) guidelines and objectives and<br />
frameworks for essential services."<br />
Most notable in the NCSC frameworks<br />
is distinction between security<br />
monitoring (section C1) and proactive<br />
event discovery (section C2). "Security<br />
monitoring pertains to known threats<br />
and compliance management through<br />
web and traffic monitoring, and IP<br />
connection reputation. Section C2<br />
addresses the need to detect unknown<br />
attacks through proactive event<br />
discovery. Rightly so, the NCSC breaks a<br />
common misconception that compliance<br />
mechanism will detect all security<br />
threats. Security operations data<br />
commonly reveals billions of events that<br />
are detected inside perimeter defences.<br />
Cyber criminals employ techniques to<br />
evade standard security monitoring<br />
tools, such as anti-virus software or<br />
signature-based intrusion detection<br />
systems, which gives a direct indication<br />
of compromise."<br />
PROACTIVE DISCOVERY<br />
Section C2 is critical to healthcare<br />
providers who must defend against<br />
determined and well equipped cyber<br />
attackers. "Proactive discovery methods<br />
scour indirect, non-signature based<br />
indicators of compromise, including<br />
unusual traffic patterns and deviations<br />
from normal user activity," he further<br />
comments. Other, less direct, security<br />
event indicators may provide additional<br />
opportunities for detecting attacks that<br />
could result in disruption to essential<br />
services. The HIPAA standard also<br />
provides administrative, physical and<br />
technical guidelines around the<br />
protection of protect healthcare<br />
information (PHI). Sangster offers the<br />
following tips:<br />
Assign a designated qualified security<br />
practitioner to build a comprehensive<br />
security programme<br />
Conduct an annual risk assess to<br />
identify vulnerabilities and attack<br />
scenarios<br />
Conduct regular security awareness<br />
training for all employees and<br />
Mark Sangster, VP and industry security<br />
strategist with eSentire<br />
conduct friendly phishing attacks to<br />
test your defences<br />
Encrypt mobile devices and<br />
workstations to reduce the risk of<br />
unauthorised access to data<br />
Design and test an incident response<br />
and service restoration plans.<br />
Cyber criminals are netting massive<br />
financial returns from ransomware and<br />
other crippling cyberattacks against<br />
healthcare providers. "This trend will only<br />
escalate as criminal organisations focus<br />
well-tested attacks on healthcare<br />
organisations and their vendors, and<br />
resulting breaches lead to punitive fines,<br />
lost revenue, and crippled patient care,"<br />
he warns. "Healthcare organisations must<br />
recognise this trend and self-identify as<br />
a cyber target. As the adage goes, an<br />
ounce of prevention is worth a pound of<br />
cure. It's time for the healthcare industry<br />
to invest in prevention through<br />
cybersecurity employee training,<br />
programme development and defences<br />
to extend beyond the identification of<br />
last year's attacks."<br />
www.computingsecurity.co.uk @CSMagAndAwards March/April 2018 computing security<br />
9
IT recycling<br />
I.T. DISPOSAL: SELECTING THE BEST<br />
LEGISLATION REGARDING IT RECYCLING & DISPOSAL, NOT TO MENTION THE FORTHCOMING GDPR<br />
REGULATION, IS COMPLICATED ENOUGH. JEAN-PIERRE NAYLOR, DIRECTOR, COMPUTER DISPOSALS LTD,<br />
OFFERS HIS THOUGHTS ON CHOOSING THE RIGHT I.T. DISPOSAL COMPANY<br />
Thankfully, with a little guidance, you can<br />
make an informed decision and choose<br />
a reputable IT disposal company from<br />
amongst the myriad of so-called 'asset<br />
retirement' companies. The following guide is<br />
by no means exhaustive, but hopefully will<br />
provide a basis to assist you in selecting the<br />
right service provider.<br />
Does the IT recycling company have<br />
appropriate licenses and accreditations?<br />
A waste carrier and environmental permit are<br />
mandatory legal requirements. ISO 9001 and<br />
14001 should be pre-requisites and ISO<br />
27001 highly desirable, as are memberships<br />
of governing bodies. Ask your prospective<br />
recycling company for a list of their licenses<br />
and accreditations.<br />
Also check what measures your IT recycling<br />
company have in place to ensure you both<br />
meet the forthcoming GDPR regulation.<br />
What documentation does it provide?<br />
IT recycling companies must provide you with<br />
both a Hazardous Waste Consignment Note<br />
and a Duty of Care Transfer Note on the day<br />
of collection, which covers you from an<br />
environmental perspective.<br />
Reputable IT recycling companies should<br />
provide you with an asset report providing<br />
you with a detailed breakdown of all<br />
equipment collected, including data<br />
sanitisation certification. Ask for sample<br />
reports, so you can see the level of<br />
information you will receive.<br />
How is your data sanitised?<br />
There have been a number of high profile<br />
cases recently where organisations have fallen<br />
foul of the Data Protection Act by allowing<br />
sensitive and/or privileged information to<br />
reach the public domain. In most cases,<br />
this can be traced back to the IT recycling<br />
company that simply did not take<br />
appropriate measures to erase or safeguard<br />
their client's information.<br />
The only NCSC or CPA (formerly CESG)<br />
approved data erase software is White<br />
Canyon or Blancco. If your prospective<br />
recycling company is not using one of these<br />
software suites, look elsewhere.<br />
Does it use its own vehicles and drivers?<br />
In terms of sensitive data, your equipment<br />
is at its most vulnerable between the point<br />
of collection and return to the recycling<br />
company, yet many companies continue<br />
to use third party carriers to collect and<br />
transport your equipment. Ask your<br />
prospective recycling company to confirm<br />
their transport arrangements. Desirables here<br />
would be companies that use their own<br />
satellite-tracked and CCTV-equipped vehicles<br />
and security vetted drivers.<br />
Does it offer on-site media destruction?<br />
With the increasing number of high-profile<br />
cases where large organisations are being<br />
fined for data breaches, many companies are<br />
finally realising the importance of protecting<br />
their data and ensuring it is sanitised<br />
correctly. An increasing number of companies<br />
are requesting on-site destruction for all<br />
forms of media. Check that your IT disposal<br />
partner can offer this service.<br />
Don't be fooled by a flashy website!<br />
Insist on a site visit. You will be amazed at the<br />
disparity in set-ups. A flashy website can hide<br />
Jean-Pierre Naylor, director, Computer<br />
Disposals Ltd.<br />
a multitude of sins. If the IT recycling<br />
company appears reluctant to offer a site<br />
visit, look elsewhere.<br />
Where should I look for a reputable IT<br />
recycling company?<br />
There are enough established and reputable<br />
IT recycling companies to enable you to make<br />
a safe and informed decision when selecting<br />
your disposal partner. Accrediting bodies,<br />
such as ADISA, are a good source, as<br />
members have to pass strict criteria, in terms<br />
of security and scope of service, although<br />
please bear in mind that not all ADISA<br />
members use their own transport and drivers.<br />
Further information can be found at<br />
www.computerdisposals.com and<br />
www.adisa.global.<br />
10<br />
computing security March/April 2018 @CSMagAndAwards www.computingsecurity.co.uk
Join the IT leaders<br />
taking the simply unified<br />
route to cloud security.<br />
IT Governance is getting more complex, the penalties more worrying<br />
and your competition more cloud-based and agile. WinMagic’s<br />
pervasive, everywhere encryption approach is the way forward.<br />
By simply securing your IT environment from endpoints across any<br />
cloud, you gain a low-cost, low-risk route to compliance and growth<br />
supported by a unique new breed of intelligent key management.<br />
Get in touch today!<br />
Contact our specialists and see how simple securing cloud can be.<br />
Email us today at sales@winmagic.com or call 01483 343020
2018 predictions<br />
AN URGENT CALL TO ARMS<br />
IN THIS SECOND PART OF OUR TOP PREDICTIONS FOR CYBERSECURITY IN 2018, SEVERAL EXPERTS<br />
REVEAL WHAT MAY BE LYING IN WAIT. AND IT DOESN'T ALWAYS MAKE FOR EASY READING<br />
Whatever we may have thought<br />
of the many breaches, hacks<br />
and ransomware attacks that<br />
hit the headlines in 2017, do things look<br />
any better, now that we have some<br />
objective distance between us and those<br />
turbulent 12 months? The truth is 2018<br />
looks like being 'more of the same', with<br />
the rhetoric regarding state-sponsored<br />
cyber assaults only ramping up. Add in a<br />
dusting of former spies being allegedly<br />
poisoned on UK soil and the feeling that<br />
we've slipped between the covers of a<br />
John Le Carré novel only intensifies.<br />
According to the latest research from<br />
Gartner, spending on information<br />
security services will reach $93 billion in<br />
2018, an increase of eight per cent from<br />
2017. Cybersecurity expert Simon Bain<br />
from BOHH Labs suggests that this<br />
increased investment will be required to<br />
address a number of critical challenges<br />
in 2018. This includes rising website<br />
attacks, chatbot technology threats and<br />
the need for greater cyber security<br />
awareness at board-level.<br />
All of which serves to remind us that<br />
can go wrong, will go wrong in<br />
cyberspace… unless, of course, we show<br />
unstinting vigilance in our own<br />
backyards to protect our organisations<br />
from the meteor shower of attacks now<br />
bombarding us across what seems to be<br />
every moment of every day. Feeling safe<br />
may be the outcome of ensuring every<br />
conceivable precaution has been taken.<br />
Being safe is a much different story,<br />
which is only as real as for however long<br />
that lasts.<br />
Read on for our experts' predictions as<br />
to where the greatest dangers may lurk<br />
over the coming several months…<br />
SIMON BAIN, CEO, BOHH LABS:<br />
Addressing ongoing cyber security threats<br />
represents a challenge for any<br />
organisation both practically and<br />
financially, and 2018 will unfortunately<br />
be no different. Looking ahead, there will<br />
be several notable issues that firms will<br />
need to strongly prepare for.<br />
One of the type of attacks that we will<br />
see gain more traction in 2018 is the<br />
website attack. With the growing use of<br />
online services (checking accounts,<br />
merchant accounts and Point-of-Sale<br />
(POS) systems, etc. now going through<br />
the web) the risk of attacks is large and<br />
has the potential to affect any institution<br />
using these services, as it opens access to<br />
institutions' backend databases,<br />
document stores and applications all<br />
12<br />
computing security March/April 2018 @CSMagAndAwards www.computingsecurity.co.uk
2018 predictions<br />
within easy reach. This type of attack is<br />
very hard to find, but it is incredibly easy<br />
for attackers to undertake. Because an<br />
attacker can gain access to the website<br />
via high jacking a user's request, and then<br />
by simply making a small change to the<br />
code to redirect payment information<br />
their way while not stopping the correct<br />
path of the request, it makes it easy for<br />
attackers to get access to critical data<br />
without alerting any red flags.<br />
Critically, the website is no longer just a<br />
marketing tool. It has become a business<br />
tool, and as such, it now needs to be<br />
properly protected from attacks and<br />
placed inside a firewall, and preferably<br />
completely encrypted, so that attackers<br />
are unable to change, manipulate and<br />
delete code to their advantage.<br />
MARKUS BRAENDLE, HEAD OF THE<br />
AIRBUS CYBERSECURITY BUSINESS:<br />
Social media platforms are regularly<br />
being used for the spread of fake news<br />
or the manipulation of public opinion.<br />
But social media can also be used for<br />
sophisticated social engineering and<br />
reconnaissance activities which form the<br />
basis of many attacks on the enterprise.<br />
Criminals and hackers are known to use<br />
these platforms to distribute malware,<br />
push rogue antivirus scams and phishing<br />
campaigns to lure their victims.<br />
Social media provide the medium for<br />
connecting people globally, in the rapid<br />
exchange of ideas, discussions and<br />
debates in our digital world. However,<br />
from an attacker's perspective, social<br />
media have become an easy target<br />
because of the number of non-cyber<br />
security savvy users, and the fact that<br />
these platforms are easy and cost<br />
effective to use. To protect themselves<br />
against social media attacks,<br />
organisations need to implement<br />
enterprise-wide social media security<br />
policies. This includes designing training<br />
programs for employees about social<br />
media usage and creating incident<br />
response plans that coordinate the<br />
activities of the legal, HR, marketing and<br />
IT departments in the event of a security<br />
breach. Attacks on Wireless networks will<br />
increase, as attackers seek to exploit<br />
the Key Reinstallation Attack (KRACK)<br />
vulnerability, first made public in October<br />
2017. The vulnerability can allow an<br />
attacker to intercept and read Wi-Fi<br />
traffic between devices and a WiFi router,<br />
and in some cases even modify the traffic<br />
to inject malicious data into websites.<br />
It could also allow attackers to obtain<br />
sensitive information from those devices,<br />
such as credit card details, passwords,<br />
chat messages and emails.<br />
Concerns about data privacy, the<br />
increasing use of cloud computing,<br />
an increase in data breaches and the<br />
introduction of General Data Protection<br />
Regulation (GDPR) will all contribute to<br />
the emergence of End to End Encryption<br />
(E2EE) as the most effective way for<br />
enterprises wishing to secure their data.<br />
But E2EE will also represent some<br />
challenges to law enforcement, as<br />
criminals continue to use this technique<br />
for espionage and subversion.<br />
TRAVIS FARRAL, DIRECTOR OF<br />
SECURITY STRATEGY, ANOMALI:<br />
Widespread cryptocurrency mining<br />
Cryptocurrency mining will become one<br />
of the major monetisation avenues for<br />
attackers, as more and more attacks and<br />
malware include mining functionality to<br />
generate revenue. In particular, a focus<br />
will be on in-browser mining that will be<br />
the result of website attacks. A simple<br />
few lines of Javascript can cause visiting<br />
browsers to 'mine' cryptocurrency while<br />
on the affected sites. This has been<br />
occurring previously, but not as<br />
widespread as it likely will be in 2018.<br />
An increase in DDoS attacks<br />
The return of mega DDoS attacks via IoTpowered<br />
botnets is likely in 2018. These<br />
have been pretty silent, compared to last<br />
year's attack against Dyn that took down<br />
many commonly used services, but could<br />
come back in a more nefarious way.<br />
The next wave could potentially affect<br />
large swathes of Internet services either<br />
by design or as collateral damage from<br />
another entity being hit, due to the sheer<br />
size of the attack. The wide attack<br />
surface of IoT devices makes them<br />
particularly attractive for botnets.<br />
Encouraging young talent into the<br />
industry<br />
The skills gap is definitely still holding the<br />
industry back. As cyber warfare<br />
increases, governments need to upskill<br />
the next generation of defenders. Figures<br />
around the cyber skills shortage make for<br />
sobering reading.<br />
A report from Frost & Sullivan and (ISC)<br />
found that the global cybersecurity<br />
workforce will have more than 1.5<br />
million unfilled positions by 2020. Both<br />
private and state schools need strong<br />
cyber programs and academies should<br />
look to develop cyber skills in children<br />
from disadvantaged backgrounds. This<br />
will hopefully prevent talented teenagers<br />
being sucked into the dark side.<br />
Stealthy 'fileless' attacks will increase<br />
There is likely to be a move towards<br />
more sophisticated 'fileless' attacks<br />
(malicious scripts that hijack legitimate<br />
software, without installing themselves).<br />
There has already been a sharp rise.<br />
Such attacks are very difficult to stop<br />
with existing endpoint security and<br />
organisations will need to move to the<br />
next generation of defences. The focus<br />
will likely be on other industries outside<br />
of financial services. As the banks<br />
become more resilient in their ability to<br />
profile and learn from actors, less well<br />
protected organisations could be<br />
targeted, as we have seen with Forever<br />
21 and the Jewson attacks in the UK.<br />
www.computingsecurity.co.uk @CSMagAndAwards March/April 2018 computing security<br />
13
2018 predictions<br />
Rik Ferguson, Trend Micro: executives<br />
should prioritise vulnerability<br />
management.<br />
Tod Beardsley, Rapid7: cyber criminals<br />
will continue to spend their efforts on<br />
much softer targets.<br />
More integrated collaboration is required<br />
The likes of NSC and GCHQ are being<br />
effective in their limited remits and are<br />
busy disrupting many adversary groups.<br />
But they need to move faster and cannot<br />
be limited to cybercrime. There must also<br />
be a focus on state-sponsored hacktivism<br />
and other sophisticated attacks, and<br />
levels of awareness and associated<br />
education should be increased<br />
concurrently.<br />
TOD BEARDSLEY, RESEARCH<br />
DIRECTOR, RAPID7:<br />
In an online world dominated by FAMGA<br />
(Facebook, Amazon, Microsoft, Google<br />
and Apple), I expect to see very few<br />
actively exploited vulnerabilities in newly<br />
created and distributed software from<br />
these mature technology vendors. The<br />
hegemony of these companies will ensure<br />
a highly secure operating environment<br />
within each of their areas of dominance.<br />
Occasional issues will surface, of course,<br />
but, on the whole, the computing<br />
environment for the average person will<br />
have a marked lack of 'classic' software<br />
vulnerabilities.<br />
However, this lack of 'new' bugs will not<br />
put cyber criminals out of business. They<br />
will continue to spend their efforts on<br />
much softer targets. These would include<br />
older software stacks that rarely see<br />
regular software updates - multifunction<br />
printers, home and enterprise switches<br />
and routers, and Internet of Things<br />
devices that ship old and unpatchable<br />
software. I also expect to see continued<br />
sophistication on the part of attackers<br />
in their ability to trick, scam and phish<br />
credentials out of users, where either<br />
no bugs, or old bugs, are required for<br />
successful exploitation.<br />
ANDY HARRIS, CHIEF TECHNOLOGY<br />
OFFICER, OSIRIUM:<br />
There were some near misses, in terms of<br />
cloud side data breaches in 2017.Given<br />
the speed of the development of clouds,<br />
we predict a major cloud side breach in<br />
2018. By this, we mean a breach that<br />
happened within cloud security at the<br />
virtual machine hypervisor level, rather<br />
than the level of the operating systems<br />
and containers that the customer<br />
organisation provisioned.<br />
With almost certainty, this breach will<br />
have a pivotal insider element. The net<br />
result will be that cloud employees will<br />
be subject to greater screening and<br />
better salaries. It's pretty obvious who<br />
will pay, but the greater question is<br />
when; our guess is that investmentdriven<br />
land rush will prevail and cloud<br />
prices will remain low until 2019.<br />
As always, data security will revolve<br />
around the people that have access to<br />
privileged accounts. The Privileged Access<br />
Management (PAM) market will continue<br />
to grow, but in different areas; more<br />
insourcing and more dedicated and<br />
outsourced security operation centres.<br />
The cloud market will wake to the need<br />
for PAM and outsourcers in chains of<br />
outsourcing will be reviewing their<br />
contracts, in terms of security.<br />
In our part of the market, tasks will<br />
grow yet again. Privileged Robotic Tasks<br />
already form a large part of security and<br />
network operations for larger customers<br />
and we predict we will see a roll down<br />
effect to the mid-market, where those<br />
with security responsibilities will want to<br />
reduce the number of people that can<br />
use unfettered privileged accounts.<br />
CHARL VAN DER WALT, CHIEF<br />
SECURITY STRATEGY OFFICER,<br />
SECUREDATA:<br />
The 2007 financial crisis brought to light<br />
just how interconnected today's economy<br />
really is. All areas of business were<br />
affected, with exposure to debt being<br />
shared. The cybersecurity industry is no<br />
different. Security 'debt' is a liability or<br />
obligation to pay or render something.<br />
14<br />
computing security March/April 2018 @CSMagAndAwards www.computingsecurity.co.uk
2018 predictions<br />
Technical Debt is already a well<br />
understood concept in software<br />
development - the cost of additional<br />
rework caused by choosing an easy<br />
solution now, instead of using a better<br />
approach that would take longer or<br />
cost more.<br />
This translates well into security; not<br />
as the potential downside resulting<br />
from a decision to compromise, but<br />
as the direct, concrete, real-time and<br />
quantifiable cost of a trade-off between<br />
the best possible approach to securing<br />
something and the more attractive,<br />
practical, convenient or affordable<br />
approach. Security debt can be compared<br />
to monetary debt. If debt is not repaid,<br />
it can accumulate 'interest' and grows<br />
over time until it is repaid.<br />
It sits on a business' balance sheet in<br />
big red letters for all the world to see,<br />
speaking to the very heart of the business<br />
- its value. If business have more liabilities<br />
in the form of security and other debt<br />
than it has assets, then you're bankrupt<br />
and eventually you must fail.<br />
In 2018, we may see the damaging<br />
effects of Security Debt that has been<br />
stacking up in the form of legacy code,<br />
third party libraries and dependencies,<br />
and even architectures used by<br />
companies. This has been building<br />
up for the past 30 years and may<br />
be catastrophic, if the right set of<br />
circumstances come to pass. Companies<br />
have been living on borrowed security<br />
for too long and 2018 may the year<br />
when those debts get collected.<br />
RIK FERGUSON, VP OF SECURITY<br />
RESEARCH, TREND MICRO:<br />
We at Trend Micro are constantly<br />
scouting out future threats that will have<br />
the greatest impact for businesses and<br />
we predict which vulnerabilities will make<br />
the biggest waves in the coming year.<br />
Many devastating cyberattacks in 2017<br />
leveraged known vulnerabilities that<br />
could have been prevented, had they<br />
been patched beforehand. This trend will<br />
continue next year, as corporate attack<br />
surfaces expand and expose more security<br />
holes. While this remains a challenge<br />
for enterprises, executives should<br />
prioritise vulnerability management<br />
as they make 2018 cybersecurity plans,<br />
particularly in the looming shadow of<br />
GDPR implementation.<br />
Ransomware will continue to be a<br />
mainstay, due to its proven success.<br />
There will be an increase in targeted<br />
ransomware attacks, in which the<br />
criminals go after a single organisation<br />
to disrupt operations and force a larger<br />
ransom payout. Business Email<br />
Compromise (BEC) attacks will also<br />
continue to gain popularity with<br />
attackers, as the return on investment<br />
for successful attacks is quite high.<br />
PAUL MCEVATT, SENIOR CYBER THREAT<br />
INTELLIGENCE MANAGER, FUJITSU UK<br />
& IRELAND;<br />
BRYAN CAMPBELL, SENIOR SECURITY<br />
RESEARCHER, FUJITSU UK & IRELAND:<br />
Cyber Threat Intelligence (CTI) can be<br />
defined in many different ways and it can<br />
simply be a threat feed. In the coming<br />
year, it will be important to use threat<br />
intelligence to provide an early warning<br />
system to customers and context to<br />
threats. In short, by doing the hard work,<br />
so customers don't have to be dependent<br />
on the service and level of access,<br />
suppliers can actually block threats before<br />
they have a chance to do any damage.<br />
That threat intelligence, in most cases, is<br />
simply providing guidance on 'protecting'<br />
using basic defences such as patch<br />
management. It's challenging in any<br />
corporate environment expressing the<br />
severity of a vulnerability not only as a<br />
technical risk, but also a financial, human<br />
and business risk. In a perfect world we<br />
would patch all the things, but reality<br />
dictates an alternative practical world.<br />
More often than not, patching a financial<br />
system for a critical vulnerability in Java<br />
the day before end of the financial year<br />
will not whet many appetites through<br />
fear of breaking the system, despite<br />
successful pre-production patching.<br />
Combining vulnerability management<br />
with threat intelligence is a great use case<br />
for protecting corporate environments.<br />
Customers are right to be worried about<br />
the next strain of global cyber-security<br />
incidents, but with last year's Petya and<br />
Wannacry outbreaks, the malware used<br />
an SMB vulnerability for propagation<br />
known months earlier that simply needed<br />
patching. For example, here at Fujitsu, we<br />
actually provided a threat advisory on<br />
that patch to CTI customers three months<br />
before Petya spread. What's more, we<br />
also provided our CTI customers with a<br />
threat advisory of the Apache Struts<br />
vulnerability Equifax was exploited with<br />
several months earlier. We also observed<br />
exploits in the wild for this attack, so<br />
there was clearly a high impact.<br />
The line between cyber security and<br />
politics is distorted with continued reports<br />
of election tampering or breaches of<br />
government agencies and departments.<br />
Investigations surrounding the US Election<br />
will rumble on into 2018 with core<br />
concerns around the manipulation of<br />
security controls and 'sleight of hand'.<br />
There were reports of similar inferred<br />
disruptive activity during the 2017 French<br />
election. In recent years, senior members of<br />
political parties around the world became<br />
all too familiar with concepts such as<br />
'Phishing' and 'Incident Response'.<br />
In the case of the Democratic National<br />
Committee (DNC), the infamous<br />
compromise, which Crowdstrike traced<br />
back to Russia, the monthly cost of the<br />
incident response to remove the attackers<br />
from the DNC network was reportedly<br />
$50k a month.<br />
www.computingsecurity.co.uk @CSMagAndAwards March/April 2018 computing security<br />
15
2018 predictions<br />
Markus Braendle, Airbus CyberSecurity:<br />
criminals will continue to use end-to-end<br />
encryption for espionage and subversion.<br />
Travis Farral, Anomali: cryptocurrency<br />
mining will become one of the major<br />
monetisation avenues for attackers<br />
Nation States continue to grow in cyber<br />
security expertise with the skill, will<br />
and resource to monetise from their<br />
endeavours or disrupt their neighbours.<br />
Not every threat model needs to protect<br />
against adversaries that seek to<br />
destabilise a nation, however, with the<br />
increasing adoption of digital services<br />
and frequent attribution of cyber-attacks<br />
to Nation States, it is feasible to suggest<br />
attacks against commercial entities to<br />
support political objectives will only<br />
continue to increase.<br />
ADRIAN DROZD, FROST & SULLIVAN<br />
DIGITAL TRANSFORMATION<br />
RESEARCH DIRECTOR:<br />
The managed security services (MSS)<br />
market in Europe, Middle East and<br />
Africa (EMEA) is experiencing significant<br />
transformation. While new market<br />
entrants with network-based MSS<br />
propositions and remediation capabilities<br />
are disrupting the MSS provider (MSSP)<br />
landscape, mature technologies such as<br />
cloud migration, enterprise mobility, and<br />
always-on availability are boosting MSS<br />
adoption. These factors have stoked<br />
demand for expert security professionals,<br />
who are in short supply. Partly in<br />
response to this human resource crunch<br />
and the need to ensure compliance with<br />
Europe-wide General Data Protection<br />
Regulations (GDPR), businesses and<br />
public entities of all sizes are turning<br />
to MSSPs.<br />
Frost & Sullivan's research, 'EMEA<br />
Managed Security Services Market,<br />
Forecast to 2021', finds that the market<br />
was valued at $4.27 billion in 2016 and<br />
is expected to reach $8.26 billion by<br />
2021 at a compound annual growth rate<br />
(CAGR) of 14.1 percent during 2016<br />
through 2021. The research analyses<br />
current market dynamics, external<br />
challenges, drivers, restraints, forecast<br />
and trends. Market share and competitive<br />
analysis of key players such as BT, Orange<br />
Cyberdefense, IBM, HP Enterprise, Atos,<br />
Telefonica, T-Systems and Verizon are<br />
provided. Customers want solutions that<br />
solve problems, rather than mere alerts to<br />
a potential problem. Therefore, MSSPs that<br />
offer consulting, professional and technical<br />
services could well outpace the overall<br />
market. The key to longevity and success in<br />
an agile MSSP environment is staying<br />
ahead of the competition by:<br />
Capturing the next wave of highervalue<br />
MSS. The two growth MSS<br />
segments in the next five years are<br />
threat intelligence, and research and<br />
detection services<br />
Growing the midsized market segment<br />
with the right pricing strategy<br />
Following a customer-centric approach<br />
by delivering solutions that meet<br />
evolving demands<br />
Adopting technology-led approaches<br />
to service delivery, such as unburdening<br />
tedious tasks through automation and<br />
a collaborative solution approach.<br />
Although the media has extensively<br />
covered security breaches, many<br />
enterprises still believe that they will not be<br />
subject to targeted attacks and, hence, do<br />
not require protection against advanced<br />
threats. This approach to security has<br />
curtailed the adoption of MSS in the EMEA<br />
region - and is one that will doubtless<br />
change as the threat landscape evolves.<br />
A FINAL THOUGHT… FROM RICHARD<br />
PARRIS, INTERCEDE CEO AND<br />
CHAIRMAN:<br />
When are organisations, their customers<br />
and regulators finally going to do<br />
something about the parlous state of<br />
information security? The black hats have<br />
had it their way for far too long, but 2018<br />
could well be the year that the pendulum<br />
swings back. On the back of some truly<br />
momentous incidents over the past 12<br />
months, many stakeholders are now saying<br />
"enough is enough", and that could spell<br />
some big changes ahead, with the concept<br />
of digital identity front and centre.<br />
16<br />
computing security March/April 2018 @CSMagAndAwards www.computingsecurity.co.uk
inside view<br />
EVERYONE IS AT RISK<br />
FROM SPEAR PHISHING TO RANSOMWARE AND THE EVER-PRESENT THREAT OF BOTS, COMPANIES OF ALL<br />
SIZES HAVE REASON TO LOSE SLEEP AT NIGHT. ELIZABETH SHELDON, CHAIRMAN, EVIDENCE TALKS,<br />
CONSIDERS WHAT THAT MEANS FOR ORGANISATIONS EVERYWHERE<br />
Cybercrime targeted at small<br />
businesses is increasing at an<br />
alarming rate and it's a problem<br />
that's not about to go away. What's<br />
more, the threat is increasing in scope,<br />
as well as size.<br />
Gone are the days when having a<br />
relatively unknown brand used to work<br />
in favour of smaller organisations to<br />
ward off hackers. These days, it would<br />
be wrong to assume that hackers will<br />
only pursue well recognised companies<br />
with huge volumes of data.<br />
As smaller businesses are far less likely<br />
to have security personnel and<br />
technologies in place that can efficiently<br />
detect and respond to an attack, it's easy<br />
to see why hackers are shifting their<br />
focus. The reward may well be smaller,<br />
if a SME is breached on an individual<br />
basis and this perhaps explains why<br />
many hackers are now leveraging attacks<br />
against smaller businesses in their<br />
multitudes.<br />
According to recent data, almost 50%<br />
of cyber attacks are aimed at the small<br />
business - a number that's likely to<br />
increase in 2018. For many small<br />
businesses, cyber security competes with<br />
other day-to-day concerns for time and<br />
resource, but better measures must be<br />
put in place to ensure they are less<br />
vulnerable to attack.<br />
As per their own structure and business<br />
model, every business faces different<br />
risks. Some will be heavily reliant on<br />
their e-commerce systems, while others,<br />
for example, may be more severely<br />
impacted by the loss of customer data,<br />
procurement systems or their intellectual<br />
property. The onus for the SME,<br />
therefore, lies in evaluating how cyber<br />
risk can be mitigated by prioritising<br />
spend in the areas that matter most to<br />
them.<br />
Long gone are the days when small<br />
businesses can view themselves as too<br />
small or insignificant for cyber security.<br />
Defending your corporate reputation is<br />
paramount and cannot be overlooked in<br />
the ongoing drive to retain your<br />
competitive edge.<br />
While a lot of attention is focused on<br />
external threats, it's now emerging that<br />
one of the single, greatest causes of<br />
information theft, loss or attack actually<br />
comes from within business walls. Over<br />
the past few years, data leaks and other<br />
news events have brought insider threats<br />
to the forefront of public attention and<br />
yet most companies, both large and<br />
small, seem to lack the motivation and<br />
capabilities to protect themselves from<br />
the malicious insider.<br />
With a lack of appropriate internal<br />
defences increasing exposure to fraud,<br />
the opportunities for miscreants are now<br />
more prevalent than ever before. For<br />
example, for those intent on stealing<br />
or causing damage, phishing has turned<br />
into a relatively straightforward exercise,<br />
due to the ease with which good<br />
phishing kits can be purchased, often<br />
Elizabeth Sheldon, Chairman, Evidence<br />
Talks.<br />
with the relevant technical support, on<br />
the black market. It's even possible to<br />
purchase ransomware-as-a-service in<br />
underground markets.<br />
Fortunately, the rise of analytics and<br />
digital forensics technologies make the<br />
identification of insider threats easier<br />
and less intrusive. Alongside adoption of<br />
the appropriate technologies, however,<br />
businesses need to gain accreditation<br />
to the Cyber Essentials (CE) scheme,<br />
have an awareness of what to look for<br />
and focus more on their security efforts<br />
to achieve best outcomes and the<br />
reassurance that robust cyber security<br />
protocols will bring.<br />
www.computingsecurity.co.uk @CSMagAndAwards March/April 2018 computing security<br />
17
smart cities<br />
RISK AND REWARD IN THE BIG CITY<br />
BACK IN THE 1960S, DISNEYLAND HAD A RIDE CALLED 'UTOPIA'. IT WAS A GLIMPSE INTO THE FUTURE OF<br />
HUMAN CITIES AND GAVE US A TASTE OF WHAT SMART CITIES COULD BE. ALASTAIR HARTRUP, GLOBAL CEO,<br />
NETWORK CRITICAL, TAKES UP THE STORY<br />
Of course, everything on the<br />
Disneyland ride Utopia, from its<br />
stoplight-less streets and smooth<br />
traffic control, was pre-programmed. It was<br />
just a theme park ride, after all. However,<br />
this shows that humanity has had the idea<br />
of a smart city on its mind for a long time.<br />
This idea is something we are only recently<br />
able to make into reality. Just like the ride,<br />
smart cities help to create a 'utopia' where<br />
life is streamlined and less frustrating.<br />
Unfortunately, as with most good things,<br />
there are plenty of problems that could ruin<br />
the dream for millions and these are caused<br />
by the threat of cyber-attacks.<br />
2018 is now well underway, but already<br />
many are expecting it to be the year of smart<br />
cities. Back in 2016, global city population<br />
was at an all-time high and commute<br />
congestion was as bad as it had ever been.<br />
However, with the introduction of Internet<br />
of Things (IoT) devices, within both the city<br />
and vehicles themselves, we have begun to<br />
slowly make driving in the city a much easier<br />
experience, just like the way Utopia made it<br />
feel all those years ago.<br />
These devices provide everything from<br />
navigational advice and real-time traffic<br />
alerts to alternative route suggestions, based<br />
on prevailing traffic conditions. We can<br />
rideshare, bike share and plan public<br />
transportation routes, and pay tolls with<br />
smartphones. Internet connectivity via<br />
personal devices is only the first step in a<br />
new wave of intelligent urban transportation<br />
technology.<br />
Centralised urban technology hubs and<br />
associated apps are being developed to<br />
provide a wide range of services. One<br />
example is the introduction of card scanners<br />
on public transport, simplifying travel<br />
payment and removing the issue of not<br />
having exact change for the fare.<br />
Centralising and synchronising traffic signals<br />
helps to smooth traffic flow, provide quicker<br />
response times for emergency vehicles and<br />
keep buses on schedule. Parking sensors<br />
have even been installed that will alert<br />
smartphone users to open parking spaces.<br />
To have IoT devices work to maintain a<br />
18<br />
computing security March/April 2018 @CSMagAndAwards www.computingsecurity.co.uk
smart cities<br />
smart city, it needs to collect and analyse<br />
personal data from the users, so that it can<br />
tell what works and what does not. To be<br />
as effective as possible, they need to collect<br />
data from users about their movements,<br />
peak traffic times, transportation mode<br />
preferences, streetlight data, traffic camera<br />
data, payment options and more.<br />
All this information then needs to be<br />
stored somewhere, whether this is a Cloud<br />
server or under the control of a municipal<br />
IT department. Doing this is a necessity,<br />
but the centralisation of information and<br />
control of an entire municipal<br />
transportation system is putting a lot of<br />
eggs in a single basket. As we've seen,<br />
though, putting so much precious data in<br />
one location is an invitation for trouble.<br />
2017 saw a rise in cyber-attacks that<br />
purposely target private data, whether<br />
to use as ransom or to release online and<br />
cause chaos. Uber and Forever 21 were<br />
just two of the many companies to suffer<br />
massive data breaches in 2017 and, in<br />
recognition of the very real risks to people's<br />
personal information, 2018 sees the<br />
introduction of the GDPR [in May], a new<br />
regulation that will force companies to<br />
take more responsibility for the protection<br />
of customer data [see page 24].<br />
If enterprises want to continue the<br />
upkeep of smart cities, then the basket that<br />
holds all this information must be designed<br />
for maximum security, controlled access<br />
and limited information portability.<br />
According to Von Welch, director of the<br />
Center for Applied Cyber Security Research<br />
at Indiana University: "We have a lot of<br />
companies making new devices for the<br />
urban Internet of Things that have not<br />
made computers or written software<br />
before." This is a critical warning to<br />
intelligent urban traffic planners. Get the<br />
IT security team involved early. There is<br />
great technology available to help protect<br />
and defend large centralised networks.<br />
Robust security requires many specialised<br />
appliances, so an intelligent connectivity<br />
solution should also be part of the initial<br />
plan.<br />
Alastair Hartrup, global CEO, Network<br />
Critical.<br />
Without properly planned network<br />
protection and rapid attack remediation, the<br />
commerce, movement and safety of entire<br />
cities could be vulnerable to a malicious<br />
breach. Traffic signals could be manipulated;<br />
electronic road signs could be hacked to<br />
provide misinformation; emergency<br />
responders could be blocked from trouble<br />
spots; funds could be stolen; or bank<br />
accounts compromised.<br />
We've seen this already: in 2014, security<br />
researchers at the University of Michigan<br />
were able to hack traffic lights of nearly 100<br />
intersections that they found to have no<br />
security controls at all. This hack was just an<br />
experiment to point out the flaws; imagine if<br />
it was performed by someone with malicious<br />
intent.<br />
This is all scary stuff, but not impossible to<br />
manage. If proper network visibility, threat<br />
landscape reduction, data loss protection,<br />
data backup and employee training are<br />
planned and implemented early on, then<br />
Utopia may, in fact, be possible, without<br />
opening the door to a municipal apocalypse.<br />
www.computingsecurity.co.uk @CSMagAndAwards March/April 2018 computing security<br />
19
otnets<br />
DEADLY GAME OF HIDE 'N' SEEK<br />
BITDEFENDER RESEARCHERS HAVE UNCOVERED AN EMERGING BOTNET THAT USES ADVANCED<br />
COMMUNICATION TECHNIQUES TO EXPLOIT VICTIMS AND BUILD ITS INFRASTRUCTURE<br />
Anew bot, dubbed HNS, has been<br />
intercepted by Bitdefender's IoT<br />
honeypot system, following a<br />
credentials dictionary attack on the<br />
Telnet service. The bot was first spotted<br />
in early January this year, then faded<br />
away in the following days, only to reemerge<br />
10 days later in a significantly<br />
improved form.<br />
"The HNS botnet communicates in a<br />
complex and decentralised manner, and<br />
uses multiple anti-tampering techniques<br />
to prevent a third party from hijacking/<br />
poisoning it," explains Bogdan Botezatu,<br />
senior e-threat analyst at Bitdefender.<br />
The bot can perform web exploitation<br />
against a series of devices via the same<br />
exploit as Reaper and other<br />
vulnerabilities against networking<br />
equipment. It embeds a plurality of<br />
commands, such as data exfiltration,<br />
code execution and interference with<br />
a device's operation.<br />
The bot features a worm-like spreading<br />
mechanism that randomly generates a<br />
list of IP addresses to get potential<br />
targets. It then initiates a raw socket SYN<br />
connection to each host in the list and<br />
continues communication with those<br />
that answer the request on specific<br />
destination ports (23 2323, 80, 8080).<br />
Once the connection has been<br />
established, the bot looks for a specific<br />
banner ("buildroot login:") presented by<br />
the victim. If it gets this login banner,<br />
it attempts to log in with a set of<br />
predefined credentials. If that fails,<br />
the botnet attempts a dictionary attack<br />
using a hardcoded list."<br />
VICTIM EXPLOITATION<br />
Once a session is established with a new<br />
victim, the sample will run through<br />
a 'state machine' to properly identify<br />
the target device and select the most<br />
suitable compromise method. "For<br />
example, if the victim has the same LAN<br />
as the bot, the bot sets up TFTP server to<br />
allow the victim to download the sample<br />
from the bot," adds Botezatu. "If the<br />
victim is located on the internet, the bot<br />
will attempt a specific remote payload<br />
20<br />
computing security March/April 2018 @CSMagAndAwards www.computingsecurity.co.uk
otnets<br />
delivery method to get the victim to<br />
download and run the malware sample.<br />
These exploitation techniques are<br />
preconfigured and are located in a<br />
memory location that is digitally signed<br />
to prevent tampering. This list can be<br />
updated remotely and propagated<br />
among infected hosts."<br />
The samples identified in Bitdefender's<br />
honeypots in early January revolved<br />
around IP cameras manufactured by a<br />
Korean company. "These devices seemed<br />
to play a major role in the botnet, as, out<br />
of the 12 IP addresses hardcoded in the<br />
sample, 10 used to belong to Focus H&S<br />
devices. The new version, observed on<br />
January 20, dropped the hardcoded IPs."<br />
Like other IoT bots, the newly<br />
discovered HNS bot cannot achieve<br />
persistence and a reboot would bring<br />
the compromised device back to its clean<br />
state. It is the second known IoT botnet<br />
to date, after the notorious Hajime<br />
botnet, that has a decentralised, peer-topeer<br />
architecture.<br />
"However, if in the case of Hajime, the<br />
p2p functionality was based on the<br />
BitTorrent protocol. Here, we have a<br />
custom-built p2p communication<br />
mechanism. The bot opens a random<br />
port on the victim and adds firewall rules<br />
to allow inbound traffic for the port. It<br />
then listens for connections on the open<br />
port and only accepts the specific<br />
commands described below. Our initial<br />
look at the sample revealed an elliptic<br />
curve key inside the file that is used<br />
to authenticate the command which<br />
updates the memory zone where<br />
configuration settings are stored, to<br />
prevent infiltration or poisoning attempts<br />
against the botnet."<br />
CHATBOT MENACE<br />
Meanwhile, a warning has been issued<br />
about another kind of 'bot' - Chatbots.<br />
According to security expert BOHH Labs,<br />
they can also pose a serious security<br />
threat. "Chatbots are quickly becoming<br />
the interface of choice for many<br />
organisations. In fact, a recent survey<br />
conducted by Oracle revealed that 80 per<br />
cent of businesses want chatbots by<br />
2020. While the advances in Artificial<br />
Intelligence (AI) and mobile technology<br />
have created a new set of tools for<br />
brands to communicate with, the<br />
technology itself has yet to reach<br />
a mature state and is consequently<br />
strongly vulnerable to cyberattacks,"<br />
cautions Simon Bain, cybersecurity expert<br />
and CEO, BOHH Labs.<br />
Current bot solutions are not entirely<br />
secure and can create open passages<br />
for cyber criminals to access the data<br />
flowing through chatbot's interface. In<br />
essence, this gives cyber attackers direct<br />
access to an organisations' network,<br />
applications and databases.<br />
As Bain explains: "While bot technology<br />
has improved drastically in recent years,<br />
for maximum security, chatbot<br />
communication should be encrypted<br />
and chatbots should be deployed only on<br />
encrypted channels. This can be easily set<br />
up on an organisation's own website;<br />
but, for brands that use chatbots<br />
through third-party platforms such as<br />
Facebook, the security features are<br />
decided by the third party's own security<br />
branch, which means the organisation<br />
does not have as much control over the<br />
security features on the chatbot. Until<br />
public platforms offer end-to-end<br />
encryption in their chatbots, businesses<br />
should remain cautious."<br />
One of the biggest advantages in using<br />
chatbots is that they are a cheaper<br />
solution to customer service. They can<br />
serve and reach customers in a way that<br />
would otherwise require a tremendous<br />
amount of time and resources. This is<br />
an area where chatbots are gaining<br />
momentum, but instead of bots<br />
Bogdan Botezatu, Bitdefender: the bot<br />
can perform web exploitation against<br />
devices via the same exploit as Reaper.<br />
replacing entire customer service teams,<br />
organisations are working with them in<br />
tandem, in order to improve customer<br />
satisfaction.<br />
However, as chatbots seek to collect<br />
information from users, the information<br />
that is stored and the metadata must be<br />
properly secured. "When running a<br />
chatbot, organisations must consider<br />
how the information is stored, how long<br />
it's stored for, how it's used and who has<br />
access to it," Bain says. "This is especially<br />
important for highly regulated industries,<br />
such as finance, that will deal with<br />
sensitive customer information."<br />
While there are clear advantages to<br />
integrating chatbot technology as a new<br />
communication tool, if companies aren't<br />
made aware of the potential security<br />
risks, confidential data will be accessible<br />
by any determined hacker. "Additionally,<br />
attackers may be able to repurpose<br />
chatbots to harvest sensitive data from<br />
unsuspecting customers." he concludes.<br />
www.computingsecurity.co.uk @CSMagAndAwards March/April 2018 computing security<br />
21
tech trends<br />
A TASTE OF THINGS TO COME<br />
RAHUL POWAR AND RANDAL PINTO, CEO AND COO OF LONDON-BASED TECH START-UP RED SIFT,<br />
SINGLE OUT THE THREE TECH TRENDS THAT THEY BELIEVE WILL DOMINATE IN 2018<br />
Randal Pinto, Red Sift.<br />
Last year saw wave after wave of tech<br />
news hitting the headlines. Whether it<br />
was documenting a huge technological<br />
advancement, the publication of a high-risk<br />
vulnerability or the announcement of a gamechanging<br />
regulation, nowhere was this more<br />
evident than in the cryptocurrency, Artificial<br />
Intelligence (AI) and cyber security arenas.<br />
Here is our forecast for how these trends will<br />
come to fruition this year.<br />
OPTIMISE BUSINESS PROCESSES WITH<br />
ARTIFICIAL INTELLIGENCE<br />
The Economist's World in 2018 predicts the<br />
next twelve months to be a 'landmark year' for<br />
Artificial Intelligence. Continued huge leaps in<br />
innovation are without question. However,<br />
what we will also see this year, is that AI will<br />
lose some of its shine and become part of the<br />
everyday technology toolbox all organisations<br />
use to automate arduous data-driven tasks.<br />
One key trend we'll see is AI starting to write<br />
AI. This is the idea of deep neural networks<br />
designing and optimising other deep neural<br />
Rahul Powar, Red Sift<br />
networks, and will become mainstream in<br />
machine learning. We won't really be any<br />
closer to general-purpose AI, but hyperbolic<br />
industry commentators will no doubt spin<br />
‘AI writing AI’ as the start of it.<br />
CONSIDER CRYPTOCURRENCY<br />
Cryptocurrency has shot to fame in the past<br />
few years and certainly became part of the<br />
business vernacular last year. However, this<br />
digital currency remains at the mercy of<br />
criminals - as 2017 came to a close, we saw<br />
reports of a hack attack in which $64 million<br />
in bitcoin had been stolen. Guidelines are few<br />
and far between, and regulators will have to<br />
play catch-up this year. However, putting a<br />
leash on a global, decentralised mechanism<br />
will not be a straightforward task and some<br />
stakeholders may resist being locked down.<br />
That said, we'll also see broader adoption<br />
of blockchain in the enterprise - finance and<br />
insurance companies have already started<br />
adopting this digital framework. IBM and<br />
Microsoft, too, have joined the fray, offering<br />
Blockchain as a service (BaaS) solutions, which<br />
will see wider adoption across other industries<br />
including energy, retail, real estate and the<br />
public sector.<br />
SOLIDIFY YOUR CYBERSECURITY<br />
Although everyone knows what they should<br />
be doing for GDPR, reports are already<br />
suggesting that not only are millions of SMBs<br />
in the UK still not compliant but, even as we<br />
start off the New Year, they haven't begun<br />
preparing for the EU-mandated regulation.<br />
Until we see a landmark GDPR case, with an<br />
organisation facing a headline-grabbing fine,<br />
firms will probably continue to keep the<br />
status quo, with minimum measures in place.<br />
Many firms cite massive costs and resources<br />
required as barriers to making the necessary<br />
changes.<br />
2018 will see a raft of companies declaring<br />
breaches and opportunistic hackers ramping<br />
up their attacks on vulnerable organisations.<br />
This year, we will also observe a maturity in<br />
quantum computing which will threaten<br />
encryption and computing security - the<br />
concern being that this level of computing<br />
power will crack previously 'unbreakable'<br />
passwords and encryption.<br />
ABOUT RED SIFT AND ONDMARC<br />
Red Sift is a London-based Platform as a<br />
Service (PaaS) startup founded in 2015 by<br />
serial entrepreneurs Rahul Powar and Randal<br />
Pinto. The cloud-based platform offers both<br />
businesses and individuals a powerful<br />
dashboard of tools, plugging into various<br />
data sources in order to receive personalised,<br />
actionable insights. OnDMARC is the first<br />
product built on the Red Sift platform; it's an<br />
intuitive cloud-based cybersecurity tool that<br />
helps organisations of all sizes and specialisms<br />
secure their email domains against<br />
impersonation.<br />
22<br />
computing security March/April 2018 @CSMagAndAwards www.computingsecurity.co.uk
Cyber Security Managed Services<br />
Brookcourt Solutions manage services across<br />
Cyber Security and Networking Technologies to secure<br />
companies across all verticals from vunerabilities and threats.<br />
We consolidate multiple partner feeds from around the world<br />
into a single platform, then provide skilled analysts in-house to<br />
extract that data to provide timely, actionable cyber intelligence<br />
for our clients.<br />
How secure is your brand?<br />
Contact us: marketing@brookcourtsolutions.com<br />
C y b e r S u r v e i l l a n c e • S e c u r i t y • N e t w o r k i n g • C o n s u l t a n c y • M a n a g e d S e r v i c e s<br />
Multi Award Winning<br />
For more information contact Brookcourt Solutions<br />
t: +44 (0) 1737 886 111 www.brookcourtsolutions.com
data regulations<br />
IT'S TIME TO BE VERY READY!<br />
WHEN THE GENERAL DATA PROTECTION REGULATION (GDPR) COMES INTO FORCE THIS MAY,<br />
IT WILL OVERHAUL HOW ORGANISATIONS STORE, SECURE AND MANAGE THEIR CUSTOMERS' DATA.<br />
SWINGEING PENALTIES AWAIT THOSE WHO FAIL TO COMPLY<br />
When Cisco launched its first Privacy<br />
Maturity Benchmark Study in<br />
February this year, it found that<br />
74% of privacy-immature organisations<br />
experienced losses of more than £350,000<br />
in 2017 caused by data breaches. The<br />
countdown to GDPR has seen organisations<br />
investing in resources and processes to meet<br />
the new standards, states the report.<br />
However, with an increasing number of data<br />
breaches reported, vendors are asking more<br />
questions about the products they buy and<br />
the organisations they partner with, states<br />
Cisco. "This is causing significant delays in<br />
the buying cycle, due to concern about how<br />
data is captured, transferred, stored, and<br />
erased."<br />
Cisco's research highlights the ways in<br />
which privacy maturity not only causes<br />
significant sales delays, but also its cybersecurity<br />
effectiveness:<br />
Two-thirds of businesses report sales<br />
delays caused by customer data privacy<br />
concerns - customers are increasingly<br />
concerned about whether products<br />
and services they buy will provide<br />
appropriate privacy protections that<br />
will meet GDPR standards<br />
Privacy-mature companies experience<br />
fewer breaches and smaller losses from<br />
cyberattacks - 74% of privacy-immature<br />
organisations experience losses of more<br />
than £350,000 last year caused by data<br />
breaches, compared with only 39% of<br />
privacy-mature organisations.<br />
GDPR DAY LOOMS<br />
Data breaches are certainly having a massive<br />
impact. As Ian Kilpatrick, EVP Cyber Security<br />
for Nuvias Group, points out: "The General<br />
Data Protection Regulation (GDPR) will<br />
overhaul how organisations store, secure<br />
and manage their customers' data. EU<br />
citizens will have extended rights that<br />
include the right to know what information<br />
is held about them, the right for that data<br />
to be removed, the right to data portability,<br />
and the right to be informed if there is<br />
a data breach. This data is known as PII<br />
(Personally Identifiable Information)<br />
"Alongside that, the Network and<br />
Information Systems (NIS) directive applies<br />
to operators of essential services, such as<br />
water, energy, transport and health<br />
providers and is aimed at ensuring they<br />
safeguard data against cyber-attacks. Like<br />
GDPR, the penalties for non-compliance are<br />
extremely high."<br />
Yet according to research published<br />
recently by the Department for Digital,<br />
Culture, Media and Sport (DCMS), only<br />
38% of UK businesses said they had heard<br />
of GDPR - and among those that were<br />
aware of it, just a little more than a quarter<br />
have made any changes in readiness for the<br />
new regulations.<br />
"However, it's not too late to do something,"<br />
states Kilpatrick. "The authorities know<br />
compliance is an ongoing process and want<br />
to see organisations showing willingness to<br />
comply. Understanding the data assets your<br />
24<br />
computing security March/April 2018 @CSMagAndAwards www.computingsecurity.co.uk
data regulations<br />
organisation collects, holds and processes is<br />
the essential step in the planning stages to<br />
GDPR readiness. Once you have identified all<br />
the data types and sources you hold, you<br />
need to understand where it is stored and<br />
who can access it. Printed copies should be<br />
securely stored, with regular reviews to<br />
ensure the copies are still required. If not,<br />
securely destroy them."<br />
Electronic storage within a structured<br />
database should be relatively easy to<br />
recognise, maintain and protect. "The larger<br />
problem is unstructured data and knowing<br />
where PII, or personally sensitive<br />
information, is stored. Data discovery tools<br />
can search all mappable drives to find<br />
sensitive files (.docx, .xlsx, .pdfs etc) that<br />
may contain the data that you are searching<br />
for - email addresses, phone numbers, credit<br />
card details, National Insurance numbers<br />
etc," he points out. "Once you know where<br />
your unstructured sensitive files are stored,<br />
move them to a central repository from<br />
which you can defend access," he advises.<br />
"Set up processes and procedures to be able<br />
to respond in a timely fashion to Data<br />
Subject Access Requests (DSARs). Finding a<br />
Citizen within your paper records will<br />
require a physical search. Finding a Citizen<br />
within your CRM or other database should<br />
be accommodated from the application.<br />
The same tool that helped your organisation<br />
find sensitive files ought to discover specific<br />
subjects within unstructured data, allowing<br />
an organisation the ability to respond to<br />
DSARs within the 30 days prescribed."<br />
BALANCING ACT<br />
Too often, companies have to balance data<br />
protection risks with the pressure to move<br />
fast. GDPR tips the scales towards data<br />
privacy, meaning global businesses have to<br />
rethink how they provide secure access to<br />
data throughout their organisation,<br />
according to Jes Breslaw, director of<br />
strategy, EMEA at Delphix. "We recommend<br />
the following tips for businesses when it<br />
comes to securing data," he says:<br />
Start learning about DataOps - companies<br />
should be investigating the idea of DataOps.<br />
This approach assigns dedicated people and<br />
tools to manage and secure data across an<br />
organisation. DataOps enables data<br />
operators to know exactly what data is<br />
where, to be able to secure (mask) data that<br />
is sensitive and to ensure that data<br />
consumers still have access to the data they<br />
require, when they need it.<br />
Govern data access - DataOps and Dynamic<br />
Data Platforms enable you to centrally<br />
control all non-production copies of your<br />
data and mask data at the same time. Data<br />
operators can manage who has access to<br />
STARTLING LACK OF PREPARATION FOR GDPR<br />
A recent survey of 118 professionals in North America by UBM showed that 98% of respondents view data governance as important, but only<br />
6% said their firms were fully prepared for GDPR compliance.<br />
Key articles within the GDPR include what to do if a data breach occurs and how quickly an organisation must report it, the requirement of<br />
appointing a data privacy officer and that any organisation anywhere in the world that processes EU data must be GDPR compliant.<br />
"For organisations that have embarked on becoming compliant, the key challenge is pulling together all of the disparate technologies and<br />
systems that need to be integrated, in order to meet what the actual regulation states," says Juliet Okafor, SVP of Global Security Solutions at<br />
Fortress Information Security. "Oftentimes, data resides in various systems with differing access policies. Organisations need to understand where<br />
this data is, how they use it, and then track and monitor the controls they have in place as part of their overall GDPR compliance requirements."<br />
The complexities involved with GDPR compliance mostly revolve around the shared risks that are across the organisation, and typically involves<br />
procurement, legal, third party risk, cybersecurity, privacy and enterprise risk teams, as well as senior management. "All of those stakeholders are<br />
a part of GDPR compliance and each has a shared piece of the GDPR mandate," she adds. "Collaboration across those groups solves GDPR<br />
compliance and the need for agreement."<br />
However, organisations tend to have issues with regard to what happens to a customer's data. "That is, what security controls can be put in<br />
place that protect the data, but also allow the organisation to use the data to make decisions on future products. The organisation is typically<br />
attempting to limit or remove the risk associated with either a compromise or breach of data they've collected."<br />
GDPR compliance is complex and will impact many departments. Integrating multiple technology solutions and update internal processes and<br />
procedures is vital. "Organisations should look for solutions and partners that will help to solve GDPR-related issues and find someone who can<br />
articulate a clear vision to meet the implementation deadline," Okafor concludes.<br />
www.computingsecurity.co.uk @CSMagAndAwards March/April 2018 computing security<br />
25
data regulations<br />
Ian Kilpatrick, EVP Cyber Security for<br />
Nuvias Group: it's not too late to do<br />
something.<br />
James Wickes, CEO and co-founder,<br />
Cloudview: organisations with old<br />
cameras or cameras not manufactured<br />
in the UK should review their systems.<br />
what data, for how long, and when. Data<br />
consumers can access and use data<br />
independently, while administrators retain<br />
full control over masking, privileges and<br />
physical resources.<br />
Treat all data equally - most security teams<br />
focus on the protection of data in a<br />
production environment, but the same<br />
budgets and security are often not afforded<br />
to non-production copies of data that are<br />
used in test, reporting, training and analytic<br />
systems. The danger is that non-production<br />
data represents approximately 80% of an<br />
organisation's total data and their most<br />
vulnerable attack surface. By treating nonproduction<br />
data as you would production<br />
data, then you can mandate policies that<br />
reduce the risk of data breaches in all<br />
environments - production and nonproduction.<br />
Use technology shortcuts - the deadline for<br />
compliance with GDPR is 25 May and you<br />
will never protect all your sensitive data in<br />
time by doing things the same way you<br />
always have. Modern data masking<br />
solutions have database profiling tools that<br />
scan tables and fields to detect confidential<br />
information, such as email addresses, credit<br />
card numbers or patient records. Some even<br />
recommend masking algorithms, which<br />
dramatically cut down the time it takes to<br />
build and enforce data masking.<br />
Stop reinventing the wheel - define security<br />
policies once, rather in siloes or at the<br />
project level, and, if possible, apply them<br />
everywhere. Set enterprise security policies<br />
to ensure that the right data is protected,<br />
using the right controls and masking<br />
algorithms. Policies must then be applied<br />
consistently, regardless of the data source,<br />
to support compliance with regulations<br />
such as HIPAA, GDPR and more.<br />
QUICK WINS<br />
Encrypting known sensitive data is<br />
recommended as a 'quick win' by Colin<br />
Tankard, managing director, Digital<br />
Pathways. "This is the only technology that<br />
is 'called out' in the GDPR rules. 'Awareness'<br />
is vitally important. Decision makers and<br />
key staff should be aware of GDPR. If not,<br />
companies should quickly instigate an<br />
awareness campaign to all staff. This<br />
provides key evidence of GDPR compliance<br />
by the organisation."<br />
Ensure that subject access requests are<br />
dealt with swiftly and efficiently. "There are<br />
current rules with regard to individuals<br />
and how companies should respond to<br />
a request to show what information is held.<br />
GDPR extends this to areas such as your<br />
data retention periods and the right to have<br />
inaccurate data corrected within 30 days,<br />
at zero cost to the requestor," he states.<br />
Other areas Tankard identifies that can be<br />
handled with reasonable ease include:<br />
Accountability: GDPR includes provisions<br />
that promote accountability and<br />
governance. Therefore, internal audits<br />
on processing activities, assessments on<br />
data protection policies and reviews of<br />
HR policies, should be started again as<br />
evidence that GDPR is being considered<br />
Data handling: it is important to identify<br />
sensitive data and control who has access,<br />
especially if it is an outside agency or<br />
processor<br />
Consent: as part of GDPR there must be<br />
a positive opt-in for data to be stored or<br />
used for marketing. Consent cannot be<br />
inferred from silence, pre-ticked boxes or<br />
inactivity. It must also be separate from<br />
other terms and conditions, and you will<br />
need to have simple ways for people to<br />
withdraw consent. Consent has to be<br />
verifiable<br />
Data breaches: a personal data breach<br />
means a breach of security leading to the<br />
destruction, loss, alteration, unauthorised<br />
26<br />
computing security March/April 2018 @CSMagAndAwards www.computingsecurity.co.uk
data regulations<br />
disclosure of, or access to, personal data.<br />
This needs to be reported within 72 hours<br />
and so companies need to have plans in<br />
place to meet this requirement.<br />
As to the NIS (Network Information Systems<br />
Directive, which takes effect from May 2019<br />
next year), this is directed at the cyber<br />
security requirements of essential services<br />
and digital service providers, so that robust<br />
security measures are installed, in order to<br />
protect networks and data against serious<br />
security breaches. "As a bare minimum," says<br />
Tankard, "they must control who has access<br />
to critical data and systems, and deploy<br />
strong authentication techniques, such as<br />
two-factor authentication, coupled with<br />
encryption. And it would be prudent to<br />
consider evidencing your security position<br />
by obtaining accreditation."<br />
AUDIO AND VIDEO<br />
As organisations work towards GDPR<br />
compliance, many may not realise that it<br />
also applies to audio and video material,<br />
if this allows individuals to be identified,<br />
points out James Wickes, CEO and cofounder,<br />
Cloudview. "This includes<br />
recordings from the CCTV systems that<br />
they use to protect people, property and<br />
premises. These systems are often installed<br />
without any involvement from the IT<br />
department, so may not be identified<br />
when assessing GDPR risks. Add in the<br />
NIS Directive and the risks of breaching the<br />
regulations escalate exponentially."<br />
The first step is to understand what data<br />
is being collected and how the risk arises, he<br />
says. "Vulnerabilities in CCTV systems range<br />
from use of port forwarding and Dynamic<br />
DNS to a lack of firmware updates and the<br />
existence of manufacturer 'back doors'<br />
which are often revealed on the internet."<br />
These back doors may be deliberate and<br />
pose a significant risk. However, ensuring<br />
compliance is relatively straightforward,<br />
Wickes says, suggesting the following:<br />
Carry out a Privacy Impact Assessment<br />
(PIA) to identity and minimise risks, and<br />
ensure there is appropriate signage and<br />
information about recording of video and<br />
audio data.<br />
Limit data access to authorised personnel<br />
only.<br />
Check record-keeping: recordings must be<br />
fit for purpose, accurately date and time<br />
stamped, and organisations should be<br />
able to access them easily to comply with<br />
a subject access request or police<br />
investigation.<br />
Continually assess data security. This<br />
includes simple precautions - ensuring<br />
strong passwords, regularly updating<br />
firmware, and ensuring CCTV data is<br />
encrypted both in transit and when<br />
stored, as recommended by the<br />
Information Commissioner's Office and<br />
the Surveillance Camera Commissioner.<br />
Some cloud-based systems encrypt all<br />
data at source and store it securely in<br />
the cloud.<br />
Limit data collection. This includes<br />
confirming that all CCTV cameras serve<br />
a legitimate purpose and the system<br />
can be switched off, so recording is not<br />
continuous. This is incredibly helpful when<br />
it comes to finding events. Continuous<br />
random recording makes it harder to find<br />
anything.<br />
Limit processing to the purpose for which<br />
the data is collected and delete recordings<br />
when they no longer serve a purpose. This<br />
prevents data being used for purposes<br />
outside those originally intended.<br />
"In the medium term, organisations with<br />
old cameras or cameras not manufactured<br />
in the UK should review their systems,"<br />
Wickes advises, "and consider whether<br />
to retrofit secure adapters or implement<br />
a more secure solution."<br />
Colin Tankard, managing director, Digital<br />
Pathways: encrypting known sensitive<br />
data can serve as a 'quick win'.<br />
Jes Breslaw, director of strategy,<br />
EMEA at Delphix: companies should be<br />
investigating the idea of DataOps.<br />
www.computingsecurity.co.uk @CSMagAndAwards March/April 2018 computing security<br />
27
product review<br />
TITANIA PAWS STUDIO 3.2.2<br />
SMEs daunted by data protection<br />
regulations and the looming<br />
GDPR (General Data Protection<br />
Regulation) can rest easy with Titania's<br />
Paws Studio. Very keenly priced, it's<br />
capable of auditing all Windows,<br />
macOS and Linux systems, and offers<br />
an impressive range of highly detailed<br />
regulatory compliance and vulnerability<br />
reports.<br />
This latest version delivers a wealth<br />
of new features, as, along with report<br />
modules for SANS, NSA, NERC, STIG<br />
and OVAL, it supports the PCI-DSS 3.2<br />
standard. It now audits to the CIS<br />
benchmark requirements and Cyber<br />
Essentials best practices guidelines,<br />
plus Titania includes a DCPP module<br />
in the Enterprise version.<br />
Paws Studio supports any host system<br />
running Windows 7 upwards, macOS<br />
Sierra or Linux. We loaded it on a<br />
Windows Server 2012 R2 host and had<br />
it licensed and ready for action in five<br />
minutes.<br />
The supported device list for auditing is<br />
equally impressive and includes Windows<br />
10 workstations. Furthermore, businesses<br />
still running legacy Windows XP, Vista or<br />
Server 2003 systems (and there's plenty<br />
that are) can use Paws Studio to ensure<br />
they aren't a major security risk.<br />
On first contact, we could see the<br />
console had received a design refresh,<br />
making it even easier to use. Creating<br />
a new audit was simple, as we chose<br />
compliance modules from the list<br />
presented or created our own custom<br />
policies and applied them to selected<br />
systems.<br />
We could choose local and remote<br />
target systems, and options are provided<br />
for manually adding devices, running<br />
a network discovery, scanning an IP<br />
address range or importing multiple<br />
systems from a CSV file. And that's all<br />
there is to do, as Paws Studio now gets<br />
on with auditing the systems.<br />
It pushes a small footprint Data<br />
Collector to each system, which gathers<br />
the relevant information and sends it<br />
back to the host for report creation.<br />
For isolated systems, you can export<br />
the Data Collector tool, along with the<br />
required audit policies, run it locally and<br />
import the results back into the host.<br />
Paws Studio is quick, too, as a report<br />
combining Cyber Essentials, SANS<br />
and NERC audits on four networked<br />
Windows 10 workstations took less<br />
than a minute. The console displays<br />
the completed report in the centre and<br />
right-hand panes, making it even easier<br />
to see which checks were passed or<br />
which failed.<br />
For our workstations, we could see<br />
immediately from the SANS audit that,<br />
although they all had anti-virus<br />
protection, users were allowed to install<br />
software on them, and our password<br />
length and complexity policies were lax<br />
at best. Choose an entry with a red<br />
cross next to it in the right-hand pane<br />
and it'll be loaded in the central pane,<br />
along with details of why the check<br />
failed and sage advice on remedial<br />
action.<br />
Yet another new feature is the option<br />
to clear a failure from a report after<br />
you've remedied the issue, so you don't<br />
have to run the whole audit again.<br />
Reports can be saved off, as Paws Studio<br />
'blueprints' are exported to the host's<br />
default web browser or saved in a range<br />
of formats, including HTML, XML and<br />
CSV - there's even an option to export<br />
just the report page being viewed.<br />
Along with accurate OS identification,<br />
the Data Collector delivers detailed<br />
hardware and software inventory.<br />
Choose a system in the report and you<br />
can view its BIOS version, CPU, memory,<br />
hard disks, network adapters, installed<br />
software, running programs and indeed<br />
a whole lot more.<br />
SMEs that want tight security and<br />
compliance with the latest data<br />
protection regulations will find Titania's<br />
Paws Studio an ideal partner. It's very<br />
easy to use, capable of delivering highly<br />
detailed audit reports for a raft of<br />
regulations and beats enterprise<br />
solutions hands down on price. CS<br />
Product: Paws Studio 3.2.2<br />
Supplier: Titania Ltd<br />
Telephone: +44 (0)1905 888785<br />
Web site: www.titania.com<br />
Price: 25 devices/3 years, £791 ex VAT<br />
28<br />
computing security March/April 2018 @CSMagAndAwards www.computingsecurity.co.uk
The first dedicated<br />
Recruitment EXPO<br />
for cyber security<br />
professionals<br />
Thursday 5th April 2018<br />
UWE Conference Centre, Bristol<br />
www.CyberSecurityExpo.co.uk<br />
The Bristol Expo<br />
is FREE to attend<br />
Come and meet the<br />
companies hiring within<br />
Cyber Security.<br />
Find out about<br />
the latest hot jobs<br />
100s of job vacancies<br />
available on the day.<br />
Free entry into<br />
the Security<br />
Cleared EXPO<br />
Industry Partners:
masterclass<br />
HOW TO UNDERPIN SECURITY TRANSFORMATION WITH<br />
COMPLETE VISIBILITY OF YOUR ATTACK SURFACE<br />
CHARLOTTE GURNEY, MARKETING MANAGER, BROOKCOURT SOLUTIONS, PROVIDES<br />
KEY INSIGHTS ON A CRUCIAL ISSUE THAT CHALLENGES SO MANY ENTERPRISES<br />
Charlotte Gurney, Marketing Manager,<br />
Brookcourt Solutions.<br />
There are many reasons why you may<br />
be considering or engaged in a security<br />
transformation programme tasked<br />
with reducing the risk of cyberattacks. For<br />
example:<br />
You've appointed a new chief information<br />
security officer (CISO) who wants to<br />
implement a fast track programme<br />
delivering immediate improvements<br />
You've deployed many different security<br />
technologies and are conducting regular<br />
audits, but you're struggling to continue<br />
to scale your IT security team<br />
You've taken a highly tool-centric<br />
approach to cybersecurity, but have too<br />
much data, not enough people, your<br />
processes aren't sufficiently mature or<br />
your operational approach simply isn't<br />
working<br />
You've tried outsourcing your security, but<br />
this isn't delivering the anticipated<br />
benefits<br />
You're struggling to answer questions<br />
from senior executives, such as where are<br />
we most at risk from an attack, what's<br />
being done and what options do we<br />
have to prevent this?<br />
A familiar thread across all these issues is<br />
the search for an improved approach and<br />
processes to help you better utilise your<br />
existing resources. But if you don't know<br />
precisely what you're trying to defend, it's very<br />
difficult to plan an effective security strategy<br />
to achieve this. And without a central model,<br />
and a clear and detailed view of your<br />
infrastructure, the likelihood is that the<br />
technologies and processes you're trying to<br />
deploy are going to be badly instituted or<br />
simply not work at all.<br />
A common sense structure and approach is<br />
needed to understand your attack surface,<br />
achieve immediate results early in your<br />
security transformation, and create a trusted<br />
platform on which to mature and evolve your<br />
processes over time. This helps address key<br />
security challenges including:<br />
Very poor context of the attack surface,<br />
on account of its complexity, scale,<br />
heterogeneous technology, use of cloud,<br />
outsourcers, etc; historical data that is<br />
often out of date.<br />
The need to demonstrate a quick risk<br />
reduction, which means identifying any<br />
gaps in compliance and exposure, high<br />
risk vulnerabilities, and all ingress/egress<br />
points.<br />
Improving security and compliance by<br />
leveraging existing processes, such as<br />
how to turn firewall change mangement<br />
into a first line of defence, ensure the<br />
patch process is serving your security<br />
needs and embed compliance<br />
management within normal day-to-day<br />
operations.<br />
Using security transformation to deliver<br />
increased business value, by elevating<br />
the security operations team from a<br />
blocker to a strategic business enabler<br />
that increases ROI.<br />
How best to plan and manage the<br />
transformation programme, to mature<br />
your approach to security and avoid the<br />
mistakes made by early adopters who<br />
over-invested in technology.<br />
Recommended phased maturity approach<br />
Resilience Assessment<br />
Start by focusing on discovery and high-risk<br />
threat mitigation:<br />
1. Build a model of your complete<br />
organisational infrastructure, and provide<br />
context around all of the ingress/egress<br />
points and complexities of your network<br />
and assets, to give you a detailed<br />
understanding of what you're trying to<br />
defend<br />
2. This model should be automatically<br />
updated on a daily basis, giving you an<br />
ongoing and always current view of your<br />
attack surface<br />
3. The model can then be regularly analysed<br />
to identify all of the opportunities to quickly<br />
reduce risk, increase resilience and deliver<br />
immediate results<br />
4. Evolve and improving your existing<br />
processes, or instituting new ones in areas<br />
including automating compliance and<br />
policy management, automating firewall<br />
and change management, and improving<br />
vulnerability management<br />
5. Moving into more advanced use cases,<br />
such as embedding Skybox into a SOC or<br />
computer emergency response team (CERT),<br />
using it to assist with outsourcing to a<br />
managed security service provider (MSSP).<br />
Brookcourt and Skybox Security will help<br />
you deliver superior results from your<br />
security transformation initiatives. Please<br />
contact: www.brookcourtsolutions.com<br />
30<br />
computing security March/April 2018 @CSMagAndAwards www.computingsecurity.co.uk
hacked credentials<br />
THE DARK DESTROYERS<br />
OVER ONE MILLION LEAKED AND HACKED CREDENTIALS FOUND ON THE DARK WEB<br />
hacked credentials. Even where<br />
passwords aren't present, each of these<br />
exposed email addresses represents a<br />
potential attack on a company's network<br />
for criminals via phishing or other scams.<br />
NO ONE IS SAFE<br />
Patrick Martin, cybersecurity analyst at<br />
RepKnight, comments: "The truth is that<br />
no company in the world is safe from<br />
the threat of the dark web. The top 500<br />
law firms RepKnight analysed almost<br />
certainly haven't done anything wrong,<br />
cybersecurity-wise, but all it takes for a<br />
breach to occur nowadays is for a single<br />
employee to accidentally fall for a<br />
phishing email or send sensitive data via<br />
email accidentally to the wrong person.<br />
It's almost impossible to prevent.<br />
More than a million leaked and<br />
hacked credentials from the<br />
UK's top law firms have been<br />
tracked down to the Dark Web, leaving<br />
the firms vulnerable to phishing scams<br />
and the possibility of significant data<br />
theft. The figures represent an average<br />
of 2,000 email addresses per company,<br />
with the largest firm having just over<br />
30,000 email addresses on the dark web.<br />
The email addresses, including nearly<br />
80,000 from the legal industry's Magic<br />
Circle, have been found by cybersecurity<br />
specialist RepKnight as part of a<br />
campaign to raise awareness of the huge<br />
number of leaked and hacked credentials<br />
circulating on the dark web.<br />
Almost all of the credentials were from<br />
third-party breaches, where a corporate<br />
email address had been used on a site<br />
like LinkedIn or Dropbox and that site<br />
was subsequently compromised.<br />
Worryingly, 80% of these email<br />
addresses featured in breaches which<br />
also contained passwords - often in<br />
plaintext. Cybercriminals could<br />
potentially use these password to gain<br />
access to other private data, such as<br />
employees' online banking or social<br />
media, via 'credential stuffing' or spear<br />
phishing attacks, because more than<br />
80% of people tend to re-use their<br />
password.<br />
Using RepKnight's dark web monitoring<br />
tool BreachAlert, RepKnight was able to<br />
uncover each of the exposed email<br />
domains across dark web, bin, dump<br />
and data breach sites, which feature<br />
almost five billion stolen, leaked or<br />
"The data we found represents the<br />
easiest data to find - we just searched on<br />
the corporate email domain. A far bigger<br />
issue for law firms is data breaches of<br />
highly sensitive information about client<br />
cases, customer contact information or<br />
employee personal info, such as home<br />
addresses, medical record and HR files.<br />
That's why - in addition to securing<br />
their networks - every firm should be<br />
deploying a dark web monitoring<br />
solution, so they can get alerted to leaks<br />
and breaches immediately."<br />
The research by RepKnight sheds light<br />
on the importance of breach detection,<br />
as well as prevention. On average,<br />
European organisations take around<br />
450 days to spot a security breach,<br />
which means that cybercriminals have<br />
a huge amount of time to access<br />
a corporate network, steal sensitive data<br />
and leave before the organisation even<br />
realises that they've been there.<br />
www.computingsecurity.co.uk @CSMagAndAwards March/April 2018 computing security<br />
31
connected cars<br />
DRIVING INTO THE UNKNOWN<br />
TACKLING THE MANY CYBERSECURITY AND<br />
OTHER SAFETY ISSUES AROUND CONNECTED<br />
CARS HAS BECOME AN IMPERATIVE<br />
Connected cars are a reality; most<br />
modern vehicles on the road<br />
nowadays have some form of<br />
connectivity to the open world. This raises<br />
important challenges on multiple software<br />
integration and cybersecurity. To address<br />
this challenge, Thales, through its German<br />
company Sysgo, along with Vector, the<br />
Stuttgart-based specialist for automotive<br />
embedded electronics, founded a joint<br />
venture to address the critical issue of<br />
multiple software managing multiple,<br />
often safety-critical, functions.<br />
The volume and complexity of software<br />
used to manage virtually every aspect of<br />
a connected or autonomous vehicle, both<br />
mechanic and electronic, could bear a<br />
potential risk to people's safety. Each<br />
software presents a potential attack surface<br />
for security breaches, which could affect<br />
the overall reliability of the vehicle. The<br />
aim of this partnership is to co-develop an<br />
integrated software platform for improved<br />
performance and cybersecurity.<br />
Through this joint-venture, Thales and<br />
Vector will combine their respective<br />
embedded systems expertise in aviation<br />
safety and in automotive software<br />
according to ISO 26262 to offer a single<br />
platform to run the car's software and<br />
applications. By simplifying the vehicle's<br />
control systems, they aim to strengthen<br />
its cyber-protection, while ensuring the<br />
isolation of individual applications.<br />
SINGLE SOURCE SOLUTION<br />
To achieve this, the two experts will look to<br />
co-develop the new platform by combining<br />
two pre-existing products: MICROSAR,<br />
Vector's AUTOSAR* Adaptive basic<br />
software, and PikeOS, Sysgo's real-time<br />
operating system. Through this integration,<br />
coupled with further co-development, the<br />
two companies are aiming to provide the<br />
automotive industry with a single-source<br />
solution. "Cybersecurity and Safety Critical<br />
Systems are part of the Thales DNA. For us,<br />
this joint initiative with Vector and Sysgo is<br />
a natural step beyond what we already do<br />
for the automotive industry in cybersecurity<br />
services and consulting", says Laurent<br />
Maury, vice-president, Critical Information<br />
Systems and Cybersecurity, Thales.<br />
Designed for the new generation of highperformance<br />
Electronic Control Units<br />
(ECUs), based on the AUTOSAR Adaptive<br />
standard, a release of the joint solution for<br />
prototype applications is planned later this<br />
year and series releases for safety-relevant<br />
control units are expected in 2019.<br />
Meanwhile, Ansys, which develops and<br />
markets engineering simulation software,<br />
states that, while connected car technology<br />
is a "bonus and a pleasure for car buyers", it<br />
poses unprecedented new engineering<br />
challenges regarding reliability, safety and<br />
security for car manufacturers.<br />
In its report on connected technology,<br />
'Ensuring Reliability and Safety of<br />
Connected Car Technology', it comments:<br />
"As we rely more and more on connectivity<br />
of cars, many potential problems could<br />
emerge from faulty connected car<br />
technology, including simple connection<br />
interruptions, display malfunctions, signal<br />
interference, and expensive failure of<br />
sensitive electronic hardware under heat<br />
and harsh conditions within vehicles.<br />
"Imagine being lost while driving in an<br />
unknown city, due to GPS signal loss, or the<br />
frustration of being unable to operate the<br />
air conditioner on a hot day, because the<br />
car's touch screen interface has difficulty<br />
recognising the touch of sweaty fingers.<br />
Connected car technology also opens doors<br />
to much more serious, unprecedented<br />
problems, such as cyber security holes and<br />
software bugs that could lead to potentially<br />
fatal safety issues." Such problems can<br />
quickly lead to consumer dissatisfaction and<br />
brand depreciation. And there can be even<br />
more serious consequences, if, for instance,<br />
remote hackers use the connectivity to<br />
32<br />
computing security March/April 2018 @CSMagAndAwards www.computingsecurity.co.uk
connected cars<br />
therefore trade off the desired level of<br />
effectiveness (and the systems that can be<br />
updated) against the costs. That calls for a<br />
deep understanding of the architectures and<br />
peculiarities of these systems."<br />
Embedded software is in the focus of the joint venture between Vector and SYSGO<br />
for autonomous driving. Image rights: Vector Informatik GmbH<br />
exploit security holes for theft or to<br />
jeopardise passenger safety, it adds.<br />
COMPLEX WORLD<br />
According to global management<br />
consulting firm McKinsey&Company,<br />
automotive products are becoming more<br />
complex, with an increasing number of<br />
electronic control units and lines of code.<br />
"Connectivity is burgeoning, with dangers<br />
at every turn. The supply chain is quite<br />
fragmented, so policing security is hard.<br />
And the integration of automotive systems<br />
can also serve to compromise any specific<br />
countermeasure.<br />
Adds McKinsey&Company: "We believe<br />
that the sector needs a holistic, two-front<br />
approach to cybersecurity. On the first<br />
front, solutions ought to address the design<br />
of the product, the way it's developed,<br />
and the maintenance-and-response<br />
architecture.<br />
"On the second, OEMs should focus more<br />
effectively on the automotive environment<br />
at the sector level (for instance, by<br />
cooperating among themselves), on the<br />
concerns of regulatory bodies and on the<br />
mind-sets of final users, who must actively<br />
protect their cars." A secure design, while<br />
necessary, won't guarantee full security over<br />
time. Solutions are effective only if they are<br />
implemented consistently, and high-quality<br />
components-software and hardware alikeimplement<br />
the design.<br />
"This requirement calls for a sound and<br />
managed development process, including<br />
reinforced collaboration between productsecurity<br />
teams and corporate IT-security<br />
teams. OEMs must thus create and enforce<br />
strict guidelines to minimise the chances of<br />
bugs and software-security gaps and to make<br />
modifying or patching systems easier.<br />
"That's why over-the-air (OTA) updates -<br />
which have recently become available for<br />
some cars, though often for limited parts of<br />
software - are clearly essential for connected<br />
systems: they help OEMs to counter attacks<br />
quickly and to eliminate specific vulnerabilities<br />
before malefactors can exploit them."<br />
DEEP UNDERSTANDING<br />
However, these benefits have a price,<br />
McKinsey&Company concedes, in that<br />
implementing support for OTA updates is<br />
quite complex and expensive, both for cars<br />
and the back-end infrastructure. "OEMs must<br />
OEMs, which exclusively control the<br />
relationship with customers and are usually<br />
the final system integrators, bear the ultimate<br />
responsibility for integration risk and for<br />
ensuring that secure stand-alone systems<br />
aren't vulnerable when connected, it insists.<br />
"These companies must ascertain that security<br />
practices have been implemented consistently<br />
throughout the full value chain, including<br />
suppliers. Procurement executives must<br />
therefore learn to negotiate over the<br />
cybersecurity features of components as<br />
rigorously as they do anything else. OEMs<br />
should also play an active role in shaping<br />
the sector's future standards-both regulations<br />
and best-practice guidelines."<br />
McKinsey&Company points to how in many<br />
sectors, including oil and gas, financial services<br />
and aviation, alliances help companies to deal<br />
with regulators and to share intelligence on<br />
threats and vulnerabilities, both internally<br />
(among OEMs and suppliers) and externally<br />
(with regulatory bodies and the media). "Such<br />
alliances also facilitate prompt responses to<br />
novel threats. Some automotive companies<br />
are already creating alliances; other OEMs and<br />
suppliers should consider joining them."<br />
Automotive OEMs face a unique challenge,<br />
it adds, so they must complement their own<br />
efforts to develop security strategies by taking<br />
action on a higher level: the sector as a whole<br />
must secure its products across the entire<br />
supply chain by developing new ways to<br />
collaborate and interact. "If it doesn't,<br />
cybersecurity problems could irritate<br />
customers or even generate regulatory<br />
burdens that might well upend the cars of<br />
the future before they hit the road."<br />
*AUTOSAR (Automotive Open System<br />
Architecture) is a worldwide partnership,<br />
which develops the standardised software<br />
framework for intelligent mobility.<br />
www.computingsecurity.co.uk @CSMagAndAwards March/April 2018 computing security<br />
33
artificial intelligence<br />
AI VERSUS A HUMAN HACKER<br />
HOW DOES MACHINE LEARNING AND ARTIFICIAL INTELLIGENCE (AI) IMPACT CYBER SECURITY?<br />
type the words you see in the<br />
image." Familiar? Yes, at some<br />
"Please<br />
point we have all completed a<br />
'captcha' to prove we are human when<br />
online. So, when a robot successfully<br />
completed the test, the inevitable question,<br />
says Jonathan Wilkins, marketing director<br />
at obsolete parts supplier EU Automation,<br />
was: "Are our computers secure?"<br />
A captcha, or 'Completely Automated<br />
Public Turing test to tell Computers and<br />
Humans Apart', is designed based on the<br />
Turing test. "Alan Turing, the founder of<br />
modern computing, built a machine that<br />
was capable of mimicking human speech<br />
in letters, so that outsiders could not<br />
distinguish between human and robotic<br />
conversations," states Wilkins. "This<br />
machine inspired the field of artificial<br />
intelligence, bringing with it security tests<br />
to distinguish between humans and<br />
machines."<br />
Technology is advancing rapidly, he adds,<br />
meaning that computers can now solve<br />
problems that could only be solved with<br />
human intuition traditionally. "But what<br />
does a robot beating a captcha have to do<br />
with cyber security in manufacturing<br />
facilities?<br />
"As manufacturing becomes more<br />
digitalised, connected machines collect realtime<br />
data that is vital in keeping facilities<br />
running at optimum capacity. As more<br />
machines become connected, thanks to the<br />
Internet of Things (IoT), they also become<br />
more vulnerable to viruses that can be<br />
introduced to the system.<br />
"The growing use of AI in industry means<br />
that manufacturers must do more to secure<br />
information," he adds. "However,<br />
manufacturers can look to similar AI<br />
technology for help. If it can hack a system<br />
by pretending to be human, could it<br />
successfully block a similar threat from<br />
a human hacker?"<br />
IMPACT UNCERTAIN<br />
Industrial viruses are traditionally introduced<br />
from an external source, such as a USB or<br />
incoming data file. "Both machines and<br />
humans will find it difficult to predict<br />
how this threat will impact the IT and<br />
manufacturing system. However, humans<br />
have the upper hand on computers, as they<br />
can use past experience and knowledge to<br />
deal with any system abnormalities."<br />
Robots do not have the same intuition, he<br />
states, but advancements in machine<br />
learning allow computers to make decisions<br />
based on collected data. Each time the<br />
machine experiences something new, its<br />
capabilities will increase.<br />
"Some professionals argue that traditional<br />
security protocols are reactive and only deal<br />
with attacks when they occur. In the past,<br />
human hackers have easily broken through<br />
barriers such a passwords and firewalls.<br />
Now, cyber security companies are offering<br />
solutions to this, using AI and machine<br />
learning technology to introduce more<br />
preventative security for manufacturers."<br />
OUT OF THE DARK<br />
He singles out security company Darktrace,<br />
which uses machine learning to create<br />
unique patterns of encryption for each<br />
machine and detect any abnormalities. "The<br />
software can then detect emerging threats<br />
that may have gone unnoticed and stop<br />
them before the damage occurs."<br />
Artificial intelligence is developing rapidly<br />
and changing cyber security considerations<br />
in manufacturing. "It is unclear how<br />
much AI will be capable of in the future,"<br />
concludes Wilkins, "but we need to rethink<br />
how we distinguish between humans and<br />
robots online."<br />
34<br />
computing security March/April 2018 @CSMagAndAwards www.computingsecurity.co.uk
2013
DETECT TARGETED ATTACKS AND ADVANCED<br />
THREATS ON YOUR NETWORK<br />
Protect your network with 360-degree monitoring from the<br />
most recommended breach detection system 1 .<br />
Achieve faster and higher ROI.<br />
www.trendmicro.co.uk/xgen-cyber<br />
1<br />
Trend Micro Deep Discovery<br />
100%<br />
Breach Detection Rate<br />
- 2017 -<br />
RECOMMENDED 4 years in a row<br />
©2017 Trend Micro, Inc. All rights reserved. Trend Micro, the t-ball logo and Deep Discovery Inspector are trademarks or registered trademarks of Trend Micro, Inc.